Earlier this year, KrebsOnSecurity featured a post highlighting the most dangerous aspects of GSM-based ATM skimmers, fraud devices that let thieves steal card data from ATM users and have the purloined digits sent wirelessly via text message to the attacker’s cell phone. In that post, I explained that these mobile skimmers help fraudsters steal card data without having to return to the scene of the crime. But I thought it might be nice to hear the selling points directly from the makers of these GSM-based skimmers.
So, after locating an apparently reliable skimmer seller on an exclusive hacker forum, I chatted him up on instant message and asked for the sales pitch. This GSM skimmer vendor offered a first-hand account of why these cell-phone equipped fraud devices are safer and more efficient than less sophisticated models — that is, for the buyer at least (I have edited his sales pitch only slightly for readability and flow).
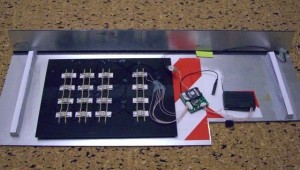
Throughout this post readers also will find several images this seller sent me of his two-part skimmer device, as well as snippets from an instructional video he ships with all sales, showing in painstaking detail how to set up and use his product. The videos are not complete. The video he sent me is about 15 minutes long. I just picked a few of the more interesting parts.
One final note: In the instruction manual below, “tracks” refer to the data stored on the magnetic stripe on the backs of all ATM (and credit/debit) cards. Our seller’s pitch begins:
“Let say we have a situation in which the equipment is established, works — for example from 9:00 a.m., and after 6 hours of work, usually it has about 25-35 tracks already on hand (on the average machine). And at cashout if the hacked ATM is in Europe, that’s approximately 20-25k Euros.
So we potentially have already about 20k dollars. Also imagine that if was not GSM sending SMS and to receive tracks it would be necessary to take the equipment from ATM, and during this moment, at 15:00 there comes police and takes off the equipment.
And what now? All operation and your money f#@!&$ up? It would be shame!! Yes? And with GSM the equipment we have the following: Even if there comes police and takes off the equipment, tracks are already on your computer. That means they are already yours, and also mean this potential 20k can be cash out asap. In that case you lose only the equipment, but the earned tracks already sent. Otherwise without dumps transfer – you lose equipment, and tracks, and money.
That’s not all: There is one more important part. We had few times that the police has seen the device, and does not take it off, black jeeps stays and observe, and being replaced by each hour. But the equipment still not removed. They believe that our man will come for it. And our observers see this circus, and together with it holders go as usual, and tracks come with PINs as usual.
However have worked all the day and all the evening, and only by night the police has removed the equipment. As a result they thought to catch malicious guys, but it has turned out, that we have lost the equipment, but results have received in full. That day we got about 120 tracks with PINs. But if there was equipment that needs to be removed to receive tracks? We would earn nothing.”
And what about ATM skimmers that send stolen data wirelessly via Bluetooth, a communications technology that allows the thieves to hoover up the skimmer data from a few hundred meters away?
“Then after 15 minutes police would calculate auto in which people with base station and TV would sit,” says our skimmer salesman. “More shortly, in my opinion, for today it is safely possible to work only with GSM equipment.
Aside from personal safety issues, skimmer scammers also must be wary of employees or co-workers who might seek to siphon off skimmed data for themselves. Our man explains:
“Consider this scenario: You have employed people who will install the equipment. For you it is important that they do not steal tracks. In the case of skimmer equipment that does not transfer dumps, the worker has full control over receiving of tracks.
Well, you have the right to be doing work in another country. 🙂 And so, people will always swear fidelity and honesty. This normal behavior of the person, but do not forget with whom you work. And in our situation people have no tracks in hands and have no PINs in hands. They can count quantity of holders which has passed during work and that’s all. And it means that your workers cannot steal any track.
I have listed only some situations in which GSM skimmers have obvious and total advantage before all other models. Do not ask me why I sell the equipment. I do not like this question. It’s my business why I drink coffee in the mornings why I go on trainings every day, and why I sell that or I do not sell. It’s my business.”
In the first video, we see our masked skimmer maker using a mock-up ATM to illustrate how to attach and reset his skimmer devices. The second movie shows the GSM card attached to the PIN pad overlay. In the final video, our skimmer seller demonstrates how to attach the SIM card to the ATM card skimmer module.
[EPSB]
Have you seen:
Sophisticated ATM Skimmer Transmits Stolen Data Via Text Message…Operating and planting an ATM skimmer — cleverly disguised technology that thieves attach to cash machines to intercept credit and debit card data — can be a risky venture, because the crooks have to return to the scene of the crime to retrieve their skimmers along with the purloined data. Increasingly, however, criminals are using ATM skimmers that eliminate much of that risk by relaying the information via text message.
