Last week, the world got the first glimpses of a man Russian authorities have accused of being “Paunch,” a computer crime kingpin whose “Blackhole” crimeware package has fueled an explosion of cybercrime over the past several years. So far, few details about the 27-year-old defendant have been released, save for some pictures of a portly lad and a list of his alleged transgressions. Today’s post follows a few clues from recent media coverage that all point to one very likely identity for this young man.
The first story in the Western media about Paunch’s arrest came on Oct. 8, 2013 from Reuters, which quoted an anonymous former Russian police detective. But the initial news of Paunch’s arrest appears to have broken on Russian news blogs several days earlier. On Oct. 5, Russian news outlet neslushi.info posted that a hacker by the name of Dmitry Fedotov had been arrested the night before in Togliatti, a city in Samara Oblast, Russia. The story noted that Fedotov was wanted for creating a program that was used by various organized crime groups to siphon roughly 26 billion rubles (USD $866 million) from unnamed banks. Another story from local news site Samara.ru on Oct. 8 references a Dmitry F. from Togliatti.
This is an interesting lead; last week’s story on Paunch cited information released by Russian forensics firm Group-IB, which did not include Paunch’s real name but said that he resided in Togliatti.
Fast-forward to this past week, and we see out of the Russian publication Vedomosti.ru a story stating that Paunch owned his own Web-development company. That story also cited Group-IB saying that Paunch had experience as an advertising manager. This Yandex profile includes a resume for a Dmitry Fedotov from Togliatti who specializes in Web programming and advertising, and lists “hack money” under his “professional goals” section. It also states that Fedotov attended the Volga State University of Service from 2003-2005.
That Yandex profile for Fedotov says his company is a site called “neting.ru,” a Web development firm. The current Web site registration records for that domain do not include an owner’s name, but a historic WHOIS record ordered from domaintools.com shows that neting.ru was originally registered in 2004 by a Dmitry E. Fedotov, using the email addresses box@neting.ru and tolst86@mail.ru.
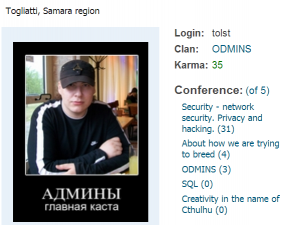
A cached contact page for neting.ru at archive.org shows the same box@neting.ru email address and includes an ICQ instant messenger address, 360022. According to ICQ.com, that address belongs to a user who picked the nickname “tolst,” which roughly translates to “fatty.”

A user who picked the nickname “tolst” or “fatty” posted this image of his new Porsche Cayenne in March 2013
This brings up something I want to address from last week’s story: Some readers said they thought it was insensitive of me to point out that Paunch himself called attention to his most obvious physical trait. But this seems to be a very important detail: Paunch had a habit of picking self-effacing nicknames.
The pictures of Paunch released by Group-IB show a heavyset young man, and Paunch seems to have picked nicknames that called attention to his size. One email address known to have been used by the Blackhole author was “paunchik@googlemail.com” (“paunchik” means “doughnut” in Russian). Blackhole exploit kit users who wished to place their advertisements in the crimeware kit itself so that other customers would see the ads were instructed to pay for the advertisements by sending funds to a Webmoney purse Z356971281174, which is tied to the Webmoney ID 561656619879; that Webmoney ID uses the alias “puzan,” a variant of the Russian word пузо, or “potbelly.”
Turns out, “tolst” was a common nickname picked by Paunch. We can see a user who picked that same “tolst” nickname posting in a Russian car forum in March 2013 about his new ride: a white Porsche Cayenne. According to this photo released by Group-IB, Paunch also owned a white Porsche Cayenne. Tolst posted pictures of the interior of his Porsche here.
Neting.ru’s archived FAQ points to an official payment page at virtual currency Webmoney, which includes the name Dmitry E. Fedotov and the ICQ number 360022. That same Webmoney account shows up on wmid.name, a site that lists account holders who have a reputation for being late with promised payments. The last account on the bottom of that page is an entry that lists the same Webmoney ID, along with Dmitry Evegeny Fedotov‘s date of birth (Nov. 6, 1986), passport number (3606578837), and physical address. It’s not clear when Fedotov was added to this list, but it’s possible he was simply unable to pay for promised transactions due to his early October arrest and detention.
