In 2015, police departments worldwide started finding ATMs compromised with advanced new “shimming” devices made to steal data from chip card transactions. Authorities in the United States and abroad had seized many of these shimmers, but for years couldn’t decrypt the data on the devices. This is a story of ingenuity and happenstance, and how one former Secret Service agent helped crack a code that revealed the contours of a global organized crime ring.
Jeffrey Dant was a special agent at the U.S. Secret Service for 12 years until 2015. After that, Dant served as the global lead for the fraud fusion center at Citi, one of the largest financial institutions in the United States.
Not long after joining Citi, Dant heard from industry colleagues at a bank in Mexico who reported finding one of these shimming devices inside the card acceptance slot of a local ATM. As it happens, KrebsOnSecurity wrote about that particular shimmer back in August 2015.
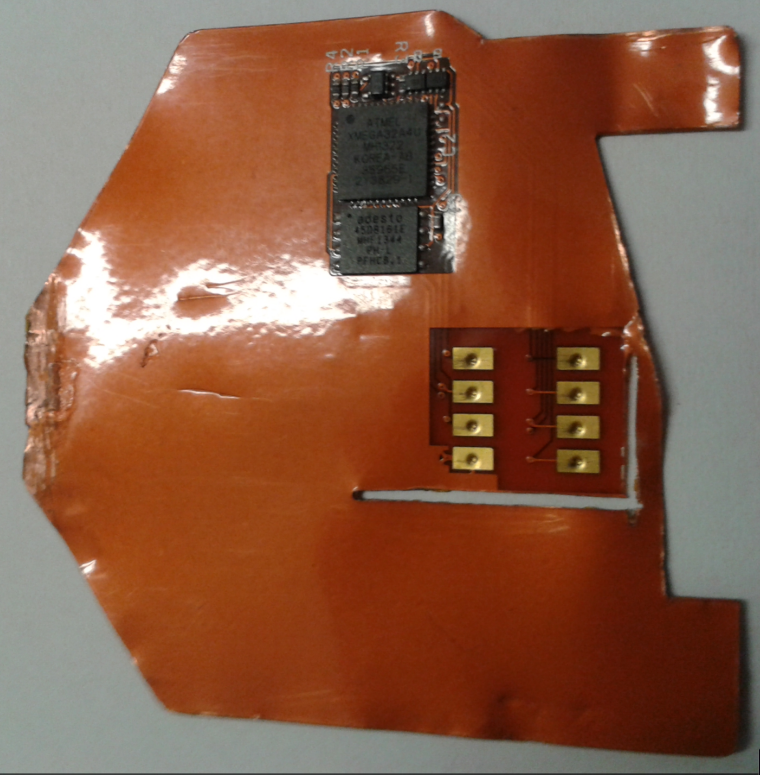
This card ‘shimming’ device is made to read chip-enabled cards and can be inserted directly into the ATM’s card acceptance slot.
The shimmers were an innovation that caused concern on multiple levels. For starters, chip-based payment cards were supposed to be far more expensive and difficult for thieves to copy and clone. But these skimmers took advantage of weaknesses in the way many banks at the time implemented the new chip card standard.
Also, unlike traditional ATM skimmers that run on hidden cell phone batteries, the ATM shimmers found in Mexico did not require any external power source, and thus could remain in operation collecting card data until the device was removed.
When a chip card is inserted, a chip-capable ATM reads the data stored on the smart card by sending an electric current through the chip. Incredibly, these shimmers were able to siphon a small amount of that power (a few milliamps) to record any data transmitted by the card. When the ATM is no longer in use, the skimming device remains dormant, storing the stolen data in an encrypted format.
Dant and other investigators looking into the shimmers didn’t know at the time how the thieves who planted the devices went about gathering the stolen data. Traditional ATM skimmers are either retrieved manually, or they are programmed to transmit the stolen data wirelessly, such as via text message or Bluetooth.
But recall that these shimmers don’t have anywhere near the power needed to transmit data wirelessly, and the flexible shimmers themselves tend to rip apart when retrieved from the mouth of a compromised ATM. So how were the crooks collecting the loot?
“We didn’t know how they were getting the PINs at the time, either,” Dant recalled. “We found out later they were combining the skimmers with old school cameras hidden in fake overhead and side panels on the ATMs.”
Investigators wanted to look at the data stored on the shimmer, but it was encrypted. So they sent it to MasterCard’s forensics lab in the United Kingdom, and to the Secret Service.
