If the miscreants behind the ZeuS botnets that Microsoft sought to destroy with a civil lawsuit last month didn’t already know that the software giant also wished to unmask them, they almost certainly do now. Google, and perhaps other email providers, recently began notifying the alleged botmasters that Microsoft was requesting their personal details.
Microsoft’s unconventional approach to pursuing dozens of ZeuS botmasters offers a rare glimpse into how email providers treat subpoenas for account information. But the case also is once again drawing fire from a number of people within the security community who question the wisdom and long-term consequences of Microsoft’s strategy for combating cybercrime without involving law enforcement officials.
Last month, Microsoft made news when it announced a civil lawsuit that it said disrupted a major cybercrime operation that used malware to steal $100 million from consumers and businesses over the past five years. That legal maneuver may have upset some cyber criminal operations, but it also angered many in the security research community who said they felt betrayed by the action. Critics accused Microsoft of exposing sensitive information that a handful of researchers had shared in confidence, and of delaying or derailing international law enforcement investigations into ZeuS Trojan activity.
Part of the controversy stems from the bargain that Microsoft struck with a federal judge in the case. The court granted Microsoft the authority to quietly seize dozens of domain names and Internet servers that miscreants used to control the botnets. In exchange, Microsoft agreed to make every effort to identify the “John Does” that had used those resources, and to give them an opportunity to contest the seizure. The security community was initially upset by Microsoft’s first stab at that effort, in which it published the nicknames, email addresses and other identifying information on the individuals thought to be responsible for renting those servers and domains.
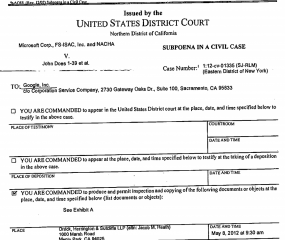
And then the other shoe dropped: Over the past few days, Google began alerting the registrants of more than three dozen Gmail accounts that were the subject of Microsoft’s subpoenas for email records. The email addresses were already named in Microsoft’s initial complaint posted at zeuslegalnotice.com, which listed nicknames and other information tied to 39 separate “John Does” that Microsoft is seeking to identify. But when Microsoft subpoenaed the email account information on those John Does, Google followed its privacy policy, which is to alert each of the account holders that it was prepared to turn over their personal information unless they formally objected to the action by a certain date.
According to sources who received the notices but asked not to be named, the Google alerts read:
“Hello,
Google has received a subpoena for information related to your Google
account in a case entitled Microsoft Corp., FS-ISAC, Inc. and NACHA v.
John Does 1-39 et al., US District Court, Northern District of California,
1:12-cv-01335 (SJ-RLM) (Internal Ref. No. 224623).To comply with the law, unless you provide us with a copy of a motion
to quash the subpoena (or other formal objection filed in court) via
email at google-legal-support@google.com by 5pm Pacific Time on May
22, 2012, Google may provide responsive documents on this date.For more information about the subpoena, you may wish to contact the
party seeking this information at:Jacob M. Heath
Orrick, Herrington, & Sutcliffe, LLP
Jacob M. Heath, 1000 Marsh Road
Menlo Park, CA 94025Google is not in a position to provide you with legal advice.
If you have other questions regarding the subpoena, we encourage you
to contact your attorney.Thank you.”
Unlike most of its competitors in the Webmail industry, Google is exceptionally vocal about its policy for responding to subpoenas. This has earned it top marks from privacy groups like the Electronic Frontier Foundation (EFF), which recently ranked ISPs and social media firms on the transparency of their policies about responding to requests for information filed by the government or from law enforcement.
Google spokeswoman Christine Chen said she could not comment on specific legal cases, but said the company complies with valid legal process.
“We take user privacy very seriously, and whenever we receive a request we make sure it meets both the letter and spirit of the law before complying,” Chen said. “When possible and legal to do so, we notify affected users about requests for user data that may affect them. And if we believe a request is overly broad, we will seek to narrow it.”
At least 15 of the email accounts named in Microsoft’s lawsuit were addresses at hotmail.com or msn.com, both free Webmail services run by Microsoft. It’s not clear whether Microsoft gave those account holders a heads up about the subpoena. I asked Richard Boscovich, the former Justice Department lawyer and one of the architects of Microsoft’s legal strategy to target botnets with civil actions; he didn’t know, and referred me to Microsoft’s compliance unit. I’m still waiting for an answer. But it’s worth noting that Google was the only email provider on EFF’s list that was recognized for reliably alerting users about data demands. Microsoft was not recognized on this front.
Marcia Hofmann, a senior staff attorney with the EFF, said Microsoft’s legal effort underscores the tension between traditional law enforcement processes and companies using civil litigation to protect their own users and to vindicate their own interests.
“I suspect this is a situation where Microsoft feels law enforcement isn’t moving quickly enough,” Hofmann said. “But it also basically compromises law enforcement’s ability to do anything about the problem, and makes it possible for the suspects to evade any sort of law enforcement action.”
CUT-AND -PASTE JUSTICE?
Critics of the Microsoft effort say certain clues prove that the company borrowed and published raw intelligence without fully understanding the data’s true value and origins. Andy Fried, a former law enforcement official and owner of the Alexandria, Va. based security consultancy Deteque, was a co-founder of the little-known ZeuS Working Group, an ad hoc and extremely secretive collection of law enforcement officials and private security professionals dedicated to tracking ZeuS activity with the aim of bringing those responsible to justice.
“A basic tenet of this trust group is that everyone feels free to share data, but the rule is you never release that data outside of the trust group without express permission of whoever provided the data,” Fried said. “But there was no way that the data Microsoft published was received independently. Much of it was cut-and-pasted verbatim, and some of the data included in the search warrant was horrifically out of date.”
