Not long ago, most companies whose brands were being abused in phishing scams focused their efforts mainly on shuttering the counterfeit sites as quickly as possible. These days, an increasing number of phished brands are not only disabling the sites, but also seizing on the opportunity to teach would-be victims how to spot future scams.
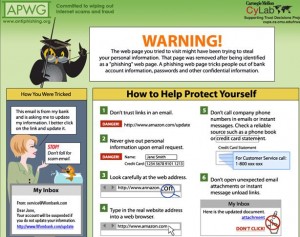
Instead of simply dismantling a phishing site and leaving the potential phishing victims with a “Site not found” error, some frequent targets of phishing sites are setting up redirects to phishing education pages.
 For the past 20 months, Jason Hong, assistant professor of computer science at Carnegie Mellon University‘s Human Computer Interaction Institute, has been measuring referrals from phishing sites to an education page set up by the Anti-Phishing Working Group (APWG), an industry consortium. Hong said the site now receives close to 25,000 referrals per month from phishing sites that brand owners have modified.
For the past 20 months, Jason Hong, assistant professor of computer science at Carnegie Mellon University‘s Human Computer Interaction Institute, has been measuring referrals from phishing sites to an education page set up by the Anti-Phishing Working Group (APWG), an industry consortium. Hong said the site now receives close to 25,000 referrals per month from phishing sites that brand owners have modified.
The redirect process works like this: The brand owner or company whose customers are targeted by the phishing site verifies it as a scam site, and then the site’s ISP, hosting provider or domain registrar will redirect the phishing site to the APWG education page.
From Sept. 2008 to April 2010, Hong tracked 1.16 million hits from roughly 15,000 unique redirected URLs. To filter out probable victims from other “noise” traffic — such as random Web crawlers and people testing the landing pages — CMU scrubbed the data of hits that didn’t identify the original phishing site, as well as those that appeared to be for testing only (Internet addresses that hit multiple phishing URLs per day, for example).
After filtering the results, Hong said his team found roughly 200,000 hits on 1,285 URLs — or about 156 hits per URL — that were very likely clicks from people who would have given away financial data and/or passwords at phishing Web sites had those sites still been active at the time. That may seem like a lot of victims per phishing site, but while the average number of filtered hits per URL was 100-300 per month, the median is quite low, from 2-7 per month.
That means there are some really “successful” phishing attacks that many people click on, probably either because a huge number of spam e-mails advertising that fake site were sent, or because the phishing e-mails were particularly compelling. However, the majority of phishing campaigns appear to be quite unsuccessful, in that they don’t hook a lot of people, Hong said.
“There are a few sites that have a lot of hits, and a lot of sites that have very few hits,” he said. “That means there is a very long tail of phish.”
These figures are likely to be conservative. For one thing, the researchers had no way to measure how many people clicked through to the phishing site before it was shuttered and further visits were redirected to the APWG education page. What’s more, most Web browsers now include anti-phishing technology that blocks users from visiting known phishing Web sites, usually within hours of the scam sites going live.
Still, it may still be worthwhile even for phishers who hook just a handful of victims per attack, as the startup costs for phishing scams often are next to nil (spam is often routed through hacked machines, and the APWG estimates that between 75-80 percent of phishing sites are legitimate sites that have been hacked and seeded with phishing kits). I couldn’t find any recent and reliable stats on average phishing losses, but if we assume for the moment that people who get phished lose on average $500, it doesn’t take too many victims to make it a profitable venture.



Brian,
thank you again for accurate and timely information. I have two comments.
1 – for some reason lately, your emails have no space between the subject and your address. For example, this current message came through as:
Momentshttp://krebsonsecurity.com/2010/05/phished-brands-seize-on-teachable-moments/
I do not know if it is your email, or my client (mail.com).
2 – I have been getting quite a few phishing emails in Operamail. I tried VERY hard to advise Amazon about one of them, and they made it so difficult to find out where to report it, I JUST GAVE UP! It is just too bad these big websites don’t put something on their front end to advise how to report.
Thanks again, please keep up the good work!
Hi Jim,
thanks for the comment. I think the email link problem is a result of a WordPress plug-in gone awry. Currently trying to figure out which one. Thanks for your patience.
jim, If you report phish to http://APWG.org your complaint will be passed on to all members, including the banks and takedowns are brutal afterwards as they throw some pocket change at the problem.
I assuming that password managers that memorize URLs, are a good way to avoid being phished. I always navigate to my vendors; I rarely follow an email, except to see if the password manager recognizes it as a legitimate address.
If I change anything in the address line, the manager treats it like a new web-site.
I have a correction. I helped with the original deployment of the landing page, and the presentation at APWG. The analysis of the APWG data was done by Lorrie Cranor (CMU) and Laura Mather (APWG and Silver Tail Systems).
They deserve more of the credit for the work, just wanted to clarify.
Silver Tail has put out some of the best webinars on banking and web-browser security I’ve ever witnessed.
Must be a pretty good company!
JCitzen,
thank you for the advice. In the instance I was referencing to, my account with Amazon has email.com as my client. The phishing email was sent to my Operamail account (which has no connection to Amazon). This flagged it for me as bogus. It is not the first time I have been phished in the Operamail account. Several of my accounts that are NOT linked to Operamail have been phished lately. What I was trying to point out was that these vendors should make it a whole lot easier to report to their websites when people are being phished. It seems to me that it would be better publicity for them than people falling for the scam and blaming the vendor.
I see; thank you very much!
Pete,
thanks for the link. I will use it as necessary.
I do not quite follow the second part of your message
“takedowns are brutal afterwards as they throw some pocket change at the problem.”
@Jim Banks always pay money to save money 😉
Once discovered, Banks, pay companies like Internet Identity, RSA, Phishlabs, Netcraft, fraudwatch, markmonitor (and others) to pursue the deactivation of phish sites. They either contact the host for shared sites or the registrar botnet hosted domains.
These companies file abuse reports, pick up the phone, have huge contact databases, the industry also fights back a little, phishfeeding for instance http://www.sans.edu/resources/student_presentations/PhishFeeding.pdf is not unknown, and I’ve heard rumour that somewhat unethical takedown methods are also available. Not that you can find that sort of thing via google of course 😉
Some of these companies also offer in house detection systems for the banks too.
i get 20-30 e mails per day
through my hotmail adress
in those e mails it is written
that i have won i great lottery
and i have to give some informations
about my name, surname, adress, telephone
number, password etc
THOSE E MAILS ARE VERY ANNOYING
mr.Krebs thank you for the useful
information
That’s funny; I only get, like one or two spam email a week, on my hotmail account! To each is own, I guess!