 Security experts have long maintained that running two different anti-virus products on the same Windows machine is asking for trouble, because the programs inevitably will compete for resources and slow down or even crash the host PC.
Security experts have long maintained that running two different anti-virus products on the same Windows machine is asking for trouble, because the programs inevitably will compete for resources and slow down or even crash the host PC.
But an upstart anti-virus company called Immunet Protect is hoping Windows users shrug off this conventional wisdom and embrace the dual anti-virus approach. Indeed, the company’s free product works largely by sharing data about virus detections from other anti-virus products already resident on the PCs of the Immunet user community.
Users can run Immunet alone, and many do: The program scans files using two types of threat profiles: specific definitions or fingerprints of known threats, and generic signatures that are more akin to looking for a specific malware modus operandi.
But what makes Immunet different from other anti-virus products is that it also incorporates detections for malware from other anti-virus products that may be resident on users’ machines. For example, each time someone’s PC in the Immunet user base encounters a virus, that threat is logged and flagged on a centralized server so that all Immunet users can be protected from that newly identified malware.
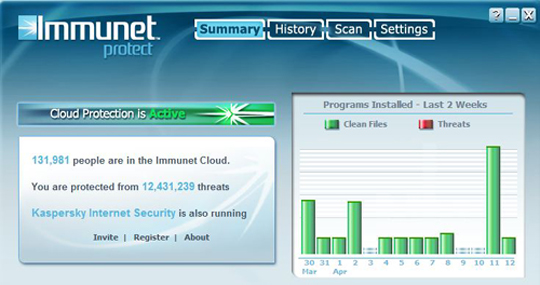
I’ve been running Immunet in tandem with Kaspersky Internet Security 2010 for the past three months, and have haven’t noticed any impact on system resources or stability issues. Immunet’s creators are especially proud of that last aspect of the program, and say it’s due to the fact that the program does most of its scanning and operations “in-the-cloud,” – that is, not on the user’s system. Immunet currently has about 133,000 active users, and that number changes constantly: Each time you reboot a system with it installed, chances are you will see a different – usually higher – number of users in the community.
I spoke recently with Immunet’s vice president of engineering, Alfred Huger, a former VP at Symantec Corp., and Adam O’Donnell, director of cloud engineering for the startup. That conversation — excerpts of which are included below — provides interesting insights into how the anti-virus industry operates, how consumers interact with these products, and how Immunet hopes to differentiate itself in already crowded field.
Adam O’Donnell (AO): People have been running multiple anti-virus packages on their desktop for years because they think they will get double protection. We’re just making sure we play well in that environment and that we tell customers, “No, it’s okay. We would like to be one of those.” A lot of our users are excited by fact that can run us in tandem with other products.
BK: Okay, but does the world really need another anti-virus product? Why should people turn to Immunet?
Alfred Huger (AH): The goal of the company was to build the next generation anti-virus product. We wanted to build an anti-virus program that could convict threats that weren’t previously seen – as well as those that were already known — but also to be able to do it in a way that was extremely light on resources and not as dependent on infrastructure, or on the way that anti-virus companies usually gather data.
BK: And how do they do that?
AH: Well, for example, with your typical anti-virus company, 95 percent of data you end up building definitions for you get from trading partners, other anti-virus companies. If I’m a large vendor and I’m sample trading, I’m probably getting 35-40 good feeds of actual malware that aren’t super false-positive laden. But the problem is I don’t always know how old those feeds are.
If you do enough testing, you’ll find that the feeds are probably anywhere between 1-30 days old. And that’s for a couple of reasons. First off, the guys trading you this stuff compete with you. They’re not stupid: The last thing they want to do is give you all of their signatures so you can compete better in product reviews. Every vendor — no matter how honest they are — games each other when it comes to trading samples.
BK: Do these samples all come from stuff the anti-virus companies have discovered, or is it just suspicious files, or…
AO: So, the way other vendors get their samples is not only from each other, but if you go far enough down the pipe, it’s off some desktop somewhere.