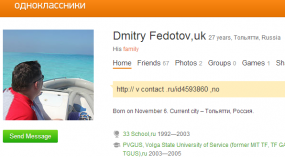 This Odnoklassniki profile for a Dmitry Fedotov from Togliatti also puts his birthday at Nov. 6, and says he attended Volga State University of Service from 2003 to 2005.
This Odnoklassniki profile for a Dmitry Fedotov from Togliatti also puts his birthday at Nov. 6, and says he attended Volga State University of Service from 2003 to 2005.
Early on, Fedotov appears to have made a living by writing and selling Web scripts for various online currency exchange sites. But by 2009, this young man was growing more interested in computer security — specifically Web browser vulnerabilities.
The Web community Fido20.ru includes a member named “tolst” from Togliatti who gives his name as Dmitry Fedotov and was very active in discussions about network security, privacy and hacking. In this post from 2009 titled “Vulnerabilities in browsers and their plugin-ins,” Fedotov can be seen warning users about unspecified new vulnerabilities in Apple’s Quicktime and Microsoft’s DirectX versions 7 through 9.
In another thread, Fedotov encourages the sharing of browser exploits and provides links to several vulnerability archives. He also tells fellow forums members that they are asking to get hacked if they leave various browser plugins activated.
“As I have done before, I am asking all the users as well as IT Security professionals to disable all plug-ins and add-ons in their browsers,” Fedotov warned forum members. “Do not think that if you are not users of Internet money (web money), there is no danger of being infected. In this case, the infected PCs are turned into socks proxies, spam/ddos bots and all the bad activity is done under your name, so that law enforcement can place all the blame on your shoulders. Safe surfing and good luck to you.”




Interesting why you are saying “Togliatti” instead “Tolyatti”?
It’s just an accepted English spelling of the same name.
http://en.wikipedia.org/wiki/Tolyatti
Tolyatti (Russian: Тольятти, IPA: [tɐˈlʲjætʲɪ]), also known in English as Togliatti
Read Wiki carefully… The reason it’s spelled with a “g” is because “in 1964, the city was renamed Tolyatti (after Palmiro Togliatti, the longest-serving secretary of the Italian Communist Party).”
Another great article, lot’s of good information
Since when “paunchik” means “doughnut” in Russian ? If i am correct is spells “ponchik” not “paunchik”.
It hardly matters. It’s a transliterated word, and there are probably 20 ways to write пончик in transliterated Russian.
You right Brian it doesn’t matter at all but still Paunch ( “paunch-ik” )witch means — a large and protruding belly; potbelly. And (- ik ) at the end stands for уменьшительно-ласкательный and it all come to ” little boy with a potbelly” nowhere where near you translation of “doughnut”. But well done for trying anyway .
I wonder if you know the difference between Дорогой and Дорогой ,Стрелки and Стрелки .кружки and кружки ?
Hey, give Brian some credit here… Пончик *does* mean doughnut or donut. I know it without having to consult Google Translate, but if you insist, here’s the link:
http://translate.google.com/#auto/ru/%D0%BF%D0%BE%D0%BD%D1%87%D0%B8%D0%BA
Semantics with words, that’s not with the context of the article is about.
What is up with the bottom right side pop up box alerting me to this article?
Don’t know. Probably because I’m not seeing it since I block browser scripts. You should block browser scripts too, you’re experience may differ but I don’t think I’m missing out on any functionality I need for this site by doing so.
It was a tracking adware cookie that was causing the pop-up box
It wasn’t a tracking anything. It was a slide-in box that directed readers to check out the other story on Paunch.
Good research Brian. I would say any doubts have been cleared. Unfortunately his bust won´t change anything. The next in line are already in his place.
