Most Internet users are familiar with the concept of updating software that resides on their computers. But this past week has seen alerts about an unusual number of vulnerabilities and attacks against some important and ubiquitous hardware devices, from consumer-grade Internet routers, data storage and home automation products to enterprise-class security solutions.
 Last week, the SANS Internet Storm Center began publishing data about an ongoing attack from self-propagating malware that infects some home and small-office wireless routers from Linksys. The firewall built into routers can be a useful and hearty first line of protection against online attacks, because its job is to filter out incoming traffic that the user behind the firewall did not initiate. But things get dicier when users enable remote administration capability on these powerful devices, which is where this malware comes in.
Last week, the SANS Internet Storm Center began publishing data about an ongoing attack from self-propagating malware that infects some home and small-office wireless routers from Linksys. The firewall built into routers can be a useful and hearty first line of protection against online attacks, because its job is to filter out incoming traffic that the user behind the firewall did not initiate. But things get dicier when users enable remote administration capability on these powerful devices, which is where this malware comes in.
The worm — dubbed “The Moon” — bypasses the username and password prompt on affected devices. According to Ars Technica’s Dan Goodin, The Moon has infected close to 1,000 Linksys E1000, E1200 and E2400 routers, although the actual number of hijacked devices worldwide could be higher and is likely to climb. In response, Linksys said the worm affects only those devices that have the Remote Management Access feature enabled, and that Linksys ships these products with that feature turned off by default. The Ars Technica story includes more information about how to tell whether your router may be impacted. Linksys says it’s working on an official fix for the problem, and in the meantime users can block this attack by disabling the router’s remote management feature.
Similarly, it appears that some ASUS routers — and any storage devices attached to them — may be exposed to anyone online without the need of login credentials if users have taken advantage of remote access features built into the routers, according to this Ars piece from Feb. 17. The danger in this case is with Asus router models including RT-AC66R, RT-AC66U, RT-N66R, RT-N66U, RT-AC56U, RT-N56R, RT-N56U, RT-N14U, RT-N16, and RT-N16R. Enabling any of the (by-default disabled) “AiCloud” options on the devices — such as “Cloud Disk” and “Smart Access” — opens up a potentially messy can of worms. More details on this vulnerability are available at this SecurityFocus writeup.
ASUS reportedly released firmware updates last week to address these bugs. Affected users can find the latest firmware updates and instructions for updating their devices by entering the model name/number of the device here. Alternatively, consider dumping the stock router firmware in favor of something more flexible, less buggy amd most likely more secure (see this section at the end of this post for more details).
YOUR LIGHTSWITCH DOES WHAT?
Outfitting a home or office with home automation tools that let you control and remotely monitor electronics can quickly turn into a fun and addictive (if expensive) hobby. But things get somewhat more interesting when the whole setup is completely exposed to anyone on the Internet. That’s basically what experts at IOActive found is the case with Belkin‘s WeMo family of home automation devices.
According to research released today, multiple vulnerabilities in these WeMo Home Automation tools give malicious hackers the ability to remotely control the devices over the Internet, perform malicious firmware updates, and access an internal home network. From IOActive’s advisory (PDF):
The Belkin WeMo firmware images that are used to update the devices are signed with public key encryption to protect against unauthorised modifications. However, the signing key and password are leaked on the firmware that is already installed on the devices. This allows attackers to use the same signing key and password to sign their own malicious firmware and bypass security checks during the firmware update process.
Additionally, Belkin WeMo devices do not validate Secure Socket Layer (SSL) certificates preventing them from validating communications with Belkin’s cloud service including the firmware update RSS feed. This allows attackers to use any SSL certificate to impersonate Belkin’s cloud services and push malicious firmware updates and capture credentials at the same time. Due to the cloud integration, the firmware update is pushed to the victim’s home regardless of which paired device receives the update notification or its physical location.
The Internet communication infrastructure used to communicate Belkin WeMo devices is based on an abused protocol that was designed for use by Voice over Internet Protocol (VoIP) services to bypass firewall or NAT restrictions. It does this in a way that compromises all WeMo devices security by creating a virtual WeMo darknet where all WeMo devices can be connected to directly; and, with some limited guessing of a ‘secret number’, controlled even without the firmware update attack.
There does not appear to be anyone or anything attacking these vulnerabilities — yet. But from where I sit, the scariest part of these flaws is Belkin’s apparent silence and inaction in response to IOActive’s research. Indeed, according to a related advisory released today by Carnegie Mellon University’s Software Engineering Institute, Belkin has not responded with any type of solution or workaround for the identified flaws, even though it was first notified about them back in October 2013. So be forewarned: Belkin’s WeMo products may allow you to control your home electronics from afar, but you may not be the only one in control of them.
