The Department of Homeland Security (DHS) is urging states and localities to beef up security around proprietary devices that connect to the Emergency Alert System — a national public warning system used to deliver important emergency information, such as severe weather and AMBER alerts. The DHS warning came in advance of a workshop to be held this weekend at the DEFCON security conference in Las Vegas, where a security researcher is slated to demonstrate multiple weaknesses in the nationwide alert system.

A Digital Alert Systems EAS encoder/decoder that Pyle said he acquired off eBay in 2019. It had the username and password for the system printed on the machine.
The DHS warning was prompted by security researcher Ken Pyle, a partner at security firm Cybir. Pyle said he started acquiring old EAS equipment off of eBay in 2019, and that he quickly identified a number of serious security vulnerabilities in a device that is broadly used by states and localities to encode and decode EAS alert signals.
“I found all kinds of problems back then, and reported it to the DHS, FBI and the manufacturer,” Pyle said in an interview with KrebsOnSecurity. “But nothing ever happened. I decided I wasn’t going to tell anyone about it yet because I wanted to give people time to fix it.”
Pyle said he took up the research again in earnest after an angry mob stormed the U.S. Capitol on Jan. 6, 2021.
“I was sitting there thinking, ‘Holy shit, someone could start a civil war with this thing,”’ Pyle recalled. “I went back to see if this was still a problem, and it turns out it’s still a very big problem. So I decided that unless someone actually makes this public and talks about it, clearly nothing is going to be done about it.”
The EAS encoder/decoder devices Pyle acquired were made by Lyndonville, NY-based Digital Alert Systems (formerly Monroe Electronics, Inc.), which issued a security advisory this month saying it released patches in 2019 to fix the flaws reported by Pyle, but that some customers are still running outdated versions of the device’s firmware. That may be because the patches were included in version 4 of the firmware for the EAS devices, and many older models apparently do not support the new software.
“The vulnerabilities identified present a potentially serious risk, and we believe both were addressed in software updates issued beginning Oct 2019,” EAS said in a written statement. “We also provided attribution for the researcher’s responsible disclosure, allowing us to rectify the matters before making any public statements. We are aware that some users have not taken corrective actions and updated their software and should immediately take action to update the latest software version to ensure they are not at risk. Anything lower than version 4.1 should be updated immediately. On July 20, 2022, the researcher referred to other potential issues, and we trust the researcher will provide more detail. We will evaluate and work to issue any necessary mitigations as quickly as possible.”
But Pyle said a great many EAS stakeholders are still ignoring basic advice from the manufacturer, such as changing default passwords and placing the devices behind a firewall, not directly exposing them to the Internet, and restricting access only to trusted hosts and networks.

Pyle, in a selfie that is heavily redacted because the EAS device behind him had its user credentials printed on the lid.
Pyle said the biggest threat to the security of the EAS is that an attacker would only need to compromise a single EAS station to send out alerts locally that can be picked up by other EAS systems and retransmitted across the nation.
“The process for alerts is automated in most cases, hence, obtaining access to a device will allow you to pivot around,” he said. “There’s no centralized control of the EAS because these devices are designed such that someone locally can issue an alert, but there’s no central control over whether I am the one person who can send or whatever. If you are a local operator, you can send out nationwide alerts. That’s how easy it is to do this.”
One of the Digital Alert Systems devices Pyle sourced from an electronics recycler earlier this year was non-functioning, but whoever discarded it neglected to wipe the hard drive embedded in the machine. Pyle soon discovered the device contained the private cryptographic keys and other credentials needed to send alerts through Comcast, the nation’s third-largest cable company.
“I can issue and create my own alert here, which has all the valid checks or whatever for being a real alert station,” Pyle said in an interview earlier this month. “I can create a message that will start propagating through the EAS.”
Comcast told KrebsOnSecurity that “a third-party device used to deliver EAS alerts was lost in transit by a trusted shipping provider between two Comcast locations and subsequently obtained by a cybersecurity researcher.
“We’ve conducted a thorough investigation of this matter and have determined that no customer data, and no sensitive Comcast data, were compromised,” Comcast spokesperson David McGuire said.
