“Bluetana,” a new mobile app that looks for Bluetooth-based payment card skimmers hidden inside gas pumps, is helping police and state employees more rapidly and accurately locate compromised fuel stations across the nation, a study released this week suggests. Data collected in the course of the investigation also reveals some fascinating details that may help explain why these pump skimmers are so lucrative and ubiquitous.
The new app, now being used by agencies in several states, is the brainchild of computer scientists from the University of California San Diego and the University of Illinois Urbana-Champaign, who say they developed the software in tandem with technical input from the U.S. Secret Service (the federal agency most commonly called in to investigate pump skimming rings).
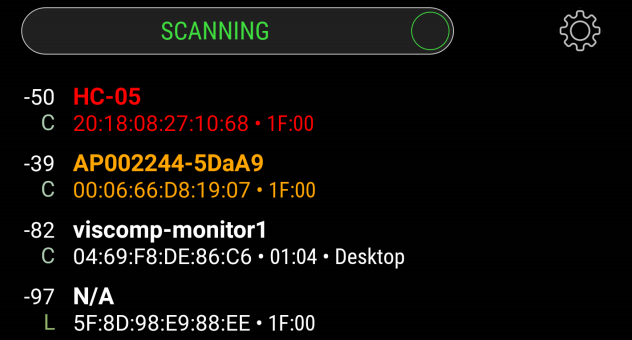
The Bluetooth pump skimmer scanner app ‘Bluetana’ in action.
Gas pumps are a perennial target of skimmer thieves for several reasons. They are usually unattended, and in too many cases a handful of master keys will open a great many pumps at a variety of filling stations.
The skimming devices can then be attached to electronics inside the pumps in a matter of seconds, and because they’re also wired to the pump’s internal power supply the skimmers can operate indefinitely without the need of short-lived batteries.
And increasingly, these pump skimmers are fashioned to relay stolen card data and PINs via Bluetooth wireless technology, meaning the thieves who install them can periodically download stolen card data just by pulling up to a compromised pump and remotely connecting to it from a Bluetooth-enabled mobile device or laptop.
According to the study, some 44 volunteers — mostly law enforcement officials and state employees — were equipped with Bluetana over a year-long experiment to test the effectiveness of the scanning app.
The researchers said their volunteers collected Bluetooth scans at 1,185 gas stations across six states, and that Bluetana detected a total of 64 skimmers across four of those states. All of the skimmers were later collected by law enforcement, including two that were reportedly missed in manual safety inspections of the pumps six months earlier.
While several other Android-based apps designed to find pump skimmers are already available, the researchers said Bluetana was developed with an eye toward eliminating false-positives that some of these other apps can fail to distinguish.
“Bluetooth technology used in these skimmers are also used for legitimate products commonly seen at and near gas stations such as speed-limit signs, weather sensors and fleet tracking systems,” said Nishant Bhaskar, UC San Diego Ph.D. student and principal author of the study. “These products can be mistaken for skimmers by existing detection apps.”
BLACK MARKET VALUE
The fuel skimmer study also helps explain how quickly these hidden devices can generate huge profits for the organized gangs that typically deploy them. The researchers found the skimmers their app found collected data from roughly 20 -25 payment cards each day — evenly distributed between debit and credit cards (although they note estimates from payment fraud prevention companies and the Secret Service that put the average figure closer to 50-100 cards daily per compromised machine).
The academics also studied court documents which revealed that skimmer scammers often are only able to “cashout” stolen cards — either through selling them on the black market or using them for fraudulent purchases — a little less than half of the time. This can result from the skimmers sometimes incorrectly reading card data, daily withdrawal limits, or fraud alerts at the issuing bank.
“Based on the prior figures, we estimate the range of per-day revenue from a skimmer is $4,253 (25 cards per day, cashout of $362 per card, and 47% cashout success rate), and our high end estimate is $63,638 (100 cards per day per day, $1,354 cashout per card, and cashout success rate of 47%),” the study notes.
Not a bad haul either way, considering these skimmers typically cost about $25 to produce.
Those earnings estimates assume an even distribution of credit and debit card use among customers of a compromised pump: The more customers pay with a debit card, the more profitable the whole criminal scheme may become. Armed with your PIN and debit card data, skimmer thieves or those who purchase stolen cards can clone your card and pull money out of your account at an ATM.
“Availability of a PIN code with a stolen debit card in particular, can increase its value five-fold on the black market,” the researchers wrote.
This highlights a warning that KrebsOnSecurity has relayed to readers in many previous stories on pump skimming attacks: Using a debit card at the pump can be way riskier than paying with cash or a credit card.