“The Secret Service didn’t have any luck with it,” Dant said. “MasterCard in the U.K. was able to understand a little bit at a high level what it was doing, and they confirmed that it was powered by the chip. But the data dump from the shimmer was just encrypted gibberish.”
Organized crime gangs that specialize in deploying skimmers very often will encrypt stolen card data as a way to remove the possibility that any gang members might try to personally siphon and sell the card data in underground markets.
THE DOWNLOAD CARDS
Then in 2017, Dant got a lucky break: Investigators had found a shimming device inside an ATM in New York City, and that device appeared identical to the shimmers found in Mexico two years earlier.
“That was the first one that had showed up in the U.S. at that point,” Dant said.
The Citi team suspected that if they could work backwards from the card data that was known to have been recorded by the skimmers, they might be able to crack the encryption.
“We knew when the shimmer went into the ATM, thanks to closed-circuit television footage,” Dant said. “And we know when that shimmer was discovered. So between that time period of a couple of days, these are the cards that interacted with the skimmer, and so these card numbers are most likely on this device.”
Based off that hunch, MasterCard’s eggheads had success decoding the encrypted gibberish. But they already knew which payment cards had been compromised, so what did investigators stand to gain from breaking the encryption?
According to Dant, this is where things got interesting: They found that the same primary account number (unique 16 digits of the card) was present on the download card and on the shimmers from both New York City and Mexican ATMs.
Further research revealed that account number was tied to a payment card issued years prior by an Austrian bank to a customer who reported never receiving the card in the mail.
“So why is this Austrian bank card number on the download card and two different shimming devices in two different countries, years apart?” Dant said he wondered at the time.
He didn’t have to wait long for an answer. Soon enough, the NYPD brought a case against a group of Romanian men suspected of planting the same shimming devices in both the U.S. and Mexico. Search warrants served against the Romanian defendants turned up multiple copies of the shimmer they’d seized from the compromised ATMs.
“They found an entire ATM skimming lab that had different versions of that shimmer in untrimmed squares of sheet metal,” Dant said. “But what stood out the most was this unique device — the download card.”
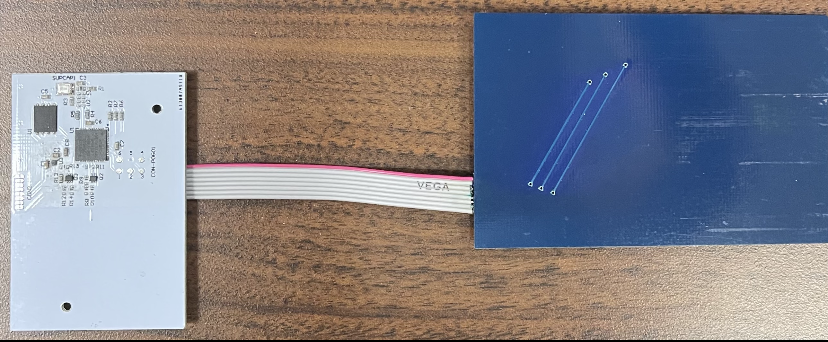
The download card (right, in blue) opens an encrypted session with the shimmer, and then transmits the stolen card data to the attached white plastic device. Image: KrebsOnSecurity.com.
The download card consisted of two pieces of plastic about the width of a debit card but a bit longer. The blue plastic part — made to be inserted into a card reader — features the same contacts as a chip card. The blue plastic was attached via a ribbon cable to a white plastic card with a green LED and other electronic components.
Sticking the blue download card into a chip reader revealed the same Austrian card number seen on the shimming devices. It then became very clear what was happening.
“The download card was hard coded with chip card data on it, so that it could open up an encrypted session with the shimmer,” which also had the same card data, Dant said.
