One of the digital underground’s most popular stores for peddling stolen credit card information began selling a batch of more than three million new card records this week. KrebsOnSecurity has learned the data was stolen in a lengthy data breach at more than 100 Dickey’s Barbeque Restaurant locations around the country.
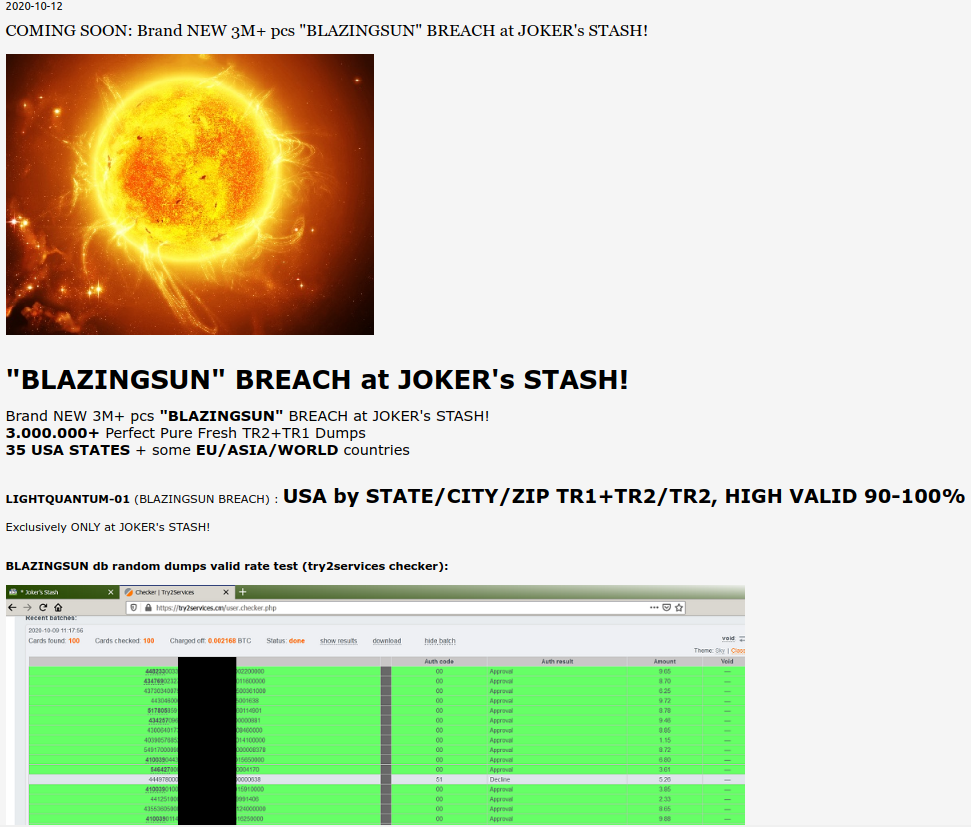
An ad on the popular carding site Joker’s Stash for “BlazingSun,” which fraud experts have traced back to a card breach at Dickey’s BBQ.
On Monday, the carding bazaar Joker’s Stash debuted “BlazingSun,” a new batch of more than three million stolen card records, advertising “valid rates” of between 90-100 percent. This is typically an indicator that the breached merchant is either unaware of the compromise or has only just begun responding to it.
Multiple companies that track the sale in stolen payment card data say they have confirmed with card-issuing financial institutions that the accounts for sale in the BlazingSun batch have one common theme: All were used at various Dickey’s BBQ locations over the past 13-15 months.
KrebsOnSecurity first contacted Dallas-based Dickey’s on Oct. 13. Today, the company shared a statement saying it was aware of a possible payment card security incident at some of its eateries:
“We received a report indicating that a payment card security incident may have occurred. We are taking this incident very seriously and immediately initiated our response protocol and an investigation is underway. We are currently focused on determining the locations affected and time frames involved. We are utilizing the experience of third parties who have helped other restaurants address similar issues and also working with the FBI and payment card networks. We understand that payment card network rules generally provide that individuals who timely report unauthorized charges to the bank that issued their card are not responsible for those charges.”