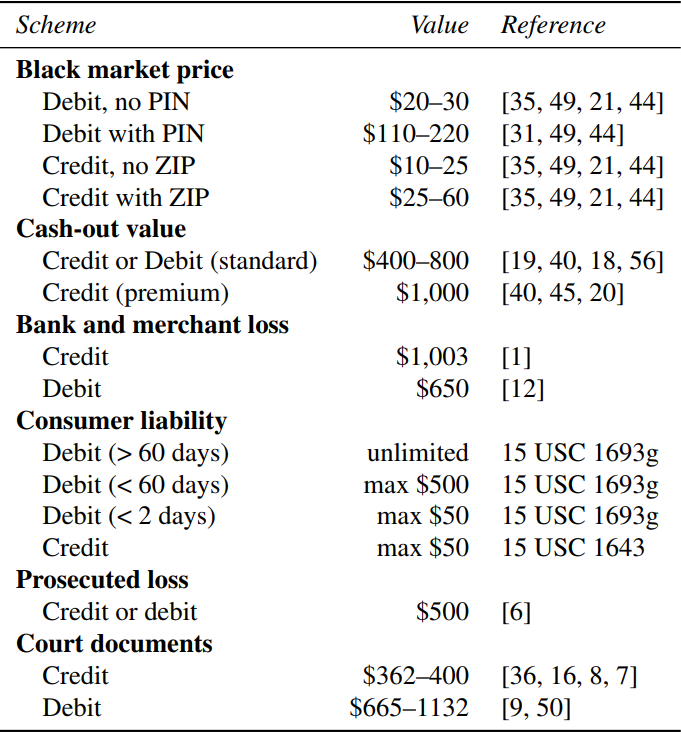
The black market value, impact to consumers and banks, and liability associated with different types of card fraud.
And as the above graphic from the report illustrates, there are different legal protections for fraudulent transactions on debit vs. credit cards. With a credit card, your maximum loss on any transactions you report as fraud is $50; with a debit card, that protection only extends for within two days of the unauthorized transaction. After that, the maximum consumer liability can increase to $500 within 60 days, and to an unlimited amount after 60 days.
In practice, your bank or debit card issuer may still waive additional liabilities, and many do. But even then, having your checking account emptied of cash while your bank sorts out the situation can still be a huge hassle and create secondary problems (bounced checks, for instance).
Interestingly, this advice against using debit cards at the pump often runs counter to the messaging pushed by fuel station owners themselves, many of whom offer lower prices for cash or debit card transactions. That’s because credit card transactions typically are more expensive to process.
For all its skimmer-skewering prowess, Bluetana will not be released to the public. The researchers said the primary reason for this is highlighted in the core findings of the study.
“There are many legitimate devices near gas stations that look exactly like skimmers do in Bluetooth scans,” said UCSD Assistant Professor Aaron Schulman, in an email to KrebsOnSecurity. “Flagging suspicious devices in Bluetana is a only a way of notifying inspectors that they need to gather more data around the gas station to determine if the Bluetooth transmissions appear to be emanating from a device inside of of the pumps. If it does, they can then open the pump door and confirm that the signal strength rises, and begin their visual inspection for the skimmer.”
One of the best tips for avoiding fuel card skimmers is to favor filling stations that have updated security features, such as custom keys for each pump, better compartmentalization of individual components within the machine, and tamper protections that physically shut down a pump if the machine is improperly accessed.
How can you spot a gas station with these updated features, you ask? As noted in last summer’s story, How to Avoid Card Skimmers at the Pumps, these newer-model machines typically feature a horizontal card acceptance slot along with a raised metallic keypad. In contrast, older, less secure pumps usually have a vertical card reader a flat, membrane-based keypad.

Newer, more tamper-resistant fuel pumps include pump-specific key locks, raised metallic keypads, and horizontal card readers.
The researchers will present their work on Bluetana later today at the USENIX Security 2019 conference in Santa Clara, Calif. A copy of their paper is available here (PDF).
If you enjoyed this story, check out my series on all things skimmer-related: All About Skimmers. Looking for more information on fuel pump skimming? Have a look at some of these stories.


It seems the “best”/most secure dispensers are from Gilbarco/Veeder Root. I’ve found it’s easy to identify those on the dispenser right below the fuel grade buttons. Look for those and it seems quick to determine which to use. YMMV
Gilbarco and Wayne have a duopoly on the dispenser market. Almost all of the Gilbarco dispensers which are old can be easily skimmed.
Shell also has a nice app where you can pay with your phone and the transaction is all within the app (not Bluetooth, not NFC). Pull up to the pump, enter in your pump number in the app, confirm the code on the screen. At least that way, it’s not using your card at the actual pump so there’s a lower risk there too.
The Costco near me has the new pumps, security tape in multiple locations on the pump, and most importantly, an employee who almost constantly walks around the fueling area. I’d buy my gas there even if it wasn’t less expensive than the Valero across the street.
Is the mobile app available for download?
From the article…
“For all its skimmer-skewering prowess, Bluetana will not be released to the public. The researchers said they the primary reason for this is highlighted in the core findings of the study.