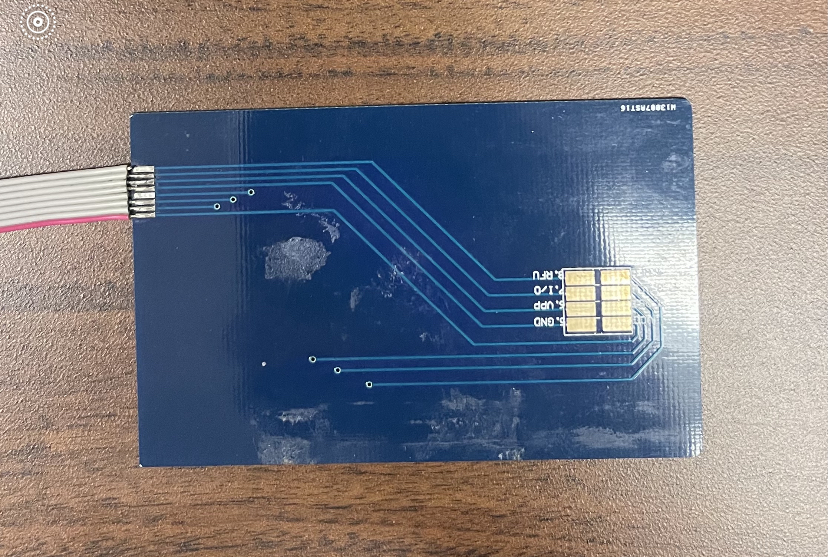
The download card, up close. Image: KrebsOnSecurity.com.
Once inserted into the mouth of ATM card acceptance slot that’s already been retrofitted with one of these shimmers, the download card causes an encrypted data exchange between it and the shimmer. Once that two-way handshake is confirmed, the white device lights up a green LED when the data transfer is complete.
THE MASTER KEY
Dant said when the Romanian crew mass-produced their shimming devices, they did so using the same stolen Austrian bank card number. What this meant was that now the Secret Service and Citi had a master key to discover the same shimming devices installed in other ATMs.
That’s because every time the gang compromised a new ATM, that Austrian account number would traverse the global payment card networks — telling them exactly which ATM had just been hacked.
“We gave that number to the card networks, and they were able to see all the places that card had been used on their networks before,” Dant said. “We also set things up so we got alerts anytime that card number popped up, and we started getting tons of alerts and finding these shimmers all over the world.”
For all their sleuthing, Dant and his colleagues never really saw shimming take off in the United States, at least nowhere near as prevalently as in Mexico, he said.
The problem was that many banks in Mexico and other parts of Latin America had not properly implemented the chip card standard, which meant thieves could use shimmed chip card data to make the equivalent of old magnetic stripe-based card transactions.
By the time the Romanian gang’s shimmers started showing up in New York City, the vast majority of U.S. banks had already properly implemented chip card processing in such a way that the same phony chip card transactions which sailed through Mexican banks would simply fail every time they were tried against U.S. institutions.
“It never took off in the U.S., but this kind of activity went on like wildfire for years in Mexico,” Dant said.
The other reason shimming never emerged as a major threat for U.S. financial institutions is that many ATMs have been upgraded over the past decade so that their card acceptance slots are far slimmer, Dant observed.
“That download card is thicker than a lot of debit cards, so a number of institutions were quick to replace the older card slots with newer hardware that reduced the height of a card slot so that you could maybe get a shimmer and a debit card, but definitely not a shimmer and one of these download cards,” he said.
Shortly after ATM shimmers started showing up at banks in Mexico, KrebsOnSecurity spent four days in Mexico tracing the activities of a Romanian organized crime gang that had very recently started its own ATM company there called Intacash.
Sources told KrebsOnSecurity that the Romanian gang also was paying technicians from competing ATM providers to retrofit cash machines with Bluetooth-based skimmers that hooked directly up to the electronics on the inside. Hooked up to the ATM’s internal power, those skimmers could collect card data indefinitely, and the data could be collected wirelessly with a smart phone.
Follow-up reporting last year by the Organized Crime and Corruption Reporting Project (OCCRP) found Intacash and its associates compromised more than 100 ATMs across Mexico using skimmers that were able to remain in place undetected for years. The OCCRP, which dubbed the Romanian group “The Riviera Maya Gang,” estimates the crime syndicate used cloned card data and stolen PINs to steal more than $1.2 billion from bank accounts of tourists visiting the region.
Last month, Mexican authorities arrested Florian “The Shark” Tudor, Intacash’s boss and the reputed ringleader of the Romanian skimming syndicate. Authorities charged that Tudor’s group also specialized in human trafficking, which allowed them to send gang members to compromise ATMs across the border in the United States.


Nice piece. Good detecting and story weaving. Check the spelling of Roomanian in the second to last para.
Great article
Very interesting!
Btw, in the line above the picture of the download card with shimmer, it says “but” twice in a row
One does not refer to some of the worlds most brilliant experts in card exploitation at Digisec Labs as “eggheads” – seriously?