For instance, several of the key crime lords that Microsoft is seeking to unmask are already in prison for their crimes. John Doe #22 in Microsoft’s complaint — alleged to have used the nickname “Jonni” — is none other than Yevhen Kulibaba, a Ukrainian man arrested in London in 2010 and named as a ringleader of a money mule recruitment gang there. Kulibaba is currently serving a four-year jail sentence in connection with the ZeuS activity.
Microsoft said John Doe #23 goes by the alias “jtk,” yet this was the nickname used by Yuriy Konovalenko, the 30-year-old accomplice of Kulibaba who also was arrested as part of the U.K.-based ZeuS gang. Konovalenko likewise was sentenced to four years in jail.
Microsoft’s John Doe #24 is thought to go by the nickname “Veggi Roma,” but according to sources familiar with the case, this was an inside joke based on a lucky break that led police to the U.K. gang’s location. Investigators in London had been working with the FBI to monitor the communications of several members of the London-based ZeuS gang, but for some time they did not know whereabouts of the men, who were known at the time only as Jonni and Jtk. That is, until Jtk used his Internet connection to order a pizza to be delivered to their apartment. A “Veggi Roma” pizza, to be exact.
Astute readers may be wondering how it is that Google’s emails and Microsoft’s subpoenas to the John Does named in the complaint are now public. According to Fried, that’s because some of the email addresses listed in Microsoft’s complaint as belonging to John Doe miscreants were in fact addresses used by security researchers who had registered domains to serve as “sinkholes” for one or more ZeuS botnets. Sinkholing is a practice by which researchers redirect the identification of the botnet control servers to their own server, so that malicious traffic that comes from each bot-infected client goes straight to the research box, ready to be analyzed.
COLLATERAL DAMAGE
Microsoft maintains that it worked with several security industry partners, and that it was operating under the assumption that the information those partners provided was either their own, or was freely available amongst them for the purpose of securing the Internet.
Microsoft’s Boscovich said the company did not work with law enforcement on this operation, and so had no idea whether there were ongoing or adjudicated investigations related the John Does named in its case. He emphasized that protecting customers was the company’s number one priority.
“Our main objective was to stop the bleeding, and everything we do is specifically related to that mission,” Boscovich said. “Congress specifically envisioned that it was and is appropriate for private entities to protect themselves and their interests, and as in this case, the interests of our customers. People are continuing to be victimized, computers compromised, identities stolen, and now those systems are posing a threat to other people on internet, irrespective of what operating systems they’re using.”
For his part, Fried said he believes Microsoft will soon find it more difficult to obtain sensitive information that security researchers and law enforcement gather about key cybercrime suspects. He also fears that the ZeuS working group and other informal information-sharing groups may disband or become less effective as a result of this case.
“Microsoft discounted everyone but themselves with their initial action, and they’ve compounded things pretty quickly with these subpoenas,” Fried said. “This is also going to cause collateral damage for a lot of trust groups, while all that they’ve accomplished is little more than a very miniscule inconvenience to the bad guys, whose servers were back up within 24 hours of the takdeowns.”
Jon Praed, founding partner of the Arlington, Va. based Internet Law Group, said he’s sympathetic to Microsoft’s position, and believes Google should have taken the trouble to investigate whether the John Doe accounts named in Microsoft’s lawsuit deserved to be notified.
“Unfortunately, most email providers have a one-size-fits-all privacy policy,” Praed said. “All of these companies have tried to create the legal right to do the right thing, but they’re making almost no attempt to apply that policy in practice. At the same time, Microsoft is spending a tremendous amount of money trying to stop this activity, and I don’t know anyone else out there who is even trying to do this.”






“At the same time, Microsoft is spending a tremendous amount of money trying to stop this activity, and I don’t know anyone else out there who is even trying to do this.”
Sorry, this statement makes me angry. Dear Jon Praed, because you don’t know or understand something does not mean it doesn’t exist. Your knowledge of something is not the indicator of existence.
While Jon needs no help from me, he has been at this business for a decade. I worked with him regarding this issues 5 or 6 years ago, and all we still keep doing is playing wack-a-mole with these b**tards.
In fact, isp’s, card processors, banks, e mail service providers, all kinds of companies have been getting paid enough to turn a blind eye to these problems, or at least ignore them. Look at the spam studies by UC San Diego and UC Berkeley referenced here an elsewhere. We know where the problems are, and Jon has been after them ever since I have known him.
Companies are building bigger, thicker castle walls trying to keep out the barbarians. The barbarians keep lobbing in cannon balls. Its time to take the fight to them, and stop just playing defense.
My thoughts on this are more nuanced than Brian’s quote could capture. Kyle, I’m happy to talk by phone if you’d like.
MS certainly has an obligation to respect confidentiality of data sharing within the community, and perhaps MS could have done a better job of respecting those confidences. That wasn’t the thrust of Brian’s article, however, which instead was focusing on Google’s notice sent to email accounts accessible to bad guys (thus, giving them notice MS was onto them).
Perhaps MS could have anticipated that risk better…I wasn’t involved in the work and don’t want to opine. I do know that lawyers chasing bad guys have to carefully manage when and how bad guys get notice they are targets, and have to anticipate how their investigations could tip off the wrong person and spoil a good case. Some civil laws allow plaintiffs to conduct discovery under seal. Trademark laws, for example, allow mark owners to bring civil suits under seal and conduct discovery under seal that is necessary to locate the bad guys and their assets to enable seizure actions. I don’t know if MS pursued that option or not, but it is a powerful and largely overlooked weapon to gather information civilly under seal.