[/EPSB]






Great article. But you didnt’ say anything about the price for the device. Did he gave you an offer?
it makes you think when you use an atm now
regards Colin
Youre GSM Skimmer would never work here in Central Europe .
I see its a Wincor Skimmer and its so different from the Original ATM inside or outside the Bank Institute.
The first customer would see that the card slot is different from the Original.
Why wouldn’t it work? Firstly, people aren’t very observant and don’t tend to notice small differences. Secondly, the skimmers come in different packages for attachment to different ATMs, so it is possible to make it look right.
Most people will never notice the difference.
Hi Brian
Apologies for being off topic but I saw this and thought it an interesting/effective approach – http://www.technologyreview.com/communications/26873/
as I’ve always said the tech has to be cheap otherwise banks won’t invest in it!
Thank you, Brian
I disagree with the skimmer’s manufacturer sales pitch regarding the shortcomings of Bluetooth or Wi-Fi skimmers, I think they are almost as safe for the skimmer and effective as the GSM model. Unfortunately, I don’t believe police routinely have equipment able to triangulate the location of receivers, especially in areas where many legitimate wi-fi or Bluetooth devices also exist. Fortunately, his pin pad seemed sloppy with “Cancel” and “Enter” buttons not sitting straight but this is something that can be fine-tuned.
The GSM module in turn, did not seem to have been cannibalized from a cheap phone, bur instead was either purpose built or, maybe bought from a source making this kind of modules for general purpose applications (such as alarm systems ?)
On a humorous note, I believe the person making the instruction videos should be fined for illegal Product Placement, I could clearly see the brand of batteries used. In those situations, the specific brand should be blurred. :).
@George,
That’s because this was a Duracell sponsored instructional video.
I know who’s batteries I’ll be buying next time!
@cybergibbons
there is no information about custom made GSM Skimmer.
The ATM Model looks like Wincor Nixdorf Pro Cash 2150 Series.
And the skimmer mold has a complete differen card slot.
but lets see what brian has to say about it.
If you can make a skimmer in one form, you can make it in another.
People really don’t notice the different card slots, as otherwise skimmers wouldn’t work at all.
I believe Brian has mentioned before that the more “reputable” skimmer makers will ask for a snapshot of your target ATM so they can do a custom job.
Brian,
Not being wise to the ways of the world, I have what may be a naïve question. Can’t the police: 1) remove the gizmo; 2) figure out the number it’s calling; 3) look up the address of said number; 4) show up at that address and make an arrest?
This tactic seems too easy. How do the criminals circumvent it?
They would never use a number attached to a contract. Prepaid or pay-as-you-go, SIMs changed every day, or couple of days. Which is why the skimmer needs to be reset, I guess.
I’m scared of plastic. Big time. Don’t think they’re deployed a lot in Eastern Europe, there’s probably not as much money to be made off of them, so unlikely to be worthwhile, but sometime soon, they’ll be here.
ATM’s are everywhere in Eastern Europe.
I was in Romania in the spring. Every ATM has a warning, displayed with large letters, to be careful and look to see if a skimmer is attached.
I have used ATM’s all over the world without any problems. Last spring in Romania every ATM I tried gave me the message : Transaction declined by your financial institution. Worried that someone had emptied my account I called my bank from Romania.
They told me that for that country, as well as for the “East” (they might have meant Eastern Europe, Ukraine, etc.) they disabled the ability to withdraw funds from their accounts because of widespread crime.
In italy it’s impossible to have Sim card without registering it with your ID, so it can be hard to use gsm module…
So they’d just use a phone from a different country. Or wifi, or bluetooth, or some other wireless protocol, or they’d just manually dump the data nightly.
Well you have to admit that to a fellow criminal, hois pitch would definetly resonate with them, after all the whole risk to this is being caught…So if you could limit your exposure to doing that, then your bettering your odds. While every scheme has it’s pitfalls as I am sure this does, You could see there will bethose that would take advantage of this. Since these are criminals I would think they would be using either pay as you go cell phones or using phony ID to get a cell phone paid for with stolen credit cards. Whether you get this info thru SMS or Bluetooth or wirelessly, I think this demonstrates just how much the criminals are changing and adapting their game and techniques to keep a step ahead in the game…
Is it me or while on the one hand we see ever more sophisticated skimmers, on the other the ATMs remain pretty much the same? Couldn’t something be done tho “harden” the ATM itself against these types of attacks?
Oh wait, that would involve banks actually caring about the problem, but since its not their money getting stolen…
> Oh wait, that would involve banks actually caring about the
> problem, but since its not their money getting stolen…
It is the banks money getting stolen. At least in the US, fraudulent ATM transactions, online banking and debit card payments are covered under Regulation E. This limits customer liability to $50. In practice most banks have a zero customer liability policy:
“Zero liability is now an industry standard,” said Doug Johnson, vice president for risk management at the American Bankers Association.
http://www.nytimes.com/2009/11/29/business/29digi.html
There is no equivalent of Reg E in Europe, but zero liability appears to be the norm there also.
