Microsoft said Thursday that it convinced a U.S. federal court to grant it control over a botnet believed to be closely linked to counterfeit versions Windows that were sold in various computer stores across China. The legal victory also highlights a Chinese Internet service that experts say has long been associated with targeted, espionage attacks against U.S. and European corporations.
Microsoft said it sought to disrupt a counterfeit supply-chain operation that sold knockoff versions of Windows PCs that came pre-loaded with a strain of malware called “Nitol,” which lets attackers control the systems from afar for a variety of nefarious purposes.
In legal filings unsealed Thursday by the U.S. District Court for the Eastern District of Virginia, Microsoft described how its researchers purchased computers from various cities in China, and found that approximately 20 percent of them were already infected with Nitol.
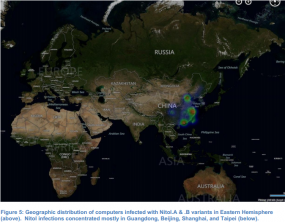
It’s not clear precisely how many systems are infected with Nitol, but it does not appear to be a particularly major threat. Microsoft told the court that it had detected nearly 4,000 instances of Windows computers infected with some version of the malware, but that this number likely represented “only a subset of the number of infected computers.” The company said the majority of Nitol infections and Internet servers used to control the botnet were centered around China, although several U.S. states — including California, New York and Pennsylvania — were home to significant numbers of compromised hosts.
Dubbed “Operation b70” by Microsoft, the courtroom maneuvers are the latest in a series of legal stealth attacks that the software giant has executed against large-scale cybercrime operations. Previous targets included the Waledac, Rustock, Kelihos and ZeuS botnets.
The core target of this takedown was 3322.org, a Chinese “dynamic DNS” (DDNS) provider. DDNS providers offer typically free services that allow millions of legitimate users to have Web sites hosted on servers that frequently change their Internet addresses. This type of service is useful for people who want to host a Web site on a home-based Internet address that may change from time to time, because dynamic DNS services can be used to easily map the domain name to the user’s new Internet address whenever it happens to change.
Unfortunately, these dynamic DNS providers are extremely popular in the attacker community, because they allow bad guys to keep their malware and scam sites up even when researchers mange to track the attacking IP address and convince the ISP responsible for that address to disconnect the miscreant. In such cases, dynamic DNS allows the owner of the attacking domain to simply re-route the attack site to another Internet address that he controls.
Microsoft told the court it found “a staggering 500 different strains of malware hosted on more than 70,000 subdomains” at 3322.org. The court granted Microsoft temporary control over the name servers for that domain. While 3322.org is owned by a Chinese firm, the dot-org registry is controlled by the Public Interest Registry, a company based in Reston, Va.
Although Microsoft did not explicitly address this in its filing, experts say 3322.org has long been associated with malware used in highly targeted attacks aimed at stealing corporate and government secrets from U.S. and other Western firms.
“The vast majority of the interactions with the 3322.org hostnames for those outside of Asia — particularly those in the United States are malicious,” said Steven Adair, a security expert with Shadowserver.org, a nonprofit that helps ISPs track malware attacks. “While not quite as prevalent now, the 3322.org domain has been a hot spot for malware used to conduct cyber espionage for several years now. We can already tell this move has had an impact on cyber crime operations.”
But it is not clear how effective this action will be at blocking that activity, or more than temporarily disrupting Nitol’s operations.
Joe Stewart, director of malware research for Dell SecureWorks, posted a message to Twitter.com this morning noting that only 57 percent of the subdomains he’s been tracking as related to targeted, espionage-type attack activity were disrupted by Microsoft’s action.
Part of the problem may be that much of the malware calling home to 3322.org has instructions built into its genetic makeup to seek out commands and updates from many other dynamic DNS providers not impacted by the court order, said Gunter Ollmann, vice president of research at security firm Damballa.
“What we’ve seen is that we’re currently tracking about 70 different botnets that had command and control domain names within 3322,” Ollmann said. “But all of those have secondary domain name [controllers] outside of 3322.org.”
