Cyber thieves stole $217,000 last month from the Metropolitan Entertainment & Convention Authority (MECA), a nonprofit organization responsible for operating the Qwest Center and other gathering places in Omaha, Nebraska.
 Lea French, MECA’s chief financial officer, said the trouble began when an employee with access to the organization’s online accounts opened a booby-trapped email attachment containing password-stealing malware.
Lea French, MECA’s chief financial officer, said the trouble began when an employee with access to the organization’s online accounts opened a booby-trapped email attachment containing password-stealing malware.
The attackers used MECA’s online banking credentials to add at least six people to the payroll who had no prior business with the organization. Those individuals, known as “money mules,” received fraudulent transfers from MECA’s bank account and willingly or unwittingly helped the fraudsters launder the money.
French said the attackers appeared to be familiar with the payroll system, and wasted no time setting up a batch of fraudulent transfers.
“They knew exactly what they were doing, knew how to create a batch, enter it in, release it,” she said. “They appear to be very good at what they do.”
Prior to the heist, MECA refused many of the security options offered by its financial institution, First National Bank of Omaha, including a requirement that two employees sign off on every transfer.
“We had declined some of the security measures offered to us, [but if] we had those in place this wouldn’t have happened to us,” French said. “We thought that would be administratively burdensome, and I was more worried about internal stuff, not somebody hacking into our systems.”
MECA was able to reverse an unauthorized wire transfer for $147,000 that was destined for a company called Utopia Funding U.S.A. The organization was not as lucky with the remaining transfers.
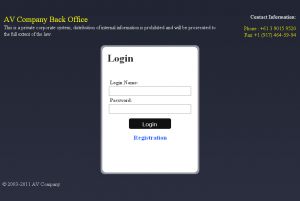 The funds stolen from MECA were sent to money mules recruited through fraudulent work-at-home job offers from a mule recruitment gang that I call the “Back Office Group.” This gang is one of several money mule recruitment outfits, and they appear to be among the most active. Like many other mule gangs, they tend to re-use the same format and content for their Web sites, but change their company names whenever the major search engines start to index them with enough negative comments to make mule recruitment difficult.
The funds stolen from MECA were sent to money mules recruited through fraudulent work-at-home job offers from a mule recruitment gang that I call the “Back Office Group.” This gang is one of several money mule recruitment outfits, and they appear to be among the most active. Like many other mule gangs, they tend to re-use the same format and content for their Web sites, but change their company names whenever the major search engines start to index them with enough negative comments to make mule recruitment difficult.
The mules used in the MECA heist were recruited through a Back Office Group front company named AV Company. Mules were told they were helping the company’s overseas software engineers get paid for the work they were doing for American companies. In reality, the mules were being sent payments to transfer that were drawn on hacked accounts from victims like MECA.
More than $9,000 of MECA’s money was sent to Erik Rhoden, a resident of Fleming Island, Fla. Rhoden was recruited in June by the Back Office Group. Rhoden successfully transferred the funds to three individuals in Eastern Europe, but says he didn’t profit from the work. His story matches that of other mules recently recruited by Back Office, and indicates a devious shift in tactics which ensures that mules never receive a payment for their work.
Typically, the Back Office group had instructed mules to withdraw transfers in cash, pocket eight percent as a commission, and wire the remainder of the funds to specific individuals overseas. Recently, the Back Office group changed its policy, and began telling mules to transmit the entire amount. In place of commissions, mules are now promised a payday at the end of the month. That payday almost never comes.
“They said I was going to get benefits, a salary, and a bonus for each transaction, but that was all a lie,” said Rhoden, who recently landed a job as a drink server in a local bar.
MECA lost more than $70,000 from the heist, although French said she believes their Travelers cyber security policy will help recoup some or all of the loss.
“We have a $25,000 deductible, plus the cost of an ongoing forensic investigation, which is going to be pretty expensive,” she said.
MECA has since added more security features to its online banking account, and access to that account is only possible through a locked-down, dedicated computer.
“All of this is a day late and a dollar short, I guess,” French said. “Why isn’t someone out shouting on the rooftops about this fraud? People need to understand how exposed they are.”




Correct me if I’m wrong:
1. Bank proposes security procedures that protect clients from fraud. Banks generally do such things because there’s been a lot of similar fraudulent activities and want to be proactive.
2. The CFO of MECA refuses company bank’s offers of extra security. Supposedly the bank offered a number of options.
3. Fraud occurs.
4. The CFO cries that they never knew about increasing chances of fraud.
Yes, I really feel for the CFO. Absolutely.
