Monthly Archives: November 2021
Arrest in ‘Ransom Your Employer’ Email Scheme
In August, KrebsOnSecurity warned that scammers were contacting people and asking them to unleash ransomware inside their employer’s network, in exchange for a percentage of any ransom amount paid by the victim company. This week, authorities in Nigeria arrested a suspect in connection with the scheme — a young man who said he was trying to save up money to help fund a new social network.
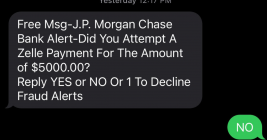
The ‘Zelle Fraud’ Scam: How it Works, How to Fight Back
One of the more common ways cybercriminals cash out access to bank accounts involves draining the victim’s funds via Zelle, a “peer-to-peer” (P2P) payment service used by many financial institutions that allows customers to quickly send cash to friends and family. Naturally, a great deal of phishing schemes that precede these bank account takeovers begin with a spoofed text message from the target’s bank warning about a suspicious Zelle transfer. What follows is a deep dive into how this increasingly clever Zelle fraud scam typically works, and what victims can do about it.
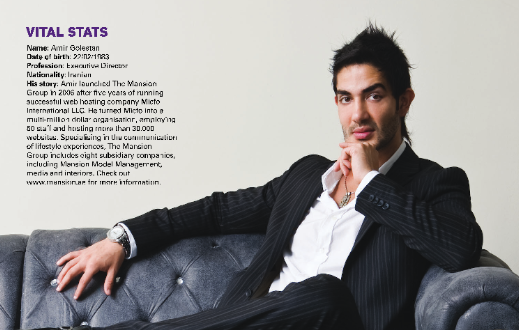
Tech CEO Pleads to Wire Fraud in IP Address Scheme
The CEO of a South Carolina technology firm has pleaded guilty to 20 counts of wire fraud in connection with an elaborate network of phony companies set up to obtain more than 735,000 Internet Protocol (IP) addresses from the nonprofit organization that leases the digital real estate to entities in North America.
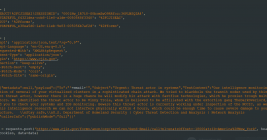
Hoax Email Blast Abused Poor Coding in FBI Website
The Federal Bureau of Investigation (FBI) confirmed today that its fbi.gov domain name and Internet address were used to blast out thousands of fake emails about a cybercrime investigation. According to an interview with the person who claimed responsibility for the hoax, the spam messages were sent by abusing insecure code in an FBI online portal designed to share information with state and local law enforcement authorities.
SMS About Bank Fraud as a Pretext for Voice Phishing
Most of us have probably heard the term “smishing” — which is a portmanteau for traditional phishing scams sent through SMS text messages. Smishing messages usually include a link to a site that spoofs a popular bank and tries to siphon personal information. But increasingly, phishers are turning to a hybrid form of smishing — blasting out linkless text messages about suspicious bank transfers as a pretext for immediately calling and scamming anyone who responds via text.
Microsoft Patch Tuesday, November 2021 Edition
Microsoft Corp. today released updates to quash at least 55 security bugs in its Windows operating systems and other software. Two of the patches address vulnerabilities that are already being used in active attacks online, and four of the flaws were disclosed publicly before today — potentially giving adversaries a head start in figuring out how to exploit them.
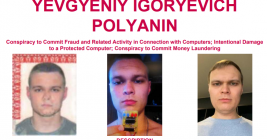
REvil Ransom Arrest, $6M Seizure, and $10M Reward
The U.S. Department of Justice said today it arrested a Ukrainian man who deployed ransomware on behalf of the REvil ransomware gang, a Russian cybercriminal collective that has extorted hundreds of millions from victim organizations. The DOJ also said it had seized $6.1 million in cryptocurrency sent to another REvil affiliate, and that the State Department is now offering up to $10 million for information leading to the arrest of any key leaders of REvil.
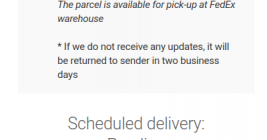
‘Tis the Season for the Wayward Package Phish
The holiday shopping season always means big business for phishers, who tend to find increased success this time of year with a time-honored lure about a wayward package that needs redelivery. Here’s a look at a fairly elaborate SMS-based phishing scam that spoofs FedEx in a bid to extract personal and financial information from unwary recipients.