If you happen to stumble upon a Web site that freaks out your anti-virus program, chances are good that the page you’ve visited is part of a malicious or hacked site that has been outfitted with what’s known as an “exploit pack.” These are pre-packaged kits designed to probe the visitor’s browser for known security vulnerabilities, and then use the first one found as a vehicle to silently install malicious software.

Exploit packs have been around for years, and typically are sold on shadowy underground forums. A constant feature of exploit packs is a Web administration page (pictured above), which gives the attacker real-time statistics about victims, such as which browser exploits are working best, and which browsers and browser versions are most successfully attacked.
One of the most popular at the moment is a kit called “Eleonore,” and I’m writing about it here because it highlights the importance of remaining vigilant about patching. It’s also a reminder that sometimes the older exploits are more successful than the brand new variety that garner all of the headlines from the tech press.
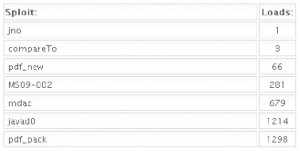
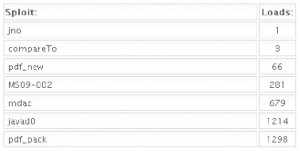 The screen captures in this blog post were taken a few weeks ago from a working Eleonore installation (version 1.3.2) that was linked to several adult Web sites. As we can see from the first image, this pack tries to exploit several vulnerabilities in Adobe Reader, including one that Adobe just patched this month. The kit also attacks at least two Internet Explorer vulnerabilities, and a Java bug. In addition, the pack also attacks two rather old Firefox vulnerabilities (from 2005 and 2006). For a partial list of the exploits included in this pack, skip to the bottom of this post.
The screen captures in this blog post were taken a few weeks ago from a working Eleonore installation (version 1.3.2) that was linked to several adult Web sites. As we can see from the first image, this pack tries to exploit several vulnerabilities in Adobe Reader, including one that Adobe just patched this month. The kit also attacks at least two Internet Explorer vulnerabilities, and a Java bug. In addition, the pack also attacks two rather old Firefox vulnerabilities (from 2005 and 2006). For a partial list of the exploits included in this pack, skip to the bottom of this post.
It’s important to keep in mind that some of these exploits are browser-agnostic: For example, with the PDF exploits, the vulnerability being exploited is the PDF Reader browser plug-in, not necessarily the browser itself. That probably explains the statistics in the images below, which shows a fairly high success rate against Opera, Safari, and Google Chrome users. In the screen shots below, the numbers beneath the “traffic” field indicate the number of visitors to the malicious site using that particular version of the browser, while the “loads” number corresponds to the number of visitors for that browser version that were found to be vulnerable to one or more of the vulnerabilities exploited by the Eleonore pack. The “percent” fields obviously indicate the percentage of visitors for each specific browser type that were successfully exploited (click for a larger version):
Continue reading →
 Both the victim corporation – Plano based Hillary Machinery Inc. – and the bank, Lubbock based PlainsCapital, agree on this much: In early November, cyber thieves initiated a series of unauthorized wire transfers totaling $801,495 out of Hillary’s account, and PlainsCapital managed to retrieve roughly $600,000 of that money.
Both the victim corporation – Plano based Hillary Machinery Inc. – and the bank, Lubbock based PlainsCapital, agree on this much: In early November, cyber thieves initiated a series of unauthorized wire transfers totaling $801,495 out of Hillary’s account, and PlainsCapital managed to retrieve roughly $600,000 of that money.