Hi Saso. Your point is well taken. I’ve sought to raise awareness about these attacks, by highlighting both the failings of the banks and of the victim organizations. Clearly, this is a case where the organization dropped the ball, and it’s refreshing that they were up front about that.
Heh, I was just about to comment that, indeed, it’s refreshing that the organisation was up front about it. I guess the fact that they’re not-for-profit means these admissions do less damage that it potentially might for say a Limited Liability company with shareholders but still – refreshing.
It’s crazy that they actually turned down their bank’s security procedures when offered. I suppose this is one situation where you really cannot blame the financial institution.
We have seen heists in other cases where people accepted the bank protections, the same thing happened, the bank obviously in violation of their own protections, judge ruled the bank security adequate, even though it violated these offerings, which are apparently to get more income for the bank in client fees, and not to provide any more meaningful security.
Clearly the gangs pulling those heists are skilled, determined and not likely to give-up easily. But it’s disconcerting that widespread lack of awareness makes their misdeeds that easy.
– business owners are not aware of how sophisticated and determined those attacks can be. Some, I think, might not be even aware that their business accounts do not enjoy the same legal protection as personal accounts.
– so many people that do not realize they are being recruited to become money mules. Those who do and pull-back do not report the recruiting attempt (where could be reported if you suspect it?) in time.
It is just sad child criminals and rapists keep frontlines for weeks instead of being locked away and never heard from them while stories of cyberheists receive appropriate coverage just in smaller, specialized, media outlets.
A 1-page brochure outlining the risks, complete with victim examples could be given to those who decline the extra security measures. That would be the equivalent of shouting from the rooftops.
The problem with that idea is people do not read the materiel given to them by banks or any other organization. If you do read that information I tip my hat to you because you are in a very small group.
I am impressed that MECA admits to some of the blame for this.
I’m always curious as to what WOULD have made a person/company take those precautions in advance. What could the bank have said to change the organization’s mind? What do we say to friends, relatives, co-workers who also see security measures as “administratively burdensome” ?
This is a societal issue that has emerged as a result of the cyber-revolution we are in. There are concepts about our new cyber environment that we do not understand. The accelerating speed of change is one, the concept of digital data having value is another.
>I’m always curious as to what WOULD have made a person/company take
>those precautions in advance. What could the bank have said to change
>the organization’s mind?
“In order to do business with us you must use a separate pinpad+card reader to authorise transactions” tends to work pretty well. At least that’s what the banks here have done.
(I must say I’m pretty surprised that they turned down the additional security measures that were offered by the bank. I guess that’s why the banks didn’t give users a choice).
Brian,
Any chance of you providing an example (without the payload, natch) of the email which the unwitting bank employee opened, thus starting this whole caper?
Ed
I can at least give you a sample of the nasty stuff that comes to employees. Receive this literally a few minutes ago, redirect to some malware not really certain what variant yet:
Below is a typical malware delivery approach:
“We hereby inform you that you are infringing on copyrighted material,
I represent Phoenix Meresis/MBS LP. It has come to my attention that you have used and/or published on your website
(commencing on or about May 18, 2011, pursuant to our information and good faith belief) and continue to publish without
permission a number of pieces owned by Phoenix Meresis (webpages, text, images, animated clips, source code, etc.) at your site including,
but not limited to, the following url references cited below.
INDEX OF YOUR INFRINGING WEBPAGES:
Mark Wahlberg,
Bretz & Coven, LLP
The above email address is extremely effective, and tends to result in employees clicking it. Now I get to go see who all clicked the link and needs a re-image.
Another day, another dollar stolen. Sad that this is so rampant now.
Whoops, didn’t mean to reply to your post with my previous comment.
Was that email directed to the legal department, or did your spam filtering catch it?
My thinking is, say a regular employee gets it. Is policy to forward that to a manager or some other department? I would think maybe an employee trying to be helpful would click on it I guess, but then that breaks the standard rules of “Don’t click on attachments or links in emails”.
It just sucks that no matter what we do, human error will always factor into this.
The email was delivered to a random subset of employees, pretty much from what I can gather harvested addresses. It is actually company policy to delete these things or report them to Security prior to opening them. Unfortunately this made it through the spam filters, but we caught it in time to stop anyone from opening it.
The beauty of this one is that it seems so urgent and terrifying that employees tend to send it right away to whatever manager/exec they think can address it. The urgency tends to make them forget their basic training.
