“Project Blitzkrieg,” a brazen Underweb plan for hiring 100 botmasters to fuel a blaze of ebanking heists against 30 U.S. financial institutions in the Spring of 2013, was met with skepticism from some in the security community after news of the scheme came to light in October. Many assumed it was a law enforcement sting, or merely the ramblings of a wannabe criminal mastermind. But new research suggests the crooks who hatched the plan were serious and have painstakingly built up a formidable crime machine in preparation for the project.
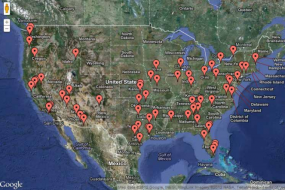
McAfee says it tracked hundreds of infections from Gozi Prinimalka since Project Blitzkrieg was announced in early September.
The miscreant who posted the call-to-arms — a bald, stocky guy using the nickname vorVzakone (literally, “thief in law”) — also posted a number of screen shots that he said were taken from a working control panel for the botnet he was building. Those images contained several Internet addresses of PCs that were allegedly part of his botnet. According to RSA Security, the botnet consisted of systems infected with Gozi Prinimalka, a closely-held, custom version of the powerful password-stealing Gozi banking Trojan.
In an analysis (PDF) to be published Dec. 13, security vendor McAfee said it was able to combine the data in those screen shots with malware detections on its own network to correlate both victim PCs and the location of the control server. It found that the version of the Prinimalka Trojan used in the attack has two unique identifiers (“Campaign ID” and “Bot ID”) that identify what variant is being deployed on infected computers. McAfee said that all of the systems it identified from the screen shots posted by vorVzakone carried the Campaign ID 064004, which was discovered in the wild on April 14, 2012.
Ryan Sherstobitoff, a threat researcher at McAfee, said the company’s analysis indicates that Project Blitzkrieg is a credible threat to the financial industry and appears to be moving forward.
“There is much speculation whether Project Blitzkrieg is real or simply a creation of Russian law enforcement as a sting operation. Our analysis suggests it is authentic, though the timing of the fraudulent activity is unknown,” Sherstobitoff said.. “We do know that the thieves have had an active system since April 2012, with at least 500 victims who can be linked to vorVzakone.”
As sophisticated as Gozi Prinimalka is, it has kept an unusually low profile. Sherstobitoff said the Prinimalka Trojan does not appear to have developed by vorVzakone; rather, analysis of underground chatter regarding this Trojan indicates that it was developed by another group and provided to them. He added that the Prinimalka Trojan linked to Project Blitzkrieg is a direct evolution of a Gozi variant seen in early 2007 and discovered by Dell Secureworks, which was linked to a turnkey fraud solution called 76Service.com.
McAfee found that the original variant of Prinimalka was created in November 2008, and was tied to attack infrastructure based in Ukraine. The second variant was tied to the vorVzakone pilot project in April. But the company spotted a third version connected to Romanian servers that was first deployed in the wild not long after vorVzakone’s call-to-arms post in September 2012.
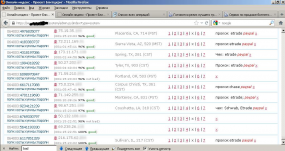
Hacker “vorVzakone” published this screen shot of a component of the Prinimalka botnet control panel [IP obfuscation added]
Sherstobitoff posits that vorVzakone most likely intended to hire botmasters who already had access to substantial numbers of login credentials for the U.S. financial institutions targeted in the scheme. As detailed in a screen shot published on this blog in early October, there are some banks you’d expect to see on the list — Bank of America, Capital One and Suntrust, for example — but many of the targets of Project Blitzkrieg are in fact investment banks, such as American Funds, Ameritrade, eTrade, Fidelity, OptionsExpress, and Schwab.
Many of these institutions — and the investment banks in particular — make customers jump through multiple hoops before being allowed to move money out of accounts. But the danger with threats like Prinimalka is that they offer thieves a myriad of tools to circumvent fraud protections and to impersonate customers. As RSA reported, the malware lets the bad guys effectively clone the victim’s PC, at least as far as the bank’s Web site is concerned:
A novel virtual-machine-synching module announced by the gang, installed on the botmaster’s machine, will purportedly duplicate the victim’s PC settings, including the victim’s time zone, screen resolution, cookies, browser type and version, and software product IDs. Impersonated victims’ accounts will thus be accessed via a SOCKS proxy connection installed on their infected PCs, enabling the cloned virtual system to take on the genuine IP address when accessing the bank’s website.