Potentially complicating matters further, 3322.org now appears to be instructing affected users on how to get around having their sites redirected to Microsoft’s servers.
Microsoft has made the legal documents related to this case freely available from noticeofpleadings.com.



Great stuff as usual Brian. Thanks.
What cracks me up about reports like this is just how quick the security “experts” are to diminish the value or effectiveness of Microsoft’s efforts.
I applaude Microsoft’s efforts; thank you for disrupting one of the major vectors used by criminals, terrorist and spies to attack, steal or compromise our resources and national security. Well done!
While it is nice that they took action, it would have been better if they had done a more thorough investigation of how the botnet operates when 3322 is shut down, then investigate what happens when the next DDNS site is shut down, and so on, then perform a takedown of all sites.
As it is, botnets and malware will route around the single domain seizure and, over time, little will come of this. In other words, while there is a current hit in traffic, it will pick up as malware fails to contact its masters and moves on to backup C&C systems on other domains.
On the other hand, who knows, maybe Microsoft is planning on asking the judge to grant it control of the other domains next.
“While it is nice that they took action, it would have been better if they had done a more thorough investigation of how the botnet operates when 3322 is shut down, then investigate what happens when the next DDNS site is shut down, and so on, then perform a takedown of all sites.”
Is this what you have done wrt other botnets? If so I would love to read about it.
Or do you know security researchers who have done this wrt other botnets? If so, I would love to read about it.
As far as I know, abuse.ch (one of the best in the biz) is about the only security researcher actually doing the kind of work you describe. He also never complains (AFAIK) when Microsoft shuts down a botnet. My hunch is that the unnamed security researchers who complain about botnets getting shut down only do so because they have a financial incentive to keep botnets around: their investigations are worth a pretty penny to multinational corporations with more money than they know what to do with, and shutting down botnets shuts down the gravy train.
I was unaware that posting comments on this site required prior experience shuttering large-scale botnets. I assume that you have the necessary experience? If so, why are you posting here when Nitol is still in the wild? Go, man, go, for the good of the internets!
Like clubbing one baby seal doesn’t kill all baby seals, shuttering one domain isn’t going to have any kind of long-term affect on malware that’s coded to use multiple DDNS providers.
Just because you don’t like the ugly reality of the situation we’re all in doesn’t change reality.
“Unnamed”? The people complaining so far do have a rather long track record in security, and certainly aren’t anonymous.
Action needed to be taken. Whether siezing the domain through a court order and proxying dns requests for it was, or was not a bad idea .. well, this could have been handled a lot better.
http://www.circleid.com/posts/20120917_microsoft_takedown_of_3322_org_a_gigantic_self_goal/
– https://blog.damballa.com/archives/1806
Sep 13, 2012 – “… Nitol… employs multiple domains from several free dynamic DNS providers, including -other- four-digit .ORG domain services such as
6600 .org, 7766 .org, 2288 .org and 8866 .org…”
(Highly recommend blocking those addresses also, if you haven’t already.)
.
waldec and kelihs are the same botnet
they only took down the public version of rustock
none of the zeus campaigns were P2P
Now that’s an interesting article IMO, and it will be interesting to see what MicroSoft does in regards to ridding the world of counterfeit versions of it’s Windows.
You probably caught this on the news this morning:
http://www.nbcwashington.com/news/local/ATM-Skimmer-169624676.html
The effect of this court order may not be that significant. But if no one takes any action against organizations that tolerate criminal activity on their networks, you end up with the situation we’ve got now where criminals operate so openly that they can amass huge botnets that constitute a threat to normal internet operations.
A court order that affects one company may cause a dozen others to give a little more thought to how they conduct their business. Even if the criminal activity were just driven a little farther underground, maybe the rest of us wouldn’t have 90% of the unfiltered email in our inboxes coming from criminals instead of people we know. Criminals ought to at least feel a need to be stealthy.
Great article Brian. The Nitol “takedown” is much much bigger than ridding the Internet of some run of the mill botnet. This is counter-cyberespionage gold.