Your exactly right human error is my daily headache.
A person in the accounting department receives an e-mail claiming to be from the Better Business Bureau regarding a complaint they have received about your company. Details of the complaint in the attached document.
Employee clicks on it, can’t get it to open. This installs keylogger instead.
Employee forwards it to co-workers. Ditto happens.
Company receives an e-mail, allegedly from Post Office, UPS, or Fed-X, or some truck company, about problems making a delivery from the company. Details are in the attachment, or the url.
Same story as I earlier shared.
where does it say the bank employee is the person who caused. Not trying to be mean I just don’t remember Brain saying anything of the kind.
The CFO said he was “hacked”….no, he wasn’t “hacked”, one of his employees was stupid enough to open an email attachment that they should have known better not to open.
If he had been “hacked” I would have had more sympathy. It’s basic stuff, never open attachments from unknown sources. AND, run firewall software that notifies you of suspicious outbound connections.
And regardless of the mules recieving earnings or not from fraud, they shoudl be prosecuted to the fullest extent of the law. Nobody holds a gun to their heads and forces them to transfer the money once they find out what their job entails; they are criminally liable for their actions.
@cherry: “AND, run firewall software that notifies you of suspicious outbound connections.”
A decade or so ago that was a really great idea. Then malware found out how to lie to the OS about what it was, or infect the browser, or just subvert the whole OS. As far as I know, detecting “suspicious outbound connections” nowadays is essentially useless.
It’s still a good idea, especially if done on the network, but even if done locally. Eventually, the malware has to DO something, and that is often something that can be detected and/or prevented. It’s not 100%, these things rarely are, but you’d be surprised how much malware breaks with something as simple as egress filtering or a non-transparent authenticating proxy.
@Matt: “Eventually, the malware has to DO something, and that is often something that can be detected and/or prevented. It’s not 100%,”
My guess would be more like 30 percent, but how do we check for 100 percent or 30 percent or even less? Infection we cannot detect is still there, even if we cannot count it.
When we cannot detect infection it is easy to claim there is none, but that does not make it so. There is no tool which guarantees to tell us. To assure security, we are forced to assume the worst, not the best.
@Cherry: “And regardless of the mules recieving earnings or not from fraud, they shoudl be prosecuted to the fullest extent of the law. Nobody holds a gun to their heads and forces them to transfer the money once they find out what their job entails; they are criminally liable for their actions.”
Whilst certainly ignorance should not be a defence I find you’re attitude extreme and simply advocating unfair punishment and hardship upon people who were acting in good faith.
There is a reason that most of the civilized world doesn’t legislate mandatory sentences for many types of crimes – there are always circumstances, intent, the accused persons place and role in society (for example a mother to young children) and yes, ignorance to consider. The reason is it is unjust to prosecute someone for money laundering and then call for the “full extent of the law” to apply – 10 years in jail for example – when they have been decieved and tricked themselves.
I’m afraid I cannot find the sources for this but maybe someone else can, some time ago researchers attempted this exact same technique (tricking users into clicking links or opening attachments in emails) against various people in the computer security industry and the number of people that were duped was extremely high, around the same as any other employees actually. Basically even people that *should know better and spend their life telling people not to* will open links or attachments given the right message.
>It’s basic stuff, never open attachments from unknown sources.
This may have been valid ten years ago, but since the bad guys have known about it for years and bypass it by infecting your friends and having them spam out the malware to you, it hasn’t worked for awhile.
I appreciate the CFO being totally upfront about what happened rather than playing the helpless victim. She acknowledged exactly what happened and how they failed which is refreshing for a change. They are one of the luckier victims IMO considering the final amount lost in comparison to other small to mid-sized businesses and non-profits.
Hopefully there will be a big takeaway for them as to how to secure their online banking transactions going forward. I also hope they consider a dedicated computer with a Linux distro used solely for banking.
My favourite sentence in the article :
“MECA has since added more security features to its online banking account, and access to that account is only possible through a locked-down, dedicated computer.”
Common sense has prevailed. They actually have a locked-down dedicated computer.
Now they need to pass their story on and hopefully stop this happening to others. Learn from other peoples mistakes. I take my hat off to MECA for admitting some of the blame.
