Over the past several weeks, a handful of frantic Microsoft Windows users have written in to ask what they might do to recover from PC infections from “CryptoLocker,” the generic name for an increasingly prevalent and nasty strain of malicious software that encrypts your files until you pay a ransom. Unfortunately, the answer for these folks is usually either to pay up or suck it up. This post offers a few pointers to help readers avoid becoming the next victim.
According to reports from security firms, CryptoLocker is most often spread through booby-trapped email attachments, but the malware also can be deployed by hacked and malicious Web sites by exploiting outdated browser plugins.
The trouble with CryptoLocker is not so much in removing the malware — that process appears to be surprisingly trivial in most cases. The real bummer is that all of your important files — pictures, documents, movies, MP3s — will remain scrambled with virtually unbreakable encryption unless and until you pay the ransom demand, which can range from $100 to $300 (and payable only in Bitcoins).
File-encrypting malware is hardly new. This sort of diabolical threat has been around in various incarnations for years, but it seems to have intensified in recent months. For years, security experts have emphasized the importance of backing up one’s files as a hedge against disaster in the wake of a malware infestation. Unfortunately, if your backup drives are connected physically or via the local network to the PC that gets infected with CryptoLocker, your backups may also be encrypted as well.
Computers infected with CryptoLocker may initially show no outward signs of infection; this is because it often takes many hours for the malware to encrypt all of the files on the victim’s PC and attached or networked drives. When that process is complete, however, the malware will display a pop-up message similar to the one pictured above, complete with a countdown timer that gives victims a short window of time in which to decide whether to pay the ransom or lose access to the files forever.
Fortunately, there are a couple of simple and free tools that system administrators and regular home users can use to minimize the threat from CryptoLocker malware. A team of coders and administrators from enterprise consulting firm thirdtier.net have released the CryptoLocker Prevention Kit — a comprehensive set of group policies that can be used to block CryptoLocker infections across a domain. The set of instructions that accompanies this free toolkit is comprehensive and well documented, and the group policies appear to be quite effective.
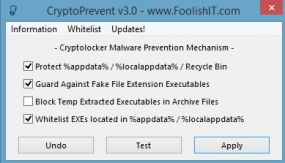
Individual Windows users should check out CryptoPrevent, a tiny utility from John Nicholas Shaw, CEO and developer of Foolish IT, a computer consultancy based in Outer Banks, N.C. Shaw said he created the tool to mimic the actions of the CryptoLocker Prevention Kit, but for home users. So far, he said, the CryptoPrevent installer and its portable version have seen tens of thousands of downloads.
He notes that some antivirus tools have occasionally detected his kit as malicious or suspicious, and that McAfee SiteAdvisor currently lists his domain as potentially dangerous without explaining why (I know how he feels: KrebsOnSecurity.com was at one time flagged as potentially dangerous by this service). In addition, some folks have been thrown by the apparent expletive in his company’s domain name — foolishit.net.
“When I started Foolish IT [back in 2008], I went for the domain foolishtech.com but it wasn’t available and this was one of the suggestions that GoDaddy gave me,” Shaw said. “I thought it was funny and decided to go with it.”
CryptoLocker might be the best advertisement yet for cloud data storage systems. Johnny Kessel, a computer repair consultant with San Diego-based KitRx, has been urging clients to move more of their data to cloud services offered by Google and others. Kessel said one of his clients got hit with CryptoLocker a few weeks ago — losing access to not only the files on the local machine but also the network file server.
“This thing hit like pretty much all the file extensions that are usable, from Mp3s to [Microsoft] Word docs,” Kessel said. “About the only thing it didn’t touch were system files and .exe’s, encrypting most everything else with 2048-bit RSA keys that would take like a quadrillion years to decrypt. Once the infection happens, it can even [spread] from someone on a home PC [using a VPN] to access their work network, and for me that’s the most scary part.”
For further reading on CryptoLocker, please see:
BleepingComputer discussion thread.