The confirmations came from Miami-based Q6 Cyber and Gemini Advisory in New York City.
Q6Cyber CEO Eli Dominitz said the breach appears to extend from May 2019 through September 2020.
“The financial institutions we’ve been working with have already seen a significant amount of fraud related to these cards,” Dominitz said.
Gemini says its data indicated some 156 Dickey’s locations across 30 states likely had payment systems compromised by card-stealing malware, with the highest exposure in California and Arizona. Gemini puts the exposure window between July 2019 and August 2020.

“Low-and-slow” aptly describes the card breach at Dickie’s, which persisted for at least 13 months.
With the threat from ransomware attacks grabbing all the headlines, it may be tempting to assume plain old credit card thieves have moved on to more lucrative endeavors. Alas, cybercrime bazaars like Joker’s Stash have continued plying their trade, undeterred by a push from the credit card associations to encourage more merchants to install credit card readers that require more secure chip-based payment cards.
That’s because there are countless restaurants — usually franchise locations of an established eatery chain — that are left to decide for themselves whether and how quickly they should make the upgrades necessary to dip the chip versus swipe the stripe.
“Dickey’s operates on a franchise model, which often allows each location to dictate the type of point-of-sale (POS) device and processors that they utilize,” Gemini wrote in a blog post about the incident. “However, given the widespread nature of the breach, the exposure may be linked to a breach of the single central processor, which was leveraged by over a quarter of all Dickey’s locations.”
While there have been sporadic reports about criminals compromising chip-based payment systems used by merchants in the U.S., the vast majority of the payment card data for sale in the cybercrime underground is stolen from merchants who are still swiping chip-based cards.
This isn’t conjecture; relatively recent data from the stolen card shops themselves bear this out. In July, KrebsOnSecurity wrote about an analysis by researchers at New York University, which looked at patterns surrounding more than 19 million stolen payment cards that were exposed after the hacking of BriansClub, a top competitor to the Joker’s Stash carding shop.
The NYU researchers found BriansClub earned close to $104 million in gross revenue from 2015 to early 2019, and listed over 19 million unique card numbers for sale. Around 97% of the inventory was stolen magnetic stripe data, commonly used to produce counterfeit cards for in-person payments.
Visa and MasterCard instituted new rules in October 2015 that put retailers on the hook for all of the losses associated with counterfeit card fraud tied to breaches if they haven’t implemented chip-based card readers and enforced the dipping of the chip when a customer presents a chip-based card.
Dominitz said he never imagined back in 2015 when he founded Q6Cyber that we would still be seeing so many merchants dealing with magstripe-based data breaches.
“Five years ago I did not expect we would be in this position today with card fraud,” he said. “You’d think the industry in general would have made a bigger dent in this underground economy a while ago.”
Tired of having your credit card re-issued and updating your payment records at countless e-commerce sites every time some restaurant you frequent has a breach? Here’s a radical idea: Next time you visit an eatery (okay, if that ever happens again post-COVID, etc), ask them if they use chip-based card readers. If not, consider taking your business elsewhere.




Another radical idea: if you just HAVE to have that BBQ (or whatever your favorite eatery serves), use ca$h. One mode that hackers can’t touch. Yet.
Or, walk in, tell ’em you were about to place a huge order, but when you saw they’re so behind-the-times, you changed your mind.
Since the banks won’t hold their merchants to the simplest of security standards, it appears it’s still every man (or woman) for himself.
Sad, isn’t it…
Armed robbery is the original form of hacking. Burglary soon followed. Both have benefitted from technological advances and face technological defenses.
Unlike cash, a credit card can have fraudulent activity unwound. If someone robs you and gets away from you, you’re out the cash (and maybe your life) with no recourse.
Unlike cash, a card is merely a reference to currency. If it is destroyed in a fire, you call to get a replacement. No value is lost. Cash burned in a fire is value lost forever.
People who say that cash is secure have never had much of it to worry about.
