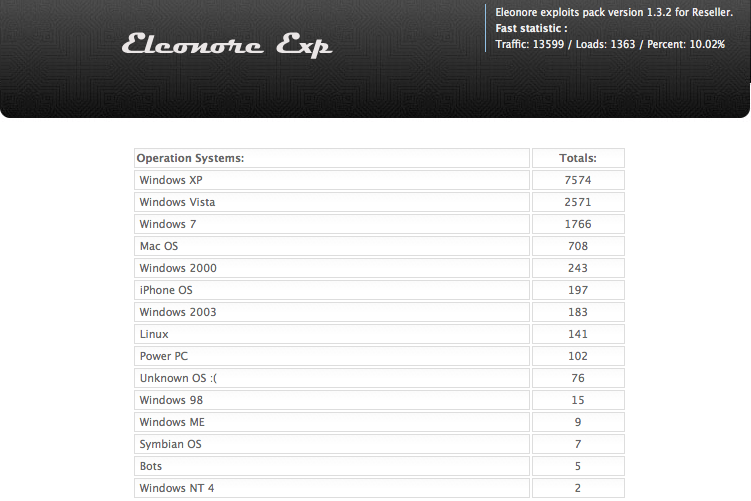
Not long after I launched this blog, I wrote about the damage wrought by the Eleonore Exploit Kit, an increasingly prevalent commercial hacking tool that makes it easy for criminals to booby-trap Web sites with malicious software. That post generated tremendous public interest because it offered a peek at the statistics page that normally only the criminals operating these kits get to see. I’m revisiting this topic again because I managed to have a look at another live Eleonore exploit pack panel, and the data seem to reinforce a previous observation: Today’s attackers care less about the browser you use and more about whether your third-party browser add-ons and plugins are out-of-date and exploitable.
Hacked and malicious sites retrofitted with kits like Eleonore have become more common of late: In a report issued this week, Web security firm Zscaler found that roughly 5 percent of the browser exploits they identified during the first quarter of this year were tied to hacked or malicious sites that criminals had outfitted with some version of Eleonore.
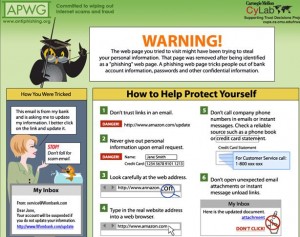
Like most exploit kits, Eleonore is designed to invisibly probe the visitor’s browser for known security vulnerabilities, and then use the first one found as a vehicle to silently install malicious software. The hacker’s end of the kit is a Web-based interface that features detailed stats on the percentage of visitors to the booby-trapped site(s) that are successfully attacked, and which software vulnerabilities were most successful in leading to the installation of the hacker’s malware.
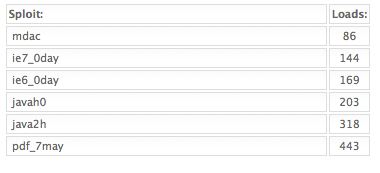
This particular Eleonore kit — which is currently stitched into several live adult Web sites — comes with at least a half-dozen browser exploits, including three that target Internet Explorer flaws, two that attack Java bugs, and one that targets a range of Adobe PDF Reader vulnerabilities. According to this kit’s stats page, the malicious adult sites manage to infect roughly every one in ten visitors.
As we can see from the landing page pictured above, Windows XP users represent by far the largest group of users hitting these poisoned porn sites.
Once again, Eleonore shows just how heavily Java flaws are now being used to infect computers (the above graphic shows the number of successful malware installations or “loads” per exploit). The last time I reviewed a working Eleonore admin panel, we saw that Java flaws were the second most reliable exploits. This time around, Java was the biggest source infections. In the Eleonore kit I wrote about earlier this year, some 34 percent of the systems that were successfully exploited were attacked via a Java flaw. In this installation, four out of every ten victims who were hacked were compromised because of they were running an outdated version of Java.