Don’t stop your Monday morning quarterbacking by just blaming the hard-working investigator for stepping on our collective evidence. There’s plenty of blame to go around, and value in revealing it. Blame often lies with the witnesses/enablers who provided services to the bad guys, and who react to requests for information by invoking simplistic interpretations of complex privacy policies that do not reflect the reality of the policies as they are actually written. I paraphrase here, but you’ll get the jist…nearly every privacy policy contains an exception that says if you use our service to hurt us, we reserve the right to do anything we want with your data, including share it with LE or third parties who are chasing you. Besides this contractual right to reveal data, nearly every law that conveys privacy rights on users also contains an exception for “network security” or “self-preservation” that permits data sharing without notice to the user.
Gmail’s own policy provides this exception to privacy:
“We will share personal information with companies, organizations or individuals outside of Google if we have a good-faith belief that access, use, preservation or disclosure of the information is reasonably necessary to:
◦meet any applicable law, regulation, legal process or enforceable governmental request.
◦enforce applicable Terms of Service, including investigation of potential violations.
◦detect, prevent, or otherwise address fraud, security or technical issues.
◦protect against harm to the rights, property or safety of Google, our users or the public as required or permitted by law.”
Moreover, no privacy policy legally commits to the user that the user will be provided notice that LE (civil or criminal) has requested access to the user’s data.
Despite these two huge safe harbors, almost every corporation that has provided services to a bad guy insists on a subpoena, and provides notice to the bad guy before responding to the subpoena. They do this not because they have to but because they are afraid some lawyer or reporter less clueful than Brian will take a pot shot at them and scare good customers into thinking their data is being handed over willy-nilly.
Privacy is an important and complex concept, best understood as a bundle of rights that come in individual sticks tied together (like real property rights). Privacy needs lots of attention as an issue, and it is clearly true that the average, law-abiding citizen is generally woefully protected wrt privacy. However, it is also true that the average bad guy is vastly over-protected by simplistic applications of privacy policies that were written, not to protect the bad guy, but to protect the rest of us. Privacy policies need exceptions, and the general public needs to understand enforcing those exceptions are sometimes as important as enforcing the general rule.
Bottom line, there are lots of ways we can catch bad guys more quickly with fewer costs without compromising real privacy and without turning everything over to Big Brother. Civil law enforcement is a vastly under-used and poorly understood weapon in the fight, yet civil lawyers are largely not engaged in the fight. Most private sector cyber lawyers spend their time on policy debates that have little impact on the bad guy community. Touching bad guys is hard, and it requires us to first touch those enabling them in material ways. We won’t turn the tide on cyber threats until we start to focus on enablers, and that is not going to be a pretty conversation.
To paraphrase Marx and Lenin: Cyber bad guys are hanging us with our own rope, and you can bet your life the last one of us they hang will be the one that sold them the most rope.
Sorry, but as Kyle wrote it seems you don’t understand the problem:
Cyber crooks don’t share their personal data with Google & Co. Instead they register with stolen and faked data and obfuscate their internet connection. Besides Google & Co. don’t care there is no way to ensure any data on the internet is authentic and they just use privacy policies to hamper inquiries to a minimum of work.
Security research observes the flow of underground transactions, for example email addresses used for communication. And in the long turn if they are lucky they can trace an individual combining observations.
Emailing criminals not to use their google accounts again is just blatant nonsense and a slap in the face of security research worldwide destroing their work. But comparing their work with those pennys microsoft spent stumbling around in a china shop is out of touch with reality.
Maybe you just read the quote and Kyle’s statement again…
…and maybe you take privacy policy serious and ask Microsoft why in hell until now they didn’t enable affordable security updates for their millions of windows bots in developing countries and ask them in how many years they start to inform users about obvious manipulations through windows themselves. Stopping those microsoft bots could be the biggest progress in privacy since stone age.
That subpoena on the website if prolly same one i alerted to my IT security researcher friends……It messed up alot of research….I had to talk to bunch of microsoft attornies…Then passed it on so word could get out…talk about stress time haha
Way to go Andy. 🙂 I just wish most people could understand what kind of damage that Microsoft is doing to these working group relationships and to the current investigations underway.
I’m with Kyle. I find it hard to believe that the “security community” is really whining at Microsoft for its effort to kill the activities of these miscreants. Well for this member of the security community its, “Horray, thank you, and keep up the good work!”
Microsoft has damaged their credibility with security researchers by going on their own without the guidance of Law Enforccement and by using privately collected and built materials by working groups. It is a blackeye for Microsoft. At least I won’t be sending them any 0days I find in their code from now on..
The failure of “law enforcement” to stop these miscreants or even register a “very miniscule inconvenience to the bad guys”, makes ME angry. These illegal activities have been going on for YEARS. Phishes, scams, malware, crappy ads go unchecked.
Judge by the bottom line. If all Microsoft has accomplished is to irritate the hell out of the bad guys, that’s fine with me because knowing their history, it’s a pretty safe bet that this is NOT the end of Microsoft’s involvement. Given the pitiful results of “official” investigations, it clearly does not matter that data is collected or that international cooperation goes on year after year after year.
Show us the beef!
It looks to me as if Microsoft’s critics have a problem with logical deduction.
Fried says, “…the rule is you never release that data outside of the trust group without express permission of whoever provided the data”, then “…there was no way that the data Microsoft published was received independently”. That means that the released data came from either a Microsoft representative in the group or someone else in the group. Then, “Much of it [the data] was cut-and-pasted verbatim, and some of the data included in the search warrant was horrifically out of date.”
If Microsoft’s own representative in the group provided the info, s/he would have known which of the data was “horrifically out of date” and not included it in his/her report. But Microsoft DIDN’T know which data was outdated which leads to the conclusion that the info was from old papers (“cut-and-pasted verbatim”) and it was leaked by someone else.
If the info came from someone not affiliated with Microsoft, the company would be under no obligation to sit on it while the crooks continued to fleece its customers.
Why does this just remind me of the Family Guy ep where Stewie and Brian are in a hotel trying to sleep, and the next room has a drug deal going on and Stewie yells “HE’S WEARING A WIRE!!!”, and next you see bullet holes in the wall and silence.