> … in the US, fraudulent ATM transactions, online banking
> and debit card payments are covered under Regulation E.
> This limits customer liability to $50.
Wow, I didn’k know that. Is this a federal regulation/law? Can you point me in some direction where can I find the relevant documents about this issue online?
> There is no equivalent of Reg E in Europe, but zero liability
> appears to be the norm there also.
I haven’t seen a bank in EU which practices customer zero liability. Please somebody corrects me if I’m wrong. But there’s an EU directive according to which by Nov 1 2009 all EU members had to adopt the law, that limits the customers liability in any unauthorised payment transactionsto up to maximum 150 EUR.
If anybody is interested her’s the directive, see article 61/I:
http://eur-lex.europa.eu/LexUriServ/LexUriServ.do?uri=OJ:L:2007:319:0001:01:EN:HTML
> Wow, I didn’k know that. Is this a federal regulation/law? Can you > point me in some direction where can I find the relevant
> documents about this issue online?
Yes, Regulation E is a Federal Reserve regulation. Banks in the US are bound by this.
http://www.fdic.gov/regulations/laws/rules/6500-3100.html
The more money a bank loses the more money the fed gives to the bank on loan, which turns interest rates and inflation up which in turn makes big banks more money in the long run….
There is this neat idea (in dutch with pics) http://webwereld.nl/nieuws/63504/ns-treft-opnieuw-maatregelen-tegen-skimmers.html
where the card reader is simplified and extends out of the machine. Unfortunately I have no idea about it or the company that came up with it.
Hi Matthew,
I’ve used those machines of the National Railway to buy train tickets, but the reader is still inside, the protruding part acts more like a guide, you place your card in there and slide it inside. This and the plates with random bumps will hinder the attachment of a skimmer and seem to be considered a success and at origin of a drastic reduction in skimmer attacks. However, I read they still had about 5 successful skimming incidents per week since the implementation. I can only guess how many incidents were BEFORE the introduction.
These skimmers are very scary. But my question is, do these act as a type of man in the middle on the atm?
If I insert my card to withdrawal money, will I still get my money?
You will get your money, after all they aren’t going after it directly because if you didn’t get your money and would be on the horn to the banks 1-800 number to tell them you didn’t recieve you cash from your withdrawl at the ATM. Now that would cause the bad guys a problem and call attention to them… not what they want… besides, they have your card information and PIN… they will get around to withdrawing the rest of your cash later…I would be more concerned with the cash they would take later then the bucks they would get at the ATM at that moment.
That’s what I figured. I knew it was the information that the skimmers get which is valuable. But I wasn’t sure if the transaction goes off seamlessly.
you still get your money, else it would alert the consumer to a problem. they take additional money when they have enough “tracks”
I don’t suppose Duracell will use this application for its TV commercials: “When ATM card skimmers need to get their signals to cell phone networks reliably, they choose Duracell batteries.”
I suppose they are breeding the new generation rabbit, the stuffed ATM rabbit, which can go, and go, and go….
I have a question: Does the device encrypt the tracks before it sms’s them?
I see him bringing up the whole honor among thieves “with whom you work” issue and it would seem prudent for the owner of the device to protect himself against everyone else in the foodchain. Obviously the installer could circumvent this on the device itself but would be more technically challenging that just switching the sim cards for your average hood.
Encryption would also seem to have a protective legal aspect if the sms’s themselves eventually become evidence.
I would also like to know more about the destination of the sms’s being sent. I imagine they dont just send it to another anonymous mobile they carry around with them pinging off their location.
It seems like the authorities could set up a kind of honeypot – a special card that they could use with the skimmer that would work for them just that one time.
But when the crooks tried to clone the cards and use them at an ATM, they have to stand in front of the camera. If they tried using them online for something, it would be even easier to track.
Just like drugs, the carders will use mules to move the skimmed cards around and pull money from the machines. That is “if” they pull the money themselves, they may be able to do an auth remotely to find balances and then sell the cards for a “potential” amount.
Or they need to have multiple special cards, the plastic equivalent of marked bills. The owner of the skimmer is not going to be standing in front of any cameras himself — he’s going to sell the data. If the majority of his data is fake numbers that immediately alert a bank about a fraudulent transaction, he’ll start losing customers.
He’s pretty confident he can cash out all the money when the skimmer is removed by the bank or the police. Presumably the bank knows immediately which numbers were compromised and can freeze the accounts. Again, anyone using a card with one of those numbers is going to call attention to himself. It takes time to either create a plastic card or to purchase something with a stolen number and have it shipped through a reshipping mule. Thieves who remove the evidence by taking their skimmer back don’t have to worry about the bank ever knowing it was there, but he seems to consider retrieving the skimmer to be an unreasonable risk to take.
