The U.S. Department of Homeland Security is warning that a group of mostly Middle East- and North Africa-based criminal hackers are preparing to launch a cyber attack campaign next week known as “OpUSA” against websites of high-profile US government agencies, financial institutions, and commercial entities. But security experts remain undecided on whether this latest round of promised attacks will amount to anything more than a public nuisance.
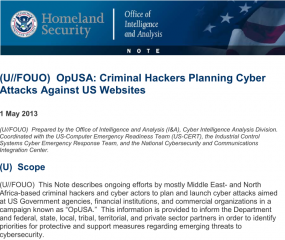 A confidential alert, produced by DHS on May 1 and obtained by KrebsOnSecurity, predicts that the attacks “likely will result in limited disruptions and mostly consist of nuisance-level attacks against publicly accessible webpages and possibly data exploitation. Independent of the success of the attacks, the criminal hackers likely will leverage press coverage and social media to propagate an anti-US message.”
A confidential alert, produced by DHS on May 1 and obtained by KrebsOnSecurity, predicts that the attacks “likely will result in limited disruptions and mostly consist of nuisance-level attacks against publicly accessible webpages and possibly data exploitation. Independent of the success of the attacks, the criminal hackers likely will leverage press coverage and social media to propagate an anti-US message.”
The DHS alert is in response to chest-thumping declarations from anonymous hackers who have promised to team up and launch a volley of online attacks against a range of U.S. targets beginning May 7. “Anonymous will make sure that’s this May 7th will be a day to remember,” reads a rambling, profane manifesto posted Apr. 21 to Pastebin by a group calling itself N4M3LE55 CR3W.
“On that day anonymous will start phase one of operation USA. America you have committed multiple war crimes in Iraq, Afghanistan, Pakistan, and recently you have committed war crimes in your own country,” the hackers wrote. “We will now wipe you off the cyber map. Do not take this as a warning. You can not stop the internet hate machine from doxes, DNS attacks, defaces, redirects, ddos attacks, database leaks, and admin take overs.”
Ronen Kenig, director of security solutions at Tel Aviv-based network security firm Radware, said the impact of the attack campaign will be entirely dependent on which hacking groups join the fray. He noted that a recent campaign called “OpIsrael” that similarly promised to wipe Israel off the cyber map fizzled spectacularly.
“There were some Web site defacements, but OpIsrael was not successful from the attackers point-of-view,” Kenig said. “The main reason was the fact that the groups that initiated the attack were not able to recruit a massive botnet. Lacking that, they depended on human supporters, and those attacks from individuals were not very massive.”
 But Rodney Joffe, senior vice president at Sterling, Va. based security and intelligence firm Neustar, said all bets are off if the campaign is joined by the likes of the Izz ad-Din al-Qassam Cyber Fighters, a hacker group that has been disrupting consumer-facing Web sites for U.S. financial institutions since last fall. The hacker group has said its attacks will continue until copies of the controversial film Innocence of Muslims movie are removed from Youtube.
But Rodney Joffe, senior vice president at Sterling, Va. based security and intelligence firm Neustar, said all bets are off if the campaign is joined by the likes of the Izz ad-Din al-Qassam Cyber Fighters, a hacker group that has been disrupting consumer-facing Web sites for U.S. financial institutions since last fall. The hacker group has said its attacks will continue until copies of the controversial film Innocence of Muslims movie are removed from Youtube.
Joffe said it’s easy to dismiss a hacker manifesto full of swear words and leetspeak as the ramblings of script kiddies and impressionable, wannabe hackers who are just begging for attention. But when that talk is backed by real firepower, the attacks tend to speak for themselves.
“I think we learned our lesson with the al-Qassam Cyber Fighters,” Joffe said. “The damage they’re capable of doing may be out of proportion with their skills, but that’s been going on for seven months and it’s been brutally damaging.”
According to the DHS alert, 46 U.S. financial institutions have been targeted with DDoS attacks since September 2012 — with various degrees of impact — in over 200 separate DDoS attacks.
