Security experts are poring over thousands of new Coronavirus-themed domain names registered each day, but this often manual effort struggles to keep pace with the flood of domains invoking the virus to promote malware and phishing sites, as well as non-existent healthcare products and charities. As a result, domain name registrars are under increasing pressure to do more to combat scams and misinformation during the COVID-19 pandemic.
By most measures, the volume of new domain registrations that include the words “Coronavirus” or “Covid” has closely tracked the spread of the deadly virus. The Cyber Threat Coalition (CTC), a group of several thousand security experts volunteering their time to fight COVID-related criminal activity online, recently published data showing the rapid rise in new domains began in the last week of February, around the same time the Centers for Disease Control began publicly warning that a severe global pandemic was probably inevitable.
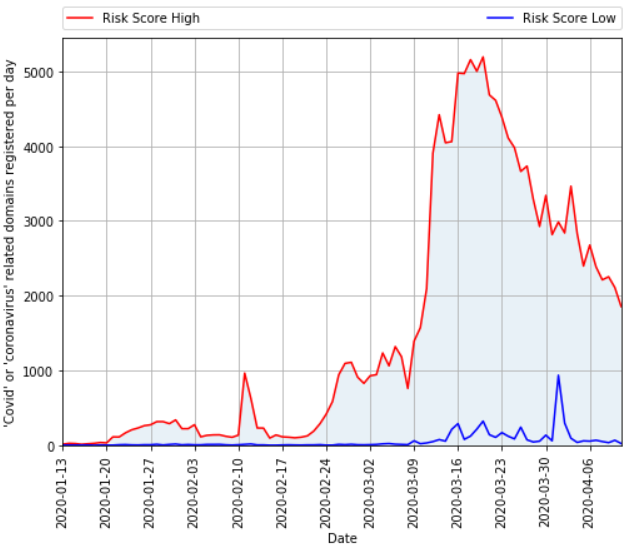
The total number of domains registered per day that contain a COVID-19 related term, according to DomainTools. The red line indicates the count of domains that DomainTools determined are “likely malicious.” The blue line refers to domains that are likely benign.
“Since March 20th, the number of risky domains registered per day has been decreasing, with a notable spike around March 30th,” wrote John Conwell, principal data scientist at DomainTools [an advertiser on this site]. “Interestingly, legitimate organizations creating domains in response to the COVID-19 crisis were several weeks behind the curve from threat actors trying to take advantage of this situation. This is a pattern DomainTools hasn’t seen before in other crises.”
Security vendor Sophos looked at telemetry from customer endpoints to illustrate the number of new COVID-related domains that actually received traffic of late. As the company noted, one challenge in identifying potentially malicious domains is that many of them can sit dormant for days or weeks before being used for anything.
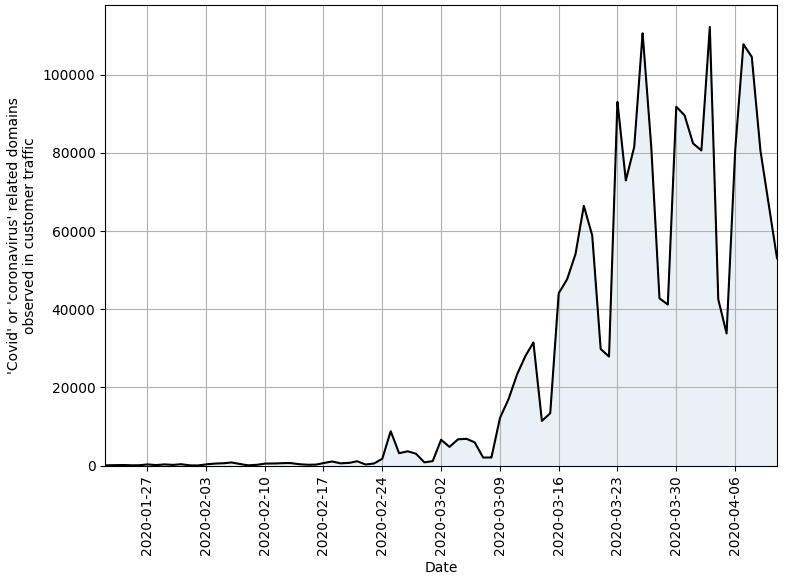
Data from security vendor Sophos, published by the Cyber Threat Coalition, shows the number of Coronavirus or COVID-19 themed domains registered per week that received traffic.