Another radical idea: don’t carry that much cash around. And, BTW, while I have never been robbed, I HAVE been the victim of credit card fraud.
Card scams happen what, maybe 5000% more often than muggings? likely more.
300 in my wallet most of the time, always use cash at restaurants and other places that don’t have budget for high security, or that I just don’t trust enough.
Even if I get mugged once (unlikely), it will still have cost me less than dealing with the burden of CC/ID theft.
Each (cash/cards) have their place and time.
And where do we get our cash these days? Especially with banks closing offices or reducing hours? That’s right, the ATM–which is quite hackable and requires use of a card with less legal protection than a credit card. I still carry cash, but most of the bills in my wallet are the same ones that were in there in March.
As for ATMs, use an ATM only card, NOT a debit card.
You can still get them, but the bank will try to discourage you. [at one bank the service rep at a desk told me that AMT cards don’t exist anymore – when I stated that I am closing my accounts and going to another bank that does have them, the manager (who was nearby) came over and ordered the ATM card for me. The manager mentioned that only a handful of customers had ever asked for an ATM card.]
[While stolen ATM card info can be used to make a fake card, using it is more time consuming and riskier for the scammer. Using credit and debit card info is safer and easier.]
As with any card, only use the bank’s machines in more secure locations.
You need to do a article on the breach at Barnes and Noble !
Diddos with the first comment.
Cash = Anonymous, Safe
The 4% credit card charge need to go toward my favorite BBQ, Indian or Thai restaurant.
We need to keep the ability to use cash.
https://www.cbsnews.com/news/kroger-coin-shortage-no-change/
I’d like to push back the Patriot Act requirements for government to gather intel on all our bank accounts, without a warrant.
And, we need to stop civil asset forfeiture, but I digress.
https://pulitzercenter.org/reporting/no-drugs-no-crime-and-just-pennies-school-how-police-use-civil-asset-forfeiture
keep the drumbeat going Keith, make ’em listen
Sadly people are begging to live under a 1984 style dictatorship, where everything you do is tracked and monitored, where freedom of speech doesn’t exist. All because some terrorist might harm a few people somewhere and it makes the news, we must surrender everything and go back to gulags. Nowadays, if you say something wrong, they erase you from history like the Soviets did to Leon Trotsky (just look at what fedbook, google, etc do if you go against the narrative). Now under the corona mania, people are begging to be locked down even further than the patriot act could ever hope for. The chip will come soon, mark my words, and it will be mandatory (the current path of mandatory vaccines can and will be used to justify the mandatory chip). You can call it conspiracy theory, I don’t give a mother ****. It was a conspiracy that the NSA was spying on everyone, too, the truth shall be revealed.
I’m not surprised at all that stores like this haven’t caught up. The economy is hanging by a thread in these times of COVID-19. They delay modernization for the sake of a limited budget. I sympathize for Ma and Pa businesses, some of which are franchise owners, and not all are particularly filthy rich.
The US economy is the largest in the world, only China comes second! It is a wonder the US has shifted to Chip-N-PIN as fast as it has, in my opinion. I do some of my business by direct bank to bank transfer; and the criminals have learned to do that on a limited bases too, by using a PayPal account they control to attack any account numbers listed in various other types of breaches.
Sorry,but chip card systems were available long before Covid!
Cash can’t be hacked or tracked!
Well, I mean, it CAN be hacked.
It just requires a more meatspace hacking methodology.
We used to call that “muggings”.
As for ‘untrackable’, well, not really sure who that’s benefiting. Particularly after being mugged…
Cash can be tracked. Ever seen a dye canister explode in a bag of cash from a bank robbery? Also, tracking of serial numbers happens all the time.
“meatspace”, really? hacking is exclusively digital. Robbing or mugging someone is not hacking in any way shape or form, its simply robbery. Stop trying to intentionally complicate reality.
Yes. Really.
It’s not exactly a revolutionary concept either.
Unless of course you’re trying to tell me that Social Engineering- which occurs mostly in meatspace- isn’t hacking, or isn’t regarded as such, broadly speaking.