AH: And it really depends on the vendor. Symantec, for example, takes a truckload of stuff of desktops but they don’t ever trade that. Generally speaking, they don’t retrade stuff off of customer desktops. Hardly any of the vendors do. And they also retrade a truckload. What they trade is stuff that they have verified as malicious — meaning they have a guy who has hand-analyzed it. They also trade stuff they crawl.
BK: By “stuff they crawl” do you mean malware they find by following links in spam and by scouring the search engines and so on?
AH: Right. But a lot of it is aged. The average lifespan for a piece of malware when it’s most dangerous is one to two days. On the other hand, Immunet is community-reliant, which means it’s taking a sample right off of your PC and — providing it can make a distinction about whether it’s bad or not — and then sharing that with everyone in the community here and now. Which means protection is a lot faster for all users.
BK: And you think with enough time and users, Immunet will be better and faster at detecting threats?
AH: We’re able to pull in data from a community that isn’t homogeneous. The data isn’t just from AVG or Symantec or McAfee. Now, this doesn’t mean we’re going to blow the rest out of the water on detection. We’re still reliant on the same sorts of heuristic engines that every other anti-virus vendor is. The difference is once we identify it, we’re able to make detection for it available much, much faster. But there’s no question whether our product will increase your ability to detect viruses, full stop.
BK: If I have Immunet on my system in addition to another anti-virus product, which one speaks up first about an infection? Or will they both?
AH: Typically, the other anti-virus product will reside in front of us, but in some cases they don’t. In both cases, they should both alert if they both have [detection for] it. If you are running Kaspersky anti-virus and our stuff, and you download a threat, if Kaspersky detects it, they’ll flag it even if we do as well.
BK: So who’s your typical Immunet user? Have you learned anything about the user community yet?
AH: We’ve found a lot of stuff that’s completely bizarre. We have a Japanese partner that co-brands our stuff and distributes it Japan, and so we get to compare their user base with ours, which is mostly Western Europe, North America, and Brazil. So, we know which anti-virus products we’re co-resident with. But a decent portion of our user base are running no anti-virus at all other than us.
If you take that over to our Japanese users, 96 percent have another anti-virus product installed. At first we thought, ‘Wow, we have a serious bug.’ But as it turns out, there are a truckload of users who are in two boats: For whatever reason, they un-installed all anti-virus. Maybe it slowed down their computer or they decided they didn’t need it. Either that or they had a virus that disabled anti-virus. The breakdown is probably 25 percent had a virus that disabled their anti-virus, and 75 percent who didn’t have any anti-virus before they installed our product thought they didn’t need it.
So there seem to be really two schools of users, [those who have] nothing or everything. There are people who run Spyware Doctor, Threatfire, AVG, and then they will have like AVIRA with resident detection turned off, and then Hitman Pro and Online Armor, all on one machine. And you think, ‘Wow, how does your computer even boot, man?’”
BK: Interesting. So, that means a fair number of your users have a virus on their system when they install your product?
AH: It’s about 10 percent. At one point, a significant portion of our user base already had a virus when they signed up with us.
BK: Doesn’t that suggest that the anti-virus industry is advertising protection it can’t provide?
AH: The majority of anti-virus doesn’t work very well. The numbers they publish in the reviews are bull. It’s shameful. When we get past the “this software has turned my computer into a brick” syndrome, everyone I know has had a virus on their system even though they had a fully up-to-date anti-virus product. One of biggest problems of AV is that it’s still not solving the problem. If people made seat belts unreliable like this, executives would go to jail.
BK: What anti-virus products does Immunet currently play nice with?
[Huger provided me with a list of those anti-virus products that are officially supported and those that are unofficially supported (meaning Immunet doesn’t test them but users report success). Readers contemplating installing Immunet should read this known issues support Q&A.]
BK: So what’s next for Immunet?
