Scam artists who deploy credit and debit card skimmers most often target ATMs, yet thieves can also use inexpensive, store-bought skimming devices to compromise modern-day cash registers. Just this past weekend, for instance, department store chain Nordstrom said it found a half-dozen of these skimmers affixed to registers at a store in Florida.
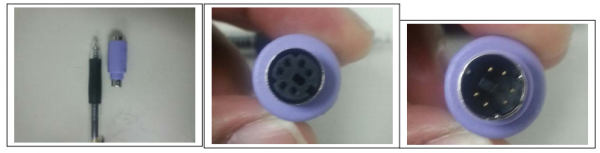
The fraud devices in this case resemble small keyloggers that are sold by dozens of stores for approximately $30 to $40 apiece. These hardware keyloggers are essentially Ps/2 connectors that are about an inch in length. The tiny data storage devices are usually purple in color to match the color-coded standard for keyboards, and are made to be inserted between the male end of a PS/2 keyboard connector and the female receptor on a computer.
According to an alert circulated by the police department in Aventura, Florida, on the afternoon of Saturday, Oct. 5, 2013, three male subjects were captured on closed-circuit cameras at Nordstrom tampering with registers in the store. Authorities there say the footage showed two of the men worked to distract sales staff, while the third took pictures of the register and removed the rear access panel to the register and took additional photographs.
Several hours later, three different males returned to the store and performed the same routine: Two of them again distracted sales staff while the third male removed the back panel to the register and installed the above pictured device. The Aventura Police Department said Nordstrom located a total of six devices attached to their registers.
“The subjects then return at a later date to recover the devices and create fake credit cards for fraud,” the Aventura PD stated in a memo describing how the thieves would complete their scam. “The connector was made to match the connections on the back of the register to include color match. Therefore, no one would have detected it unless there was a problem with the register.”
The Aventura PD did not return calls seeking comment. Nordstrom spokeswoman Kara Darrow said the company believes the skimmer incident is limited to one store location. She said it’s not clear yet if any of the men caught on camera were arrested, or if they tried to return to the store to retrieve the devices.
“We did find some unauthorized devices on some of our cash registers,” Darrow said. “”It’s not anything broader at this point. As soon as we figured out this was happening, we had forensics experts looking at the situation, but it’s still very early in our investigation.”
Skimmer scammers who place these devices on cash registers may not need to return to the scene of the crime to retrieve the stolen card data: I found several of these hardware keyloggers that include 2 GB of storage and built-in wireless support that allows the devices to connect to a local wireless network and send email reports of the stolen data.
Although the color and shape of these PS/2-based skimmers indicates that they are designed to interface with a keyboard, that does not mean they can’t steal data from a credit card reader. Many cash registers at retailers have PS2-based card readers, or connect the card reader directly to the computer’s keyboard.




Good stuff. I would point out that if the credit card reader encrypted on-board, this logger should be useless. I thought that PCI required that now.
Merely encrypting within the PIN pad is not enough. Encryption needs to be point to point from the PIN pad all the way through the network to the payment processor. However not all payment processors support point to point encryption (as ours does not) so our payment transactions are in the clear but within a private, controlled network.
Then again, encryption over the PS2 wire just means that they’d need to capture data further upstream. I’m sure the credit card scanners themselves are some off-the-shelf device, so the thieves could just go buy one of the same model, embed a bug inside it, and then swap it out for the real one.
Or even simpler, they could just happen to be playing with their smartphone when the customer in front of them pulls out their credit card, and then snap a 41-megapixel photo that just happens to include the card number and expiration date. People aren’t terribly protective of their card numbers.
Brian, “People aren’t terribly protective of their card numbers.”
If you never, ever share your credit card number with anyone, it becomes a bit problematic to use it to buy stuff.
Talk about dumb criminals. You’d think everyone would know by now, they used video surveillance. Maybe they figured no one was reviewing the footage? Jeeze!
Or maybe it wasn’t a concern?
Pick a location far enough from home, use loggers that transmit their data wirelessly, and once set up the miscreants don’t need to reveal themselves again. So while they may be on camera, what’s the big deal if they’re multiple states over banking on that data committing online fraud now.
Good point! Thanks for posting! 😀
Or, if they’re dumb and use public internet, just poison the network, intercept the traffic, find the video cameras(if sent over wireless/bluetooth), create a loop in the video, then distract the guards/manager.
VERY good point BV1!!!