“These attacks have utilized high bandwidth webservers with vulnerable content management systems,” the agency alert states. “Typically a customer account is compromised and attack scripts are then uploaded to a hidden directory on the customer website. To date the botnets have been identified as ‘Brobot’ and ‘Kamikaze/Toxin.’”
In an interview with Softpedia, representatives of Izz ad-Din al-Qassam said they do indeed plan to lend their firepower to the OpUSA attack campaign.
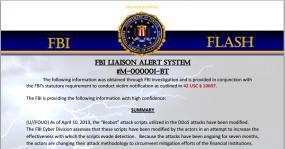
What’s more, the DHS warning comes just days after the FBI issued a flash alert on Brobot (PDF) warning that hackers have been modifying the attack scripts to ensure they can evade their targets’ mitigation efforts.
“Because the attacks have been ongoing for seven months, the actors are changing their attack methodology to circumvent mitigation efforts of the financial institutions,” reads an FBI alert obtained by BankInfoSecurity.com. “The latest version of the ‘Brobot’ attack scripts that have been utilized to attack the login capabilities of a financial institution’s website spoofs a fraudulent access cookie, user-agent string and referrer. The login script includes several random strings, but does contain one hard-coded string, ‘63.83.61.17-1365521883478351’, in the script,” it continues.
The FBI alert notes that the hard-coded string does not affect the new attack script, but can be used as signatures for intrusion detection and intrusion prevention devices to detect and block attacks from the Brobot botnet.
A copy of the full DHS alert on this topic is available here (PDF).




I thought you once told me in an email you don’t cover this junk?
And this isn’t aimed at you, Brain, but with so many people flying the Anonymous flag, everyone might as well just as easily say “SOME PEOPLE ON THE INTERNET”. There is NO group as a whole. There USED to be some people posting a “FUNNY” idea on some chan board (site and game raids) in which anyone&everyone could comment on and add to. That is exactly how Scientology raids started, not as protesting, but because they were a “fun” bunch to target. If there was any press, then it was laughed at because they realized how stupid people would have to be to take them seriously. Even if any of those things were dickish, all of it was petty compared to worse things that happen online (equivalent of teenagers spray painting penises, compared to bank theft) and all of which was done without the delusion they were some elite badass hackers.
Now it’s changed to, exactly as you put it, “script kiddies and impressionable, wannabe hackers who are just begging for attention”, or bored college kid protesters who listen to Alex Jones – because they saw a spooky Anon Youtube video. So the worse thing they could do is try to convince some OTHER moron that they ARE a “badass hacker” with the intention of getting more skid tools/backing.
And now your comments section will be shit up for months after someone posts this on a chan board and you’ll have 90 pages of teenagers calling you a “Faggot” and photoshopping your head.
You had it right at the first thought, don’t even bother giving them ANY attention.
You’re right, I normally don’t cover this stuff. One reason I did in this case was because some folks had asked me what I thought, and I actually agreed with the thrust of the DHS advisory for once.
But I can tell you that the banking industry is very much concerned about these attacks aimed at knocking their sites offline. They’re extremely disruptive and costly for the banks, which have to talk customer who conflate availability with security down off the ledges.
When millions of customers can’t get to their accounts because some lame hacker group took the bank’s site down, that’s a fairly big deal for the bank and for the customers, regardless of the skill set of the attackers.
The Izz ad-Din al-Qassam Cyber Fighters part of it, that is interesting though. I don’t think OpUSA would have their backing so much as I’d think they stumbled across their stuff. So, either way, this is Izz ad-Din al-Qassam (what a mouthful) all the way.
I agree with the DHS too, in the exact same sense you do of “have these kids, in their habit of using other peoples tools IRONICALLY become a TOOL themselves of actual people capable of damage in all their ignorance?”
And that part is so sad, it’s almost funny.
I’m also more posting that bit of history here because not a lot of people DON’T view Anonymous as some “elite hackers”, you know, the very people that don’t follow security.
