2011 has been called the year of the data breach, with hacker groups publishing huge troves of stolen data online almost daily. Now a new site called pwnedlist.com lets users check to see if their email address or username and associated information may have been compromised.
 Pwnedlist.com is the creation of Alen Puzic and Jasiel Spelman, two security researchers from DVLabs, a division of HP/TippingPoint. Enter a username or email address into the site’s search box, and it will check to see if the information was found in any of these recent public data dumps.
Pwnedlist.com is the creation of Alen Puzic and Jasiel Spelman, two security researchers from DVLabs, a division of HP/TippingPoint. Enter a username or email address into the site’s search box, and it will check to see if the information was found in any of these recent public data dumps.
Puzic said the project stemmed from an effort to harvest mounds of data being leaked or deposited daily to sites like Pastebin and torrent trackers.
“I was trying to harvest as much data as I could, to see how many passwords I could possibly find, and it just happened to be that within two hours, I found about 30,000 usernames and passwords,” Puzic said. “That kind of got me thinking that I could do this every day, and if I could find over one million then maybe I could create a site that would help the everyday user find if they were compromised.”
Pwnedlist.com currently allows users to search through nearly five million emails and usernames that have been dumped online. The site also frequently receives large caches of account data that people directly submit to its database. Puzic said it is growing at a rate of about 40,000 new compromised accounts each week.
Puzic said information contained in these data donations often make it simple to learn which organization lost the information.
“Usually, somewhere in the dump files there’s a readme.txt file or there’s some type of header made by hacker who caused the breach, and there’s an advertisement about who did the hack and which company was compromised,” Puzic said. “Other times it’s really obvious because all of the emails come from the same domain.”
Puzic said Pwnedlist.com doesn’t store the username, email address and password data itself; instead, it records a cryptographic hash of the information and then discards the plaintext data. As a result, a “hit” on any searched email or username only produces a binary “yes” or “no” answer about whether any hashes matching that data were found. It won’t return the associated password, nor does it offer any clues about from where the data was leaked.
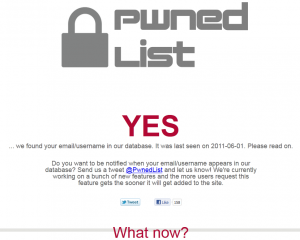
Any site that raises awareness about the benefits of strong passwords is a good thing in my book. But deciding what action to take — if any — after finding a hit on your email address at pwnedlist.com. I searched for my email address, krebsonsecurity [at] gmail.com, and the site told me my address was found in the database on June 1, 2011.
Answering the question of, “What now,” pwnedlist.com offers the following advice:
“Don’t panic! Just because your email was found in an account dump we collected does not mean it has been compromised. Your first reaction should be to immediately change any passwords that might be associated with this email account. It is probably a wise idea to go through all your accounts and create new passwords for each of them, just in case. Once one account has been compromised its best to assume all others have been too. Better safe than sorry.”
My email password is ridiculously long and complex, but being the ultra paranoid type, I tend to change it frequently, and have done so several times since it landed in this database.
Length and complexity are two of the most important factors in determining a strong password. It’s also a good idea to periodically change passwords for sensitive accounts, provided you have a decent way to recover the password should you forget or lose it. Check out my Password Primer for a list of tips and resources to help create and protect strong passwords.
Puzic said while his site does not store username or email address submitted to the pwnedlist.com form, for security reasons he does keep a record of Internet addresses of those who use the site: It seems some users have been trying to poison the database or include malware and exploits in data dumps submitted to the site.
“We have attempts about every other week [to plant malware or hack the site], but nobody’s done it yet,” he said. “We’ve had lots of different attempts. Someone tries just about every week.”
The two researchers plan to begin publishing regular updates to their Twitter account (@pwnedlist) when new data dumps are discovered. Longer term, Puzic said he has multiple goals for the site, including a longitudinal study on password security.
“I would love it if this could raise awareness about cybersecurity,” he said. “Also, it could serve as a good measuring stick for the amount of breaches that happen every day. For example, if you see that all of a sudden I have eight million more entries, something big may have happened.”




Looks like they are getting a DDOS attack… : (
It is working now…
Pwnedlist.com pwned? 🙂
Puzic says the traffic spike caught them in a middle of an upgrade, and their Amazon auto-scaling is disabled. They say they’re working to remedy this and the site should be back up soon.
Either that, or there are too many paranoid people following KOS that are trying to check to see if there user/email are on the list. Maybe KOS has inadvertently created a DDOS. That’d be ironic.
nice! guess it must be going against some people’s (criminal) interests…
I cannot connect at the moment (keeps timing out). Can you only check once? I mean this in the sense that if you check and find you’re on the list, then go about changing all your passwords, would there be any way to check in the future to see if your account was compromised since then?
Kevin, I believe I saw a blurb that said if your email didn’t show up in the database, you can check in the future. Also, you can get a tweet from them if it does show up later. I’d go back and copy it but I can’t connect.
I managed to check 2 of mine right after you posted, and they both said “nope”, which is nice. But now the site is showing signs of overload. Nice work, Brian, all your readers broke the “pwnedlist site”. Ha ha. 🙂
“… Enter a username or email address into the site’s search box, and it will check to see if the information was found in any of these recent public data dumps…”
‘Damned if you do, damned if you don’t.
What happens when (not if) -they- get whacked with all that information in there?
.
???
You apparently missed the whole paragraph that said:
“Puzic said Pwnedlist.com doesn’t store the username, email address and password data itself; instead, it records a cryptographic hash of the information and then discards the plaintext data. As a result, a “hit” on any searched email or username only produces a binary “yes” or “no” answer about whether any hashes matching that data were found. It won’t return the associated password, nor does it offer any clues about from where the data was leaked.”