Hey Microsoft, if it was bleeding so much why did you not patch the bloody thing in the OS? Or put a patch in on IE to detect it? Or even do like you normally do, force a turn on on your silly Windows Defender update it, and detect it?
Oh and people at Microsoft, stop reading all those Cyberpunk books and such, you are NOT a megacorp and have your own army and own laws.
Sounds to me like the “internet security community” needs to seriously get over itself. This is about the victims of these crimes, nothing else. Civil actions by Micrsosoft do not preclude law enforcement action, and I suspect that the security community’s agita has more to do with its members pockets than pride or any legitimate operational concerns. Phishers, hackers and others have become so bold and greedy that it makes doing business on the web tantamount to entering a booby-trapped battlefield. Enough. Let Microsoft give it a try its own way.
What is very disappointing about the comments here is that members of the security community know that those railing against the the community and rah rahing at Microsoft don’t really know what’s going on. Both from a technical perspective, and a people perspective. Why is this disappointing? Because these comments slamming the community are based in ignorance, yet many in the community can’t come out and directly refute what is being said due to ongoing investigations and general bad practice (refuting some ignorant comment may allow bad guys to take advantage of more people). So why do people post that stuff? It doesn’t help, it’s rooted in ignorance, and ingeneral it’s akin to a auto mechanic stating that a report on deep sea microbiology doesn’t go far enough to explain how ancient sea life contributed to today’s oil supply.
If you have a real statement to make great. If you are just defending Microsoft cause “well they are the only one doing anything” then please get educated before posting.
If you are disappointed that we are expressing support for Microsoft taking action, flawed though it might be, imagine how disappointed we are at your arrogant “We know what is best for you and if you aren’t one of us you are just ignorant so keep your mouth shut” attitude. I suspect that all you in the “security community” have wonderful (read expensive) security for yourselves and your families while we poor ignorant bastards are slugging it out here in the trenches and getting robbed. But that’s okay, right? Okay that we get scammed while you put together your nice little “case” – in a decade or so – and then it will either be flawed and dismissed or you’ll win and the decision will be appealed for years.
If Microsoft has stepped on the toes of the security community, could it possibly be that they offered you technical and monetary support on the proviso that you promise to take quick and decisive action “to stop the bleeding” but you blew them off like you’re blowing us off? If so, you are the ignorant ones. Blowing off a nobody like me is safe. Blowing off Bill Gates, et al, would qualify as incredibly stupid.
Diane and Mike: Do you have any experience with the Security Community, Financial Institutions who actually are working diligently to stop this, or law enforcement? Do you have any shred of credibility to make the statements you are saying with a straight face because there is some basis of fact? Based on your comments, my hypothesis is no, but I’m open to hear what you have to say about the subject.
instead of whining, you can provide a generic, non-personalized info. about how these communities work.
Just read the comments of the last few weeks… (to make it short: hope your anti virus software is based on security research)
The answer to Kyle’s first question is no. I am not a security expert. The biggest security breach I ever had to deal with involved my then 2 yr old son’s getting into the household cleaners under the kitchen sink.
As to his second question, “Do you have any shred of credibility to make the statements you are saying”, damn straight I do. I have records on my emails going back to 2002. In Aug, 2002, I received an average of 51 emails/day. Approximately 20 of those were real, not spam, phishes, scams. By March, 2012, my daily quota was 389/day with approximately 45 real emails/day. I know a s**tload about how to grow my penis, make a killing in the stock market, collect millions from a secret Nigerian bank account, correct faulty information in my bank account and verify my login information on my credit card accounts. As I mentioned earlier, I’m in the trenches fighting off this crap so yes, I have credibility, based on facts, to address this problem.
Do you? Or do you let AOL/gmail/hotmail/your ISP/whatever filter your emails? I’ll bet you do. I’ll venture you have NO CLUE what’s out there, on a daily basis.
BTW, do you think they really CAN grow my penis? Inquiring minds want to know.
I’m no expert…
But a lack of results usually means one of 2 things, either no one is working on it, or the ones working on it are incompetent.
It doesn’t really matter how much “research” that someone hordes, or how hard people work on it, if ultimately it does nothing to fix the problem.
Well said, Mike.
I admit my initial reaction to Kyle’s post was indignation, a purely emotional response. Let me take another run at his comments.
“…members of the security community know that those railing against the the community and rah rahing at Microsoft don’t really know what’s going on.”
Okay. So what? A 70 year old grandmother sits at her computer and types, “Go Billy! Go!” and this is a problem how? Kyle said, “Because these comments slamming the community are based in ignorance”. Again. So what! Just what impact does that old lady giving Microsoft kudos have? How does that impugn prestigious security groups or interfere with their investigations? Hello… it doesn’t.
“…many in the community can’t come out and directly refute what is being said due to ongoing investigations…” ROFL! Why in hell would they need or want to? Again, how does a private citizen’s remarks, disappointingly IGNORANT comments at that, have any impact on anything? The idea is ludicrous and Kyle’s inference that such remarks will somehow interfere with “ongoing investigations” is even more preposterous. He then equates people expressing “ignorant” good will toward Microsoft with an “…auto mechanic stating that a report on deep sea microbiology doesn’t go far enough to explain how ancient sea life contributed to today’s oil supply.” ROFLMAO! Any microbiologist who gets his panties in a wad over some ignorant wrench jockey’s criticism of his work has an extremely tenuous grasp on reality.
“If you are just defending Microsoft cause ‘well they are the only one doing anything’ then please get educated before posting.”
Kyle, we are not defending Microsoft, we are applauding them, and not because they are “the only one” doing something but because we can see that they ARE doing something. Rest assured that when the work of your vaunted cyber security task forces results in indictments, we’ll praise them too.
