Some of the most successful and lucrative online scams employ a “low-and-slow” approach — avoiding detection or interference from researchers and law enforcement agencies by stealing small bits of cash from many people over an extended period. Here’s the story of a cybercrime group that compromises up to 100,000 email inboxes per day, and apparently does little else with this access except siphon gift card and customer loyalty program data that can be resold online.

The data in this story come from a trusted source in the security industry who has visibility into a network of hacked machines that fraudsters in just about every corner of the Internet are using to anonymize their malicious Web traffic. For the past three years, the source — we’ll call him “Bill” to preserve his requested anonymity — has been watching one group of threat actors that is mass-testing millions of usernames and passwords against the world’s major email providers each day.
Bill said he’s not sure where the passwords are coming from, but he assumes they are tied to various databases for compromised websites that get posted to password cracking and hacking forums on a regular basis. Bill said this criminal group averages between five and ten million email authentication attempts daily, and comes away with anywhere from 50,000 to 100,000 of working inbox credentials.
In about half the cases the credentials are being checked via “IMAP,” which is an email standard used by email software clients like Mozilla’s Thunderbird and Microsoft Outlook. With his visibility into the proxy network, Bill can see whether or not an authentication attempt succeeds based on the network response from the email provider (e.g. mail server responds “OK” = successful access).
You might think that whoever is behind such a sprawling crime machine would use their access to blast out spam, or conduct targeted phishing attacks against each victim’s contacts. But based on interactions that Bill has had with several large email providers so far, this crime gang merely uses custom, automated scripts that periodically log in and search each inbox for digital items of value that can easily be resold.
And they seem particularly focused on stealing gift card data.
“Sometimes they’ll log in as much as two to three times a week for months at a time,” Bill said. “These guys are looking for low-hanging fruit — basically cash in your inbox. Whether it’s related to hotel or airline rewards or just Amazon gift cards, after they successfully log in to the account their scripts start pilfering inboxes looking for things that could be of value.”
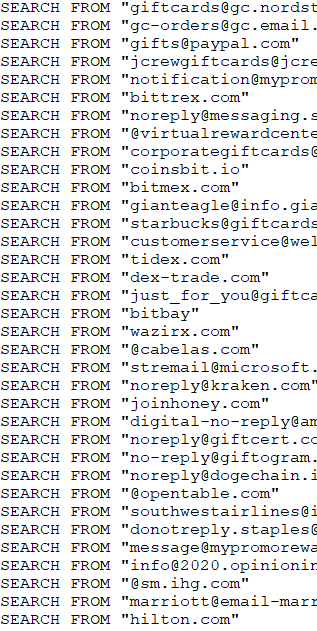
A sample of some of the most frequent search queries made in a single day by the gift card gang against more than 50,000 hacked inboxes.
According to Bill, the fraudsters aren’t downloading all of their victims’ emails: That would quickly add up to a monstrous amount of data. Rather, they’re using automated systems to log in to each inbox and search for a variety of domains and other terms related to companies that maintain loyalty and points programs, and/or issue gift cards and handle their fulfillment.
Why go after hotel or airline rewards? Because these accounts can all be cleaned out and deposited onto a gift card number that can be resold quickly online for 80 percent of its value.
“These guys want that hard digital asset — the cash that is sitting there in your inbox,” Bill said. “You literally just pull cash out of peoples’ inboxes, and then you have all these secondary markets where you can sell this stuff.”
Bill’s data also shows that this gang is so aggressively going after gift card data that it will routinely seek new gift card benefits on behalf of victims, when that option is available. For example, many companies now offer employees a “wellness benefit” if they can demonstrate they’re keeping up with some kind of healthy new habit, such as daily gym visits, yoga, or quitting smoking.
Bill said these crooks have figured out a way to tap into those benefits as well.
“A number of health insurance companies have wellness programs to encourage employees to exercise more, where if you sign up and pledge to 30 push-ups a day for the next few months or something you’ll get five wellness points towards a $10 Starbucks gift card, which requires 1000 wellness points,” Bill explained. “They’re actually automating the process of replying saying you completed this activity so they can bump up your point balance and get your gift card.”