“We can see a rapid and dramatic increase of visits to potentially malicious domains exploiting the Coronavirus pandemic week over week, beginning in late February,” wrote Sophos’ Rich Harang. “Even though still a minority of cyber threats use the pandemic as a lure, some of these new domains will eventually be used for malicious purposes.”
CTC spokesman Nick Espinosa said the first spike in visits was on February 25, when group members saw about 4,000 visits to the sites they were tracking.
“The following two weeks starting on March 9 saw rapid growth, and from March 23 onwards we’re seeing between 75,000 to 130,000 visits per weekday, and about 40,000 on the weekends,” Espinosa said. “Looking at the data collected, the pattern of visits are highest on Monday and Friday, and the lowest visit count is on the weekend. Our data shows that there were virtually no customer hits on COVID-related domains prior to February 23.”
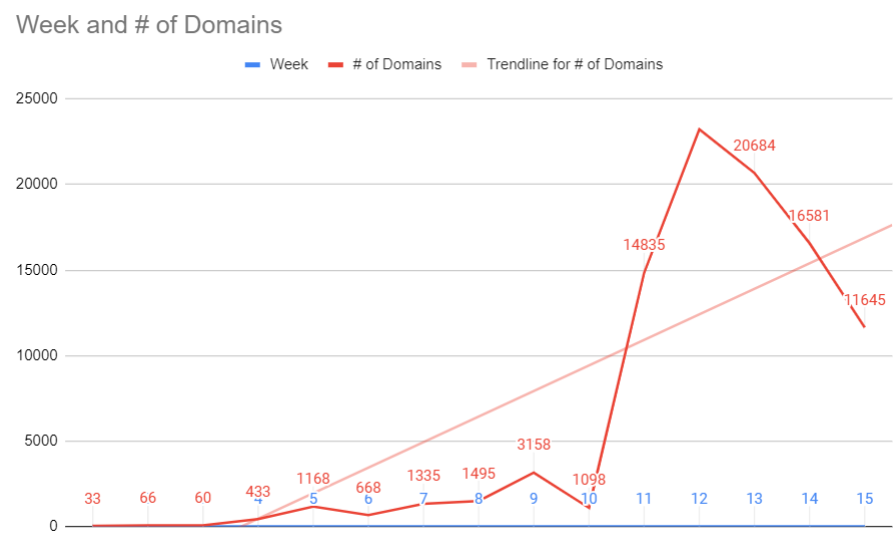
Milwaukee-based Hold Security has been publishing daily and weekly lists of all COVID-19 related domain registrations (without any scoring assigned). Here’s a graph KrebsOnSecurity put together based on that data set, which also shows a massive spike in new domain registrations in the third week of March, trailing off considerably over the past couple of weeks.
Not everyone is convinced we’re measuring the right things, or that the current measurements are accurate. Neil Schwartzman, executive director of the anti-spam group CAUCE, said he believes DomainTool’s estimates on the percentage of new COVID/Coronavirus-themed domains that are malicious are too high, and that many are likely benign and registered by well-meaning people seeking to share news or their own thoughts about the outbreak.
“But there’s the rub,” he said. “Bad guys get to hide amidst the good really effectively, so each one needs to be reviewed on its own. And that’s a substantial amount of work.”