Another fantastic article and reporting! And people complain about the proper translation of russian words. Ugh! Keep up the good work….
The nickname Paunch (Понч) likely comes from “Neznayka Na lune”, a very popular Russian children’s book (http://en.wikipedia.org/wiki/Dunno#Dunno_on_the_Moon
Russian article, which is not linked to the English one: http://ru.wikipedia.org/wiki/%D0%9D%D0%B5%D0%B7%D0%BD%D0%B0%D0%B9%D0%BA%D0%B0_%D0%BD%D0%B0_%D0%9B%D1%83%D0%BD%D0%B5)
One of the main characters is named Ponchik (Пончик) who is also overweight. at some point he strikes it rich and changes his name to Mr. Ponch (Мистер Понч)
I highly recommend the book, not only because it’s a major cultural reference, but also also because it somehow managed to predict the modern Russian capitalist system to a t.
Interesting! I imagine, also – it isn’t common for someone in the US to call someone very familiar “Dear friend”; likewise, depending on the situation and cultural shift, Russian, or any language would have alternate meanings for words of the same spelling.
And we have tons of descriptive garbage that would be almost impossible for someone from even another neighborhood to understand – just local customs.
+1
Look for voksalna to declare that you have written yet another adolescent and/or ad hominem attack on dear Paunchoolichka.
It is not Brian’s fault, but it is strange that an English transliteration of Тольятти is Togliatti when there is clearly no hard ‘g’ letter or sound in the Russian word. It would be understandable if it was similar to сегодня with the ‘g’ sound changed to a different sound.
Probably because Americans have trouble with the palatalization of soft sign, and it turns into a mistaken guttural like the one in Google translate ‘Togliatti’
The town is named after Palmiro Togliatti, an Italian communist. Hence the Italian spelling
If you put Togliatti into Google Translate, select Italian as the language, and then click on the speaker symbol and listen to the way the word is pronounced, it sounds very much like Tolyatti.
Well I’ll be! Good observation Peter B! 🙂
Quit it Francis, you are making an ass of yourself. Hee-haw. 😉
. This man made $866 millions USD according to MVD source ,he was richer then Jay-Z: $475 million or Bono $ 600 million witch is pretty amazing , he earned more then Michael Jackson: $350 million and Mariah Carey $ 500 million both made in the life time .With this sort of money you don`t go to jail at list not in Russia .
That figure refers to the total estimated amount taken by all people using the exploit kit.
Try slowing down your reading you might not invent things in your head when you see figures in a story about a person …
Nice work, Brian! I have to admit I’m impressed with all the searching in obscure places to get info on this guy. I mean, searching in a Russia car forum? Too much like work for me! 🙂
I find it kind of amusing that wmid.name is, after a fashion, doxing criminals who get caught.
In their zeal to punish people who don’t pay their bills, they expose personal details that criminals would rather stay hidden… and just in time for reporters to dig them up for articles about their criminal activities.
Brian,
Did you happen to see this earlier article? April 22, 2013 – “Hacker from Togliatti repented and received a suspended sentence” — http://www.regnum.ru/news/1651368.html — the article says that between August 2011 and February 2012 the unnamed hacker from Togliatti “wrote more than 10 programs, which were intended for embezzlement of funds from customer accounts various major Russian banks. For his program, he received from $ 400 to $ 1,500.” [The prosecutor] “convicted [him] of creating and using computer software, obviously intended for unauthorized destruction, blocking, modifying and copying information. Taking into account the fact that the defendant admitted his guilt and repented and actively cooperated with the investigation, as well as petitions for review of the case in a particular order, the court sentenced him to a six months’ imprisonment.”
Any idea if this is the same guy, or someone else?
Keep up the amazing work!
_-_
gar
Wow, nice find, Gary. I don’t know if it’s connected, but it sure looks like it. More research to do, now, thanks! 🙂
Hmm. Timeline. Let’s see : he leaves Volga State University in 2005, by which time he has already set up his own Web development company. So, he’s smart and ambitious.