The Gift Card Gang’s Footprint
How do the compromised email credentials break down in terms of ISPs and email providers? There are victims on nearly all major email networks, but Bill said several large Internet service providers (ISPs) in Germany and France are heavily represented in the compromised email account data.
“With some of these international email providers we’re seeing something like 25,000 to 50,000 email accounts a day get hacked,” Bill said. “I don’t know why they’re getting popped so heavily.”
That may sound like a lot of hacked inboxes, but Bill said some of the bigger ISPs represented in his data have tens or hundreds of millions of customers.
Measuring which ISPs and email providers have the biggest numbers of compromised customers is not so simple in many cases, nor is identifying companies with employees whose email accounts have been hacked.
This kind of mapping is often more difficult than it used to be because so many organizations have now outsourced their email to cloud services like Gmail and Microsoft Office365 — where users can access their email, files and chat records all in one place.
“It’s a little complicated with Office 365 because it’s one thing to say okay how many Hotmail connections are you seeing per day in all this credential-stuffing activity, and you can see the testing against Hotmail’s site,” Bill said. “But with the IMAP traffic we’re looking at, the usernames being logged into are any of the million or so domains hosted on Office365, many of which will tell you very little about the victim organization itself.”
On top of that, it’s also difficult to know how much activity you’re not seeing.
Looking at the small set of Internet address blocks he knows are associated with Microsoft 365 email infrastructure, Bill examined the IMAP traffic flowing from this group to those blocks. Bill said that in the first week of April 2021, he identified 15,000 compromised Office365 accounts being accessed by this group, spread over 6,500 different organizations that use Office365.
“So I’m seeing this traffic to just like 10 net blocks tied to Microsoft, which means I’m only looking at maybe 25 percent of Microsoft’s infrastructure,” Bill explained. “And with our puny visibility into probably less than one percent of overall password stuffing traffic aimed at Microsoft, we’re seeing 600 Office accounts being breached a day. So if I’m only seeing one percent, that means we’re likely talking about tens of thousands of Office365 accounts compromised daily worldwide.”

In a December 2020 blog post about how Microsoft is moving away from passwords to more robust authentication approaches, the software giant said an average of one in every 250 corporate accounts is compromised each month. As of last year, Microsoft had nearly 240 million active users, according to this analysis.
“To me, this is an important story because for years people have been like, yeah we know email isn’t very secure, but this generic statement doesn’t have any teeth to it,” Bill said. “I don’t feel like anyone has been able to call attention to the numbers that show why email is so insecure.”
Bill says that in general companies have a great many more tools available for securing and analyzing employee email traffic when that access is funneled through a Web page or VPN, versus when that access happens via IMAP.
“It’s just more difficult to get through the Web interface because on a website you have a plethora of advanced authentication controls at your fingertips, including things like device fingerprinting, scanning for http header anomalies, and so on,” Bill said. “But what are the detection signatures you have available for detecting malicious logins via IMAP?”
Microsoft declined to comment specifically on Bill’s research, but said customers can block the overwhelming majority of account takeover efforts by enabling multi-factor authentication.
“For context, our research indicates that multi-factor authentication prevents more than 99.9% of account compromises,” reads a statement from Microsoft. “Moreover, for enterprise customers, innovations like Security Defaults, which disables basic authentication and requires users to enroll a second factor, have already significantly decreased the proportion of compromised accounts. In addition, for consumer accounts, adding a second authentication factor is required on all accounts.”
A Mess That’s Likely to Stay That Way
Bill said he’s frustrated by having such visibility into this credential testing botnet while being unable to do much about it. He’s shared his data with some of the bigger ISPs in Europe, but says months later he’s still seeing those same inboxes being accessed by the gift card gang.
The problem, Bill says, is that many large ISPs lack any sort of baseline knowledge of or useful data about customers who access their email via IMAP. That is, they lack any sort of instrumentation to be able to tell the difference between legitimate and suspicious logins for their customers who read their messages using an email client.
“My guess is in a lot of cases the IMAP servers by default aren’t logging every search request, so [the ISP] can’t go back and see this happening,” Bill said.
Confounding the challenge, there isn’t much of an upside for ISPs interested in voluntarily monitoring their IMAP traffic for hacked accounts.