One bad thing is though is you get one script kiddie with enough money to buy/hire a botnet you have a whole different story
Well said Bro . We do what we have to do , if we dont then the question is why we did not .
For the record.. those were a group of kids that took the name of my crew to get them famous. they are NOT affiliated with the original #n4m3Le55 Cr3w http://pastebin.com/SET1TrjZ i need to make sure everyone knows. I am one of the original founders of the crew. These guys are NOT affiliated with me. You can email me at n4m3le55cr3w@hush.com or contact me on twitter if you need anything http://www.twitter.com/an0nfl
Thank you!
Actually FWIW as I understand the course of events the protests against Scientology were actually the first time that Anonymous organised as an “entity” and conducted a concerted protest. It wasn’t just done purely for “the lulz” (juvenile amusement and fun).
Although as I once read in an article – to paraphrase: everything you read about Anonymous is wrong including what you are reading now 😉
It was the first time a group of college kids bought a bunch of Guys Fawkes masks from Amazon and actually went outside for a day, yes. Exposing Scientology isn’t a bad thing, but doing it with unwarranted self importance isn’t good.
The Anon site raids and messing with loony organizations however, that practice is as old as the chan boards themselves. One of the first petty ones that gained media attention was the Habbo Hotel raids. But now with so many different meme wikis, the knowledge while even not being very exclusive in its self, is easily picked up byall sorts of new types. The ancient meme usage of OpUSA is a sign of that, that stuff was old back in 2008.
That hard-coded string appears to contain an IP address for a Verizon server in New Jersey. Is that just misdirection?
Very likely misdirection. The IP is answering HTTP like an Akamai node and the rest of the string looks like a microsecond timestamp in “Unix epoch” time (2013-04-09 15:38:03 and change UTC) It’s not hard to find cookies with very similar format. Obviously if it IS a cookie of some sort it MIGHT be trackable to a clicktrail of some sort somewhere, but one would need to look at the context to figure out where. Seems like an easy sort of string to invent & drop into an exploit as intentional misdirection, i.e. to get investigators to chase a ghost cookie that never really existed outside of the script or (better) which was sniffed at random at a NJ Starbucks.
I read the message on the pastebin site. That made my day with the rambling going on and on. It sounded like the person who wrote it was a total lunatic
I think its posting is mertited. Think of this, if anything its an awareness training of what is out their and potentially what they are capable of doing.
OP Israel was more bark than bite, it seemed that they got into alot of sites, but not much “damage” was done. That could have been a pre-cursor for what their true attck was going to be – vs the USA.
Sure its lmost like a form of terrorism – they make a statement and people knee-jerk, panic and act worse than “normal”. The LAN is falling, and the old charlie chaplin firemans firetruck fiasco comes to mind.
In my opinion, they gave the USA too much time to “prepare”. I don’t mean the businesses and lower government agencies, but some of the “agencies” that wish to see what type of affect this sort of attack could cause.
It may involve more countries than you think. If there are scheduled DDoS attacks planned on goverment sites, what prevents other, non-announced / supposedly non-participating countries from getting in the ruccus and looking around? Any countries ticked off at the USA ? I can think of a few.
They will attempt and may be successful at geting in. DHS reports in their infrastructure report of the last few days that the Army Corps of Engeneers Dam information may have been breached. Add in the Department of Labor spreading “Poison Ivy”, and the list slowly grows.
I am sure through propaganda, some of the sites and eventual numbers will be hyped up beyond belief, but it is better safe than sorry. Ignornace is bliss until an agency beats on doors and they want to know why the servers are part of a DDoS attack against USA assets.
If anything, its a small gesture to get IA and CND folks to break out any incident management books and have a refresh of what may come. Update the points of contact while u r at it.
This probably has been going on for a while, and they have a list of specific sites they plan on hitting, or have compromised already. If you from this date, back a year – there have been a LOT of breaches, and this “event” only offers the opportunity for more of the same.