Up to 2009 he seems to be on the side of the good guys, warning against browser-based malware exploits. He’s also interested in network security. Perhaps his interest is already veering towards the opportunities offered by exploiting vulnerabilities, but that’s not known for certain.
If the hacker in the regnum.ru news report is indeed Fedotov then some time between 2009 and August 2011 he goes rogue and starts writing malware code. Blackhole first appears in 2010, but would have taken some time to develop; so was 2009 the year Fedotov actively began work on it?
Some time after February 2012 he is arrested, co-operates with the police, goes to trial in April this year. His criminal activities are only noted as being between August 2011 and February 2012, and the charges specifically mention the potential damage to Russian banks from his programs. Still, he receives only a lenient 6-month suspended sentence
But … less than 6 months after his trial Fedotov is arrested (again) on October 4th, and this time the charges are much more serious. What changed in the intervening six months? Was it just the investigation by Group IB that made it impossible for the authorities to ignore his activities?
It is likely that Fedotov was a developer, perhaps the lead developer, of the Blackhole exploit kit. But if all he received during the development phase was a series of small payments, was he working for someone else? Perhaps the mysterious J.P.Morgan, who clearly was still at large and active after Fedotov’s arrest?
Lokks like there is another post about the Blackhole clan. Looks like up to a dozen were taken;
31. December 6, Softpedia – (International) Russian authorities prosecute BlackHole creator and 12 other suspects. Authorities in Russia announced charges against the alleged creator of the BlackHole exploit kit and 12 others for allegedly using BlackHole to distribute banking trojans and cause losses totaling $2.1 million. Source: http://news.softpedia.com/news/Russian-Authorities-Prosecute-BlackHole-Creator-and-12-Other-Suspects-406627.shtml
For the article listed above, there are related articles below it, with some interesting charts and graphs. They are short reads, but maybe the charts can tell more.
Wow,Brian you now accept donations in Bitcoin 🙂
Woha! I’d have to win the lottery to donate just one bitcoin! HA! Sorry Brian! :/
Yes, I added that over the weekend. It defaults to .01 bitcoins, which these days is about $10. People can adjust that up or down however they like.
Kewl! I’ll admit I’m ignorant about Bitcoins, even though try to I read everything I see about them on the news. In fact I swear I heard on CNBC it went public and hit the NASDAQ the other day? :O
http://techcrunch.com/2013/12/11/pubnub-mtgoxs-real-time-price-streaming-partner-now-offers-trading-data-to-other-bitcoin-exchanges/
The short rticle seems a bit misleading, but I had to share. If the card site is going down, what is Brian to do!
December 9, Wired.com – (International) Guilty verdict in first ever cybercrime RICO trial. An Arizona man was found guilty of federal racketeering charges for his participation in an underweb marketplace known as Carder.su that sold stolen payment card information, counterfeiting equipment, and online criminal services. The marketplace created $50.5 million in losses according to a government estimate. Source: http://www.wired.com/threatlevel/2013/12/rico/
carder[dot[su went down quite some time ago. the forum that took on many of its members was carder[dot]pro and more recently cpro[dot]su. Sadly, the latter disappeared a little over a month ago, and it’s not clear what the story is there, but it was widely assumed to have been overrun by feds and researchers, as are many crime forums.
for better or worse, carder[dot]su and their ilk are not unique snowflakes; there are dozens upon dozens of these carding forums. there are so many that I’m still discovering more of them each week. 🙂
Understood. What the article talks about is using that RICO law to “evenly” distribute punishment to all users of the site(s), thus squashing any sort of half-botched sentencing.
The Feds were in carder, selling fake id’s for years, so I am sure they have a laundry list they are cleaning up.
Good job on keeping up, I know it can be a pain in the rump sometimes to get the info you seek, just stay safe out/in there young man.
Brian,
I am curious as to what your personal opinion is on using RICO for these sorts of prosecutions.
Any chance of an article on your opinion on it all — including what you believe it will bode for the future of ‘cybercrime’ and ‘cybercriminals’, as well as forums that specialise in such acts?
Thanks.