The recent data breach at Adobe that exposed user account information and prompted a flurry of password reset emails impacted at least 38 million users, the company now says. It also appears that the already massive source code leak at Adobe is broadening to include the company’s Photoshop family of graphical design products.
In a breach first announced on this blog Oct. 3, 2013, Adobe said hackers had stolen nearly 3 million encrypted customer credit card records, as well as login data for an undetermined number of Adobe user accounts.
At the time, a massive trove of stolen Adobe account data viewed by KrebsOnSecurity indicated that — in addition to the credit card records — tens of millions of user accounts across various Adobe online properties may have been compromised in the break-in. It was difficult to fully examine many of the files on the hackers’ server that housed the stolen source because many of the directories were password protected, and Adobe was reluctant to speculate on the number of users potentially impacted.
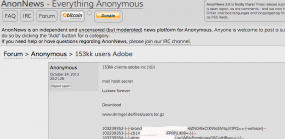
But just this past weekend, AnonNews.org posted a huge file called “users.tar.gz” that appears to include more than 150 million username and hashed password pairs taken from Adobe. The 3.8 GB file looks to be the same one Hold Security CISO Alex Holden and I found on the server with the other data stolen from Adobe.
Adobe spokesperson Heather Edell said the company has just completed a campaign to contact active users whose user IDs with valid, encrypted password information was stolen, urging those users to reset their passwords. She said Adobe has no indication that there has been any unauthorized activity on any Adobe ID involved in the incident.
“So far, our investigation has confirmed that the attackers obtained access to Adobe IDs and (what were at the time valid), encrypted passwords for approximately 38 million active users,” Edell said [emphasis added]. “We have completed email notification of these users. We also have reset the passwords for all Adobe IDs with valid, encrypted passwords that we believe were involved in the incident—regardless of whether those users are active or not.”
Edell said Adobe believes that the attackers also obtained access to many invalid Adobe IDs, inactive Adobe IDs, Adobe IDs with invalid encrypted passwords, and test account data. “We are still in the process of investigating the number of inactive, invalid and test accounts involved in the incident,” she wrote in an email. “Our notification to inactive users is ongoing.”
Part of the Adobe breach involved the theft of source code for Adobe Acrobat and Reader, as well as its ColdFusion Web application platform. Among the cache was a 2.56 GB-sized file called ph1.tar.gz, but KrebsOnSecurity and Hold Security were unable to crack the password on the archive. Over this past weekend, AnonNews.org posted a file by the same name and size that was not password protected, and appeared to be source code for Adobe Photoshop.
Asked about the AnonNews posting’s similarities to the leaked source code troves discovered by this publication in late September, Adobe’s Edell said indeed that it appears the intruders got at least some of the Photoshop source code. In both cases, Adobe said it contacted the sites hosting the data linked to from the AnonNews postings and had the information taken down.
“Our investigation to date indicates that a portion of Photoshop source code was accessed by the attackers as part of the incident Adobe publicly disclosed on Oct. 3,” Edell wrote.
FREE CREDIT MONITORING?
As many readers have pointed out in comments on previous KrebsOnSecurity posts, Adobe has offered a year’s worth of credit monitoring to customers whose encrypted credit card data was stolen in the breach. As it happens, Adobe’s offering comes through Experian, one of the three major credit bureaus and a company that is still reeling from a security breach in which the company was tricked into selling consumer records directly to an online identity theft service.
One of the most frequently asked questions I receive involves whether readers should take advantage of credit monitoring services, particularly those offered for free by the major credit bureaus in response to some breach. My response is usually that free credit monitoring generally can’t hurt, as long as you’re not automatically signed up for a non-free monitoring service after the free period expires. Monitoring especially makes sense if you’ve been the victim of ID theft before.
But bear in mind that having your credit card information stolen is not the same thing as identity theft — which generally involves the fraudulent opening of new accounts in your name. Some types of ID theft involve the creation of synthetic identities — using parts of your personal information combined with some aspects that are not yours — and credit monitoring services may have a hard time detecting these types of accounts.
For consumers reacting to news about their credit or debit card being compromised, it probably makes more sense to opt for placing fraud alerts and obtaining free copies of your credit report several times annually, as specified by law. And remember that the card associations all have zero-liability policies.
A big part of monitoring your credit involves checking your credit file for oddities and errors. The credit bureaus would prefer that you purchased a copy of your credit report from them (the annoyingly catchy commercials for freecreditreport.com, for example, are advertisements for Experian’s service). But this is completely unnecessary. U.S. consumers are entitled to a free credit report from each of the three major bureaus once per year, via annualcreditreport.com. That means that roughly every four months, you should be able to get an updated copy of your credit report from one of the three bureaus (calendar reminders come in handy here).
But back to the question about credit monitoring: Having been the recipient of a large number of attempts to open new lines of credit in my name, I have chosen to take advantage of a credit monitoring service, but it is not one of the services offered by the three bureaus (and I’ll leave it at that). The main reason for this is that if you run into a situation (as I am in now) where particular credit grantors consistently fail to remove fraudulent credit inquiries that negatively affect your credit score and file, you may eventually need to take that up directly with the credit bureaus.
While it may be tempting to believe that paying Experian or one of the other credit bureaus (Equifax or Trans Union) to monitor your file might make them more likely to help you in this situation, there is absolutely nothing in the fine print that says they will. Also, remember that these are the same companies that are tricking consumers into paying for free credit reports and making money hand over fist selling your credit information to would-be creditors and marketers (or in the case of Experian, even to ID theft services).