But, if facial recognition continues to grow under all the disparate law enforcement entities and IF the perps, errr, the thieves already have their mug shots in the system, then it would only be a matter of time before the perps, dang – the thieves are picked up.
— maybe….
This happens far more than what many people might realize. It is true JCitizen that most department stores do not actually review the video footage. They are understaffed and the video is only referred to after an incident! The criminals were actually pretty slick and if the store employees wouldn’t have been on their toes then they would have recovered their ill gotten booty!
What likely happened is some other incident (e.g. shoplifting) happened on the day in question, probably around the same time but in a different part of the store, and the footage was reviewed to provide details from that incident, at which point this operation was discovered.
I don’t know what counts as a department store over in the US but here some have rooms that look something like NASA Mission Control to watch over the store in real time.
The Target stores supposedly have some sophisticated monitoring of all the CCTV’s inside and outside the building. It lowers the chance of shoplifting which keeps profits in house rather than out the door.
In a situation like this, its crazy to think that in “broad daylight” that an unauthorized person is messing with a cash register. The stores must not be crowded, thats for sure, otherwise some one may have seen and reported the act.
I am just surprised the cash registers are loose like that. typically the registers are in a make shift booth and they aren’t going anywhere. They could easily be secured down.
This type of bold move by the crooks does sound like they know some one from the inside. They may know the people who are easy to distract. Plus it probably doesnt take a lot of time to insert one of these devices.
The setups are probably very close to the same at each store. All it takes is learning the name or two of people who work at the store, memorize some of the info off social media sites, walk in and start a general conversation about them and in 2 minutes max per cash register, the job is done.
And realize, that a typical big box retailer (Target, Wal-Mart, etc.) tends to have all it’s registers in the front of the store where it is easier to monitor and spot activity like this. Department stores have registers scattered throughout the store, most of them not always staffed. So installing these would be pretty easy once you identified times of day with lower volumes where there are likely unmanned registers and fewer staff to be noticing the odd behavior.
But even the cash lane setup isn’t immune. Think back to the Shaw’s and Hannaford issues of several years ago where crooks installed skimmers on the card swipe devices.
Yes, more and more of the big retailers are using preventive theft measures, i.e. possible shoplifting software.
The technique supposedly uses advanced algorithms to determine the likelihood of an individual(s) ripping off the store.
It looks at things such as:
lingering in an aisle for a long time, coming back to the same aisle spot multiple times, wandering around the store multiple times, looking furtively over their shoulders, etc….
Some versions of this monitoring software evens extends out to the parking lot. And the developers along with the retailers are constantly improving the success rates of this kind of software.
I think that you will find that not actively watching displays is the norm, not the exception. Most installations have multiple cameras, and if they use split or cubed screens, the individual views are so small it is hard to tell what is happening. If you have full sized displays you may not have enough wall space.
There may be exceptions such as watching a few specific cameras, but it is safe to say that no one is watching. In some situations software is watching and flashes an alert to suspicious activity, but this is also the exception.
It may be said that most CCTV installations are good for forensic investigations, but not actively preventing unlawful actions.
Most camera installations I’ve put in are not actively monitored but only used in the event of something happening whether it be a health and safety perspective, theft or something along those lines. I’d so those that are actively monitored are very rare indeed.
Any idea who or what is behind this website? This has got to be a scam, but I can’t pin down the “gotcha”.
employmentpay[dot]com
Spammity spam spam spam.
It’s an honest question.
It looks to me like it’s more of a scam than a technically malicious site.
But I don’t like spam.
McAfee reports minimal risk – but I’m not sure I trust them. Web-Of-Trust(WOT) has no reports, so it is a risk, as far as I’m concerned, until it gets a reputation.
Funny, I typically consider sites too new for WOT to have any data as “likely malicious”. But then again, I’m a skeptic.
Totally agree!
Here, add this to your bookmarks:
https://www.virustotal.com/en/#url
(or just go to VirusTotal and click on URL scanner)
ESET has it labeled as Job Search.
http://kb.eset.com/esetkb/index?page=content&id=SOLN141
Thanks for the Virustotal URL. It had two negative hits. I noticed that Symantec’s Norton Safe Web was not polled so here is the Safe Web URL: https://safeweb.norton.com/report/show?url=www.employmentpay.com . Norton has not rated the site yet which I take as a bad sign because I assume that an honest business would make an effort to have the major AV vendors give the site a clean bill of health. Call me Old School.