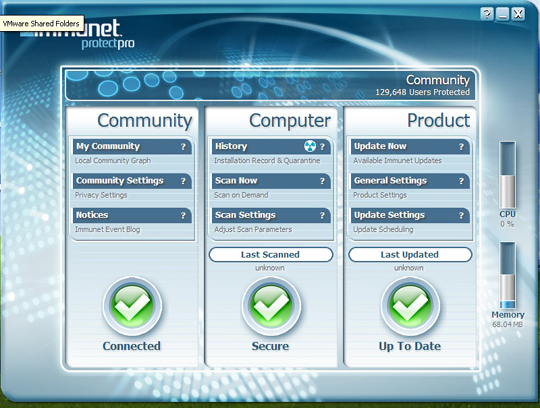
AH: The 2.0 version – which ships at the end of May – will be significantly different [screenshot below]. It has all of the functionality that a ‘pro’ main line AV product has. It still supports installing along side other AV products and it does have two new [anti-virus scanning] engines. One is called SPERO which is machine learning and cloud based and another called TETRA which is an ‘offline’ traditional PC side side engine which will only ship in the ‘Plus’ (commercial) version. We will also have both our Free version and a new commercial version which has offline protection and enhanced malware removal.




Brian,
I have been running Immunet along side of Symantec EndPoint for about 6 months without a problem. In fact it caught a file that Symantec missed.
Great article
When I stand up a new Windows Box, I always install ClamWin AV and AVG Free. I also use 2 free anti-malware programs & stay of those special sites. i have been using those to AV programs in conjunction since about 2003 or 2004. I admit that I have been infection free. It made sense to me to run AVs that were not system hogs to double check each other.
I really like the cloud based approach to AV, I am sure they are getting lots of good info from customers using it and another product.
Not sure how this is worthwhile. Typically when you see tests of AV products the top 10 or so all do better than 98% or 99% and all seem to miss the same obscure ones.
Its more likely you’ll be dealing with more false positives and other negative issues by doing this.
A smarter approach is what MS does with its commercial AV product. It uses different scan engines/definitions and then weighs the results depending on what engine/definition thinks its a virus.
Lastly, once people have reached the point of running multiple AVs its really time to start introduction them to running as a limited user instead of an administrator. Smarter rights management beats overly complicated AV solutions every time.
“Scanned in the cloud” kind of bothers me. If indeed it scans them off of the host machine, the files have to be uploaded some where to be scanned. How secure is this process? How do I know that the company isn’t just copying my documents and selling any decent information it finds?
Don’t think files are uploaded to be scanned; have watched network traffic and it’s not happening. It appears to only watch what loads/runs in memory and doesn’t scan HDs. File theft can happen in the same sense that Microsoft could try to upload your files on Patch Tuesday as well but they don’t. MS Security Essentials also requires you to join MS’ SpyNet and will upload detections as well. It’s whom you trust not to harm you. I installed ClamAV from Sourcefire (same thing, different name) because the Sourcefire brand has been around longer than Immunet and I trust Sourcefire not to harm me. Am not encouraging you to install – it’s simply a personal choice.
@Mike;
As far as scanning from the cloud; why should you trust your scanner to scan from an infected PC? Seems like it would be even more trustworthy from the cloud; who knows how malware may be controlling your PC scan process!
Mike, I have the same question as you do regarding privacy/security. I will say I like the idea of being able to run multiple sets or protection from different vendors.
DrZaiusApeLord, rights management paired with AV is the best way to go. The enviroment I work in has everyone running as a standard user and we still get infections. The more attack vecotrs I can close off the better and then I need to protect the vectors which cannot be closed off.
I installed this alongside Avast! and it reported that I am running something called “Trend Micro Virus Buster” instead of Avast? That’s odd.
I think having ThreatFire as a secondary AV is the best option as it’s zero-day protection.
While I always promote a layered defense (defense in depth) in which AV software is one important layer, and even though one could say this approach is adding another layer, I’m afraid this could be problematic beyond any performance issues.
First, it reinforces the idea that AV is your primary defense (or worse your only needed defense). Second, it seems to say the solution to the known failures of the AV industry is to double down and install more AV. Third, it can actually raise the attack surface of a system should there be an exploitable bug in the AV processes that typically run with elevated privileges. Fourth, it adds complexity and possibly user confusion. Are typical home users going to keep BOTH products up to date? I could see where they see one is up to date, but forget about the other.