As mentioned earlier, consumers also are entitled to place a fraud alert on their credit files, and to require that potential creditors first get the consumer’s approval — such as via a phone call — before granting any new lines of credit. The protections are more strict if consumers can show they’ve been victims of identity theft – in that case the fraud alert stays in the files of identity theft victims for seven years. While a regular fraud alert expires after 90 days, consumers can simply renew the alert online when the old one expires. The credit bureau with which you file the alert is required by law to share it with the other two agencies.
Finally, consumers always have the option of placing a security freeze on their credit file — which blocks creditors from accessing your credit reports until the freeze is lifted. It generally costs $10 to place a freeze and another $10 to thaw it if you ever want to buy a new car or open a new line of credit. This may sound like a hassle, but it may ultimately make more sense than paying $15 a month for a credit monitoring service, or trying to remember to file new fraud alerts every 90 days.
Update: Oct. 29, 9:26 p.m. ET: Modified paraphrasing of Edell’s comment on completing the notification campaign, from “..to contact existing users whose login and encrypted password information was stolen,” to the current text.




So much for alerting customers. My account was compromised according to the database hacked accounts lastpass have.
I am still to receive an email from Adboe. Of courser I changed my password regardless.
My exact same comment. I have not heard from Adobe but was advised by my mobile AV vendor that I was in the list.
I just received an email which may be attempting to exploit the Adobe theft of source code. They start by offering to sell the Adobe CS 6 suite and training video, then offer the MS Win 8.1 Pro version. They point out that it’s the promo version of Win 8.1 without activation files, so can be installed on multiple computers. No MS support, of course. Sent from overseas, only $50 via Western Union. You can even examine the product (see if your computer can read the files), then send the money and receive a code number for installation. Enticing, but a total scam, and you wonder what else gets installed besides the OS.
Haven’t used Adobe products for years. I use open-source products that I have thoroughly researched and do not set up auto updates, register or allow statistic feedback. I also run a two malware programs on the exe file before I run it.
Just sayin’
So Adobe are only contacting their paying customers?
Is that what they mean by “completed a campaign to contact active users whose user IDs with valid, encrypted password information was stolen”?
They didn’t contact me to inform me that my data was stolen. I’m active all right. Alive and kicking.
Tossers.
I already received email from Lookout that my email was in the list and that I should take precautions. No emails or any warnings received from Adobe..
Same here.
Same here as well.
Same here, received email from lookout, nothing from Adobe. Absolutely disgusting.
So the anons hacked adobe?
I wouldn’t trust the email from lookout. Click their link, give them all your information and reset your password from a link that im not 100% positive is even really from lookout?, Im not going to play that game. Ill wait to see if adobe sendsme anything…
Once you change your password, adobe will send you an email to inform you of the change.
I received a letter in the mail from Adobe today (Nov 20th) informing me that my info was among the ones compromised- the letter was dated October 23rd. TOOK ALMOST A MONTH for the letter to travel through the post from US to Finland!!! Has Adobe not heard of airmail!?!? WOW- canceled my credit card and will receive an other with a new number in a week. How on earth can they not inform their regular customers a bit faster of such an important matter?
Same here; but mine arrived to my address in Melbourne, Vic, today (27th Nov): envelope is stamped the 25th Nov, and letter is dated 23rd Oct. Pretty disgusting on Adobe’s behalf.
http://timesofindia.indiatimes.com/tech/tech-news/internet/Adobe-struggling-with-data-breach-notification/articleshow/26400902.cms
Excerpt:
Adobe Systems Inc said it is taking longer than expected to warn customers about a massive data breach that compromised data on tens of millions of people, leaving some in the dark 10 weeks after the attack was discovered.
That puts those who have yet to be alerted at increased risk of cyber-scams and identity theft, because part of the massive trove of data stolen from Adobe is circulating on the Internet.
“This is a pretty massive screw-up,” said Chester Wisniewski, a senior security advisor at anti-virus software maker Sophos. “Anybody can go and download the list. It’s not a secret.”
Adobe identified the attack on September 17 and began notifying customers “immediately” after it disclosed the breach on October 3, according to company spokeswoman Heather Edell.
“Email notifications are taking longer than we anticipated,” she said.
The company has had to validate email addresses of those affected, and also limit the number of notifications sent at any one time to make sure they don’t get blocked by email providers or tagged as spam, she said.
(snip)
I received a letter from adobe2 days ago telling me that my details have been compromised. Also a week ago i get a call from my bank 6am telling me that my credit card has been charged and then reversed. They caught it before charges could be processed and have blocked my account luckily.
Weird thing is that the letter I received is from Adobe Ireland and i am in brisbane Australia. Shouldn’t adobe Australia notify the customers in Australia? And what is up with Adobe saying that they have notified customers via email? no email arrived in my mailbox.And if it did it would be deleted.
How can they notify people about this in an email? Are there any people with brains switched on at Adobe? People receive hundreds of these scam emails about resetting accounts etc. all the time. Isn’t it obvious that WE cannot trust these emails and is virtually impossible to know is it a real or scam email?
Finally and most importantly, how do we trust Adobe again? Us finding out a month later when most of the people have been relieved of their money – thanks Adobe for being so quick about it. And do I give you my Credit Card details again?
I don’t bloody think so.
Final thought. It is funny to say that we might be much safer to use cracked versions of Adobe software. At least we are running less chance of our credit card details being stolen. Think about this adobe.