Over the past several weeks, a handful of frantic Microsoft Windows users have written in to ask what they might do to recover from PC infections from “CryptoLocker,” the generic name for an increasingly prevalent and nasty strain of malicious software that encrypts your files until you pay a ransom. Unfortunately, the answer for these folks is usually either to pay up or suck it up. This post offers a few pointers to help readers avoid becoming the next victim.
According to reports from security firms, CryptoLocker is most often spread through booby-trapped email attachments, but the malware also can be deployed by hacked and malicious Web sites by exploiting outdated browser plugins.
The trouble with CryptoLocker is not so much in removing the malware — that process appears to be surprisingly trivial in most cases. The real bummer is that all of your important files — pictures, documents, movies, MP3s — will remain scrambled with virtually unbreakable encryption unless and until you pay the ransom demand, which can range from $100 to $300 (and payable only in Bitcoins).
File-encrypting malware is hardly new. This sort of diabolical threat has been around in various incarnations for years, but it seems to have intensified in recent months. For years, security experts have emphasized the importance of backing up one’s files as a hedge against disaster in the wake of a malware infestation. Unfortunately, if your backup drives are connected physically or via the local network to the PC that gets infected with CryptoLocker, your backups may also be encrypted as well.
Computers infected with CryptoLocker may initially show no outward signs of infection; this is because it often takes many hours for the malware to encrypt all of the files on the victim’s PC and attached or networked drives. When that process is complete, however, the malware will display a pop-up message similar to the one pictured above, complete with a countdown timer that gives victims a short window of time in which to decide whether to pay the ransom or lose access to the files forever.
Fortunately, there are a couple of simple and free tools that system administrators and regular home users can use to minimize the threat from CryptoLocker malware. A team of coders and administrators from enterprise consulting firm thirdtier.net have released the CryptoLocker Prevention Kit — a comprehensive set of group policies that can be used to block CryptoLocker infections across a domain. The set of instructions that accompanies this free toolkit is comprehensive and well documented, and the group policies appear to be quite effective.
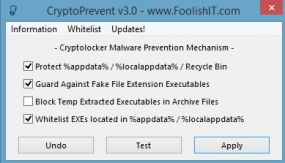
Individual Windows users should check out CryptoPrevent, a tiny utility from John Nicholas Shaw, CEO and developer of Foolish IT, a computer consultancy based in Outer Banks, N.C. Shaw said he created the tool to mimic the actions of the CryptoLocker Prevention Kit, but for home users. So far, he said, the CryptoPrevent installer and its portable version have seen tens of thousands of downloads.
He notes that some antivirus tools have occasionally detected his kit as malicious or suspicious, and that McAfee SiteAdvisor currently lists his domain as potentially dangerous without explaining why (I know how he feels: KrebsOnSecurity.com was at one time flagged as potentially dangerous by this service). In addition, some folks have been thrown by the apparent expletive in his company’s domain name — foolishit.net.
“When I started Foolish IT [back in 2008], I went for the domain foolishtech.com but it wasn’t available and this was one of the suggestions that GoDaddy gave me,” Shaw said. “I thought it was funny and decided to go with it.”
CryptoLocker might be the best advertisement yet for cloud data storage systems. Johnny Kessel, a computer repair consultant with San Diego-based KitRx, has been urging clients to move more of their data to cloud services offered by Google and others. Kessel said one of his clients got hit with CryptoLocker a few weeks ago — losing access to not only the files on the local machine but also the network file server.
“This thing hit like pretty much all the file extensions that are usable, from Mp3s to [Microsoft] Word docs,” Kessel said. “About the only thing it didn’t touch were system files and .exe’s, encrypting most everything else with 2048-bit RSA keys that would take like a quadrillion years to decrypt. Once the infection happens, it can even [spread] from someone on a home PC [using a VPN] to access their work network, and for me that’s the most scary part.”
For further reading on CryptoLocker, please see:
BleepingComputer discussion thread.
Malwarebytes: Cryptolocker Ransomware: What you need to know.
Naked Security (Sophos): Destructive malware Cryptolocker on the loose.
http://www.symantec.com/connect/forums/cryptolocker-and-adc-policies
Reddit thread: Proper care and feeding of your Cryptolocker
Makeuseof.com: Cryptolocker is the nastiest malware ever and here’s what you can do
Ars Technica: You’re infected — if you want to see your data again, pay us $300 in Bitcoins





Cloud storage does not protect you if it is mapped to a drive letter on a protected machine. CryptoLocker will happily encrypt any drive letter it finds regardless of its endpoint.
Yes, but most of these sites have versioning in place and once the actual virus is cleaned, you can pull older copies of your files from there that are not encrypted. Older files are better than no files.
Version will not a help if it’s common to have only one version of something, e.g. your family or holiday photos…
I would think the encrypted version would *be* a second version, thus allowing you to restore to the original.
Cloud storage like DropBox provides no protection if the local client is enabled and connected to the cloud. As the local copy of files in the local DropBox folder are encrypted, the Dropbox client will dutifully synchronize the new and encrypted files up to the cloud overwriting the files there. Any cloud storage that utilizes a local client and folder will have the same issue.
Versioning will not be a help if it’s common to have only one version of something, e.g. your family or holiday photos…
(Sorry… Spelling checker kicked in the first time)
All my files are on my NAS, and the important shares are read only to all normal users. If I want to write to a drive I have to login to the share with a specific admin account.
as for those querying versioning, cloud storage services like http://www.dropbox.com and http://www.copy.com automatically keep back-ups of previous versions for at least a month (more if you have a paid account), so you can “restore” previous unencrypted versions, or absently deleted photos of grandchildren etc.
May be that’s why the Bitcoin price is currently $355 per BTC ? Too many infected victims are looking for Bitcoins 🙂
I asked Foolish IT to reply to the following inquiry: What assurances can you give that CryptoLocker will not exploit the automatic update feature of your paid version of CryptoPrevent to infect the purchaser with a download of the ransom-ware program? Obviously, purchasers of CryptoLocker would be prime targets.
I cannot now find my query after it was initially present and marked as “Comment in Progress.” Brian, could you please check on the security of the automatic update procedure for CryptoPrevent, which I have purchased. Thank you.
Ive dealt with many things virus you name it and nothings beaten me yet…The longest I spent cracking a nasty took a week now I crack them within hours/minutes…COME TO ME OH NASTIES…I need a new laugh…
Not just that some idiot was playing table tennis with my firewall for about a day…I called the police they said it would take upto 48 hours to a possible track…Well 10 minutes later I called them back up with the guys name address contact details everything they said and how did you do that…I just laughed at them and said it aint that hard and said if you need out doing quick you have my details…
Wow this is crazy! I’ve dedicated my time to follow CryptoLocker.
youtube.com/CryptoLocker