Thank you Diane. You have proved my point. Don’t worry, myself and others will continue to protect you, even if we don’t get credit for it. Do we get 100% of the malware or spam, naw, but we do make a difference, even if from your point of view, no one is doing anything.
It’s really sad that there are people, who ever day come to work to defend you and others, and because we don’t make movies or press releases about our successes, mainly so we can continue to have them without criminals learning and becoming better at what they do, they can only sit and watch as you emotionally vomit over sensationalist stories like that. Way to keep your defenders motivated Diane.
Kyle, one of the biggest problem is, that people are frustrated because “nothing happens”, yet they fail to understand that law enforcement cannot just gun down guilty people. They fail to understand, that using illegal pepperspray may get yourself in trouble. Heck, even mere self-defence may get you jailed, if you do it “wrong”!
We could try the Fearless Fosdick approach.
Also, except for Microsoft saying it took down server, what has the positive result been? Have you seen less malware/spam. My guess is no. I know that through my work, malware is up, account take over is up, fraud attempts are up. So why are you applauding Microsoft, or are you the type who, when a huge multi-billion dollar corporations says “We did good things… FOR YOU” you believe them because of their nice you tube video? I applaud your lack of critical thought.
I share Kyle’s concern that the bad guys’ “production numbers” are still going up…and I’m concerned that this is happening despite all that Kyle and others are doing in the security space to stop them.
Indeed, that’s kind of the entire point being made by the laymen/women commenting here….at a strategic level, what we are currently doing is simply not working. Doing more of the same is not going to fix the problem.
We need to consider new approaches and evalute what impact they have on the problem. One tool that is vastly overlooked is civil legal process, and MS is one of the few actors experimenting with how to use it. The experiment is a good thing, but it needs to be expanded. Here’s why…
Lack of attribution is the single greatest impediment to stopping cyber threat sources. Attribution is important not only because it enables legal enforcement measures, but also because it enables economic, market enforcement measures. Market mechanisms are important because they are the cheapest way to shift costs through risk. Bad behavior imposes risks on bad actors AND on those enabling the bad actor. But those risks cannot be imposed if we cannot attribute the bad acts to bad actors or enablers.
The reality is we can easily identify many enablers, but almost no one is doing anything to shift the costs that fall on victims onto those enablers. Too many enablers simply ignore their enablement or, when confronted with it directly, respond by merely “processing” the account they enabled — terminating an email account or taking some other technical action against the internet fingerprint tied to the bad guy but never actually touching the bad guy directly…personally. Morever, they take too few steps to reveal information to those who need it — whether it is the victim community that could take the information and use it chase the bad guy down, or the future enabler community which could use the information to do better diligence (if they were motivated to do it out of say…fear of being held accountable for not doing it) to deny services to a bad guy based on his prior history of bad conduct.
Essentially, too many essential service providers are making money by selling key services/goods to cyber bad guys. Those enablers wrongly think they can avoid accountability by simply implementing a poorly considered “revolving door” fraud/abuse prevention system. When an enabler does throw a bad guy out the door, the bad guys just turn around and come right back in, often times without even having to change their identity to regain access.
The solution to this revolving door problem is to hold enablers accountable in a more meaningful way. This is simple to do if we start attacking the problem using the tools that come in the tool box that all lawyers are issued when they pass the bar — one of those tools is the remarkable power to file lawsuits on behalf of victims and to use those lawsuits to initiate discovery to gather attributional information needed to start shifting risk and cost from victims to enablers and ultimately onto bad guys. Currently, there are almost no private sector lawyers spending much time helping victims shift costs onto those enablers who are willfully enabling bad guys for a share of the profits.
Willful enablers aren’t hard to find. A small number of banks are laundering the vast majority of credit card sales made by bad guys, yet the major card associations are moving extremely slowly to cut them off. Why? Because they make money off the fraudulent activity. A handful of registrars are selling domains to bad guys. Why? You guessed it…they’re making money off it.
Most third graders could identify this conduct as “wrongful.” We don’t need new laws to stop the conduct. What we need most is simple enforcement of pre-existing legal rights. Private sector victims (both corporations and consumers) have any number of claims they could bring against bad guys and those intentionally enabling them. Microsoft is one of the few robustly using the civil law to effect change.
Name another private sector victim doing what MS is doing. You can’t. Yet the problem is far larger than even MS can take on alone. We need private sector lawyers broadly engaged, and we aren’t yet close to having that happen. My legal practice is the only one in the world specializing in this field. We aim to do for the rest of the victim space what Microsoft is trying to do for itself — we bring strategic civil actions on behalf of victims and groups of victims, based on a sophisticated understanding of the data that shows who is enabling what and for whom.
We’ve sued banks, counterfeiters, spammers, phishers and a host of affiliate marketing operations, with an eye toward establishing precedents that will shape the law and encourage market players to pay more attention to the risks of enablement.
Why aren’t more law firms doing this? They don’t understand the nature of the problem or how to contribute to the solution. Indeed, most large law firms in the US are doing a poor job of policing their own acts of enablement. That’s right, most lawyers today are doing more harm than good. Here’s why….
Almost no law firm today is doing a simple conflicts check on the Internet fingerprints that matter to their clients. As a result, too many big firms are stumbling to help victims of cyber crime find bad guys at the same time they are aggressively defending enablers helping the bad guys hide.
By playing both sides of the game, big law firms contribute to this false sense that the problem is just too complicated to be solved. It isn’t that complicated…the problem would be easy to solve if we were more broadly using civil legal process to gather attributional information, and then sharing that information broadly enough to allow market forces to allocate risk onto enablers.