At the same time, Schwartzman said, focusing purely on domains may obscure the true size and scope of the overall threat. That’s because scammers very often will establish multiple subdomains for each domain, meaning that a single COVID-related new domain registration could eventually be tied to a number of different scammy or malicious sites.
Subdomains can not only make phishing domains appear more legitimate, but they also tend to lengthen the domain so that key parts of it get pushed off the URL bar in mobile browsers.
To that end, he said, it makes perhaps the most sense to focus on new domain registrations that have encryption certificates tied to them, since the issuance of an SSL certificate for a domain is usually a sign that it is about to be put to use. As noted in previous stories here, roughly 75 percent of all phishing sites now have the padlock (start with “https://”), mainly because the major Web browsers display security alerts on sites that don’t.
Schwartzman said more domain registrars should follow the example of Los Angeles-based Namecheap Inc., which last month pledged to stop accepting the automated registration of website names that include words or phrases tied to the COVID-19 pandemic. Since then, a handful of other registrars have said they plan to manually review all such registrations going forward.
The Internet Corporation for Assigned Names and Numbers (ICANN), the organization that oversees the registrar industry, recently sent a letter urging registrars to be more proactive, but stopped short of mandating any specific actions.
Schwartzman called ICANN’s response “weak tea.”
“It’s absolutely ludicrous that ICANN hasn’t stepped up, and they will bear significant responsibility for any deaths that may happen as a result of all this,” Schwartzman said. “This is a CYA response at best, and dictates to no one that they should do anything.”
Michael Daniel, president of the Cyber Threat Alliance — a cybersecurity industry group that’s also been working to fight COVID-19 related fraud — agreed, saying more pressure needs to be applied to the registrar community.
“It’s really hard to do anything about this unless the registrars step up and do something on their own,” Daniel said. “It’s either that or the government gets involved. That doesn’t mean some [registrars] aren’t doing what they can, but in general what the industry is doing is nowhere near as fast as the bad guys are generating these domains.”
The U.S. government may well soon get more involved. Earlier this week, Senators Cory Booker (D-N.J.), Maggie Hassan (D-N.H.) and Mazie K. Hirono (D-Hawaii) sent letters to eight domain name company leaders, demanding to know what they were doing to combat the threat of malicious domains, and urging them to do more.
“As cybercriminals and other malevolent actors seek to take advantage of the Coronavirus pandemic, it is critical that domain name registrars like yours (1) exercise diligence and ensure that only legitimate organizations can register Coronavirus-related domain names and domain names referencing online communications platforms; (2) act quickly to suspend, cancel, or terminate registrations for domains that are involved in unlawful or harmful activity; and (3) cooperate with law enforcement to help bring to justice cybercriminals profiting from the Coronavirus pandemic,” the senators wrote.



I registered azcovidtxt.org though Amazon Web Services DNS service for a public health project for the University of Arizona and found it was almost immediately blacklisted by the OpenDNS name servers. Fortunately the security folks at the University of Arizona were able to whitelist that domain, but until then any Cisco Umbrella customers (including the University of Arizona!) couldn’t see that site.
It could be that the university is using a feature of OpenDNS that looks at ‘newly created domains’ and is blocking them until they gain reputation. We use this setting for our clients because it helps protect them.
It has been already a week since I noticed that some antivirus vendors automatically add domains with COVID keyword as phishing to the database. Particularly Fortinet does this.
I’d rather keep ICANN out of this. It’s really not their place to be deciding what domains should and shouldn’t be allowed.
I didn’t hear anyone suggesting ICANN should be any kind of per-domain arbiter, but rather that they do something other than pay lip service to the problem.
This latest response by ICANN is laughable, as is the idea that this is a new problem. With each local and global disaster, a handful of well-meaning domain registrations sit amongst the overwhelming majority of malicious ones registered. And whether the disaster is local, regional, or global, the abuse is profound and most often causes harm to those impacted by the disaster and those that want to somehow help. Let’s try not to be surprised when the next 911, Katrina, or Fukushima strikes and that both the security and the ICANN community are caught flat-footed by the level of malicious activity. Now is the time to consider how the ICANN community can anticipate the next disaster and implement a policy that governs how registrars can swiftly react.