The company said it also confirmed that the information included on the device can no longer be used to send false messages to Comcast customers or used to compromise devices within Comcast’s network, including EAS devices.
“We are taking steps to further ensure secure transfer of such devices going forward,” McGuire said. “Separately, we have conducted a thorough audit of all EAS devices on our network and confirmed that they are updated with currently available patches and are therefore not vulnerable to recently reported security issues. We’re grateful for the responsible disclosure and to the security research community for continuing to engage and share information with our teams to make our products and technologies ever more secure. Mr. Pyle informed us promptly of his research and worked with us as we took steps to validate his findings and ensure the security of our systems.”
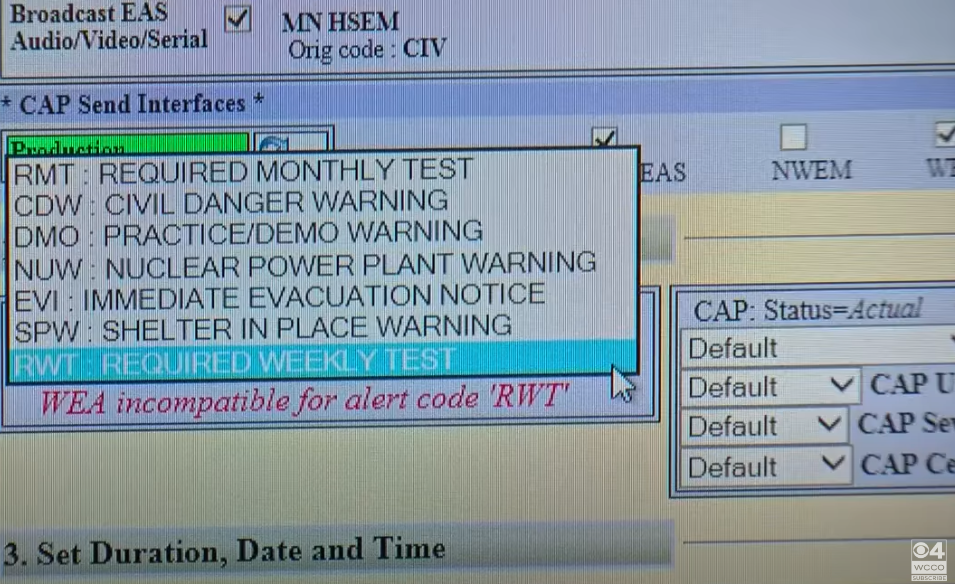
The user interface for an EAS device.
Unauthorized EAS broadcast alerts have happened enough that there is a chronicle of EAS compromises over at fandom.com. Thankfully, most of these incidents have involved fairly obvious hoaxes.
According to the EAS wiki, in February 2013, hackers broke into the EAS networks in Great Falls, Mt. and Marquette, Mich. to broadcast an alert that zombies had risen from their graves in several counties. In Feb. 2017, an EAS station in Indiana also was hacked, with the intruders playing the same “zombies and dead bodies” audio from the 2013 incidents.
“On February 20 and February 21, 2020, Wave Broadband’s EASyCAP equipment was hacked due to the equipment’s default password not being changed,” the Wiki states. “Four alerts were broadcasted, two of which consisted of a Radiological Hazard Warning and a Required Monthly Test playing parts of the Hip Hop song Hot by artist Young Thug.”
In January 2018, Hawaii sent out an alert to cell phones, televisions and radios, warning everyone in the state that a missile was headed their way. It took 38 minutes for Hawaii to let people know the alert was a misfire, and that a draft alert was inadvertently sent. The news video clip below about the 2018 event in Hawaii does a good job of walking through how the EAS works.



Found it interesting that in the list of alert types there was one labeled “Trump rally nearby, beware of roaming stupid people”.
Really? You didn’t “censor” this comment, Brian? But you’ll censor my reply. Good grief.
Hey Pete. Welcome. Some comments here get auto-moderated. This can happen for a variety of reasons. Maybe the post has so many links it looks spammy to our systems. Maybe it includes profanity, which gets a post auto-moderated. It also sometimes happens if you post too many comments too quickly, or hit the submit button more than once.
Point is, there can be 100 reasons why comments don’t immediately show up. I try to keep up with them, but some go straight to spam, and those I almost never have time to look at.