@ Peter, “everyone running as a standard user and we still get infections”. I’ll surmise from poor decisions made by end users? (The person at the keyboard is also a layer of defense). I’ll also bet the infection is limited and easier to cleanup since they’re not running as administrators.
@ xAdmin: You are right AV is not the first line of defense. It should be the last line. Users need to learn how to navigate the net and learn what not to click.
What would the other layers of defense be in a home enviroment or a laptop I take with me?
How does Immununet work with Zone Alarm Suite?
@Frank: Poorly: I looked up on their FAQ and they specifically say that if you have ZoneAlarm and/or TrueVector installed, you shouldn’t install their product
I’ve been running Immunet and ZoneAlarm Security Suite together for 6 months on an XP machine with no conflicts or noticeable performance issues.
Hi Brian,
I am not the most computer literate guy on the block so please excuse any obviously stupid questions.
I am currently running AVG, Advance System Care Pro and IObit360 as well as Windows Defender. I have been running these three programs without and real performance issues other than the fact that I am on an older laptop (6 yrs). I do not run sweeps at same time however and when I do run sweeps I do so without other programs open.
At what point do I say ‘enough’?
If I wanted to download the Immunet program, would I drop one of the above mentioned others?
Thanks in advance,
Sean
Sean,
AVG offers good protection. I am not familiar with the other packages from a detection point of view. If you really rarely encounter threats (that your AV tells you about) I would not rush to install anything more than you already have.
Best,
Alfred
All,
There are some questions about privacy and Immunet Protect Beta. Our privacy policy is here:
http://support.immunet.com/index.php/Immunet:Privacy_policy
Our EULA is also clear on the topic. We, like other AV vendors, will take suspicious files (or what we think is suspicious) off your desktop. In our case it’s only PE (executable) files.
We do not upload files to the cloud and scan them for each file we review. For an overview of how we do detections please see:
http://blog.immunet.com/blog/2010/3/7/how-immunet-detects-threats-in-a-nutshell.html
If you’ve other questions, please feel free to post them here, to me personally, alfred at immunet.com or to our Community site community.immunet.com
Best,
Alfred
Have ClamAV 1.0.26 on fully-patched XP Home SP-3. It displays fine in admin account but displays as a white rectangle with missing images and buttons in user account, works fine otherwise. BTW, how are updates done? Silently, or do I have to manually uninstall old and install new?
Michael,
Sounds like your using IE6, what you are seeing is an IE rendering issue. I would suggest updating (for security concerns and to make our UI look better).
We can do both silent and user prompted upgrades.
al
No, don’t have IE6, have IE8 but Firefox is the default browser, could this be the problem?
Michael,
I may have misunderstood, are the white boxes on our site or in the product?
al
Agree with David Bradley, above. I run ThreatFire alongside F-Secure AV. Apart from a challenge every now and then by F-Secure to something ThreatFire is doing, they seem to work well together.
just want to clear here, as i read at Known issues
http://support.immunet.com/index.php/Known_Issues_-_Support#Immunet_Protect_Beta_is_not_compatible_with_PCTools_Firewall_Plus
PC Tool Firewall Plus (i assumed the free version of this) is not compatible with Immunet Beta. I download the lastest version of 32bit for XP Pro SP2 together with Avira AntiVir Free 10, latest version of Theatfire & latest version of PC Tools Firewall Plus Free. After a week observation on client PC i don’t have any issue see on it. Can you clarify what’s the exact error it prompts or any that i conclude PC Tools Firewall Plus & Immunet is not compatible?
TIA
Sheen,
It’s actually a user issue that is so common we had to designate it as incompatible, at least for the beta. The issue is that the firewall when configured strictly will deny access to our cloud.
al
Hi Al,
Good day. I’m just installing the PC Tools Firewall Plus Free with default configuration & don’t configure it on advanced mode, strict one or any. Just for basic protection & to replace the default Windows Firewall of XP.
regards, Sheen™
Thank you for the reply.
