A major new malware spam campaign mimicking invites sent via business networking site LinkedIn.com leverages user trust and a kitchen sink of browser exploits in a bid to install the password-stealing ZeuS Trojan.
 The spam campaign began Monday morning, according to security experts at networking giant Cisco Systems, and for a while the fake LinkedIn invitations accounted for as much as 24 percent of all spam. Recipients who click links in the message are taken to a Web page that reads, “Please Waiting, 4 seconds,” and then sent on to Google.com.
The spam campaign began Monday morning, according to security experts at networking giant Cisco Systems, and for a while the fake LinkedIn invitations accounted for as much as 24 percent of all spam. Recipients who click links in the message are taken to a Web page that reads, “Please Waiting, 4 seconds,” and then sent on to Google.com.
On the way to Google, however, the victim’s browser is silently passed through a site equipped with what appears to be the SEO Exploit Pack, a commercial crimeware kit that tries to exploit more than a dozen browser vulnerabilities in an attempt to install ZeuS.
This attack will no doubt fool a large number of people. Dan Tynan, a reporter for IT World, said he was tricked into clicking the link and possibly infecting his system.
It’s a good idea to avoid clicking social networking site invites that arrive by e-mail, especially if you don’t recognize the name of the person who’s inviting you. Instead, consider just browsing to the social networking site and handling any invites there. Also, this attack is a good reminder that it pays to stay up-to-date on the latest security patches.
What interests me most about this scam is that it shows that criminals wielding ZeuS are now using employment-oriented online services both to infect new PCs and to “cash out” these same victims, thanks to money mules recruited at job search sites like Monster.com and Careerbuilder.com.
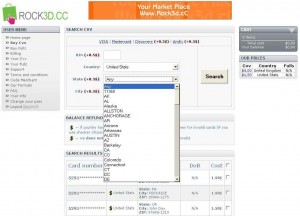
I asked Cisco to supply more information about the domains used in this attack. Some of that information is included at the summary listed here (please take care with the domains on this list — they all should be considered hostile).