Update, 10:24 p.m. ET: Belkin has responded with a statement saying that it was in contact with the security researchers prior to the publication of the advisory, and, as of February 18, had already issued fixes for each of the noted potential vulnerabilities via in-app notifications and updates. Belkin notes that users with the most recent firmware release (version 3949) are not at risk for malicious firmware attacks or remote control or monitoring of WeMo devices from unauthorized devices. Belkin urges such users to download the latest app from the App Store (version 1.4.1) or Google Play Store (version 1.2.1) and then upgrade the firmware version through the app.
Original story:
NETWORK ATTACKED STORAGE
As evidenced by the above-mentioned ASUS and Linksys vulnerabilities, an increasing number of Internet users are taking advantage of the remote access features of routers and network-attached storage (NAS) devices to remotely access their files, photos and music. But poking a hole in your network to accommodate remote access to NAS systems can endanger your internal network and data if and when new vulnerabilities are discovered in these devices.
One popular vendor of NAS devices — Synology — recently alerted users to a security update that fixes a vulnerability for which there has been a public exploit since December that allows attackers to remotely compromise the machines. A number of Synology users recently have been complaining that the CPUs on their devices were consistently maxing out at 100 percent usage. One user said he traced the problem back to software that intruders had left behind on his Synology RackStation device which turned his entire network storage array into a giant apparatus for mining Bitcoins.
According to an advisory that Synology emailed Monday to registered users, among the many not-to-subtle signs of a compromised NAS include:
- An automatically created shared folder with the name “startup”, or a non-Synology folder appearing under the path of “/root/PWNED”
- Files with meaningless names exist under the path of “/usr/syno/synoman”
- Non-Synology script files, such as “S99p.sh”, appear under the path of “/usr/syno/etc/rc.d”
Synology urges customers with hardware exhibiting the above-mentioned behavior to follow the instructions here and re-install the disk station management software on the devices, being sure to upgrade to the latest version. For users who haven’t encountered problems yet, Synology recommends updating to the latest version, using the device’s built-in update mechanism.
SYMANTEC ENDPOINT INFECTION?
Although not strictly hardware-related, other recent vulnerability discoveries also to be filed under the “Hey, I thought this stuff was supposed to protect my network!” department is new research on several serious security holes in Symantec Endpoint Protection Manager — a host-based intrusion protection system and anti-malware product designed to be used by businesses in search of a centrally-managed solution.
In an advisory issued today, Austrian security firm SEC Consult warned that the flaws would allow attackers “to completely compromise the Endpoint Protection Manager server, as they can gain access at the system and database level. Furthermore attackers can manage all endpoints and possibly deploy attacker-controlled code on endpoints.”
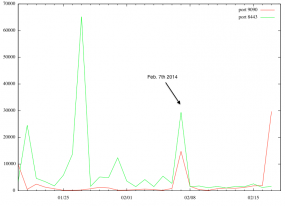
Symantec has released updates to address the vulnerabilities, and probably none too soon: According to the SANS Internet Storm Center, over the past few weeks attackers have been massively scanning the Internet for Symantec Endpoint Protection Management system. SANS’s Johannes B. Ullrich says that activity points to “someone building a target list of vulnerable systems.”
ROUTER FIRMWARE ADVICE, CONT’D
Continuing the discussion from above about alternatives to the stock firmware that ships with most wired/wireless routers, most stock router firmware is fairly clunky and barebones, or else includes undocumented “features” or limitations.
Here’s a relatively minor but extremely frustrating example, and one that I discovered on my own just this past weekend: I helped someone set up a powerful ASUS RT-N66U wireless router, and as part of the setup made sure to change the default router credentials (admin/admin) to something more complex. I tend to use passphrases instead of passwords, so my password was fairly long. However, ASUS’s stock firmware didn’t tell me that it had truncated the password at 16 characters, so that when I went to log in to the device later it would not let me in with the password I thought I’d chosen. Only by working backwards on the 25-character passphrase I’d chosen — eliminating one letter at a time and re-trying the username and password — did I discover that the login page would give an “unauthorized” response if I entered anything more than that the first 16 characters of the password.
Normally when it comes to upgrading router firmware, I tend to steer people away from the manufacturer’s firmware toward alternative, open source alternatives, such as DD-WRT or Tomato. I have long relied on DD-WRT because it with comes with all the bells, whistles and options you could ever want in a router firmware, but it generally keeps those features turned off by default unless you switch them on.
Whether you decide to upgrade the stock firmware to a newer version by the manufacturer, or turn to a third party firmware maker, please take the time to read the documentation before doing anything. Updating an Internet router can be tricky, and doing so demands careful attention; an errant click or failure to follow closely the installation/updating instructions can turn a router into an oversized paperweight in no time.
Update, Feb. 19, 8:10 a.m. ET: Fixed date in Synology exploit timeline.




Great article! You are the Chuck Norris of IT security journalism.
FYI – I know its nit picking but you double up “comes with” in the second last paragraph.
Moon is nothing mate. I’ll see your thousand infections and raise you ten million. PDF search
“Full Disclosure”+”The Adversaries”
So why doesnt the government just seize these sites, look at all the compromised cards and hand them over to the banks? seems like the smart thing to do ? no?