Heaven, just sue Microsoft and you ‘ve hit the biggest “enabler” himself: 99.8% of all bots are Windows manchines, infected due to Microsoft’s lack of product security. You don’t have to sue providers for anything if you could sue the criminal customer because it’s not a hacked account and a hacker hiding behind a windows bot…
You’re fighting bots and Micorosoft is their confederate whore. Or “Enabler”, if you want. 😛
The ignoramuses who run Windows machines using administrative accounts as their normal day-to-day working accounts (or blindly disable UAC, or automatically enter administrative credentials at every UAC prompt they see) are to blame.
If you don’t have the smarts to create a non-administrative account on your windows machine, use only non-administrative accounts for day-to-day tasks, and know _when_ to use administrative credentials, do the rest of us a favor and carefully pack your computer in a shipping box and return it to the seller. You’re too stupid to own a computer.
Hi, you bigoted public relations slave, i’ve talked about the millions of PCs infected due to your client’s laziness in usability and all you have to reply are insults demonstrating Microsoft didn’t make their OS ready for mass-market? – Thx, that’s what I said. 😉
Somewhere in this thread, someone mentioned addressing the “enablers” of these cretins. Perhaps we need something like the consumer protections that make companies recall products that could cause injury (child car seats, playpens, etc). Perhaps then Adobe, Microsoft and Oracle would be forced to remove/disable their products widely used to enable malware.
It’s one thing to download something that contains malware; it’s another to have the software installed by the mfg be exploited. Consumers expect their machines to be safe “out of the box”.
Maybe a warning label like cigarettes would get some attention:
“Use of the software installed on this computer by the manufacturer may be detrimental to your financial well-being. Please consult a repair professional to adequately protect your computer.”
Precisely.
It often isn’t the software per se that often causes people to become infected. It is people who do not update their software that gets themselves infected.
One study found about 80% of people never bothered to update their software. This isn’t the manufacturers fault. This is ignorance on the part of stupid and/or lazy people. Most of the time, legal, big business content sites do NOT infect computers, it is more often than not pornography websites, the content of which is illegal in many jurisdictions. i.e. many bring it on themselves.
Why is it that someone cannot drive a device with a powerful engine without a licence, but when we’re talking about enabling identity theft, damaging economies, and making the internet a less safe place, somehow individuals aren’t responsible?
I would personally love to see a big organisation that has been infested and spewing spam get sued civilly for negligently allowing it to happen. A wake up call to users. I would also like a 3-weeks-disconnection policy for users, where a person would be notified of malware and have 3 weeks to clean the data coming off it, or they would be nationally banned from connecting until they could certify it was clean (at their own expense).
“It is people who do not update their software that gets themselves infected.”
Not entirely true. User can do nothing when he gets hit thru a hole that’s not been fixed.
http://krebsonsecurity.com/2012/04/urgent-fix-for-zero-day-mac-java-flaw/
“Most of the time, legal, big business content sites do NOT infect computers, it is more often than not pornography websites”
Most of the time, they dont. But when they do, the effect can be well beyond the scope of any single porn site ever possible.
http://krebsonsecurity.com/2011/09/mysql-com-sold-for-3k-serves-malware/
“Why is it that someone cannot drive a device with a powerful engine without a licence, but when we’re talking about enabling identity theft, damaging economies, and making the internet a less safe place, somehow individuals aren’t responsible?”
How often you hear in news about how some drunken PC-user clicked someone to death? Or anything similar? On the other hand, how often you hear that a person is responsible for getting sick because he did not pre-boil his drinking water “just in case”, while the malfunctioning equipment in water treatment plant leaks some dirt into clean water circulation, all sudden?
But after all, I agree with one point with you, cherry. People update their software too lazily. I’ve noticed that by myself by merely observing people and their computers, thus I have no difficulties with swallowing as high number as 80%.
And that’s precisely why MS is attacking botnets. MS understands it could face potential exposure for enabling cyber threats and it is behaving responsibly by doing something to address it beyond simply trying to do a better job of writing perfect code. One may criticize MS for merely following the kindergarten concept “if you make a mess, clean it up.” I understand the criticism, but shouldn’t we first direct our criticism at those who are making no effort to clean up their own messes, and indeed are actively sweeping their messes under the rug?
Nope. Microsoft is cheating public. In fact they are just destroying evidence that they didn’t clean up knowingly infected customer’s pcs themselves, making your interwebs a darker place.
Truth is Microsoft repeatedly failed to clean up millions of infected machines, knowingly leaving those customers vulnerable to further abuse through cyber criminals.
“Truth is Microsoft repeatedly failed to clean up millions of infected machines…”.
Could you be more specific and cite your sources? I’m unclear what millions of machines you are referring to, how they got infected, whether MS could have reasonably prevented those infections and to what extent failure on the part of the owners to install released updates played a part.
First Microsoft only grants licenses, so every running copy of windows is their property: From a product liability point of view Microsoft didn’t prevent malware infections of their product licensed to useres relying upon microsoft doing everything possible to keep them safe.
Those ‘bots’ connect to C&C servers. Knowing the C&C servers’ means to know the IPs of the bots: Microsoft could have notified users of infected machines about malicious traffic to C&Cs using windows functions. They decided not to do.
Finally Microsoft could set up a website where useres could check whether their pcs are affected and add support to clean up those windows licenses. Again they decided againsts something every respectable company would do.
Instead they plan to inform providers to look up IPs of infected windows machines, leaving it to providers to inform users that their pcs are infected…
To be honest microsoft does not inform providers about infected customers themselves – instead they leave that to third parties, so users do not ask microsoft for support and/or compensation…
Microsoft could do more to prevent their customers from being infected. They could have informed customers connecting to C&Cs about infections. And they could give support to clean up infections. But they decided just to switch-off C&Cs and leave the rest to others.
