A few years back, when I was a reporter at The Washington Post, I put together a chart listing the various ways that miscreants can monetize hacked PCs. The project was designed to explain simply and visually to the sort of computer user who can’t begin to fathom why miscreants would want to hack into his PC. “I don’t bank online, I don’t store sensitive information on my machine! I only use it to check email. What could hackers possibly want with this hunk of junk?,” are all common refrains from this type of user.
I recently updated the graphic (below) to include some of the increasingly prevalent malicious uses for hacked PCs, including hostage attacks — such as ransomware — and reputation hijacking on social networking forums.
One of the ideas I tried to get across with this image is that nearly every aspect of a hacked computer and a user’s online life can be and has been commoditized. If it has value and can be resold, you can be sure there is a service or product offered in the cybercriminal underground to monetize it. I haven’t yet found an exception to this rule.
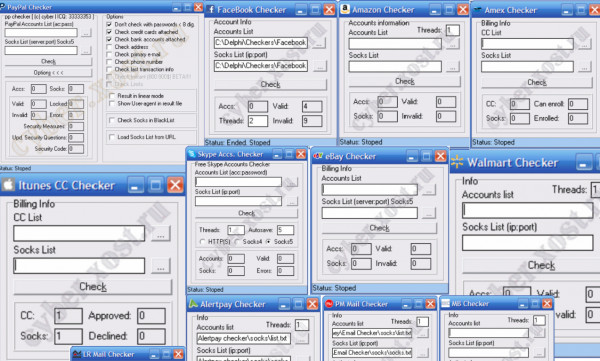
By way of example, consider the point-and-click tools pictured below, which are offered on several fraud forums by one enterprising young miscreant. This guy makes and markets dozens of account checking tools that are used to test the validity and status of many popular online stores and services, including Amazon, American Express, eBay, Facebook, iTunes, PayPal and Skype, to name a few.
Principally, I see the hacked PC graphic as a way to capture the average user’s attention and imagination. Hopefully, these folks can then be guided toward some simple steps to keeping their machine from getting hacked. I’m building a running list of applications, simple tools and tips that can help on this front, available here.





Good work (as always)!
Would you allow a german translation (at least of the picture), that then will be published on a non-commercial blog?
Greetings
Thomas Wallutis
My vote for a wikipedia article and translations there. 😉
GREAT INFO!!!!
This is a handy-dandy visual that should capture a lot of folk’s attention.
And yes, you are definitely correctly in the mentality of folks who make those kinds of comments – they still generate a lot of information without realizing it.
These people are only thinking of the moment and not down the road holistically as to what they do on their PC (or Apple, or UNIX or etc…).
Great diagram Brian. I’d also add some other uses for a hacked server in support of criminal infrastructure. IRC server or bot for an oldie but a goodie, proxy box, malware C&C, drop-box location, DNS server, etc. Lots of great uses for those CPU cycles.
Rod
In your “Tools for a Safer PC” list you mention that only one program you know is designed to run alongside other Virus software. A program I have used a ton and found very effective is Hitman Pro, and it is also designed to run alongside other virus programs. It leverages the cloud to utilize multiple virus databases and I’ve found it also works for several rootkits such as TDSS and TDL4 that other apps miss. I’ve used it several times on my computers and found it works really well.
Great graphic, thanks. What kind of reuse license is associated with the graphic? I’d like to send it to management.
I would recommend Qualys Browser Check too, which checks for missing patches and other common issues. Install the addon to scan in depth, and to scan your other installed browsers. Or scan without the addon and it will audit just your current browser for security issues via information it leaks to all websites. Their FAQ says they support Mac and Linux too, but I’ve only tried it on Windows and Android.
You may want to also add espionage, sabotage, and eavesdropping as possible uses, especially when thinking about Flame and its use in the Middle East.
What is “CAPTCHA solving zombie” exactly?
Since I use various automated processes in marketing efforts I’m familiar with outsourcing – Death by Captcha and many other services – and external applications – Captcha Sniper and Xrumer “bridge” method – to solve captchas. Is this what you’re referring to?
It would make sense particuarly for solving ReCaptcha using Xrumer: this often takes many attempts and more or less as much CPU time as you can throw at it.
I hear (but don’t have access to or anything other than rumours to go on) that there are private or semi-private captcha solving applications out there that are kept private to combat captcha providers reacting to them.