“There are many legitimate devices near gas stations that look exactly like skimmers do in Bluetooth scans,” said UCSD Assistant Professor Aaron Schulman, in an email to KrebsOnSecurity.”
So, no.
From Brian’s post:
For all its skimmer-skewering prowess, Bluetana will not be released to the public. The researchers said they the primary reason for this is highlighted in the core findings of the study.
This seems rather short sided on the surface. If everyone could check before they put their card in it would prevent a lot more loss than the present approach ever will. It seems that, as always, the authorities are not really concerned about preventing the public from getting ripped off. They are more concerned about their own priorities of being able to publicize finding the skimmers. The fallacy in that is that there is no way they can keep up with the constant attempts of skimmers, many of which will just return in the future to re-attack detected pumps.
In point of fact this device will do the public very little good the way it is being used.
Not really short sighted but practical.
Bluetana seems to be effective only when narrowing down. The operator needs to be able to open the dispenser and confirm… otherwise, too many false positives.
This tool, in the hands of the public, may only incite panic and loss of business, because people will see tons of false positives.
Also, having this tool available to the public will accelerate the evolution of the attackers. Custom identifiers and switching to BLE are two cheap/easy ways to completely thwart Bluetana… and attackers won’t bother until they truly fear it.
There are other tools available that do the very same thing which are already public. Releasing this tool to the public will have a minor effect on that.
I see where you’re coming from, but that makes no sense if you think about it. Why create a tool like this–to serve the public–that won’t be used by the public? Who would be the one driving to every gas station and scanning with that one app? The logistics make no sense. Also, how are they publishing this data to the public for us to know which pumps to avoid? Seems as though it would be much easier to just release it to the public.
I get that… But this tool isn’t really for that purpose. The white paper is the product. It is more a tool to identify the scope of the problem, not to try and solve the problem.
Sounds weird, but it is common to see a tool (physical or code) designed purely for academic or research purposes. The white paper does reflect this purpose.
Also, many tools are designed to be use by people who have direct access to the equipment…. not consumers. It may be considered a tool that is only really effective in the hands of those servicing the dispensers.
I’d like to have it too, but if everyone had access to it the miscreants who create the skimming hardware (who may not be the ones who install them in retail pumps) would also, and could find it much easier to modify their hardware designs to avoid detection and stay well ahead of the app’s developers in catching up.
Limiting its availability to key regulators and relevant security professionals will significantly enhance their ability to detect skimmer installations in the field more quickly (thus greater coverage and response capability with more effective/efficient use of their time and resources) while retarding miscreant designers’ capability to purvey an undetectable version of their hardware.
There is an app called Skimmer Scanner on Google’s app store that use’s bluetooth to look for common skimmer hardware. It’s existed for a couple of years now.
Is there an IOS version?
Skimmer Scanner doesn’t appear anymore on the Google app store. I have it installed, but it seems to have been removed from the App Store. It also hadn’t been updated for quite a while.
There are, however, a bunch more BT scanner apps on there.
I still don’t understand why, when new pumps are installed, they still lack chip readers or contactless payment terminals. In 2019. I can’t help but feel that the (American) payments industry miscalculated in the timing of their transition away from magnetic stripes.
Same reason why they don’t enable the door and tamper alarms with auto shut-off that come standard in most of the new pumps-convenience and/or laziness. They just DGAF… it isn’t their money, so until the individual state’s regulating agencies and legislatures get involved, like Florida and some other states finally are, nothing will be done at the vendor level. We just hitting over 4800 pumps at over 500 stations in 3 parishes last week and only 1 vendor had the alarms/cut-offs enabled that I am aware of.
It’s really about who owns the loss in a fraud which is determined by payment card rules. This is from Visa:
Visa has been working with merchants, acquirers, and fuel-industry providers to support migration to the more secure EMV technology. However, due to challenges with EMV Automated Fuel Dispensers (AFD) solution readiness, Visa is delaying the U.S. domestic AFD EMV liability shift date to 1 October 2020.
And, while they’re delaying it to 2020, I’d be willing to bet it still won’t be widely used for at least 3-5 more years. I work in the hospitality industry as a vendor and there still aren’t that many EMV readers available where I am, and it’s been 2+ years now, almost, since the liability shift.
I still think in the US that NFC will be a more readily available solution. That way you don’t even need to swipe an actual card. Just pull your phone out and use a one-time token or another stand-in for your actual card number.
NFC also includes newer credit cards, not just phones. My recent credit card has NFC. I use NFC wherever I can, instead of either swipe or chip reader.
From RandomOracle – Compatibility of CVC1 and CVC3, 2012
The magnetic-stripe profile of certain EMV payment protocols such as Paypass produces data in a format similar to what swiping a traditional plastic card might yield. This backwards compatibility has undeniable advantages for transitioning to the more advanced protocols. For example, point-of-sale terminals can have an NFC capability added as bolt-on accessory, without altering the transaction further downstream.