Hi Brian,
The article doesn’t mention if the email was spoofed from MECA’s internal domains or not. I’ve witnessed this trend decreasing over the years especially for the higher end targeted stuff. But I feel it’s still a common enough tactic that I blogged about a way to use an Outlook/Exchange infrastructure to help detect such tricks for the average click-first-ask-questions-later user BEFORE and AFTER they open the email in Outlook. The blog entry is located here http://scottfromsecurity.com/blog/2011/05/28/detecting-spoofed-emails-using-only-outlook-rules/
** PS. Not sure if you allow links to a commenter’s own content, I’d understand either way. Although as a heads up I get no advertising or donation revenue from that site. Just trying to help **
Thanks
I’m guessing the change in payment method for the mules was because banks (and probably Western Union offices) have notices posted describing the typical scam. Those notices likely specifically mention “jobs” that entail keeping a percentage of the money being transferred as one’s own salary.
Perhaps too many mules were getting a last-minute education and refusing to transfer the money.
Perhaps the company should consider how the perpetrators knew about the procedures for setting up employees on the payroll. Is this (in part) an inside job?
Regards,
Many companies use a standard payroll system, with standard options, menus.
If the e-mail payroll included a keylogger, and reached an employee who works on it, the enemy could very rapidly have figured out what standard system it was, seen menus of options, and got the password of the person who works on it. With other malware they could have got access to the actual payroll files, with abilities to update contents without going thru the standard programs.
Most standard payroll systems come with documentation which can be viewed by people who do not have a license to use that software.
@Robert Scroggins “an inside job?”
In effect, the eThief IS inside. If I were the eThief, I would have watched an entire payroll cycle, or at least waited until I gathered enough information to carry out the theft without error. If the eThief has enough authority to add employees and transfer money he also has enough authority to read all the documentation on payroll procedures.
It is interesting to note that French had said that the organization had declined to follow the security advice because the processes for handling transfers would be “administratively burdensome.”
I wonder now if French considers it more “administratively burdensome” to stand in front of the media to explain just why they didn’t follow a process that may have prevented the crime in the first place?
I think this is the only thing that will shift most organizations way of doing things to a safer paradigm. They have to get hit and get hit hard or they just won’t change the way they do things. RSA is still being hurt by a policy where they didn’t shift to Thunderbird or some other MUA that doesn’t render HTML. What would have happened if RSA had done that?
@Robert Scroggins: I suspect that a lot of those procedures are consistent across various companies. It’s easier for auditors to determine if a nonprofit is operating ethically if they don’t make up their own procedures.
It seems generally bad when my city makes the news. 🙁
“….I was more worried about internal stuff, not somebody hacking into our systems.”
Hey, send me a job app. I want to work at a place that thinks like that. Informed about security threats and strong in its relationships to its peons, er employees.
I’m curious if the individual who opened the attachment had local admin rights on his/her machine.
Earlier in this thread it says that the keylogger is getting installed upon receiving one of these emails and “the employee clicks on it, can’t get it (link) to open. This installs keylogger instead.”
Okay, I am missing something here. How does this keylogger get installed without a warning from the OS or Browser or email client or something “are you sure you want to install this software?” How does it get around this, or does it warn them, but the user just clicks “OK” and it installs it? Does it depend on the version of Windows?
Doug
If you have ever worked “help desk” where a person has a computer problem and needs a technician to guide them, it is extremely common that there were error messages or pop-ups with specific text, but the person with the problem cannot remember what the text said, even a few minutes later.
Occasionally, I have remotely accessed log of activity of person calling me. I find a specific error message, and ask “When you got that message, what did you do?” and they are in denial they got that message.
Click thru, without reading the text, is so pervasive, some capabilities should be disabled for some users, if practical.
In the case I heard about 3rd hand, the company did not know they had a problem until the bank accounts got drained, then tried to reconstruct how it happened.
Multiple employees had failed to open the attachment, so then they called the Better Business Bureau for details, but there were no complaints against them, so at that point they quit everything. It did not occur to anyone that the bogus e-mail might be suspicious, should be reported to anyone.
Doug
Again in the case I heard about 3rd hand, the PC which had got infected.
Some unknown time before the infection, there had been some other software knowingly installed by the user – I not know what, which asked the user to disable PC security so it could be installed. PC security was never re-enabled afterwards.
We recently blogged about a set of emails that do just what is described in the article. The post also links out to this article since I have always admired Brian’s work. We show the traffic for all of the exploit attacks and a sample of the configuration sent to the running trojan.
http://www.barracudalabs.com/wordpress/index.php/2011/08/27/how-a-linkedin-notice-could-empty-your-bank-account/