Malwarebytes: Cryptolocker Ransomware: What you need to know.
Naked Security (Sophos): Destructive malware Cryptolocker on the loose.
http://www.symantec.com/connect/forums/cryptolocker-and-adc-policies
Reddit thread: Proper care and feeding of your Cryptolocker
Makeuseof.com: Cryptolocker is the nastiest malware ever and here’s what you can do
Ars Technica: You’re infected — if you want to see your data again, pay us $300 in Bitcoins





Ransomware is nothing new, but this is the first I’ve seen that demonstrated this level of technical proficiency. My real concern is that the money they make off the first wave of victims can be poured into improving the attack, buying vulnerabilities, etc. I expect this to get a lot worse before it gets better.
Currently, the infection and spreading mechanism is trivial, and they are targeting low-hanging-fruit users ignorant enough to open an attachment. But if they use that money to buy unlatched vulnerabilities this could get really ugly. I expect them to do a Mac version as well, as those users are not used to thinking defensively, and have statistically higher disposable income to target.
hey…if this kind of advancement is taking place in 21st century…then what will happen in the next generation
will be draine out of wealth…and…what about banks,offices…mnc”s etc
It’s extremely important for every internet user to have full protection via AVG, NORTON or FIREWALL. Google chrome, as well.
You can have FIREWALL, NORTON, AVG, etc., etc. installed until your system runs so glacially slow that you can’t accomplish much of anything and an ignorant user unwilling to learn basic security procedures can still click their way to an infection. You can put all the barriers in the way of them preventing an infection, but if they’re going to download one-time executables (that don’t trigger AV because they’re too new for signatures to exist), run them, allow them access through the firewall, etc. then they’re still going to get infected.
Users who refuse to learn will be burned, the only way to stop them from getting burned is for them to learn, and some people simply refuse to learn no matter how many times they get burned. I call these people willfully ignorant.
what is your take on comodo?
You are kidding right…? Norton is a joke of an AV program…im assuming the AVG program you are referring to is the free one as well…wont do much to defend against something like this…
@Jones
Ok comment until here: I expect them to do a Mac version as well, as those users are not used to thinking defensively, and have statistically higher disposable income to target.
As most Mac users probably migrated from Windows, EVERYONE should know: Don’t open email, and certainly not attachments sent from unknown senders. That’s just Internet 101!
“Don’t open email, and certainly not attachments sent from unknown senders.”
Right. But isn’t the problem that if someone you know gets hacked or infected, their contact list can be compromised, and the email *seems* like it came from someone you know.
I’ve trained my mom so well that she won’t click on links or open attachments even in email from me. I’ve had to start adding a line to the email like, “The dog I had in second grade was name Fido.”, something a hacker wouldn’t likely know. That assures her the email actually *is* from me.
Great Idea!
I’ve always read how for years these types of ransoms were common in eastern europe and always wondered why I never heard of it happening in the USA?
I guess thats changing now, Is it because there is just more bold malicious hackers nowadays?
where are the money pac, bitcoin operations operators? Are there not ways to track the money, so to speak. these have to be random accounts open at a high rate.. with bogus info? what about the exchange?
They are designed to be anonymous and hard to track.
Thats not true, currencies such as “BTC” are not “designed to be hard to trace”. This is not the intention when “designed”.
It makes sense to follow these bitcom accounts, but I don’t understand just how bitcom works.
I wonder if on a network it will encrypt mapped drives? This is starting to really get scarey! Keep up the good work!!
Yup if the mapped drive if contactable then yes it will encrypt the data
To Theresa – yes it also encrypts any mapped drive the impacted user has rights to. It nails any drive letter location across the network.
“CryptoLocker might be the best advertisement yet for cloud data storage systems. ”
Moving data to the cloud(s) doesn’t seem like it would do any better. Cloud(s) seems more venerable than backing up data and putting it in the drawer.
I see retinal scanners and cloud access terminals in the future.