The downside of this seamless transition is that there is no strict firewall separating NFC payments with dynamic CVV3 from swipe-transactions that rely on static CVV1 for authorization. It is possible, albeit inconvenient, to encode NFC transaction data on a plain card and use it at a regular point-of-sale terminal. This explains the replay demonstration that Kristin Padgett performed at Shmoocon in January in 2012. Intended to prove the ease of skimming information from contactless credit cards, this stunt actually serves as an unintended proof of the interchangeability of CVV1 and CVV3. The researcher executed one round of the payment protocol between a hypothetical victim’s contactless plastic card and an NFC reader controlled by the researcher. This transaction does not actually cause any money to exchange hands. It is never reported to the payment network. It is only used to record the transcript of the protocol. (This is the often hyped “skimming” part: in the US many cards have no additional protection such as PIN required to complete the transaction, unlike in Europe where it is common to have PIN entry above certain transaction threshold.) The transcript is then used to construct track data, encoded on a plastic card and swiped through a Square reader, to conduct the actual “fraudulent” transaction.
NFC still exposes the same card data as the magnetic swipe. NFC has the ‘ability’ to also do encryption (like Yubikey NEO)… but unless they stop exposing the full CC data… it’s a liability to use it on a credit card.
Try it with a free app for Android called “Credit Card Reader” by devnied in France.
Surprisingly, some NFC EMV cards store transaction history on the card itself. Yes, there is a list of your transactions that is unencrypted and available to any NFC scanner.
That is SO MUCH WORSE than a magnetic stripe skimmer. DO NOT USE NFC!
I specifically try to buy gas at gas stations that use NFC. Just tap your card, no PIN required below $100 here in Canada! Of course your card must be a chip card to get the additional security! The added benefit of NFC can be that some card use a different PAN (card number) for NFC transactions. Marking the transaction as NFC (card entry mode) is part of the authorization data.
The problem with gas pumps, especially in the US, is they are quite outdated, and many use old equipment that would not be allowed in a retail store. Implementing E2EE or P2PE between the device and the acquirer would also eliminate all this skimming.
All that is great… but you have to make sure there is no ability to “fallback”. Because that is the huge problem. EMV, Chip and PIN, etc… are all great, but if there is an ability to fallback, the skimmer will still work.
If you’ve ever seen a terminal without a working chip reader, and the cashier instead swiped… it has Fallback capability. There is unencrypted data that can be cloned, and purchases can be made with that cloned card.
NFC is like chip and pin, in that is has a lot of security built in. But scan it with devnied’s app or something similar, on a newer Android, and you’ll see the data. You might even see an unencrypted list of your transactions.
I prefer using the actually chip, because at least I don’t have to insert the card all the way into a reader… so not risking a magnetic stripe read. With NFC, the same interface that will use encrypted data, can also be used to skim the unencrypted data.
There are two types of fallback:
1) fallback from TAP to insert 2) fallback from insert to MSR swipe
The first one happens when you exceed the no CVM amount limit. This rarely happens, since it is high enough to fill a big tank with gas. So you are still safe. Typically this is automatic.
The second one occurs on insert chip read errors. It is now your choice to proceed, or use another card.
For the merchant it is a business decision; they can leave it automatic, but a lot of merchants turn this off because it is a main area of fraught.
Note that new rules from the card brands now mandate that if the insert reader is chip, the CTLS reader must also be chip. But in oil and gas (pay at the pump) the companies are still dragging their heels (and allowed to do so)
Apply proper E2EE or P2PE technology at the pump, and the whole skimming issue goes away!
PS: For a chip read you cannot partially insert your card. That does not work! If the card reader works properly it will actually lock your card until you enter your pin (which is what I want to avoid – which is why I TAP)
Not to mention the plethora of stores you walk into that over the last couple years installed EMV/swipe readers but still haven’t actually activated the chip reader or if they have it’s “dysfunctional” every other day “chip card error please swipe card”
Or you can just shove your library card in the chip slot 3 times and that’ll tell you to swipe too.. It all comes down to it basically seeming like not many merchants care.. And even if they do, there isn’t enough being done to inform their cashiers or attendants of what signs to look for in a typical attempted fraudulent TX. It takes 2 minutes to print out an geographic and tape it up in the employee lounge or behind the counter.. *facepalm.. Life goes on.
As always good job Krebs!
While I agree that a number of gas station operators will miss the October 20 liability shift deadline primarily due to their belief that the significant cost of upgrading their equipment (as well as the petroleum industry’s certification requirements and limited personnel to conduct such certifications), they will soon be the target of massive first party fraud. This is where the cardholder did the transaction but then disputes the transaction knowing the card brand regulations that their card issuer will simply charge back the disputed item to the merchant using the “no chip card” chargeback rule and the merchant has little to no recourse. This is has become a problem in the casual and fine dining industry with customers having expensive meals and leaving generous tips and then disputing the charges so the restaurant takes the loss.