It’s like microsoft just watching someone breaking into your home using vulnerabilities they are responsible for. And afterwards they anonymously call the police to let you know you should have paid more attention…
Consistently funny how those PR bots act… (if you downrate a post after a topic is gone the comments don’t disappear, ostrich attitude doesn’t help. :-P)
Say I follow your advice and contract you to provide me with your services as a repair professional. Can you guarantee (on point of legal recourse) that you will protect me from *all* malware, nasties, exploits, baddies and viruses out there?
You can’t? Why not? I think this is what others such as Microsoft are fighting as well.
Any activity that makes the baddies look a little more often over their shoulder can’t be a bad thing, can it?
Hardly. Perhaps annually-renewed “computer owner/operator” licenses should be required to qualify for an Internet connection. With a bit of competence and a willingness to learn, Windows can easily be operated in a relatively very secure manner (not so conceptually different from safe sex as taught in high schools: wear a condom, use contraceptive, etc.). Of course, there is always a certain level of risk when a computer is connected to a network (particularly the Internet). Just as abstinence outside of marriage is the safest sex practice, so is abstaining from connecting your computer to a network (esp. the Internet). If you’re not willing to learn to operate your computer safely, at a minimum stay offline. Better yet, do the rest of us a favor: carefully pack your computer and return it to the seller. You’re too stupid to own a computer.
Disclaimer: I don’t really think users should be required to have a valid “license” to access/use the Internet. But I do get very annoyed with users that choose to remain willfully/blissfully ignorant.
The beauty of the Internet is in a) its standards b) its openness and c) relative ease-of-use; you don’t need to know much before you can _begin_ using it productively. The problem I see is that too many users quickly plateau and decide they don’t want to learn more, even if it means they’re vulnerable. If this is you, please do the rest of us a favor and pack up your computer and return it to the seller. You’re too stupid to own a computer.
I can certainly appreciate what it feels like to do a lot of research and get no credit for it.
But if I were the owner of one of the small businesses whose accounts were cleaned out because of a ZeuS infection on an employee’s Windows computer — and yes, you can keep your AV completely up to date and still get pwned, and no, not every business can operate in a Linux environment and have their data flow between their business, accounting, and banking software — I would have a hard time feeling sorry for people whose strategy is to allow the criminals to continue to ruin people like myself year after year, while they harvest data about them for some future legal action … especially when there is still a huge barrier to ever bringing criminal charges against criminals in countries like Russia, Ukraine, China, and Nigeria.
ZeuS is available for sale to criminals who lack the skills to program anything remotely that sophisticated for themselves. The number of potential perps is unlimited at present. There are plenty of criminals for everyone to go after.
While I’m usually no fan of Microsoft, if they can discourage criminals from even starting to victimize innocent people in this way and can discourage legitimate internet companies from allowing their resources to be used for illegal activities, I can’t get too upset.
No-no. Unfortunately mickeymousesoft just knocked out some C&C servers. That’s likewise burning some cars in the street to reduce traffic: High attention, but little impact in the long term. 😉
I would like to know from people more knowledgeable than me on this list if Google sending notices of a subpoena to those miscreants could in any way enable them to be more successful in removing evidence. I suspect/hope that even if they immediately delete all their emails once they receive the notice, once the subpoena is activated, those inboxes can be restored from backups along with (heck, this is Google) all kind of additional metadata generated with data mining (what time they opened the notice mail, for instance, from which IP address, etc. etc).
How is it really, how deep can such subpoena go in accessing information which is beleived to be removed by the user ?
Whatever Google says about you owning your data, the law dictates how long they must keep their backups. Certainly, once an account has been subpoenaed, they have to preserve the data.
Basically Google’s interest is profiling data, not storing copies of deleted sources. Storing internet traffic for further use are the folks at the agency. 😛
george,
it is unlikely there is any “evidence” in those GMail accounts.
The criminals need a stable email address to register their domains and a few other things, but their daily business information is exchanged on closed forums and other networks that get taken down regularly (and then pop up on another server).
I have read over the comments above and it looks like there is to much emotion motivating people for there to be any logical discussion possible on the matter.
Shame on you, Microsoft. Your hype and PR stunts fool nobody. What you should do is give people the secure OS they expected and stop behaving like a disenfranchised Gordon Gecko’s baby brother.
Get over yourself already. If you have even a modicum of knowledge on Windows, you can run it quite securely. If you can’t manage that, maybe its time to ship your computer back to the seller and buy yourself a Mac. You know Macs are impervious to viruses, Trojans, and the like, right?
http://www.macworld.com/article/1166195/apple_releases_java_security_updates.html
If those with zombies and too lazy or ignorant to have figured it out would be knocked offline in July (hopefully for a while) because of DNSChanger, I think it would be hysterical!
http://news.cnet.com/8301-1009_3-57418276-83/web-could-vanish-for-hordes-of-people-in-july-fbi-warns/
When ‘aviating’ terrorists attacked a decade ago, the ‘war on terror’ was launched far and wide. We sent our youth to fight in far away places such as Iraq and Afghanistan, guns blazing and bombed the opponents to smithereens. That war has not stopped.
Now when we have ‘digital’ terrorists causing just as much financial damage, reaching into our very lounge rooms and wallets across the world, we politely advise them to close their email accounts and seek legal advice while we take long winded legal proceedings.
If we were serious, there would be a swat team, silently removing/rendering these threats, not researching them for academic white papers.
Wake up folks – we live in a real world, with terrorists doing their very best to fleece you, left, right and centre, daily!
If the fight against digital terrorism was treated as a military exercise, I’m sure the world would be a different place.
As an aside: All we have to do is show the military what the enemy looks like and how to exterminate him. Hence the academic research I suppose.
We have met the enemy, and he is us. The ZeuS bank robbers depend on undereducated, unemployed Americans to act as money mules, and they depend on computer-naive users to install their malware.
So true!