“Let’s say you’re an ISP that does have the instrumentation to find this activity and you’ve just identified 10,000 of your customers who are hacked. But you also know they are accessing their email exclusively through an email client. What do you do? You can’t flag their account for a password reset, because there’s no mechanism in the email client to affect a password change.”
Which means those 10,000 customers are then going to start receiving error messages whenever they try to access their email.
“Those customers are likely going to get super pissed off and call up the ISP mad as hell,” Bill said. “And that customer service person is then going to have to spend a bunch of time explaining how to use the webmail service. As a result, very few ISPs are going to do anything about this.”
Indictators of Compromise (IoCs)
It’s not often KrebsOnSecurity has occasion to publish so-called “indicators of compromise” (IoC)s, but hopefully some ISPs may find the information here useful. This group automates the searching of inboxes for specific domains and trademarks associated with gift card activity and other accounts with stored electronic value, such as rewards points and mileage programs.
This file includes the top inbox search terms used in a single 24 hour period by the gift card gang. The numbers on the left in the spreadsheet represent the number of times during that 24 hour period where the gift card gang ran a search for that term in a compromised inbox.
Some of the search terms are focused on specific brands — such as Amazon gift cards or Hilton Honors points; others are for major gift card networks like CashStar, which issues cards that are white-labeled by dozens of brands like Target and Nordstrom. Inboxes hacked by this gang will likely be searched on many of these terms over the span of just a few days.




My email settings send most offers like the ones mentioned to the spam and trash folders. Do the scanners these crooks use also scan those folders in addition to the inbox? I would guess “yes,” but am curious to know for sure.
I wonder how many people out there are like me – who keep no email’s? I am a retired home computer user… any email containing important info/files are downloaded and the email deleted. I have a “temporary” folder – but it gets cleared out systematically.
I keep no emails on the server, not sure if that’s the same as your doing.
I use Outlook and pop3 access. Outlook pulls all the new emails and removes them off the server. I don’t have any use for these http email clients. Don’t really like the idea of storing years of my emails on servers I don’t control. I have been slowly dropping public email provides I have used I the past (hotmail, gmail, etc) and switching to an email server I control.
That makes at least 3 of us who don’t leave any trace of emails on the server. Although I guess hackers could find a way to undelete emails or get into the “we keep your emails forever in case the Gov’t needs to see them server”.
I know more than a few people who leave them online so they can access them from anywhere. But they have tons of emails on the server just waiting to be hacked and maybe be held hostage. I download them, back them up with other critical files on my PC and get on with life.
The idea of someone easily reading even the mundane emails I have is not one I want to think about as someone can easily find a way to cause problems for me (you too). Let alone the banking emails which I’m sure hackers would love to access. Even if they can’t use the info at the moment, they now know way too much about where I bank, ditto credit cards, Amazon, eBay, etc… all potential cash cows as I see it.
They could get them in between arrival and you checking.
They still need you to reuse a comped credential like before.
You do not control the “inbox” you are thinking you deleted things from.
An email server you manage will have other issues. All details matter.
I understand the utility of gift cards as — you know — gifts, but I can’t get my mind around their popularity for rebates. A merchant offering / paying a rebate — either by check or by gift card — knows the recipient’s physical address. How can it be cheaper to pay for a gift card rather than issue a check? And yet, I’ve become accustomed to receiving rebates in the form of gift cards. Worth adding: because of the suspect nature of gift cards, some merchants refuse them. It seems to me: if gift cards weren’t used as a mode of payment, there’d be fewer fish in the sea for miscreants to waylay.
Gift cards have a low redemption rate. Some are not redeemed at all, others partially. You do not see this as much with cash or checks. The companies are banking on the low redemption rate to keep more of the rebates.
Gift cards are limited usually to a particular merchant, thus making them ‘sticky’ and useful for economic/marketing reasons to the issuing company. Also breakage is quite a bit more when you limit those redemption choices counter to cash or cash-like equivalents (Visa/Mastercard).