Egghead in this instance is not being used in a wholy derogatory way. It is typical for some British posters to use the term interchangeably with/similarly to how they use the terminology “boffin”. The Lab being based in the UK would have had British reporting of it in similar fashion. It is not an attempt at slighting anyone so much as it is meant as a tongue-in-cheek reference.
Example:
theregister.co.uk/2021/06/15/mensa_data_breach/
And the regular [interesting] people [likely more in on the being referred to as eggheads than idolized as the “world’s most brilliant experts”] behind it all:
youtu.be/Yqg8VkS8yyc
Fascinating as always!
If the thickness of the download card is the only thing preventing this type of attack, it might already be obsolete. Probably only gang rivalries is what is holding back the next gang from using a scheme which uses a slimmer download card.
It’s not the only thing preventing the attack.
Proper implementation of the Chip/Pin EMV standards make the attack obsolete.
Sure mate, sure! I will open you secret, there is no “proper implementation”, “proper implementation” is what banks want you to think as cause of problem, because they failed with lies about chip cards being soooooooo secure. Especially US, US banking is worst in the world, but US is good at lies. Maybe some sort of dynamic discretionary data would fix chip cards, but even with that, I am not sure.
Read how EMV actually works. Yes, what you call, “dynamic discretionary data”… IS being used.
Your grudge against the US aside…
Europe has implemented this widely, and the attack discussed here, would fail with that proper implementation. That is why these shimmers are popular in Mexico and not the US… because of the Chip and PIN can and is often implemented correctly. It’s not about “trusting banks” at their word. It’s about understanding that nothing is a panacea, but there are comparatively more secure or less secure implementations.
It’s interesting that this article is not only drawing comments from Security and ATM personnel but also the grammar police.
Seriously, my in bank technical ATM career has gone from supporting and testing hardware and software to 50% security.
Thanks for the great article.
Did they actually crack the encryption?
The solution described sounds like a “known plaintext” attack on the symmetric key encryption. Knowing the contents, they were eventually able to recover the key.
“these are the cards that interacted with the skimmer, and so these card numbers are most likely on this device.”
“had success decoding the encrypted gibberish”
So a known plaintext attack?
@Brian:
“bit long longer [sic]”
One word: Apple Pay. LOL
So putting aside that is two words – what is your point? Some merchants are still cash only, what does Apply Pay have to do with anything?
Skimmer/shimmer?
Auto-incorrect?
Good investigative job Krebs. I love your insights.
As a security consultant and from a technical point of view, the problem is fairly simple to solve – about the 16 numbers being upstreamed and flagged by system security.
I will not post the solution as it can be used for wrongdoing.
Keep the good work.
There is obviously someone intelligent working for the gangs. I doubt that a simple solution exists that they just haven’t thought of yet. Rather, the circumstances dictate using a static number.
Here were my initial thoughts:
I guess since the skimmers can’t actually block the card data from going across the network, their static code was going to be found eventually.
The shimmer’s intermittent power supply (only powered when the ATM is presented a card), rules out clock based like TOTP for the “download card” to present. Hashtables wouldn’t work well since the counters would never be synced when there are few-to-many download cards to ATM skimmers.
The download card data would also have to pass LUHN checks, because otherwise it would be just as easy for banks to track down. That’s probably why they used a real stolen card number.
“download card causes an encrypted data exchange between it and the shimmer” and “two-way handshake”
My guess is that they don’t want two-way communications to begin until the download card has “triggered” the shimmer.
Similar to the bluetooth problem, they don’t want to announce the shimmer’s presence first. That rules out HMAC challenge response.
And having a unique number for each ATM shimmer would probably not work, because the gang’s installers are probably not also the downloaders, so it would be hard to mass produce and scale that kind of management.
—
I don’t think there would be an easy to implement solution that can work for a crime gang at scale, seeing how they operate (separate installers and retrievers, many ATMs to few download cards, power supply only on during card read, and the limitations of directly tapping onto the card reader).
It limits their possibilities.