“What is “CAPTCHA solving zombie” exactly?”
Here’s one example:
http://www.inwyrd.com/blog/2010/03/hijacking-koobfaces-captcha-solver/
Oh wow, that is devious. I wonder if DBC and other captcha solving services utilise this. I was under the impression it was software + low paid workers but maybe not …
Syllogism:
1. If security of my PC was a big problem, I’d have to do a lot of work to prevent it.
2. I don’t want to have to do a lot of work.
Ergo:
Obviously the security of my PC is not a big problem. Otherwise I’d have fixed that a long time ago…
Funny, but blatant truth is there are vegetative life-forms of ignorant and/or brainless meatballs out there simply too stupid for information society. Some call that evolution. Bizarre twist: they know they’re failing… Ergo: no need to worry about. 🙁
Great article. Thanks.
Want to point out though that the HTTPS version of your page has insecure content (actually a friend spotted). Would be good to fix that, because it might encourage people still learning about security to trust mixed content sites more than they should.
Cheers, David.
Brian: In your “Tools for a Safer PC”. You mention turning of JavaScript. I’m pretty sure you mean Java, don’t you? You’ve always spoke out against Java, not JavaScript (which has nothing to do with Java).
Please read the JavaScript passage again; in the second to last paragraph Brian points out: “Please note that Java and Javascript are two very different things.” – So yes, he’s taking about JavaScript there, but he didn’t suggest to turn JavaScript off…
Yeah, the part about JavaScipt and Java being different that he mentioned I missed somehow (I scanned over the article too quickly). But he does say:
“But disallowing JavaScript by default and selectively enabling it for specific sites remains a much safer option than letting all sites run JavaScript unrestricted all the time.”
Which seems to be suggesting to turn JavaScript off. Though you can do this, running software like NoScript is not something for anything but experienced users to do. There are far too many scripting options that come up and it is probably not obvious to most users, even sometimes advanced ones, that JavaScript has changed a site making it hard or impossible to use (most menus are JavaScript based, for example). I’ve used NoScript myself for a month or two and just ended up finding it more of a nuisance than anything.
I’m a computer teacher and I recognize what people can and will do. This isn’t a recommendation I’d agree with (turning JavaScript off by default and selectively turning it on) except possibly for advanced users. And even then, it makes using the web a lot more unpleasant.
I’m curious about whether the owner of an unsecured PC is, in the jurisdictions of our various countries, liable if it is used to commit fraud. I’d hope that a PC owner who didn’t take “reasonable” (using a word seemingly beloved by the law) security precautions would be considered partly responsible. I gather that this is generally the case in English law, though I don’t know about the specific case of a unsecured or improperly maintained PC.
Yes, in India the liability of the owner of the compromised system or network has been enshrined in the IT Act. As you said, the phrase “Reasonable Precautions” also finds mention here.
Even if they aren’t held personally liable, it is rare that someone with a pc is not going to have any personal info on it… The folks who fail to take any precautions and let themselves get extremely infected likely find their bank accounts bled dry and identity theft problems that more than make up for the problem.
It might not happen to all of them but I’d hate to take my chances on it.
It’s an excellent question. Seems like it would be hard to prove the PC owner knew that something illegal was happening.
Knowingly or not the source is liable for every avoidable threat negligently caused to others in my world. .oO(In most cases that leads us to a company with a strange sense of justice and responsibility in Redmond, Washington, U.S. :roll:)
Hi, may the picture be republished on commercial site, with link to the permalink of the original post?
You might want to update it with Bitcoin wallet harvesting. This assumes that the user has not bothered to encrypt it, or has used a weak password allowing the attackers time to crack it.
Good info. Reminds me of a former employer a few years ago, a small business (non-computer related) whose owner didn’t believe in using a simple firewall for their Internet connection and didn’t have any concern in securing the half dozen PC’s they used. His mentality was that there was nothing of importance on the PC’s and that no one would be trying to break into them from the Internet anyway. I carefully explained to him the threats at hand (like in the diagram) and offered my assistance to secure things. Sadly, end of the story, nothing was ever done. Shortly thereafter I left that job partly because of that. The ignorance out there is astounding at times.
Can I do an italian language version of your graphic? (maybe a more attractive, less schematic one) ?
If you want I can “pimp up” also this one 😀
… Bitcoin Mining…