Operation USA is a 34 year old international relief agency and is also known as OpUSA. We are in no way connected to these idiots using our name and if we could find them and they were someplace with a functioning legal system, we’d put an end to their using our name. Hope people don’t confuse what may happen on May 7 with our charity! http://www.opusa.org
Times are tough; you guys could use a little better financial control in your organization.
I suppose you were picked because of the “USA” in your name – evil does not want the world to know where the charity is actually coming from.
I pray for organizations like yours; we all should pray!
Why May 7th? It’s a Tuesday, it’s not the beginning or the end of anything I’m aware of. It’s not close to a pay day or a day that most people would pay bills. I Googled it and didn’t find any real historical, religious, or symbolic significance (although one site did say that this was the day that Martin Lawrence had a nervous break down).
I read through some of the pastebin ranting, but I still don’t see a connection to the date. BTW, paragraphs please! Giant grammatically challenged walls of textZ do not convey your message well.
Anyway, I think this article could be summed up by saying the following: Wall of Text predicts large bot net may continue to attack financial industry after reinventing it’s marketing approach. Customers are cautioned not to pay bills or withdraw money on what can only be called the worst day EVERz to launch a DDOS attack.
To present a somewhat contrary, yet hopefully not FUD-laiden viewpoint:
I find it alarming how many people seem to be immediately ridiculing and downplaying a direct threat issued toward US infrastructure, just because of the alleged minimization of the Israeli impact–a ridicule which seems embodied by the tone of the DHS release itself, which seems kind of haughty and dismissive.
The problem is that amidst all this holier than thou discrediting coolness–undoubtedly crafted at least partially in order to encourage keeping cool heads–I see very little evidence of very much actual threat level research being done to warrant such apathy in an industry which prides itself on proactivity and preparation. Where are the Danchevs in this week’s blabosphere?
I see mostly people who seem to hunger more for being seen to minimize the threat than people willing to actually analyze it in depth. Embodied by the first reply to this thread, which is the essence of individual security theater–be sure to cynically downplay any threat as “kiddiez” for which I hold no personal accountability because the only consequence of taking such a stance is the potential benefit of people viewing me as wise and discriminating. Whatever.
One affiliated group has been seriously deteriorating various parts of US financial infrastructure for almost a year now, and several of the other actors command a relatively heavy presence in defacement archives, to say nothing of other joiners we don’t even know about who might like to use this as cover, from GUI-clickers up to the APT level. Several of the attackers planning involvement are suspected to have APT level skills.
Not all critical sites have DDOS protection, and with just the number of bots implied by the defacement counts of the declared actors, it’s entirely possible that thousands of EDNS casualities could be abused to multiply force to a continuous assault equivalent to a 120,000+ host botnet in a relatively short period of time, if they are so motivated.
What’s more, brute power tools are not even necessary if and when layer 7 http request malformation tools are deployed against vulnerable webserver versions, all the layer 4 filtering devices in the world aren’t going to stop inbound port 80 traffic that is busted at layer 7.
Maybe we’ve become complacent because the banking industry has endured these attacks for so long, that we must suppose they’re not impactful. Except that big bank security people tend to be of a higher skill level than your average Joe I.T. who is in charge of a lot of the sites that will probably get flooded next week.
So maybe less dopey cynicism and more analysis, eh? Taking security threats seriously is our JOB.
You make a lot of great points. My previous post notwithstanding, I don’t really see anything in the above article or your reply that leads me to believe that any of this is new. The same threat existed last year, did it not?
Yes, it’s likely that someone will eventually make good on these threats. I don’t know what job any single individual has to stop it. It seems more like a systemic problem that will never be fixed unless something like this actually occurs, imo.
I’m not cheering for the bad guys here, but it’s a storm that either demands change or delivers more of the status quo. In many ways, these threats are like weather reports and you either bring an umbrella or you get wet.