It now looks more likely that this was a “legitimate” fraud campaign being planned in the underground, but it’s impossible to say whether the Spring of 2013 will bring the promised blitzkrieg of fraud, or if the mastermind himself is even still coordinating the project. Shortly after my story on vorVzakone went live, he disappeared from the underground forum where he’d hatched the plan, and was roundly chastised by forum members for bringing so much public attention to the topic. In all likelihood, he is simply maintaining a lower profile these days.
Modern malware like Gozi Prinimalka highlights the need for Internet users and banks alike to take more aggressive steps to ensure the integrity and security of online transactions. Live CDs are a great way to achieve that from the customer’s end (this approach works even when the user’s underlying hard drive is already infected with malware). Financial institutions need to consider approaches that don’t rely mainly on forcing the user to supply ever greater amounts of personal information to authenticate themselves, because this approach fails when the user’s computer is already compromised.
Update, Dec. 14, 11:30 a.m. ET: Added link to McAfee’s research paper.




“…a blaze of ebanking heists against 30 U.S. financial institutions in the Spring of 2003…”
2013?
Great googley moogley! Fixed, thanks.
Were (are) there any comments or speculation on why PayPal is on most of the accounts?
Speculation: perhaps because it’s easy to add a paypal account to another account that you have control over. Answer some questions, and confirm a microdeposit amount and you’re done.
Brian,
When sharing, the extract/headliner still reads “2003”.
When sharing on what or how? I just flushed the cache on the site. The summary was changed along with the lead. Check again?
I shared on Yammer and the lead still says “2003”. I can send you a screen shot if you like.
It will be interesting to see if projects of this size are actually feasible, or whether the hackers involved will collapse into the usual internecine feuding and backstabbing or alternatively that the entire project will be leaked (as it appears to have been), detected and (more or less) successfully defended against if and when it occurs.
In other words, are there limits to the level that hackers using existing technology can reach in terms of mass financial attacks? Or to put it another way, is something akin to “Stealing the Network: How To Own a Continent” at all feasible?
Keep on keeping on. Thanks, krebs!
I want a child from you, you are so smart!
The virtual-machine-synching modules seems like an overly complicated solution to a relatively simple problem: evading device fingerprinting.
In a nutshell, the issue is that by checking various browser settings, the banking website can guess with a high probability whether the connection comes from the usual user’s pc or some other machine. To evade the detection, the attackers want to mimic the victim’s system as much as possible.
I don’t want to go into technical details here, but you can completely defeat this protection with either off-the-shelf software or a simple custom browser extension. Building an entire virtual machine environment for this task seems positively Rube Goldberg-esque.
I agree its so easy to do and it dont cost much either . But people like Brian Crebs and Mcfee team thinks its out of this word and only professional hackers like them can do it .so out of touch
cookies
Good report Brian. Thanks!
Half of America must be crapping there pants right now , just cos some kid with 500 infected PCs said something publicly . Brilliant — yellow press at its best .it only takes 3 min to infect 500 PCs this days anywhere in the word no problemo they even let you pick the country .
Brian u said it before .You like traffic this story brings to your blog that all .So you keep going over and over and over the same old dead story again and again . SUCK it till its dry !!
i will lough my head of in spring/summer/winter/when ever in 2013 when every single bank will say , we spent all this money and nothing happening .bloody Brian Crebsky and his BS story’s .
If only all Windows and Mac users would perform their online banking under the protection of Trusteer Rapport. If only all banks would place Trusteer software in their systems. One can dream …..
I am pleased to see that an advert for Trusteer now appears on the front page of http://krebsonsecurity.com
For Windows and Mac users, there is no better way to make online banking as reasonably secure as possible. It is impossible to ensure total security but to use Trusteer Rapport is to exercise Due Diligence with two capital Ds.
I would no more go online to my bank without Rapport than I would leave my house without being decently clothed.
Brian we watching you .
From FSB With Love .
There never seems to be any comment about the South Carolina Department of Revenue being hacked. Maybe we are just unimportant???