I will say this: I allow a ridiculous amount of inane, vapid and even personally offensive comments to be published here, because I’m not interested in being the thought police here. But I DO censor comments from readers who baselessly charge that I am censoring comments.
Well made me chuckle. Good way to start a Monday.
Not changing default passwords for critical infrastructure devices should be considered negligence. There is no excuse for this in today’s world at all. If municipalities, companies, or unions won’t voluntarily hold employees accountable, laws should. That being said, we shouldn’t need to legislate everything to get people to perform basic tasks such as this. Unacceptable.
Welcome to the wonderful world of ICS. Default passwords are just the tip of the iceberg, typically.
We need more private oversight of government. Take Marquette, Mich for example. It looks like they’ve got a grand total of 6 government commissioners. In their latest commission meeting (available on YouTube) the big get was a guy complaining that there is a dead tree hanging over the parking lot at the park. There is no way they have the time or the specialized manpower to setup or monitor these types of systems to a high level. I know, everyone *SHOULD* take the cybersecurity aspect of these things seriously, but everyone should also know how to turn their water, or gas, or electricity off to their house and I can tell you most people have no idea what that means.
My stab at the problem would be one piece of legislation mandating that if you are incorporated as anything larger than say a township (1,000 people) or larger you will be required to have a yearly audit done by a private security company and all critical and high level findings be mitigated within the calendar year. This pen test will be performed at standard market rates.
If you start slapping the negligent label on people they will do even less than they are doing now out of fear, and if something does happen the truth will be very hard to find behind all the lies meant to cover themselves or people they care about. You can’t call someone stupid enough for them to agree with you. You need to walk with them for a bit and then lead them the right way.
A comprehensive peer-reviewed open source (branding agnostic) security checklist and accompanying public audit would be preferable to a private audit. IMO. The issue is they don’t tend to have money or the burning desire to get up to date even when audits find glaring issues so they just sit there for years. There’s no enforcement of such a finding like a security-DCMA takedown or something. Unless insecure systems are routinely and automatically excised and without a legal mechanism to do so within years (if at all), an audit is just a suggestion.
OTOH an audit along with a volunteer public committee that reviews such a security checklist and makes public those findings on a routine basis could be useful to at least increase the shame level on those unwilling to invest in security basics and best practices. Any public officials and stewards of those systems would be seen as derelict in their duty to secure that public trove, and the public being made routinely aware of that concern could be an interesting political lever to call them to secure funding and the impetus required to do things correctly. Currently it’s CSPAN3 level interest by most and officials are happy ignoring what the public seems to accept.
“public committee that reviews such a security checklist and makes public those findings”
I agree. What I meant by private oversight was the ones doing the audit should be non-government experts in the field. I’ve known a few auditors from government agencies. Some are competent, but most seem to only know what is on the checklist they photocopied from the local library in 2001.
Whether it’s a public or private audit is kind of a blur when we’re talking about private security researchers / organizations informing public policymakers on best practice checklists. I just meant the reports must be transparently public as private audits don’t necessarily go that way, NDA’s etc. Another trip up is making such reports public before the vulns are fixed given the pace of those fixes. It’s a treasure map meanwhile. Some % of those municipalities and bureaus are just not going to get it done and must be taken down. There’s no mechanism to achieve that. You can imagine the local popularity of a suggestion that they go dark until they’re secure.
I agree that “slapping the negligent label” will make people hide. It is not a good approach. The best practice is approach in a way of self disclosure. Most importantly to understand consequences via teaching.
As a owner and operator of a competing brand of EAS system (from SAGE Alerting Systems), I can tell you that it REQURES both the admin and user passwords be changed as part of the startup. It will not allow you to use the username in any part of the password such as admin / 911admin911. The DASDEC is typically installed in TV and CABLE installations because of its ability to generate a composite video output with the alert information displayed or scrolling that can easily and automatically be switched on-air. SAGE units are installed in may radio stations across the country.
Also, the SAGE has a specific parameter that must be set in order for it to be able to locally create and send a national level alert. That parameter is factory default to OFF. The SAGE is a wonderful box to work with.