I get what you’re saying, but I tend to be with Clausewitz. I’ve already got the first design approach I’d try roughed out in my mind. Won’t comment here, no sense contributing to making it easier for the bad guys. Also will observe I think the two of you may be talking about slightly different aspects of the problem. Seems to me that Clausewitz was eliminating the signature from network traffic and you’re talking about eliminating the download handshake. Related but not the same. BTW I’m not so sure your rationale for eliminating HMAC is sound, physical insertion is dissimilar to broadcasting bluetooth. Do banks stick protocol analyzers into ATM slots to look for such things? Do those tools even exist? Hmmm, never mind, my next unrealistically narrow niche startup product just came to mind… 🙂
I understand where you two are coming from. I happen to value open discussion among the white hat defenders, knowing that black hats are not stopped, not even slowed down, because security pros “don’t want to give them ideas”. They are already discussing this stuff, they aren’t stupid, and they aren’t waiting for ideas.
For 0day vulnerabilities, I would agree about waiting for responsible disclosure and for the patch. But open discussion about the problem is more likely to help defend against it, rather than help bad actors.
It’s the whole reason we have red teams and threat modeling. Defenders MUST think like bad guys, and work through the attack scenarios before it becomes a reality in the wild.
I guarantee, whatever we humble security professionals are thinking of, they are thinking the same/better, and have been for years. Their profit motivations ensure they are having these discussions and working through the problem.
–
Yes, I am talking about eliminating the signature from the network too. Not the handshake. The handshake is the reason the signature is needed though. The real problem that I think is the reason they opted to keep the static CC as the trigger to begin the handshake… is the nature of how the shimmer is tapped onto the reader. It is a physical tap, and cannot “block” the traffic between the card and the ATM networking components.
–
You’re right though, it would be very difficult for banks to go to every ATM with an analyzer. Hell of a lot harder than just looking through the logs.
It kinda reminds of other trends in cybersecurity where one side validates the other, but it’s only one way.
Here, ATMs always validate a card. But should cards (now smart), begin to validate the integrity of the ATM?
I have never done any kind of hardware development but would love to know how this type of thing is generally made and how hardware communicates over encrypted channel between two different devices that are so small, etc. I am familiar with software handshake/encryption/public-private key but would love how (be kind – hardware noob just looking for the right ‘terms’ to search or read about) hardware like this in small form does it and how it’s programmed to it’s firmware (terminology correct?)..
A lot of people in the maker space (especially in wearables) use the ESP devices. Small form boards easy to program to do all kinds of things.
ESP32 and ESP8622 are quite popular and cheap.
You can also use SoC (system on a chip) search term and there is a lot of information.
Just an observation:
The article states “The download card … features the same contacts as a chip card.”
But the shimmer and the download card show 8 contacts. I looked at my chip cards and they all have 6 contact points.
ISO7816 cards have 8 contacts, a bank card uses only 6 of them, the remaining two are application-specific. The download card shown here is probably 20 years old, back then they were made commercially in large quantities to be used as smart card emulators, primarily to fake pay tv access cards (a big thing in eastern Europe) and prepaid cards for public phones. The design of the “shimming device” shown above also isn’t really new (it contains an Atmel XMEGA), this is probably a recycled “tv card enabler” – a device that modified subscription messages and went between pay tv card and decoder.
Since so many are getting into the amateur editor role, I’ll throw in my two cents. Paragraph 18 refers to an account number found on the download card, but the download card itself was not introduced and described until paragraph 22. Thus, reading paragraph 18 had me scrolling back looking for this download card that I didn’t understand and thought I’d somehow missed.
Amazing that you were able to compose the entire article without once mentioning organized criminal gypsy gangs from Romania.
Do the operators of the international network (SWIFT?) behind all these financial transactions keep track of how often an individual card is used? It seems in this case that a single Austrian bank card number was used for gazillions of transactions. Should that raise a red flag or is that information not obtainable?
SWIFT is more back end, bank to bank.
Each ATM supports networks, as shown on your debit card.
The video of his arrest was most satisfying. “Mexican frogmarch”.
Hopefully the Romanian authorities haven’t been sufficiently corrupted.
Is this related to the (also Romanian) skimmer gang that is accused of funding politicians in Mexico?
Seems like too much of a coincidence.
I understand passive powering the low power SoC bus and the printed circuit layer, but I’m not seeing how insertion and extraction by the ops worked… Those chips would rub and break SM solder joints easily and even the PC sheet would see friction..
I bet they had a lot of problems out of this design in terms of durability… Also it’s annoying how influential people in the industry don’t call out banks for not ditching mag strip(ISO-7811) and the SDA and DDA modes of EMV. Just have EMV(ISO-7816-1) and NFC(ISO-14443/18092/21481) with CDA and carding and skimming dies over night…