Gift cards will typically make up 2-8% of overall sales, depending on retail type, so they are big business. Using gift cards as rebates has two main advantages. If you write a check, the customer can spend that anywhere. Merchants want that rebate to come back into their store. The whole model of the rebate only makes sense if it drives additional spend – giving away cash just discounts the purchase. Similarly customers will spend 50%+ more than the gift card value, so even a rebate on returns card will drive additional revenue. Gift cards are either “brand owned” which are always accepted, or Visa/MasterCard branded and have to be accepted if the retailer belongs to those schemes. Like other frauds, such as cold callers getting susceptible folks to buy gift cards and read out card numbers and PINs over the phone, this is not gift card fraud. Gift card is just the innocent target.
Like KFritz, my settings will dump those offers in a local spam folder. But I run POP3 accounts so everything gets downloaded to my local server. Wonder if POP3 servers have run into this issue?
I’m confused. I have a Gmail account where I have enabled two factor authentication through Google authenticator. That account is also tied to a Thunderbird client through using IMAP. When I read my email through the Thunderbird client I am never asked for a second form of authentication. However when I log into my Gmail account through a web page I am always prompted for my second factor authentication.
Which prompts this question, does using IMAP in Thunderbird completely negate the protection of two factor authentication in my Gmail account?
Do you remember when the IMAP client was set up?
IIRC, setting up email clients requires going into the Google/Gmail settings and generating an application key (app password). Basically a long, random password that is only good for authenticating to the IMAP service (it can’t be used for all the other Google services).
“An App Password is a 16-digit passcode that gives a less secure app or device permission to access your Google Account. App Passwords can only be used with accounts that have 2-Step Verification turned on.”
So yeah, it does mean there is a single factor method to get access to your email. But it should be much more secure than your user-chosen password.
All victims should get refunded.
Anyways tge world is full of free money nobody dont work we have china india who can slave for the western countries if needed can also use africans and the usa canada uk and other well known western country people all of them should not work and they even dont need to.
They all can get stimulus checks playing on stock markets earning online and other funny things lol.
Funny but thats how the world is nowdays
And gift cards really isnt any real victims it just the number s out of the thin air as all usa dollars 90% of all usa dollars out of thin air.
What lossess we really talk about here ? Just the numbers just the digits nothing real
Also the china cheap labour and india can supply all the world so the rest of the world can just be the yputubers ig influencers investors speculators and video games players while staying home lol
What are you, twelve years old? That’s not how the world works.
That hurt to read.
Thank you JamminJ.
You don’t need to thank yourself.
Frustrating it can be when people have adjusted to the problem, know some emails being read first by someone else for small cash only to accumulate for than a live is interesting and something to be wary of. Thank you for the post.
Interesting tool. I once read it somewhere about a similar one, with support for proxies nearby the geolocation of the inboxes, dont remember which site I read this.
Some people often forget how many assets one possess.
Good work, Krebs. Keep us informed.
Reminds me the film : “Man bites dog” dialog.
If you catch a whale, you have everybody against you, the ecologist, the pacifist, the youngs, the olds, … If you catch a school of anchovies, nobody cares, they even help you to put them in tin cans.
Disable IMAP and POP3 access to the Email Server and use http based access. IMAP is legacy code.
Use proper passwords for your IMAP account, and don’t share credentials between accounts. The vulnerability this attack exploits has nothing to do with IMAP specifically, but with credential re-use.
IMAP offers a lot of advantages over doing everything through a webbrowser.
Exactly right. This is password stuffing of known credentials being applied.
If you are doing passwords correctly this will never be an issue.
And http(s)-based authentication is safer?… Dream on and get some education on subjects you clearly have no knowledge about
Yes, safer because it has options for MFA. That alone, makes it potentially much safer by just turning that on. CISA now regards single factor authentication as a “bad security practice”.
It’s an interesting story, but it still seems to be about weak/stolen usernames/passwords, not “SMTP, POP or IMAP are bad”, etc.
> You can’t flag their account for a password reset, because there’s no mechanism in the email client to affect a password change.
There is, though, a mechanism to _tell_ the user to go reset their password. The IMAP server can send an [AUTHENTICATIONFAILED] response with some text directing the user to the provider’s website. All mainstream clients are capable of displaying such a message to the user. Gmail proactively disables IMAP access every so often, and uses this technique; the login will fail with a message like “You must login via your browser first.”