In the last two weeks, I differently seen a increase in spam going into my “honey pot ” account. No domain names related to Covid-19 yet, just fake China made facial masks be sold. I just gets links going to malware or spam written in foreign languages
I hadn’t expected to see Namecheap setting a good example. I’ve had some pretty frustrating experiences with their place when trying to avenge clients who’d been victimized by tech support scams. Maybe I’ll have to re-evaluate.
To be clear, they made the change only after getting sued by the Justice Department: https://abcnews.go.com/Technology/wireStory/internet-firm-restricts-virus-themed-website-registrations-69825166
“Los Angeles-based Namecheap Inc. made the pledge after a federal judge in Texas ordered the takedown of a website the U.S. Department of Justice accused of stealing credit card information while offering fake coronavirus vaccine kits. The website allegedly offered what it claimed were World Health Organization vaccine kits in exchange for a $4.95 “shipping charge.”
Totally agreed. Namecheap is a horrible service. And it is not LA based. It’s based either in Ukraine or Russia. They just have an office in US. There’s a big difference there, Brian.
I’m with Schwartzman on this. If it’s not centrally-managed, it cannot be managed, and the potential for new fraud, beyond existing, is significant.
Nip it in the bud before it becomes a greater challenge. As central authority, ICANN is the place to start.
This is consistent with what we’ve seen. Also useful to note at the DNS level: The overload of newly registered fraudulent domains is causing lots of legitimate domains to be tagged inappropriately, especially when there is little or no content to start. We suggest existing organizations do NOT register new domain names, especially with certain keywords, and re-use their existing trusted domain properties for distribution of information.
https://www.quad9.net/help-my-new-covid-19-site-is-getting-blocked/
JT
Organizations like yours are colluding to deny free commerce to legitimate companies. We will be filing a FTC complaint immediately.
Watch out Brian, Talking to a Lawyer is on your case. LOL
Scams are every where. Many companies claim to be U.S.A. Based but then a foreign trans action fee is added and the payments go to questionable sites. Example I ordered a thermometer supposedly from a U.S.A. based company, but the payment went to an clothing store in Hong Kong. Bank of America in a recording on their fraud line says if you made the charge it will not be removed and you are also stuck with the foreign transaction fee, Also they sent a notice with my monthly statement to that effect dated after the date I made that charge. I paid but if I do not get what I ordered, I will write them a letter.
I’m not sure where my previous comment went ….
What I was saying is that Namecheap should not be lumped into “good guys.” I’ve had tons of bad experiences with them myself and heard similar references from other people. They do anything from luring ppl in with cheap prices and then auto-charging their cards on new rates, to having no easy ways of closing the account, to upselling on TLS certs and not allowing free Let’s Encrypt. You name it … and the list goes on.
And they are not LA based, Brian. They are based either in Ukraine or Russian, and just have an office here in US.
…the cto is from ukraine…says it all…
…the cto is from ukraine…that’s all you need to know…
Netcraft (no affilliation) has incorporated Covid-19 scam pages in its browser extension for Chrome/FireFox browsers.
Regards,
I believe the Netcraft browser extension has incorporated PROTECTION AGAINST Covid-19 scam pages. They aren’t delivering the scams.
Unless you know something different, Robert.
Neil Schwartzman is right with his comment on measuring the right things, as we are not measuring the right things.
We looked at the number of COVID/Corona registrations on our registrar platform and 62% of the registrants were already a registrant of non-corona/COVID related domain names prior to 1 November 2019.
85% of the registrations are parked.
I suspect when we would really drill down on the registrant data 62% is most likely 72-80%.