I think the advantage of some cloud services is versioning – yes if you use Google Drive client, the latest cloud version gets encrypted, but you can still access previous versions
Yes but you could implement the same thing using a local backup server that doesn’t use drive mnaps, it uses a software running on each client that backs it up over a network. It runs far faster than a “cloud” solution and, more importantly, the data would always be under your control. Good luck when your cloud provider gets hacked and their NSA/FBI/TLA backdoor encryption keys get handed out.
I use several VM machines none of which are connected and the internet is available by attaching my wireless dongle to the USB port of the guest machine.
At no time can the Host machine connect to the internet.
I also have MalWare Bytes on each machine.
Each machine is cloned so I can use them in rotation one day apart, so, hopefully even if one did get infected then everything else is secure.
I have seven machines, each locked in its own safe, and I’ve thrown away the keys.
@d “As most Mac users probably migrated from Windows, EVERYONE should know: Don’t open email, and certainly not attachments sent from unknown senders. That’s just Internet 101!”
That might be Internet 101, but you should probably take Internet 201.
Haven’t you ever gotten email “from” yourself? Or spam links in email “from” someone you know, someone whose Yahoo or AOL account password was compromised and the spammers took over their accounts and sent everyone in their address book these emails?
I’m telling my clients to not open ANY attachment UNLESS THEY WERE EXPECTING IT. And even then, if there’s anything hinky at all, text or call the sender and confirm.
@ tonydi
Internet 301!
Yes, but after the first time (that was a scam employed years ago!), I set up a rule for that. And if it still gets through, I don’t open it! Secondly, if you send one to yourself, it should get to you in seconds, probably before you close the account. Oherwise, you should know it’s not from you. Thirdly, you can set up email to have a certain marker on them so you’ll know it’s from someone trusted.
For safety reasons, I use an Internet account where I have a sh*tload of filters. And I forgo using the common services like yahoo, gmail or hotmail.
Hello, I am Mac user, but I still employ safeguards.
I may be wrong but I assumed webmail accounts such as Gmail are in fact safer than using a local email client.
Webmail hosts are just as vulnerable, since their AV protection is just as behind the curve as everyone else. They may prompt you not to download executables from untrusted/unknown sources, but a user can still go ahead and do it. Its not like modern mail clients made in the past 5 years don’t put up the same roadblocks, that’s why they started putting executables in zip files.
Those complex mechanisms of protection you guys come up with are part of the reason I started building a new solution to this problem.
For enterprises, check out spikes.com for a very compelling prevention mechanism for CryptoLocker which is quite a bit more effective and simple.
We’re building the first purpose-built, enterprise-class, multi-platform air gapped browser, free from malware, and built for privacy.
Its clear from things like this, it’s time we start browsing the web differently.
I can’t say that I find my solution particularly complex, and, since I use VirtualBox from Oracle it is free.
It also has a number of advantages:
1. The host machine has virtually no software on it at all apart from the VitualBox program and a few others.
2. If CryptoLocker did attack a machine then it would (as far as I am aware) be limited to that machine which could be totally erased by a file shredding program.
3. Cloning a machine only takes a few minutes and the cloned machine is identical to the original including all the programs running on it.
4. By using them in rotation if CryptoLocker did attack one then the attack would be limited to only that particular machine and the only files encrypted would be on that machine.
It may seem complex but once set up is absurdly easy to use for almost everything.
In fact I often forget that I’m even using a VM because it looks and behaves exactly like an ordinary PC running, say, Windows XP, or WIN 7, or Linux are whatever I choose.
And at the moment I am on this site within a VM and simply can’t tell the difference.
Its a good solution but won’t work for a lot of users as they have large file stores they don’t want to be cloning. For many it is their home entertainment (mp3, TV series and movies quickly stack up the GBs) that drives them to use NAS. Even if the client is a VM the NAS would be encrypted.
I do a lot of photography so I do make a cold backup of my NAS each month and keep it disconnected in a drawer. Potentially losing a month is alarming though (I know I could do it more regularly but its a trade off).