The bank could even have a plainclothes employee make routine rounds on its ATMs daily or more often. To get around the problem of increasingly clever skimmer overlays, part of the inspection could be inserting a fake card coded to the particular machine, to see if any transactions start coming in with that number.
I just love the “you lose money” and “you have the right to work in another country” comments.
Its this sense of entitlement to steal that irks me so much.
The advantage for the fraudster, that he doesn’t have to come back, is not that big; as long as the police knows how to react.
they have to wait for a few people using the ATM (or make some fake transactions) and the cell phone network will tell them the phone number and, more important, the location of the receiving cell phone. from that point the police shouldn’t need much help.
of course the fraudster could by-pass this situation, but he could avoid most of the counteractions as long as he is able to modify the ATM, use technology, and leave the location.
His cell phone doesn’t have to be on all the time. He could switch it on, receive the SMS messages, and turn it off giving no time to triangulate his position.
but when the police knows the number, they should be able to find out when and where the mobile phone was turned on. I didn’t say it is foolproof. but GSM based ATM skimmers aren’t foolproof either.
The best thing is “hardening” the ATM.
That would only give you a radius of several km to even 30km around the base station that the phone used to receive the messages. Then what?
I think this depends on the specific environment, situation and technique.
But there is also a legal aspect.
Google voice and other services allow you to receive SMS messages online. Then you simply go to the local starbucks coffee shop, connect via wifi, use a free anonymous proxy, login to google voice and download all your card numbers. Good luck catching that guy!
What about building in small, low power GSM blockers inside the ATM’s?
The power should be low enough not to interfere with the surrounding but powerfull enough to block a cell phone right next to the ATM.
Of course the limiting factor is the price of equipping every ATM.
I imagine more than the costs involved would be the legal cloud surrounding gsm jamming. The jammers themselves are relatively cheap and widely available from Chinese suppliers however the use of them has quite serious legal implications.
not sure where you are based but i know of a department store and a book store i frequent that use jammers…you walk through their doors and loose signal instantly…how many shoppers would even realise or really care if they even twigged that the store was jamming their ph reception?
“The jammers themselves are relatively cheap and widely available from Chinese suppliers however the use of them has quite serious legal implications.”
If GSM jammers are cheap and available, if you need to use the ATM, why not take onewith you as a precaution against GSM scanners? At least YOU wouldn’t be scanned.
Are they also illegal to use in this fashion. Of course, if you are that smart, you are probably going to detect a scanner, n’est pas?
This won’t work probably. While your jammer may succeed in blocking the SMS while you are near the ATM, the device may just retry sending the SMS later, once you walked away from the ATM.
So you will only get one or two minute delay before fraudsters gets your card details with PIN.
Seller is talking crap, because when police or bank service takes off skimmer, they immediately block all cards what have been used in that ATM for time from last check(when collector accessed atm and last time seen it without skimmer).
So you will lose those 8-12k EUR anyway. And that price for that crap is to big, to make skimmer like that you need no more than 1k eur and brains.
And the story about black jeeps and 120 tracks is absolute idiotic. Thats all the marketing to sell crap for big money, good skimmers never go for public and never go for sale. If you buy this skimmer you need 99% luck to earn some money. 90% that you will not get back you money and lose that skimmer.
Also there are a lot of antiskimming devices in ATMs who works with GSM and detects.
Hi BadBisBack, may you tell me which kind of antiskimmer are better to protect EU ATMs ?
I don’t know why I just came across this article, but it going in my security awareness training program.
Thanks Brian.
P.S. Heard you on Pauldotcom
i could give you my card and my pin number and you could never withdraw money from my account. I have two accounts – one is not linked to the card. It holds my funds. i just transfer funds as required to the account that is linked to the card and then withdraw funds immediately and keep the account that is linked to the card at zero balance. In this day and age of phone banking and mobile internet banking it is of no inconvenience to protect your accounts this way. Also, even if i gave my internet banking login details to you, you could never transfer to your account as all withdrawls need an approval code sent to my cell phone.
I search only electricalnod. who has it, please to announce. on youtube. look on youtube=spycar1000
Brilliant. Yet, why are these third world countries still using the “track”, where every country in western europe are using EMV based cards. Magnetic tracks are obsolete and unsafe, just get rid of them and this type of skimming will be obsolete.
With EMV, you need the card, you can’t easily copy the SIM.
Problem solved.
True, but all of my cards still use magnetic strips in the USA.
The banks just don’t want to doll out the money to upgrade their ATM hardware AND essentially ‘teach’ the consumer how to use their card. So, they put off that upgrade in the US until later.
“why are these third world countries still using the “track””.
you really have no idea of what you’re talking about.
try searching for brasil + PCI.
(IT security analyst for major bank in brazil here).