Judging all the COVID/Corona related domain names as potential malicious results in people chasing down issues that are not there. Focusing efforts on the actual incident response will yield more and better results.
Criminals already stepped up their game and use more generic domain names now for COVID related scams, malware and whatever.
I think this is hum … not your best article … Brian. Don’t be fooled by so-called security experts that just (also) want to monetize this horrible situation. Most of the new registrations are done by gold diggers. People that like to speculate. Some do it on the stock market, some to it on the domain name market.
The quality of those blocklists/blacklists is just poor. Those so-called security experts shoot first, then ask. That’s not the way it works this side of the ocean.
The challenge for registars is trying to identify good vs. bad intentions of new domains. Is it their job to do that? I don’t know, maybe. Continuing to work closely with the cybersecurity community and improve feeback loops so bad domains can be brought down quickly is probably best option.
When they come for us to chip us like dogs, resist at all costs.
Have you seen what it’s like out there, Murray? Do you ever actually leave the studio? Everybody just yells and screams at each other. Nobody’s civil anymore. Nobody thinks what it’s like to be the other guy. You think men like Thomas Wayne ever think what it’s like to be someone like me? To be somebody but themselves? They don’t. They think that we’ll just sit there and take it, like good little boys! That we won’t werewolf and go wild!
Am volunteer mentor with Score Some clients who have applied for EIDL are getting email responses from an sba.gov address which is slightly different than the official address. Is SBA switching email addresses??? Bad practice…yes? Known good address has been disastercustomerservice@sba.gov but some responses are coming from DisasterCustomerService3@sba.gov Moreover, the email response states: “You will receive an email invitation to create a portal that will provide you with the agency’s determination on your loan request. You may also provide additional information/corrected information if necessary.” Advising client to proceed with extreme caution & to inspect the email header details and the URL as it appears in browser window. Would appreciate more advice from Krebs.
In every situation tech guys wanna have their profit. This time there is no difference at all
Kudos on a balanced article.
We’ve known for a long time that NRD (Newly Registered Domains) are essentially not trustworthy. Palo Alto Networks recommends blocking domains < 30 days old.
Covid-19 NRD take the issue to a new level.
Agree, changes in governance and policies are necessary to move the needle.
From Covid-19 NRD data from zone files for the week of April 5-11, it looks like Namecheap had ~ 180 new Covid-19 domains; GoDaddy ~ 4,800. Some of these are legit, or at least not unambiguously sketchy or evil, but the vast majority are parked. And I could still find some names that Namecheap registered, that if not sketchy were close to it.
Both GoDaddy and Namecheap, and probably all others, still encourage registration of Covid-19 domains. If you try to register a name, their recommendation engines gladly try to get you to register like-named domains if the requested domains is taken, cross-sell you to additional TLDs, and up-sell you to names they consider to be 'premium' Covid-19 names.
We realy don’t need any more covid themed sites anyway. The best of the best info has been available on established educational/research, government, and media sites worldwide since the start of the epidemic.
On the other hand, if one wants to get rich by selling bleach, hydrogen peroxide, natural “cures”, etc. at a huge markup, then I guess one needs a covid related domain.
There is some good news, judging from that graph we have at least flattened the curve on domain registrations.
In every situation tech guys wanna have their profit. This time there is no difference at all
This is a fantastic leap that Namecheap has taken. It is commendable.
Time and again, among domainers on NamePros as well as other forums and a number of other occasions, Namecheap(if I am not mistaken here) has been highlighted as the place where many of the stolen domain names would be transferred.
It looks like they have indeed taken a big step and set a precedence for others to follow. Really happy about this.
At the same time, this could be a good solution, coming from registrars. Every event which is a bit different invites cybercriminals. No one, but a registrar can help control it.
“…but the site’s WHOIS registration records (obscured since the Reddit thread went viral) point to an individual living in Florida.” Hah! Florida Man again, I knew it! Crossposting now to /r/floridaman