Matthew, many gas pumps do use chip readers. They just have to be enabled. The Kroger stations I frequent recently posted signs on their pumps that you now need to insert your card and leave it in the slot until directed on the display to remove it. This is a change from the old insert/remove “swipe-style” operation.
hey they putting stickers on the pumps here that say secure on the reader and if removed says tampered… im sure no clever crook could ever come up with a sticker 😉
Another great read !
Regulators need to do more than just confiscate the skimmer HW. They need to shut the station down and force the station to improve security before they can reopen. Yes, I know that the station can also be considered a victim of the skimmers, but franchised station operators will NEVER spend a dime on upgrades unless they are forced to. In addition, shutting the station down (and also shutting down the % of sales that goes to the franchisor) will also put pressure on the parent brand (Exxon, Mobil, Shell, etc) to implement security upgrade programs that are affordable for their franchisees. Nothing makes a national brand move faster than something that interferes with their revenue stream.
I have 30+ years in the retail petroleum industry.
Most skimmers we find are not blue tooth but a simple device that is connected to the card reader inside the pump. Consumers should look for a pump with a gas pump alarm installed. These station owners have taken an extra step to protect customers.
Aaannd…. how do we identify these alarms?
Gas pump alarms are available. Due to the fact that a UL listing is required for installation into a fuel dispenser. It does raise the cost .
Usually gas station owners, that have gone that extra mile, will have a label on the outside of the pump informing the customer of an alarm. Putting a label on the dispenser without the actual alarm would be a bad idea. That would really piss people off when their card gets skimmed.
Bluetooth skimmers are also simple devices. How do you know that the devices you are finding do not have bluetooth capabilities? Do not assume that just because they have a microSD card, that it isn’t bluetooth.
Without wireless, criminals have to go back and reopen the dispensers, continuously putting themselves at risk. So unless you are finding these devices when criminals return and setting off alarms… they probably DO have bluetooth. You just may not recognize it.
The article mentions Android. I’m assuming the app will be available on iOS as well, right?
No, it won’t. From the researchers: “It is only available on Android. The Bluetooth scanning API in iOS only shows classic Bluetooth devices that are authorized to pair with Apple devices. Most Bluetooth-to-serial devices have not been authorized to pair with iOS (although they can pair with MacOS).”
This would explain why, when I went to Mexico a few years ago to do that story on the bluetooth skimmers behind hidden inside ATMs by the cash machine technicians, my iPhone couldn’t detect any of them. I had to buy a cheapo Huawei phone from a local Telcel store before I could find any of them.
https://krebsonsecurity.com/2015/09/tracking-a-bluetooth-skimmer-gang-in-mexico/
I ran across a station that is using chip readers that has vertical card acceptance slots. Apparently, nothing is absolute.
Hi Brian, you can find an App called “Skim Plus” on android. Bluetana looks like a copy…
Hi guys, you can buy it for 1.99$. The App is good and able to ignore false positives (legitimate bluetooth). Scanning rogue devices everywhere will also help the police.
Btw, skimming devices dont contact their c&c with bluetooth anymore. Skimmers are using GSM for evasion.
Cheers
The paper talks about GSM:
GSM poses a more serious challenge for detection.
Cost to attacker:
While using GSM would avoid detection using Bluetana, it creates an additional trail of evidence link-ing the perpetrator to the skimmer. Law enforcement officers could obtain information about the SMS recipient through subpoenas, so receiving the SMS messages on another phone on a US carrier, for example, would be easy to trace. The perpetrator would need to use an SMS service that would not expose his/her identity.
Response: In addition to legal tools available to law en-forcement to trace SMS messages, a GSM modem could be detected using a Software-Defined Radio.
“Modem could be detected using a Software-Defined Radio”
Do you really think that they are able to make a difference between 2 frequencies when using a Software-Defined Radio lol ?
Law enforcement are not Mr. Robot.
False positives a problem? I believe there is a form of step-attenuator built into cell phones which could probably be coded to eliminate distant interference.
I have some experience with this issue, so maybe I can help. Yes, the older style pumps are the ones targeted by thieves, almost exclusively, older Gilbarco models. Practically, you can identify an older model by the pin pad, as they will be flat with a plastic cover. Raised buttons on a pin pad means encryption at the pin pad itself, versus the old style where the encryption happens at the motherboard.
And yes, there are a lot of dispensers out there with universal locks/keys, but even with site specific locks/keys those older style dispenser doors are easily pried open to gain access to the internal card reader and Crind Board.