My good ol’ hotmail account does a “reenter password” thing periodically but with 2FA on, I can verify the reset via authenticator
You have missed the point as to what is being looked for, and what is behind this attack. Your source is made up in my opinion and your knowledge of security appears very basic.
Two sentences and no specifics really drives the coup de grace home.
How could he go on knowing you’re skeptical and also vague? It’s too much.
Sure bet Krebs takes the entire site down now because of that wicked burn.
great story, but …
what can email acct holders DO to prevent their acct being scanned and info stolen?
those suggestions SHOULD be front & center in an article like this!!!
i’m thinking 1) change passwird immediately 2) use MFA.
anything else??
The entire story was about what happens to people who re-use passwords. So don’t do that. Also, use multi-factor authentication.
WoW this Bad 🙂
Use 2FA/ multi-factor & MD5 Hash Password 🙂
MD5?
The almost-as-scary part is just how many IMAP servers are running without TLS required, based on the fact the source is able to so easily see the IMAP server responses over the wire (unless they are seeing them from the hacked client end directly?). In either case, this is extremely common with smaller/local ISPs, which may explain the geographic targets. Don’t most/all modern email clients support basic IMAPS/IMAP-STARTTLS? It doesn’t fix the password reset or 2FA issues others have mentioned, but it’s definitely low hanging fruit on the security checklist.
“Bill examined the IMAP traffic flowing from this group to those blocks.”
= if not backend then side-in, not a good indicator of TLS or not.
They just sat on the specific port traffic, no need to read the emails.
I have to admit that you have shown a great insperation in this wonderful site. I understood that we should teach a tactical approach in every learning opportunity that we received even in our own ways of learning before teaching technical skills and showing the result to others to come up for successful and contented result and through this i was able to modify each poject that i have specialy this one: I have to admit that you have shown a great insperation in this wonderful site. I understood that we should teach a tactical approach in every learning opportunity that we received even in our own ways of learning before teaching technical skills and showing the result to others to come up for successful and contented result and through this i was able to modify each poject that i have specialy this one:
What startles me here is despite the breathless headline and claims about compromised email accounts, there simply is NO EVIDENCE presented of actual hacked/stolen gift cards (or for that matter, travel rewards accounts)
The comments above are likewise written by apparent clueless wonders who have no idea how huge the on-line gift card re-selling world is. Is this the new Krebs style? Breathless warnings, with no actual substance? Selling their services to on-line merchants? (about a threat presumed to exist, but not actually documented) Pardon the cynicism about the ordinarily good Krebs name, but as one who has traded heavily in gift cards for nearly a decade, and monitored private gift card re-selling forums closely for years, I’ve never seen or heard of such …. horrors.
What gives here?
Ummm… “A sample of some of the most frequent search queries made in a single day by the gift card gang against more than 50,000 hacked inboxes” Screenshot in the article.
This article is full of links and evidence. Also, there are plenty of YouTube channels for scambaiters that show how gift cards are abused for fraud.
Your comment is either disingenuously trying to defend fraudsters or you are trying to bury your head in the sand.
Sounds like you don’t want a light shined on your “business”, because people will see how much it’s used for criminal activity.
You’ve traded heavily in gift cards for almost ten years and you’ve never considered how much of it is related to outright theft? Have you ever wondered why there are so many heavily discounted cards out there? In any case, gift cards and prepaids in general have been a massive way for thieves to launder stolen funds or access to accounts at hundreds of retailers, and this is not new.
What I thought was interesting was that this gift card fraud industry has become so commoditized that some criminal groups seem to laser focus on that alone, even when they could be doing 100 other bad and profitable things with the access they gain each day to all those inboxes. It’s also interesting because gift card fraud is in many ways close to a perfect crime because there are so many different, unrelated parties involved that it is very hard for all those parties to work together toward a common goal — especially if the incentives aren’t aligned right (they aren’t).
What sort of “evidence” would satisfy you, in the context of this story? Also, I’m not sure I get where your angst comes from. There are no services or companies being promoted in this story, and no companies being made an example of. The only way I could get this source (who I’ve known for many years) to agree to talk about and share data on his findings was to agree not to mention his real name.