I can’t find this talk listed on the Defcon calendar or workshop page, any other links/info? He’s got something on Sunday but doesn’t say anything about EAS.
they were in the Villages, IOT and App Sec.
The researcher was at DefCon in the IoT Village but definitely was not on the mainstage. Those talks are typically reserved for serious legitimate researchers. This researcher dumpster dove a poorly disposed device. Not a typical mainstage discussion these days.
“In January 2018, Hawaii sent out an alert to cell phones, televisions and radios, warning everyone in the state that a missile was headed their way. It took 38 minutes for Hawaii to let people know the alert was a misfire, and that a draft alert was inadvertently sent.”
That was not an EAS hack or compromise, unless you consider mistaken use by an authorized alert originator a compromise. The FCC investigation found that an officer sent the erroneous alert because he believed an internal drill, phoned into the warning point, was real and not a drill, as it contained the words “This is not a drill”. The FCC called that a “deviation from the drill procedure.” While the drill also repeated the word “Exercise”, the warning officer said he did not hear that word.
“Use of the same language for both test and live alert initiation procedures could cause confusion among warning officers who received the message without prior notice, notwithstanding the statements at the beginning and end of the message that it was an exercise,” the FCC said.
The frequency with which the Hawaii emergency management agency conducted drills “far exceeds the norm,” the FCC found, increasing the likelihood of a false alert; and the agency lacked any procedure for correcting a false alert.
I was able to attend both of Ken’s presentations At Defcon this weekend. Nothing short of amazing. Besides sharing information, his encouragement of people to learn, understand at different levels of tech to improve security postures was powerful.
Negligence was a factor touched upon in the article but the extent of that negligence is rather greater, I susepect.
For example, the “Required Weekly Test” is repeated for several days on the local system, and that testing includes RWT’s from other regions, and not necessarily adjacent regions. For at least the first half of the week, and for the first week of every month, It’s less “cable TV” and more “The EAS Cable Network”. Perhaps there could be a channel dedicated to nothing but EAS alerts from anywhere just for the EAS fans so they don’t have to put it on all the channels every day?
…simple negligence is almost never punished…
…it takes gross negligence to rate punishment but then only if the normal course requires care…
…since no legislation governs…
…but I repeat myself…
I continue to suffer due to IT negligence. Its great that they know about this but when will I see feel and hear a difference?
When what? When criminal intent is no longer a thing. Not. Ever.
An unsatisfying dunk on an insurmountable problem in ourselves.
Power will always corrupt, technology will always be abused for that.
It’s a struggle until there is no further cause for struggle in this world.
I suggest a drink while we wait.
Everything’s relative. Yes these are valid concerns, but its still hygiene 101 which is not just on these “critical devices”. As to starting a civil war, the researcher is generating hype. Having a previous career as a broadcaster before the EAS, the system was the EBS, totally manual, and the passwords for the entire country were distributed on paper to every broadcast station and cable company. Monthly passwords were on the outside of the pink envelop, and inside were password for each day of the year. Talk about insecure. As to the Comcast device, one would hope if a trusted carrier lost the device, then passwords and certificates were changed. Frankly the story is not as significant as it seems.
When EBS was replaced by EAS in the 90s, physical access to the device (and a password) was required to change settings or initiate an alert. Never would I have dared connect it to a modem let alone the internet, and it only trusted two upstream stations. An FCC license was required just to bask in its presence, and playing games was sure to attract the attention of federal law enforcement.
We were trained to say our prayers if an alert ever went off outside of a testing window. Today it goes off on my phone for so many non-events, I have disabled it.
Humans will always attempt to connect critical infrastructure to the internet when their parents are away.
Microsoft in the 90’s routinely ignored security holes. It’s operating system was apparently “Good Enough” to run voting machines when everyone who knows anything about security knows Windows is about as useful to security as a pail with many holes is to holding water.
I suspect that there are people who are “paid to look the other way” for anything that has to do with notifying “The People” of events. Keep in mind that there was the whole dialog of a “Missile” that hit the Pentagon during 9-11 and there is decent evidence that Pearl Harbor had some forewarning. Both of those events were used as justification for later wars which translated into may billions of dollars of lucrative contracts.
i wonder if this happened in la a few days ago ….