>“… Enter a username or email address into the site’s search box, and it will check to see if the
>information was found in any of these recent public data dumps…”
Better than “enter your usernames and passwords and we will check to see if any have been compromised”.
I believe that some people would actually input BOTH email and password to see whether the account has been compromised, if both would be asked for.
I wish there was a way for me to search my company’s domain name. While *@gmail.com would obviously show up as “pwned” something less useful such as *@GusTaco.com would be helpful. Perhaps this is a service they will offer later?
This guy beat them to it months ago: https://shouldichangemypassword.com/
looks better and more up to date.
How do you know its more up to date. Their FAQ still states: “As of June 25th 2011 there are just over 1 million records in the datbase”.
Just go to the sources page – https://shouldichangemypassword.com/sources.php – last db upload was October 11, 2011, so yes it is being maintained. What’s more you can find out which attack pwned your account, if any.
+1 for more ‘features’ -1 for less up to date
PwnedList: We update our database at least once every 24 hours. … As of Nov 3rd, 2011, we have 4,945,786 entries.
One of my e-mail did not show up on that list despite the fact I know it was compromised recently. So it seems to me false negatives are a significant issue here. Yes, I know they address that issue in their mice type but like all mice type it doesn’t get read often and I worry about a sense of false confidence this site can breed.
My other issue is that according to Ghostery they are using Google Analytics. So now Google knows that I’m concerned enough about security issues to go visit such a website. Time to market me new ads!
“My other issue is that according to Ghostery they are using Google Analytics.”
Firefox + NoScript.
Ghostery doesn’t just report it. It can block it too.
With worries like that, it’s time to put google-analytics in your HOSTS file.
yes. shouldichangemypassword beat this guys site. and threat post beat krebs to posting about this…
In spite of what they claim about not capturing queries, this seems to be a great way for them to gather email addresses.
Brian, what makes you trust these fellows?
They cover that: “Don’t trust us? You can also use a SHA-512 hash of your email/username as input.”
Just hash the address yourself, and they check it directly against their list of hashes.
C’mon folks, are you telling me that you are gullible enough to trust the html words? Isn’t that the problem with so many victims? They read the content of a web page and assume it’s truthful. None of us know what’s going on behind the html, regardless of what the words say. Brian, I appreciate your never-ending quest for raising awareness of the innocent in the methods of security unprofessionals and the thieves that wear the title hackers, but I see patterns of behavior in the comments of many of your blogs: readers (whether they be honest or whether they be hackers) blindly trust your recommendations. This is a very dangerous pattern. I place high value on your blogs and ask you to continue your exemplary work, but let’s face it – this very web page we’ve all come to know and blindly trust could have been posted by someone other that Brian, and we have no way of confirming the author’s identity, or do we? Are there mechanisms that can be incorporated into a blog that would verify the integrity of the content? Yes. Are they used in this blog? No. Brian, one of your flock seeks guidance on this matter. Would you consider a supplemental blog that is secure? I think many of us would be willing to pay a subscription to cover the fees, if any, to know for certain that the web content we read that is labeled “krebsonsecurity” is in fact authored by Brian Krebs.
Wow! I’ve always thought that I was near the top of the paranoid heap. Thanks for convincing me that I still have a long way to go. 🙂
If you submit a hash, who cares what they may or may not do.
In your hurry to comment, you have probably missed others who have brought out the same issue and have resolved it.
This is interesting information. Thanks a lot, also My company EZMCOM is conducting a survey to understand your business need and address the security requirement. Please click on the link http://www.surveymonkey.com/s/2HCM8TJ to take this 1 minute survey. We also have lucky draw where we are giving 10 iPod Shuffles for those that complete the survey and LIKE & SHARE our http://facebook.com/ezmcom page
It was a bit confusing what actually was meant when pwnedlist.com showed my email address has been pwned.
I assumed it meant some hacker got both my email address AND my password, as if the email acct itself had been hacked.
But not necessarily . . .
I knew my email address was exposed in the gawker media intrusion by Gnosis on 2010-12-12.
But what they got was my email address – but my password for gawker media – not the password for my associated email address – they’re different.
But because of that intrusion, pwnedlist.com shows that email address as pwned.
But again, Gnosis didn’t get the associated email password.
For now, I am safe. My email addresses were not found in the database. Like this post states, I firmly believe having a long and complex password is very important. Also, you should get into habit of changing your passwords at minimum once per year.
“change any passwords that might be associated with this email account”
I fear that this kind of site could do more harm than good. People often seem to react to this kind of non-specific fear-mongering with “it won’t happen to me” thinking which could carry over to more specific threats.
Also, once your address is in the database as you’ve done all the work to change your passwords, the next hit is worthless — you already know it was compromised.
This is an amusing advertisement for password security, but I don’t see how it is useful information.
Well, perhaps this will lead people to change their e-mail address altogether or at least disassociate it from vulnerable commercial accounts.
Personally, I never use my main e-mail address with any commercial accounts. I’ve been using disposable @sneakemail.com addresses since 2004, which was completely free until about 2010. Now they charge $2 a month, but I consider it cheap insurance.
What are peoples thoughts on expanding this and allowing wildcard usages. I’m just thinking along the lines of being able enter “*@company.com” and being able to check if your company as leaked email addresses.
I get notice of ‘large volume of requests from my IP’ (static IP) then the captcha plugin crashes my browser. (latest chrome dev build, fresh install)
Frustrating