The increase in skimmer activity is due to several reasons, but the main reasons are the EMV deadline and new tactics by the criminals. The EMV shift is the driving force, because the thieves know their game will be up soon. That forced them to change tactics, which included Bluetooth chips, and now GSM chips. Additionally, the thieves now install the device deeper inside the dispenser on the Crind Board vs the Card Reader. The switch in placement combined with the new connectivity options make it extremely hard to catch at the store level. Hell, I have seen them hard wire a skimmer in a card reader and replace the entire card reader with their own compromised one.
All that said, the company I work for is moving to EMV, we are replacing dispensers, or retrofitting them with kits. Before too long, all our dispensers will be alarmed, encrypted, contactless(if you choose), and EMV ready. I would imagine other companies will follow suit. So these Bluetooth apps are late to the game, and as Androweed mentioned, the devices are already shifting to GSM.
Hope this helps to some degree…
The paper talks about GSM:
GSM poses a more serious challenge for detection.
Cost to attacker:
While using GSM would avoid detection using Bluetana, it creates an additional trail of evidence linking the perpetrator to the skimmer. Law enforcement officers could obtain information about the SMS recipient through subpoenas, so receiving the SMS messages on another phone on a US carrier, for example, would be easy to trace. The perpetrator would need to use an SMS service that would not expose his/her identity.
Response: In addition to legal tools available to law en-forcement to trace SMS messages, a GSM modem could be detected using a Software-Defined Radio.
—-
Be careful with “contactless” using NFC. Although it can be encrypted… there is still a lot of card data that is exposed unencrypted to any skimmer that also on the reader. Pretty much all the data available on magnetic stripe, is also available via NFC.
Some cards even store transaction data on the card itself. There are free apps (devnied) that scan credit cards for this info.
Contactless is a convenience feature… and although encryption can be used… it can be a false sense of security, as downgrading to unencrypted is possible. At least with Chip and PIN, the card isn’t inserted far enough to read the unencrypted mag stripe data. With NFC contactless… it is all the same interface. Dangerous.
Most mobile NFC signals don’t broadcast much further than 5-8 millimeters. That makes it hard to skim. The data you can skim from NFC is not enough to complete a transaction. You’d need to get the dynamic CVV number correct. The dynamic CVV number changes every time the card is read.
You are not correct. Skimmers can have better RF gain, because they are designed to skim, not be used as intended.
Placing a higher gain NFC receiver a few centimeters behind the real reader is trivial. And while they are there, they could even potentially place their skimmer in front and reflect or relay the signal to the real reader.
You are also wrong about the dynamic cvv. This skimmer is not designed to clone the entire card, complete with full NFC capability. But rather to clone the static, unencrypted data that would be available on the static mag stripe.
As I said, there IS encryption in the NFC process, but there is fallback information that can be used to clone a generic mag stripe card.
CVV1 is static unencrypted data on the mag stripe. A mag stripe skimmer will get CVV1. That’s the situation described in this post. A skimmer is not going to get CVV1 from a NFC transaction. A NFC skimmer might get a lot of card data, but not a useful CVV.
There are certainly still merchants that will complete a transaction without a CVV, but that number is dwindling.
How is this different from Sparkfun’s Skimmer Scanner app?
$25 to buy the skimmer hardware? Obviously not all gangs are competent at building a circuit out of junk, or they wouldn’t be paying that much! Of course if they are using GSM, they may have to pay for an account on a burner phone, perhaps.
Pay for a burner phone? Nope. Phones, clothes, food, gas, everything is basically free to thieves who use stolen credit card data.
EMV fallback makes all this possible and no one seems to care enough to do anything about it.
True – they can just use stolen credit card information to buy what they want using our good names.
Yeah, the extra cost may be easy for them, since they are making more than enough to justify… but there is extra risk even with a burner phone.
It opens up a whole path for investigators. The burner phones receiving the SMS messages from the GSM skimmers, get turned on… and the cellular towers can triangulate the position. So law enforcement can potentially trace or at least determine location trends.
If not using SMS, attackers will need data plans to send messages. This is higher cost, but the receiver won’t have to be a cell phone at all.
Pardon my ignorance here, but they receive the credit card details via SMS (obviously not in all cases)? That’s interesting and doesn’t sound too smart to me. Though, the smart thing would be for them to get a real job, I guess… It seems to me that method makes it hard to cover their tracks–to which I say, good! I’ve had to replace my debit card before due to this and it’s not fun. Luckily my bank spotted it quick enough, cancelled my card, and sent a new one in the mail right away.
There’s a Chevron station nearby that takes Apple Pay at the pump: just hold your iPhone by the wireless-pay logo and use your fingerprint, faceID or passcode on your iPhone to pay. Then select the credit button on the pump itself and that’s it.
It won’t matter if that pump has a skimmer and/or infected payment computers because Apple Pay hides pertinent info. And if you use your fingerprint or faceid on your iPhone, rogue video cameras won’t have a chance to see you type your iPhone passcode.