My cloud store maps in windows explorer so I expect this kind of malware could have that too!
I also have large stores of the same kind of things, DVDs, MP3s, Photos etc (at the moment about 10-12TB of data), but I wasn’t suggesting even attempting to clone them.
The VMs are actually very small and very easy to use but I only use them for surfing, downloading various items, movies etc (legally) and trying out various programs.
They can also be cloned in about 2 mins or so with the clones an exact copy of the original, even down to the programs running on them.
So no more re-installing Windows.
All my data, especially movies and photos are on external HDDs which are never connected to the PC used for surfing, but are on a totally seperate PC which is never connected to the internet at all.
In this way they are air-gapped.
Obviously this would not work in a corporate environment (and was never intended to) but for individuals wishing to protect their data against CryptoLocker it should prove to be fairly effective as long as the right methodology is use.
And, since this particular virus does not seem able to attack shadow files, make sure that System Restore is activated and create a new restore point at least once a week.
An “air gapped browser”? Please elaborate. In my understanding “air gapped” means “not connected to a network.” How would a non-networked browser function?
CryptoPrevent appears to have some similarity to Windows Software Restriction Policy which is built into gpedit.msc and Parental Controls. And, since the tool prevents executables of type exe, com, scr, and pif from running in %appdata%, %localappdata%, %temp% and the Recycle Bin, I suspect that it will protect individual users from additional variants of Windows malware beyond just CryptoLocker. For example, the Zeus trojan (aka ZBot) places its executable in %appdata%:
http://www.symantec.com/security_response/writeup.jsp?docid=2010-011016-3514-99&tabid=2
The tool seems particularly relevant to users of Windows XP Home and Windows XP Media Center Edition which include neither gpedit.msc nor Parental Controls.
P.S. Brian, this tool might be worth adding to your “Tools for a Safer PC” article?
CryptoPrevent is a front end to adding these SRP rules to the registry. It’s a great tool that definitely makes it easier to add these rules rather than to do it manually.
The Zbot infections that are installing CryptoLocker are actually being installed under %AppData%\random\random.exe.
I wonder if the ‘Annual Form – Authorization to Use Privately Owned Vehicle on State Business’ emails are the cause, I’ve been getting these for about a month now. I get Company Business variations too.
I was reading in a few Internet security related emails that the best way to avoid CryptoLocker is to block all ” “.exe, ” “rar , “”.pdf.exe or ” “.zip files being installed in the Windows “/appdata” folder. This would essentially block all program downloads but it appears that you can white list files so that they can be installed normally.
The best way in my opinion to deal with this problem is to do daily full or incremental backup’s your important files to a external hard drive (one that uses a password protect) or a good cloud service, not based in the United States. I am talking about doing a manually setup verses automatic backups which would over write the existing backup files if the Window’s based hard drive became infected with CryptoLocker . For all the readers worried about the N.S.A. , I found Mega free cloud hosted in New Zealand to be a outstanding service which encrypts your files that are being stored on their cloud service.
Unfortunately if you did get infected all this would do is spread the infection to your backup, since by the time CryptoLocker announces its presence it’s usually too late and has already encrypted all the files it can reach.
Not if the back up drive was password protected and or not physically mounted to Windows. I have external password protected U.S.B. hard drive, but I don’t see how the malware could infect the drive without defeating the authentication process.
For example, Aegis encrypted hard drive’s can be connected to a computer psychically but won’t mount until the correct password is entered. CryptoLocker would not be able to access such drives if they where connected via the U.S.B. or Firewire port but the drive was not password authenticated.
In other words encrypt , zip and password protect your important files.
Question to B.K. , has there been evidence to show that CryptoLocker will infect files that are already encrypted, compressed down to a zip file and are password protected already? Or a combination of the above order for that matter?
You just better hope that you don’t authenticate access to the drive while this nasty is in the process of encrypting files ie. before it’s alerted you to it’s presence.