In any case, you’d still be missing the point, even if right. The reason there’s so much going on these days in terms of cybercrime is because that is where the money went.
Years ago, they used to rob people because that’s where the money was. Then it moved to banks… because that’s where the money was.
The point is: Advocating a return to cash isn’t really a solution.
Franchisees have been telling Dickeys corporate for years that they needed to upgrade their card security to chip and pin. They force the payment system on their owners, they refused to listen even when we constantly had stolen cards used at our stores.
Although the card holder may not be liable, what Dickey’s forgets to mention is that if they still accept non-chip transactions they will be held liable!! Or their franchise holder will be! Plus the card issuers may bill them for the card replacement and other cost they incurred for their non-compliance. Making then rue the delays in upgrading their POS systems and payment terminals.
Really, the transition should have been mandated by law with “no longer able to accept cards” being the penalty for missing the deadline. Of course, with the usual caveat of the deadline being far enough in the future such that merchants actually have time. (For instance, I suspect the networks should have moved the 2015 liability shift to at least 2017 or so given that it took that long for a significant number of major merchants to accept chip in the first place.) That said, I don’t think there was ever political will to implement such a mandate, so my suggestion might not have been (or will ever be) realistic.
BTW, if you want to put your money where your mouth is, make sure the place you’re visiting is on https://emvacceptedhere.com/. (Disclaimer: it’s my site.) Or add it if it’s not already there, that’s appreciated too!
I rather let myself to be frauded scammed and usually banks reinburse 100%
But nobody Don’t like violant crimes specially in USA there is so peacful because thugs are well feed and well dressed from all Kind of fraud actvities.
Imagine if there is no fraud?
We would need bodyguards
It must be confusing to write a piece on chip and pin and then have so many correspondents talk about cash. Cash is just inconvenient to obtain, carry and pass to suppliers.
Then others suggest Moms and Pops can’t afford a new card reader. A reader and dock, which accepts contactless, chip and pin, Apple and Google Pay costs about $150 (ask Amazon or eBay). Who can’t afford $150 for a piece of equipment that will last for five years and the rest.
Come-on, stop kidding.
“You’d think the industry in general would have made a bigger dent in this underground economy a while ago.”
Well, I mean, the things you have to ask are:
1. Is it actually costing “The Industry” anything?
And here I don’t mean regular costs, like cyber insurance or anything like that. I mean have they experienced a sudden, out-of-band loss of some sort as a result of this?
If ‘no’ then why should they care?
2. Are the consumers/customers asking for better security measures? Are they actively avoiding merchants that don’t provide this kind of security?
This is an easier one. I’ve never had to go very far in any given week or month to find someone in a checkout line complaining about chipped cards (and new things in general).
That this is a measure undertaken for their own good is never a consideration, or even a conception, I suspect.
Put that all together and ask yourself: what incentive does “The Industry” have precisely to move quickly and decisively on this?
Q15: What are the penalties for non-compliance?
A: The payment brands may, at their discretion, fine an acquiring bank $5,000 to $100,000 per month for PCI compliance violations. The banks will most likely pass this fine along until it eventually hits the merchant. Furthermore, the bank will also most likely either terminate your relationship or increase transaction fees. Penalties are not openly discussed nor widely publicized, but they can be catastrophic to a small business. It is important to be familiar with your merchant account agreement, which should outline your exposure
https://www.pcicomplianceguide.org/faq/#15
It starts with money. When profit margins are low, the
small business cannot pay these fines.
The credit card machine we used, had encryption point to point. When big companies store this data in the clear (which is probably what happened) that maybe where the breach occured.
Cherry keyboards can read the card data in the clear, and that is a PCI compliance issue. Been there, done that, thanks to an IT guy that didn’t want to use up to date software.
PCI compliance fails again.
“It starts with money. When profit margins are low, the
small business cannot pay these fines.”
So, some years back (and while the company I was working for was under different management) we had our first fire drill in what I conjure to be close to 6-7 years since I had arrived there.
Putting aside how abysmal that sounds from a safety perspective, an evac plan was developed, posted in multiple locations, and now we were running our first drill and gathering out on the lawn in our designated muster points.