…and back to what our jobs are. I have a related job (ever so indirectly) where I’m interested in this stuff. But APT’s? Even if I were a CISO of a major bank I’m not sure it’s really my job to stop that any more than it’s my job to stop an invasion from a foreign country.
Businesses only need to develop “commercially reasonable” controls and polices to avoid civil or criminal liability; or so it would seem based on the last 50 years of history.
So if the DHS can’t handle it, what exactly are “we” supposed to do then? Maybe I’m complete off base here and everyone else but me is a top level government cyber ninja.
You hit that right on the money – My view – Our “cyber-security” is a joke in the US – and we have a president only willing to lead from behind.
No soldier respects that!
I went through those toys they listed in that pastebin link. All of them are picked up by malware scanners and VirusTotal (usually 20-40 detection ratio). They’re all 3+ years old, probably older. A lot are even flagged as W32.Sality. There’s also more DDoS junk than I can count. No doubt someone is walking around with these on their USB keychain, feeling like Neo from da Matrix.
But, this sort of further tells me they’re bluffing or the Izz ad-Din al-Qassam Cyber Fighters are using N4M3LE55 CR3W as puppets.
Tiny little nitpick: the classification U//FOUO means that the FBI document is UNclassified, just marked for official use only.
Jake, with whom/what are you picking nits? Did someone claim this document was classified? I don’t see that, in the article or the comments.
Whoops, my bad. Saw “confidential” and read “classified.”
Brian,
What he is trying to say, is that the document is Unclassified, but it may contain sensitive data.
Point blank – The FOUO can sometimes mention information that the general public shouldn’t know about.
For example, lets say we have a FOUO document that is sent to organizations. Its more of a heads up for those establishments. Its meant to – in most instances – to fly below the radar.
The reason for the FOUO designation is to let the establishments and organizations to know what to look for, and not let the people on the “dark side” know what the immediate focus is.
Though “unclassified for Official use only” – the information, as indicated above – can contain some sensitive data.
I have dealt with this type of “information” for over 30 years, and if the right heads turn in the direction of FOUO they will ask questions. That’s not a threat – just be aware of the impact of posting the FOUO information before doing so.
IF there were “traps” being placed to nab some of these guys, posting this type of FOUO information may change the potential outcome.
May be – but we’ve seen such abuse in “top secret” information by our government, that we’ve become not only ambivalent to it, but actually quite irritated.
Confidential information should be tactically and actually confidential – all other information should be freely available, as that is a TOP strength of a free society. We can thus blow the whistle on the wolves among us!
What is Tuesday, May 7? One day after businesses-small, medium, and large- turn on their out of date compromised desktops on Monday, May 6.
So it’s a patch Tuesday? Do the bad guys (does anyone) work that fast? Do you think maybe we’re giving people a little too much credit here?
Is it official ? Has this even started ? I don’t see much chatter about this…..
Should this be renamed to…….
FLOP USA ?
“While the al-Qassam Cyber Fighters, a group that claimed responsibility for a slew of attacks on U.S. banks, has distanced itself from OpUSA, Radware warned the operation could gain new recruits.”
http://www.foxbusiness.com/technology/2013/05/07/hackers-launch-opusa-targeting-banks-government-agencies/
Which in turn quotes Krebs.
But, basically the only group that held any slight threat didn’t want to be associated with them, which was pretty self evident it’d go that way.
http://news.softpedia.com/news/Thousands-of-Sites-Hacked-for-OpUSA-but-Not-All-Hacktivists-Support-the-Campaign-351197.shtml
“Anonymous is a leaderless group and these attacks are being carried out by Muslim extremists and we are asking all domestic Anons not to participate in this OpUSA,” one Anonymous hacker told us.
“We have noticed that all of the people taking part in this operation have never been part of our group before. They are all new users. Anyone can claim to be part of Anonymous.”
Not even a Patch Tuesday. It seems to me they may have picked an arbitrary day to conduct this activity, as nothing significant (except Martin Lawrence losing his marbles) happened today. Trying to get into the history books, I suppose…