I tried connecting a drive to my computer psychically but all I got was a headache.
I assume it needs local admin rights to be installed and start the encryption process. No?
No, local admin rights aren’t necessary. See this article on CryptoLocker:
http://nakedsecurity.sophos.com/2013/10/12/destructive-malware-cryptolocker-on-the-loose/
“CryptoLocker installs itself into your Documents and Settings folder …”
P.S. local admin rights aren’t necessary for the Zeus banking trojan either.
If drives are already encrypted with Microsoft’s Bitlocker encryption, are you still vulnerable to Cryptolocker? Would installation of Bitlocker be an effective compensating control? If not, why not?
Is Bitlocker primarily protection against physical threats such as theft, but not against threats when the computer is being normally used by the legitimate user?
Since the malware will encrypt any device and directory it can read/write to, and since Bitlocker, once authenticated, mounts as a read/write filesystem, it would be very unlikely to prevent this particular piece of malware, assuming bitlocker devices (or directories) are mounted at startup and left mounted.
the malware (bitlocker) runs with the rights of the user so even if bitlocker is run it will be able to do it’s thing, and yes it hits shared drives very very quickly. IMHO the “I run virtual machines yadda yadda” idea is practically worthless in the corporate environment, one can only do so much, imagine trying to not only deploy but train 300 users to work in a virtualbox environment… teaching some how to find applications without shortcuts on the desktop is enough of a challenge.
Two methods of mitigation in this risk scenario, method one we SHOULD ALL BE DOING and that is having reliable and tested backups and maintaining backups to at least a 30 day retention. This mitigation alone has saved me in more than one scenario whether it’s cryptolocker or a forest fire. Method two is also just as simple, *talk* to your users often, remind them that attachments are bad if not expected, bear in mind that some companies will bring on temp staff here and there for projects or seasonal work, inform them as well. You have to sync your own clock with your customers and make sure you spread your vigilance accordingly.
APT tactics change daily, if not hourly…. it always kills me when I see so called security professionals that are not spreading the word on a consistent and easy to understand manner. Our users do not need to know the mechanism just the mitigation simply put
Great post, Brian !
As soon as I read this I installed CryptoPrevent on my friend’s XP Pro machine. Then I went to install it on my W7 starter edition netbook (used the exe installer in both cases). The install seemed to go fine. However, after I got the request to restart the machine I also got a message saying that the working (i.e. not the installer) exe file was not a valid Win32 file.
Restart seemed to go fine.
CryptoPrevent is now on the Start menu, but does not show up as a running process in Task Manager.
Question to anyone, what do you think ?
CryptoPrevent sets policy regarding what executable types can run and where they can run via Windows registry settings. Thus, there is no running process.
You can test it by downloading a safe executable, actually a utility, from Nirsoft. For example, download CurrPorts fro here:
http://www.nirsoft.net/utils/cports.html
Unzip the archive ‘cports.zip’ in your %appdata% folder (expand Windows explorer to find it), and attempt to run the executable ‘cports.exe’ and see what happens.
P.S. CurrPorts is a great utility to monitor one’s network connections in Windows.
Yes, this is one particularly well-planned out and nasty infection. I understand that the person behind it even fields questions from infected users on how to get him his money/save their files. I’ve (personally) seen it lock a computer with no backup and no recourse, jump network (mapped) drives to encrypt QuickBook and Public folders and a company pay the ransom– 3 hours later, they got their files back. Oh, and the mastermind behind this even offers “support” if you don’t get all your files unencrypted after paying up; he will help you fix or unlock them. Charming.
Brian, thanks for the article and the heads-up on CryptoPrevent; the “blocking all attachments” thing has been annoying our customers and causing us grief.