.oO(And finally we rely on companies constantly failing to secure their products.)
that’s a good point that is often missed. So long as people have the rights to install software, there is no need to exploit the system as users who don’t know any better simply install the trojan and then move on when it doesn’t show them the promised doc/video. My experience is that Adobe reader/flash and Java are the most commonly exploited right now. There’s a reason for that and MS deserves some credit.
It seems there are at least three issues under discussion here resulting in cross-communications between individuals addressing one concern and other individuals seeing the comments as pertaining to a different concern. So…
1) Microsoft: should MS have taken the actions it did? Is it a good thing to involve non-LE types in the battle? Were their actions helpful? Harmful? Both?
2) Email providers: should they always notifiy their clients whenever a private concern, or LE for that matter, supoenas records pertaining to their accounts, without examining such situations case by case?
3) Comments by “the common folk”: does it truly interfere with the efforts of LE or secretive security groups when plain vanilla computer users express satisfaction with efforts by those outside the criminal justice system? Will MS or other private parties give weight to such comments in deciding future policy?
For example, IF you think that MS was wrong in what they did, AND you think that the comments of a Midwest housewife have no bearing on information gathering efforts, then criticizing the housewife is dumb because it lets MS off the hook while pillorying someone you don’t believe has any power.
I can answer at least part of your question.
Microsoft makes widely used operating systems. It charges a lot of money for them and uses various methods to make sure people don’t just make copies and upload them to filesharing sites. Those methods are less than 100% successful, and a high percentage of computers in developing countries have pirated Windows operating systems. Microsoft used to allow those pirated copies of Windows to update just like all the real copies. But now they have “Windows Genuine Advantage” that checks to make sure your copy is legitimate. If it’s pirated, you don’t get an update. That means your computer becomes a hazard to all the other people using the internet because it is vulnerable to multiple well known types of malware as well as the new “zero day” ones that everyone has to worry about. Microsoft has been criticized for that decision.
Notifying users about subpoenas: Companies like Google don’t always have the option. As mentioned above, Microsoft could have asked for the subpoenas to be sealed rather than public. And in criminal cases, the Patriot Act gave the government the right to seize your data (including your medical records) and made it illegal for the agency in possession of that data to notify you to allow you to file an appeal.
Re: Attitudes expressed toward your comments. You’re expecting that everyone who reads your comments thinks about the fact that there is a real human being who typed them, a woman who worries about being victimized by criminals before law enforcement gets around to taking action, a housewife who worries about her even less clueful friends and family members falling victim as well. I don’t think it would be very easy for a researcher to monitor an infected computer to gather data, knowing that real people are losing real money, without developing some degree of emotional disconnect. It sounds cold, but someone has to do it to eventually get these guys in jail. Don’t hold it against them.
“I don’t think it would be very easy for a researcher to monitor an infected computer to gather data, knowing that real people are losing real money, without developing some degree of emotional disconnect.”
Compare it to real-world crime. Somebody killed B. For law enforcement B is just a piece of the puzzle to find A, who killed him. The victim is a technical component.
When you’re infected with Zeus and I get my hand on the logs from your computer, I don’t care what the balance of your accounts is, which porn sites you visited and I’m not interested in the content of your emails. The only thing I care about is technical parameters (like your bank and account number).
You (well, your bank account) then end up on a list for the specific bank and like thousands of others that day your online banking access will be blocked. Hopefully before the bad guys emptied the account.
Sometimes I feel sorry for you who became a victim, even if you work as a money mule (it’s usually not the educated middle-class people). But I can’t be sorry for long because I just got another dataset with logs for 20k of you to look through.
anon’s post seems to have been ignored but his/her point is a good one. Since the cyber security insiders posting here are so upset with those of us not in the know, why not educate us, provide “… generic, non-personalized info. about how these communities work”? If you just call us ignorant and unthinking, you succeed only in setting us against you. You create an “us” vs “them” environment. However, if you give us information on your efforts and something more specific than “MS did bad” regarding the problems with private companies stepping in, if you show us how you want to and CAN work with private organizations or why that is totally impossible, you give us the information we need to make informed decisions on these issues. It may be that we choose not to agree that your approach is the best, or even adequate, but that can be good too. If we are on the same side, and you see us as such, our comments from outside the box might help YOU find new and possibly more fruitful ways to address cyber crime.
really, it isn’t that difficult, but the info is technical.
google “zeus analysis”.
forgot to mention:
the big problems I see are:
– taking down the server won’t do anything, because the bot, as a tool, is made aware of that.
– also, you just can’t be sure about the info. really, is too easy to make a mail account with fake data, or even steal an account.
so, in the end, what microsoft did doesn’t help at all, and they probably know it, because they have the technical knowledge.
Since I don’t recall gmail being used for sending ZeuS spam, the question is what those accounts were used for. The information exchanged with mules might lead to email accounts of mules who have not been apprehended because they were aware of what they were doing and created bank accounts under false names. We’ve seen that these folks can be quite careless about reusing the same accounts for personal information.
There were two types of addressees Microsoft was seeking John Doe information on: One were the inboxes of miscreants thought to be involved with a Ukrainian-based Zeus crew, and the other was mainly just email addresses used to register the domains that served as control centers for Zeus botnets.
From the story:
“Part of the controversy stems from the bargain that Microsoft struck with a federal judge in the case. The court granted Microsoft the authority to quietly seize dozens of domain names and Internet servers that miscreants used to control the botnets. In exchange, Microsoft agreed to make every effort to identify the “John Does” that had used those resources, and to give them an opportunity to contest the seizure. The security community was initially upset by Microsoft’s first stab at that effort, in which it published the nicknames, email addresses and other identifying information on the individuals thought to be responsible for renting those servers and domains.”
Google is front company for CIA, so obvious.
whatever this was about, i guarantee it has nothing to do with them caring about peoples safety or wanting to clean up the internet.
who still believes things like this?