Since a skimmer at a closer 76 Station recently got my card, I usually drive to that Chevron to use Apple Pay.
I’ve never seen ApplePay at another station, though.
The most telling point in this article is contained by the paragraph beginning with the words “The fuel skimmer study also helps explain… .”
Namely, the fraud prevention industry and Secret Service both report **four times more** cards being skimmed than were actually being skimmed in this sample.
What can be deduced is that the people who make a living off preventing fraud are liars who inflate a problem to ensure their continued employment.
“What will be the ‘true’ tipping point that causes people to actually, fully & completely, stop carrying ANY amount of nationstate-issued paper (i.e greenbacks, euros, renminbi, rupee, yen) around on their person as an insurance/fallback gap in their daily transactional life”?
I still feel forced to carry, in spite of not wanting to, I still feel forced. Yup. I am a carrier. Of what, anymore, I am not sure.
Interesting, as usual.
But, has anyone checked the settings on Bluetooth, and or used just one of the free connection managers on their phone? Apparently not. Some have an effective map. Some just read range and strength. Some show it as a radar. You don’t always need a law enforcement tool for your safety. Secondly, they operate on a burst transmission for the better hidden ones, do not look for a constant carrier wave. After all, that would show a presence. After all, some people keep their Bluetooth on, a bad idea, by was busted into the day it arrived in your phones. And thirdly, just because a pump has security tape on it, doesn’t mean it’s clean, or if it’s new, even new stuff could be unclean, you don’t know who may have put it there.
I agree with this statement, “so until the individual state’s regulating agencies and legislatures get involved, like Florida and some other states finally are, nothing will be done at the vendor level”. Having daily or weekly manditory checks would be helpful but that’s not going to happen until the stations are required to. I typically use only two different gas stations Costco for their security stickers and mostly Speedway because they are the first in my area to process chip.
Forty-four volunteers scanned fewer that 1,200 gas stations in a year. That seems pretty underwhelming. Was the purpose a POC on the technology or to actually find and disable compromised pumps?
The purpose was not to find all the bad.
It was a POC, and it is more than enough of a sample size to get good metrics for the tool and statistics on the larger scope of the problem.
“Interestingly, this advice against using debit cards at the pump often runs counter to the messaging pushed by fuel station owners themselves, many of whom offer lower prices for cash or debit card transactions. That’s because credit card transactions typically are more expensive to process.”
It also shifts the liability to recover off the banks and on the individual. That is why Chip and Pin was preferred over Chip and Signature. Easier to fake a signature. More liability on the end user if the PIN was stolen as well. Banks and stores love to shift the costs to a consumer.
Did the same thing last year with a Pi3 and Ubertooth One. It was obvious why the Android apps failed because they had hardcoded device names like HC-05 but skimmers come from various manufacturers and advertise differently. Very important to find the ones that are hidden and not broadcasting at all. It’s also way better to “Skimmer Drive” at night to eliminate false positives. I think this story will make the bad guys rename their devices to Suzy’s iPhone 8 or something.
Scroll to bottom > September 27th to see a pic.
https://detsec.org/calendar
Suzy’s Iphone, perhaps. Probably more like “FBI Surveillance Van #23” or something like VZW32F3, like all the WiFi access points installed by cable companies.
I do not understand why the USA is still 10 years behind.
Those “new” keypad/readers are what the banks are using on their 10+ years old XP based ATMs. That is the lowest acceptable security standard for any unattended payment terminal.
Gas stations around here usually supports contactless, and for 5+ years, everything has been chip&pin. No cardreaders. Everything is P2PE or equivalent. No way for stores to get access to a cardnumber
How can those insecure solutions even be PCI certified ?
Why is the US so far behind ? I see contactless as the biggest step forward in many years, if it is secure.
I know! I’ve not seen someone use the magnetic strip on a credit or debit card anywhere in Europe for at least 15 years. Even tiny, independent shops owned and run by one old lady have contactless, or at least chip & PIN. If anyone ever asked be to swipe my card at any shop, I’d be walking straight out of the door.
I wonder if the PCI compliance rules are different in the US – or if just hardly anywhere is compliant? Scary,
The problem is fallback. Encryption can be flawless, but if there is a backward compatibility requirement that drives the need… then people will choose convenience every time.
PCI is the bare minimum… and meeting it, is not considered good security. PCI compliance must be exceeded to even be considered secure.
Contactless is NOT a security feature. It is a convenience feature. And like before, it will lead to a false sense of security.
Although it can be encrypted… there is still a lot of card data that is exposed unencrypted to any skimmer that also on the reader. Pretty much all the data available on magnetic stripe, is also available via NFC.
Some cards even store transaction data on the card itself. There are free apps (devnied) that scan credit cards for this info.
Contactless is a convenience feature… and although encryption can be used… it can be a false sense of security, as downgrading to unencrypted is possible. At least with Chip and PIN, the card isn’t inserted far enough to read the unencrypted mag stripe data. With NFC contactless… it is all the same interface. Dangerous.