From my experience, just be careful with CLEAN MX, Fortinet, Sophos, ParetoLogic and sometimes even Websense ThreatSeeker. Those are the equivalent of ClamAV for being false positive trigger happy. And even then newer threats, or sites that don’t host malware but are still shady might not be picked up for a while. But, if a site does get picked up (even by a false positive) they do share that site with all the AVs they partner with, so sometimes you can help spread the word that way. The “Additional information” can be helpful too.
But the url scanner is best used for download link scanning though. That way the file in question is never downloaded to your PC, but goes straight to VirusTotal.
Oh, just noticed BitDefender has it flagged now. “The URL domain/host was seen to host badware at some point in time”. So yeah, if BitDefender flags it then it’s a pretty shady site. They have a good track record in my experience.
I’ll buy that for a dollar! 😀
From software scam to hardware skim 🙂 hardware is more trustable than software …
You hope – most chips are made in China, and there has been doping in the past.
For goodness’ sake. I’ve always wondered how criminals get the skimmers on inside-store registers, but I hadn’t realized how small those things have gotten. And wireless to boot? One of these days we’ll be reading about the criminals walking around with skimmers in their ears and picking up credit card numbers in the airwaves.
Or is it already happening and I missed that post?!
It’s not wireless, it stores the logged data on-board. The thieves would have to come back and recover the device at a later time. These were actually designed originally as physical keyloggers. You could sneak into an office, say masquerading as an exterminator, crawl around under desks and install these
I didn’t read any articles other than here from Krebs to know what hard facts there are out there about this attempted heist, but a 2 second web search and you can find pages of results. Standard spec is 2 gigs of storage with wifi in a package that looks identical to those pictured above. So yea they could be sending captured data home via wifi
Yes,
Brian linked to a search to the wireless models:
“I found several of these hardware keyloggers that include 2 GB of storage and built-in wireless support that allows the devices to connect to a local wireless network and send email reports of the stolen data.”
They are exactly the same size, only the price is 140USD and not 40USD for the wireless model. I guess even have AP functionality and not only client wifi. They take advantage on the fact that plenty of power is available on the PS/2 connector, no need to integrate bulky batteries.
Evil stuff, if you ask me, and I cannot think of one single legitimate use.
There exist legitimate uses for keystroke loggers, but certainly not as many as illegitimate ones.
It’s becoming a popular idea to record everything you do, to be able to construct analytics for your own life. Stephen Wolfram does this, for example.
they have for a while now with RFID cards, you gotta keep it in tinfoil.
I noticed at Kmart stores that their registers are wide open in the back and anyone can put one of these key-loggers in the necessary ports. All one has to do is find the cable that goes to the card reader unit, and “tap” into it, using one of these units.
I don’t know if Kmart card readers use encryption, but if they didn’t this would be a be a very viable way of getting credit card numbers from a well known big box retail store. However, I doubt this would be very easy , since the store has overhead camera surveillance in that location.
You would think K-Mart wouldn’t be worth the low-limits ‘poor’ people have on said credit cards compared to nordstrom?
http://www.kansas.com/2013/10/09/v-print/3049072/cyberattack-on-wichitas-computers.html
http://articles.kwch.com/2013-10-08/website-hacking_42803152
http://www.scmagazine.com/not-in-kansas-anymore-thousands-affected-by-wichita-website-hack/article/315305/
Story on hack of e-procurement website in Wichita, KS by Turkish hackers – most likely by SQL injection, apparently other cities also involved.
Wow, I didn’t even know that was possible to do.
I must be really ignorant, I assumed these types of devices would only be for sale in a dark alley (figuratively speaking) but even Sears sells them. That’s why I read this site, I get useful info here.
They’re on sale in the open because businesses are one their customers. Bosses put them on company computers to track employee activity. It’s a lower-tech monitoring method for smaller companies that don’t have network-based monitoring capability.
The last Nordstrom I was in was using mobile POS units. So I think that would very difficult surveliance to set up and monitor.
I would think that the thing that got them noticed was an interuption in the pc functionality. PS2 is not a hot swappable device…sometimes they will continue to work if unplugged and reinserted, but most times a reboot is required to get the pc to recognize the equipment. So most likely one of the keyboards stopped working and it was reported and a tech found the insterted skimmer when looking at the connections. The video was probably only looked at to see who put it on there.
Lets not forget: most chain stores are on consignment these days.
Home Depot etc. They don’t get hit when actual theft occurs.