This trend worries me: somewhat improving the protection at the expense of layering AV products on top of each other. Even if those AV products to run side by side are as light on resources as their vendors claim to be, I expect a pretty modest ROI (extra security vs. performance hit). I think a radically different approach would be needed. Currently, I’ve created a couple of virtual images for Linux and Windows and I’m using VMware player to deploy them whenever I want to do Internet Banking or, on the contrary, to try a suspicious utility. They are disposable (I remove them after every single use). I did not got infected since 1995 (some luck and caution probably also played a role in this).
It seems to me that Immunet is the same thing as Prevx but with less capability. At least with Prevx, I have anti-key-logging and video screen blocking.
When I investigated Immunet I found it interesting, and will recommend it for users who don’t find Prevx or Rapport to their liking.
I wonder if Immunet and Prevx will work together…
Earl:
Be prepared for trouble if you do that. I purposely tried that with Snoopfree Privacy Shield and Prevx and ended up in a boot loop. Once I got into Safemode, I simply uninstalled Snoopfree as it is obsolete anyway.
I have a suspicion that many of these tools, including Rapport are actually root kits. Rapport is free, and makes similar claims about putting a bubble around the browser; however I’m not sure how well it blocks all keyboard and screen capture. This feature works very well with Prevx, but it isn’t free like Rapport.
Beware uninstalling any of these tools without checking to see if they have an uninstaller. This can hose your system just like a improperly removed rootkit would.
Prevx has its own uninstaller – only use it – not Windows.
I will highly appreciate if Alfred Huger can clearly explain as how immunet benefits from an installed AV?
Assume there is no AV installed and all users just use immunet, there is no way in the world you can protect user system based on some heuristic and cloud computing, which essentially works on hash based logic.
This is what i guess:
Say user has KAV and immunet installed and say KAV detects a threat, some how immunet figures out as which file is detected by KAV and sends hash(SHA1/MD5) of that file to their server and from that it gets passed to other users running immunet, that’s the only possible angle and benefit i can see.
I find Alfred not revealing what they actually are doing!
Can we please have a better explanation to have more trust in immunet?
-onlooker
I sympathize with you Fighter;
However, with all the fights over intellectual property now days, it would be a spot of luck to get much more information, unless they have a manual. I haven’t checked.
They also like to keep the malware coders in the dark about just how they work too. As I’ve said elsewhere, I suspect these are a family of legal root-kits, that fight fire with fire. Since they work at a lower level in the operating system, or have their own kernel which is independent, they don’t conflict with standard AV already installed on the operating system.
I can’t vouch for this product, but Prevx has done very well for me on my Vista x64 install; and sometimes beats Avast to the punch. It works VERY rapidly as far as heuristics go, and never gobbles up RAM or other resources. The keyboard/video blocker works quite well, although I’m not sure what all the product mentioned in this article does. You can be assured it is good science, and probably the fastest growing type of tool for security coming online this year!
I do not work for any of these companies, but I encourage the furtherance of PC security any way it can be fashioned. It is very good anytime you can have more than one real time protection scheme running at the same time with no hit on the system, or conflict with other products. Plus if it is free, all the better. Prevx is free for Facebook subscribers, and they get the anti-keylogging and screen capture feature in that version.
Don’t worry I don’t work for them either, or any single person or company. I just try to find the best utilities I can for my clients at the cheapest price, and I run a lab for some of them, and help others test new utilities for themselves.
AV is not rocket science and in the disguise cloud all sort of things are being done.
I will highly appreciate Brian if he can get an exact answer for data which Alfred mentioned :
———————————————————-
BK: And you think with enough time and users, Immunet will be better and faster at detecting threats?
AH: We’re able to pull in data from a community that isn’t homogeneous. The data isn’t just from AVG or Symantec or McAfee.
———————————————————-
When Alfred says this data isn’t just from AVG etc, what data he is talking about?
Brian, can we hear from you please?
I would also like to ask Alfred, if you send file from user system to your cloud?
And also do you scan those files by any other anti-virus in cloud as i tested few files and they seemed to have McAfee based malware names!
Guys, need lot of answers to understand what is special about it.