This! I’ve travelled all over the Europe, and even in the tiniest, one-old-man, shops in the most remote parts of Europa, I’ve never had to swipe my card. It’s always been Chip & PIN – and in most cases contactless.
The US is decades behind, not just a few years. I am 28 and I can’t remember anyone using the magnetic strip on the back of a card in my adult life.
I wonder if the PCI compliance rules are different over there, or are they just not compliant?
The state of California is implementing (or has implemented?) compliance for private consumer data called California Consumer Privacy Act (CCPA). However, as of right now, this is really only at the state level and does not have the impact like GDPR has. US-based companies that have clients or consumers in Europe do fall under GDPR, but we ourselves do not have a regulation other than CCPA–at least to my knowledge.
Where is “around here”?
Both my credit card supplier (Citibank Visa) and credit union offer zero liability for credit (Citibank) and debit (credit union) card misuse. Additionally, both offer instant sms notification for any transaction over a customer selected limit. When I use my credit card I normally get a text within a few seconds identifying the amount and the merchant. I have a credit union debit card but only use it to get cash POS at a single merchant (Walmart). Again, the transaction is texted to me within seconds. Citibank also monitors for suspicious transactions. On the one occasion when my credit card was compromised I got a call within minutes saying my card had been used in my Georgia home town (legitimate) and in Chicago a few minutes later. They had already cancelled the card.
It’s so bizarre when I visit the US.
Back home in the UK contactless is normal, Apple Pay and Google Pay are absolutely normal, so normal I don’t even bother carrying any cards at all, I use my Apple Watch for all but one thing I buy.
So when I visit the US and it’s suddenly swiping cards, signatures, and then the odd place that has chip reader seems to bypass the PIN bit, and ask you to sign anyhow, it’s very bizarre and slow and backward. I’ve managed to use contactless via Apple Pay a few times in the US but mostly it’s either not working, not understood or some other issue exists. Contactless seems to work OK in any Starbucks or a McDonalds, but that’s about the only “norm” I see there. It’s slightly better than it was, but it’s so frustrating going back in time to pay for stuff there.
I don’t really understand why the US hasn’t just moved forwards in so many years.
To add to the advantage of paying with NFC; Use Apple Pay or Google Pay; They don’t actually use your PAN, but a one time token instead.
This is indeed more secure than the alternative. It just sucks we have to add yet another big corporations in the middle of our transactions.
At least the banks are regulated.
Apple and Google do good security. But now there are privacy concerns. Apple is much better than Google here too.
Google is tracking all purchases and selling data to advertisers. Even purchases without Google Pay, if you merely get a receipt to your GMail address… they scan it and use it.
Use your contactless (NFC) credit card is as secure as Apple Pay and Google Pay, and does not require you to carry the powered device. For more details on contactless EMV card, read this resource
https://www.uspaymentsforum.org/wp-content/uploads/2019/03/Debunking-EMV-Myths-March-2019.pdf
It answers these common questions regarding chip technology:
Does EMV chip technology eliminate all payments fraud?
Do chip card transactions use encryption?
How does chip technology impact fraud liability between the merchant and issuer, and is the consumer ever liable?
Is the use of a PIN necessary for chip technology to be effective?
How has the implementation of chip technology impacted card-not-present (CNP) fraud?
Can a thief electronically pickpocket your contactless card or device and create a counterfeit card that can be used successfully in stores?
Can contactless card information be stolen and used to steal a consumer’s identity?
Are fraudsters able to create usable counterfeit cards through shimming?
The folks at Sparkfun created a skimmer app. I don’t know if they’ve updated it lately.
https://learn.sparkfun.com/tutorials/gas-pump-skimmers/all
Just a few days ago the card reader at a gas pump was acting unusual. I fired up the skimmer app and sure enough, there was a skimmer on the pump. It took quite an argument with the filling station operator to get them to do anything. I had to threaten to call the police, if they didn’t.
the ‘Skimmer Scanner’ from SparkX. does not seem to be available on GooglePlay at the moment.
Why dont they install an “alarm” system on the pump, if the door is opened, it phones home and needs to correlate with a work order. Maybe they can nab a bad service person that is installing them. Its not like you need to open these things up each day. Who looks for a seal before they pump gas? I just want to get out of there before I get physically robbed.
There’s a Chevron station nearby that takes Apple Pay at the pump: just hold your iPhone by the wireless-pay logo and use your fingerprint, faceID or passcode on your iPhone to pay. Then select the credit button on the pump itself and that’s it.
It won’t matter if that pump has a skimmer and/or infected payment computers because Apple Pay hides pertinent info. And if you use your fingerprint or faceid on your iPhone, rogue video cameras won’t have a chance to see you type your iPhone passcode.