On my first run in with this infection, the user claimed that the attachment showed up on her desktop and she, confused, clicked on it to see what it was. I blew that off as an excuse, since I had only heard of email attachments as the attack vector. However, I later heard that the CryptoLocker author had partnered with the Zbot guy/folks to push his Ransomware down. Computers that were previously infected and probably laying low could have his junk pushed to desktops. So maybe that user wasn’t lying after all.
I found these instructions on how to set up Local Security Policy and add rules to block Cryptolocker. This looks like a reliable site:
“Cryptolocker: How to avoid getting infected and what to do if you are”
See:
http://www.computerworld.com/s/article/9243537/Cryptolocker_How_to_avoid_getting_infected_and_what_to_do_if_you_are_
In my case, Vista, I would use Programs > Administrative tools > Local Security policy
Under Software restriction policies > Additional Rules (Rt click) > New path rule
And enter the rules provided.
Does anyone see an objection to this approach?
This is the exact same approach that we published in the guide at BleepingComputer and that CryptoPrevent utilizes in the program. CryptoPrevent just makes it much easier to apply the rules, especially to home users.
For administrators the best approach would be to set these up manually via GPO so that it protects all the computers on the domain.
“(and payable only in Bitcoins)”
There is also MoneyPak.
Would it be possible to decrypt the files by moving them to a linux machine and accessing them as root using command line?
My understanding is that trying to access them on a different platform (eg. Linux) will not work, as the files themselves are encrypted
This is not runtime encryption. The files are actually encrypted and remain so regardless of where they are located.
I have 3 thoughts on this:
1. Can the virus be installed only when the user has admin
privileges?
2. Does changeing security permissions in specific folder
properties prevent the virus from encrypting files? (Only
reading, running is permitted. Writing requires the admin
password).
3. Does a proper firewall (e.g. Comodo) prevent the virus
from phoning home and receiving the encrytion key?
Any reaction is highly appreciated!
Trudy
1. The infection is run as the invoker. Therefore it runs under the security credentials of the user who opens the attachment.
2. Yes, if the infected user does not have access to a particular file or folder, then they are unable to be encrypted.
3. Yes, an outbound firewall would block the initial phone home. Hardware or inbound firewalls would not help in any way.
@Trudy — the ransomware installs just fine under a regular user account. As per #2, I believe that’s part of what the different Cryptolocker tools do. #3: It’s unlikely that your firewall is going to prevent your files from being encrypted once you have downloaded and run the stub installer for Cryptolocker.
Thank you very much, Lawrence and Brian, both for your prompt reactions.
In order that I understand how things work:
Concerning the firewall: doesn’t a firewall give a warning, whenever a new program tries to establish an internet connection?
Software can only be installed with admin privileges, am I right?
(Excuse me for my problems with the English language..)
Hi Trudy,
Yes, an outbound firewall should display an alert before the outbound connection is created. Hopefully a user would detect that a randomly named file shouldn’t be doing that and not allow the connection to start.
Executables can run as the user who started it or can ask for elevated privileges to run as Administrator. CryptoLocker is happy to run as a non-admin and will thankfully only be able to encrypt those files that particular user has access to.
If some local files are already encrypted by the user, will CryptoLocker re-encrypt them with its own algorithm or will these files remain unchanged (“thinking” that they have already been encrypted by CryptoLocker)?
Thanks.
CryptoLocker does not analyze the file before it encrypts it. As long as the file matches a particular file extension the infection goes to work on it.
I have read in another website that preventing this disaster is quite easy to do, but many will “consider doing it”. Then when they get whacked, all they can do is throw their arms up in disgust.
As of the last 10 years or so, as technology gets more advanced, as well as the users, they are simply into the, ahhhh whatever…next, next, next mode. Always in a hurry, no time for attention to detail.
The USB style “back up drives” are pretty cheap. Most operating systems support, or have built in backup software. Its not complicated to run. You can set yourself reminders via Outlook, Google or other time management software to plug in your external USB drive and perform a backup as often as needed.
Once the drive is done backing up, simply unplug the power cord. Plug it in only to retrieve a copy of the data you are looking for. When your done, its simply unplugging the drive and it should be safe for quite some time.
