Experts from across the security industry collaborated this week to quarantine more than 110,000 Microsoft Windows PCs that were infected with the Khelios worm, a contagion that forces infected PCs to blast out junk email advertising rogue Internet pharmacies.
Most botnets are relatively fragile: If security experts or law enforcement agencies seize the Internet servers used to control the zombie network, the crime machine eventually implodes. But Khelios (a.k.a. “Kelihos”) was built to withstand such attacks, employing a peer-to-peer structure not unlike that used by popular music and file-sharing sites to avoid takedown by the entertainment industry.
Update, 11:07 a.m. ET: Multiple sources are now reporting that within hours of the Khelios.B takedown, Khelios.C was compiled and launched. It appears to be spreading via Facebook.
 Original post: The distributed nature of a P2P botnet allows the botmaster to orchestrate its activities by seeding a few machines in the network with encrypted instructions. Those systems then act as a catalyst, relaying the commands from one infected machine to another in rapid succession.
Original post: The distributed nature of a P2P botnet allows the botmaster to orchestrate its activities by seeding a few machines in the network with encrypted instructions. Those systems then act as a catalyst, relaying the commands from one infected machine to another in rapid succession.
P2P botnets can be extremely resilient, but they typically posses a central weakness: They are only as strong as the encryption that scrambles the directives that the botmaster sends to infected machines. In other words, anyone who manages to decipher the computer language needed to talk to the compromised systems can send them new instructions, such as commands to connect to a control server that is beyond the reach of the miscreant(s) who constructed the botnet.
That’s precisely the approach that security researchers used to seize control of Khelios. The caper was pulled off by a motley band of security experts from the Honeynet Project, Kaspersky, SecureWorks, and startup security firm CrowdStrike. The group figured out how to crack the encryption used to control systems infected with Khelios, and then sent a handful of machines new instructions to connect to a Web server that the researchers controlled.
That feat allowed the research team to wrest the botnet from the miscreants who created it, said Adam Meyers, director of intelligence for CrowdStrike. The hijacking of the botnet took only a few minutes, and when it was complete, the team had more than 110,000 PCs reporting to its surrogate control server.
“Once we injected that information in the P2P node, it was essentially propagating everything else for us,” Meyers said. “By taking advantage of the intricacies of the protocol, we were providing the most up-to-date information that all of hosts were spreading.”
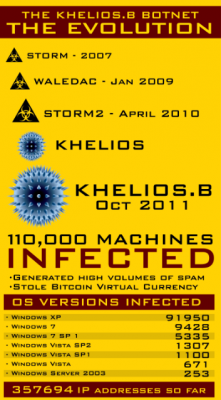
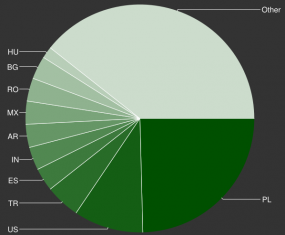
The group is now working to notify ISPs where the infected hosts reside, in hopes of cleaning up the bot infestations. Meyers said that, for some unknown reason, the largest single geographic grouping of Khelios-infected systems – 25 percent — were located in Poland. U.S.-based ISPs were home to the second largest contingent of Khelios bots. Meyers said about 80 percent of the Khelios-infected systems they sinkholed were running Windows XP, an increasingly insecure operating system that Microsoft released more than a decade ago.
It remains unclear whether this offensive action will stick: It comes close on the heels of a similar campaign waged by Microsoft last year, which targeted an earlier variant of Khelihos. Within weeks of the Microsoft effort, the miscreants responsible for the botnet rebuilt the network, deploying the Khelihos.B variant that was the subject of this week’s takedown.
Khelios shares a major portion of its code with the Waledac worm, an extremely virulent P2P worm that also forced infected systems to spread bogus Canadian pharmacy spam. It is also widely considered to be the grandchild of the Storm Worm. All three computer worms were responsible for pushing fake antivirus software, as well as spam promoting flight-by-night Internet pharmacies.
The research team behind this latest takedown said they were confident that Khelios was being deployed to victim PCs via so-called pay-per-install schemes, in which hackers who control huge numbers of compromised machines rent them out for malware installs to other miscreants.
It remains unclear who is responsible for either version of Khelihos, but all signs point to a hacker who uses the alias “Peter Severa.” In July 2011, I published a story showing that Severa was running a pay-per-install program that paid affiliates commissions for frightening Internet users into installing and paying for fake antivirus software. As it turns out, the malware that Severa asked his affiliates to distribute installed two components: A fake antivirus tool, and a version of Khelios.B, the very malware targeted in this week’s takedown. In a follow-up investigation published in January 2012, I presented evidence that Severa is the same individual responsible for the Waledac and Storm worms.
Reached via the same instant messenger address that he uses to advertise his spam and fake antivirus schemes on underground forums, Severa denied ever using spam botnets or spreading fake AV.
Update, Mar. 29, 5:47 p.m. ET: Facebook released the following statement about reports that Khelios was spreading via the social network.
“Kelihos is not spreading on Facebook, but is being dropped by a separate botnet, Fifesoc, which we have been monitoring for several weeks. We have been proactively remediating any infected users in our malware checkpoint, and users can detect and remove the virus themselves by running an updated anti-virus product.
We are in active discussion with researchers attempting to eliminate the threat, and have been largely successful at blocking message spam being sent by this botnet since it was first detected. We are still investigating the issue further, and will continuing iterating on our systems until Facebook has completely mitigated this threat. As of yet, the campaign has been largely ineffective at spreading on Facebook and only an extremely small percentage of users have been infected. Fifesoc also spreads through other social media websites, and as always, we encourage people to not click on suspicious links and report any spam they observe on the site. You can find more ways to protect yourself on Facebook here: http://www.facebook.com/




What is Bitcom virtual currency? or should that read Bitcoin in the graphic?
yep. just updated the graphic, tx.
with the plethora of different payment systems out there, bitcom could have been the name of one. interesting news as always.
Seems like the botmaster’s rxn is yet another good reason to defer or avoid use of Facebook for awhile, or at all….
Yes:
But I’m posing it on Facebook anyway, for the benefit of my clients.
Should we also be concerned that the encryption scheme was so easily cracked for the group to take control of this bot-net? Or were the criminals just using a weak type of encryption?
Another excellent article by the way; very interesting!
Most encryption offers a smaller security buffer than people realize.
Take AES for example, one of the strongest ciphers and yet fatally flawed. It’s vulnerable to cache timing attacks over the network, and there’s even a hole that allows someone who can run a program on the same machine to recover the AES key in I believe under a minute. And that’s AES — imagine the weaknesses in many (but not all!) other ciphers. 🙂
Thanks Nic, good post;
I’m familiar with that, but good information for others tuning in. I hope that is what the crooks were using?!
Another great article Brian!
I do enjoy reading just about everything you blog about! 🙂
By the way, will you please acknowledge receipt of the email message I sent to you recently. TIA,
David
Websites should prepare for such bot nets, since not only do PC users fall victim to fraud by crimeware. The same bot nets assist in automatic fraud against websites. This type of activity may be spotted by web anomaly detection systems, capable of noticing deviation in user actions. Hybrid Telepath profiles user behavior and alerts upon suspicious activities.
Brina – good post and good site – bookmarked you.
Perhaps with the continual malaise being exhibited by many PC users who don’t seem to get the basic parameters of ‘staying safe’ on the net – all PC’s should have a start-up screen warning them what not to do 🙂