As I’m out there, I hear a shrill, loud voice exclaiming “I don’t even know why we’re doing this! If this building lit on fire, it’d just burn. We’d be done.”
And I turned around to look at the person who had uttered this insanity and saw… the company’s CEO.
See you say “There’s a penalty. It’s in the Law.”
And then they say “That only matters if I get caught.”
Then you say “If you get caught, it’s all over for you.”
And they say “So? Then it’s over. That’s it. Who cares?”
I guess what I’m trying to say is, this was one of those “small companies”. The intent of the law is of course to create an existential threat.
But what it fails to account for is just how nihilistic companies like that can be when backed against a wall.
The company you worked for must have been bigger than the company I worked for….At it’s peak in 1991, total number of employees was 11…4 were owners of the LLC.
When the boss closed down the retail location in 2018, only 2 of us were left: he was the owner, and I worked for him for 34 years. The cost of doing business with Amazon buying and selling against you, is not worth it anymore.
Their BBQ is only OK. Their franchisee in San Antonio apparently went out of business because their web site no longer shows any locations there.
The last time I was at one of their locations was 2+ years ago and they were only doing swipes at that time.
One of the problems with this whole Covid-19 thing, is that a large majority of business are not taking Cash because of the money “handling” and potential for spreading the virus… DOH!
I love your work but its complicate to see myself all this website
3M should have stayed in their lane making Scotch brand tape and Post-it Notes instead of wandering off into flammable credit cards
Simple way to fix this problem is that the card issuers need to remove the magstripe from all credit and debit cards issued and force all transactions to be completed either by the “dip the chip” method or the rfid “touchless” method. And no other. Eliminate the magstripe and eliminate the possibility of fraud. Or at least greatly reduce the chances that it might happen.
But of course, since the card issuers have made sure that the merchant will pay for the fraud instead of them then that will never happen.
I can’t remember when was the last time I had to use a swipe only eftpos machine. We (Australia) stopped using them years ago.
The providers only supplied tap’n’go, problem solved.
So if the magstripe is still such a problem with fraud why do the card issuers still put them on the back of the credit and debit cards. They should simply eliminate this obsolete entry method on the cards (credit and debit) altogether and go strictly to EMV chip entry and/or RFID contactless entry as methods of payment. End of problem. Easy peezy.
Phasing out mag stripes is taking longer than it needed to, and would improve card security for sure.
(Btw, payment cards use NFC – which is an active system – rather than the passive and unsecure RFID.)
Sorry, the “it’s taken us too long” excuse isn’t flying here. If the card issuers were truly worried about magstripe fraud then they’d simply remove the magstripe (or leave it blank) and be done with it. But since they’ve all managed to move liability from themselves to their clients in the great chip migration. So nothing is going to change. The card issuers have no reason to change it and therefore won’t. (I bet they’d do just that toot sweet if they were still held responsible for magstripe card fraud. But they aren’t so nothing will happen.)
(Btw, I’ve seen both credit cards and debit cars equipped with both EMV chips and RFID chips. And the RFID chip reads more reliably than the EMV chip. Every time.)
Issuers haven’t moved liability to their clients, what on earth are you talking about?
Visa/MC/Discover and Amex all have zero dollar liability for fraud, Reg E has 60 days on Debit and Reg Z/FCBI has 60 days for Credit cards.
The issuers haven’t taken off mag stripes (YET) because too many consumers would go to another issuer. We can decline more transactions that are processed as a Mag Stripe, and you’ll start seeing that as soon as Gas Stations migrate to Chip (Maybe March? They are good at whining to Visa/MC so maybe not)
Carrying cash is not the answer. Businesses need to make sure that their equipment is secure and updated to a certain level. There are too many businesses that are too lackadaisical with their security measures and hackers are able to get in and get out because of it.
Another extreme thought: in the event that you simply HAVE to have that BBQ (or whatever your #1 diner serves), use ca$h. One mode that programmers can’t contact. However.
https://www.centralprotection.ca/
abc