People seem more scared to install a hard drive in a computer than they are to deal with paying crooks ransom money. A hard drive would cost about $100.00 or less. If you have the operating system installation disk, you could be back online in a few hours. A new hard drive means a new start, and a pretty good chance at a system that is clean. It takes some time to load everything up and get the system “back to normal”, but its doable. One thing I will recommend if you do build a system, is to make a image of the system after everything is installed. That way, should anything happen, a rebuild is quick and painless.
Hats off to Krebs and the companies for ID’ing the group policy settings (GPO). I would recommend showing the exact name of the registry hack or identifiable name of the settings applied, so people can go to places like Technet and read up alittle more, especially the Corporate and Government workers. Those people are going to have to ask for permission before begging for forgiveness to apply this prevention.
Windows is adptly named, just about anything can get into the building as long as there are Windows.
Excellent post 🙂 I clone my PC’s HDD every 4 weeks in addition to full-disc imaging occasionally with a USB HDD that I disconnect from my PC’s after the image has completed.
Both of my backups HDD’s are disconnected from the PC’s when not backing up and cloning.
Routine cloning has enabled me to recover fast from past intrusions.
Instead of investing in the time in HDD cleanup attempts and $$’s to clean my HDD’s if affected, I remove the affected HDD, install my cloned HDD, and am running as normal fairly fast.
Then I format (and delete the partitions) the affected HDD and re-clone for the next recovery situation.
HDD install/removal can also be made expedient with inexpensive hardware with one’s Desktop PC, with hot-swap HDD racks, or an Enclosure for Laptop PC’s.
Lot of info about Software Restriction Policies can be found here. This is what I referenced to learn about and create the original CryptoLocker rules:
http://support.microsoft.com/kb/310791
http://technet.microsoft.com/en-us/library/cc786941%28v=ws.10%29.aspx
I know it feels easy to blame this on Windows, but it’s important to remember that this infection could be targeted at any OS and have the same results.
The biggest issue here is lack of safe computing practices and weak or non-existant backup strategies.
Just an FYI for those who haven’t seen yet, but it appears the developers have made a change with their business strategies. They now have a dedicated decryption service and are charging 10 Bitcoins (~$2,120) to get your files back.
http://www.bleepingcomputer.com/forums/t/512668/cryptolocker-developers-charge-10-bitcoins-to-use-new-decryption-service/
http://thehackernews.com/2013/11/CryptoLocker-Ransomware-Decryption-service-malware-keys.html
Question:
Pretend for a minute that someone wanted to target a Mac with this attack. Normally, you would be prompted with “do you want to run this software?” the first time any newly downloaded software attempted to execute.
Could malware such as cryptolocker defeat the Mac’s protection scheme (if so, how?) or does this help make the Mac less vulnerable to such attacks?
If a Mac would be hard to infect with malware similar to cryptolocker, then why doesn’t windoze have similar protection?
@Neej, it depends on the webmail account.
Some don’t even encrypt the login. Some encrypt only the login.
For example, verizon webmails only encrypts the log in but not when composing or sending mail. But it will send a popup notifying you of this at least.
AT&T’s version of yahoo on the other hand(since at&t mails is now combined with yahoo), does not even notify nothing is encrypted……although regular vanilla yahoo does encrypt everything. (it also takes much longer to send and receive emails for some mysterious reason then vanilla yahoo does)
Since Microsoft stopped giving outlook with a copy of windows…and replaced it with a free downloadable version called outlook express, its been a huge problem. I don’t recommend it, and only recommend the version of outlook that comes with a paid office suite…. On linux there are plenty of safe mail clients, that can be tweaked even better, and def still recommend that over using webmail.
I found Hitman Pro Alert
http://www.surfright.nl/en/cryptoguard
Would that be a good protection?
I have a client that was encrypted by crypto locker despite using cloud storage.
They have mapped drives into the cloud…. something most businesses do.