In early October, news leaked out of Russia that authorities there had arrested and charged the malware kingpin known as “Paunch,” the alleged creator and distributor of the Blackhole exploit kit. Today, Russian police and computer security experts released additional details about this individual, revealing a much more vivid picture of the cybercrime underworld today.
A statement released by the Russian Interior Ministry (MVD) — the entity which runs the police departments in each Russian city — doesn’t include Paunch’s real name, but it says the Blackhole exploit kit creator was arrested in October along with a dozen other individuals who allegedly worked to sell, develop and profit from the crimeware package.
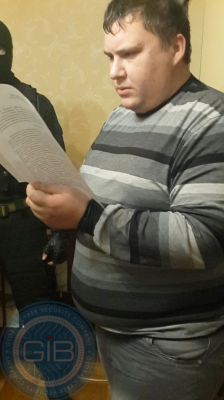
Russian security and forensics firm Group-IB, which assisted in the investigation, released additional details, including several pictures of the 27-year-old accused malware author. According to Group-IB, Paunch had more than 1,000 customers and was earning $50,000 per month from his illegal activity. The image at right shows Paunch standing in front of his personal car, a Porsche Cayenne.
First spotted in 2010, BlackHole is commercial crimeware designed to be stitched into hacked or malicious sites and exploit a variety of Web-browser vulnerabilities for the purposes of installing malware of the customer’s choosing. The price of renting the kit ran from $500 to $700 each month. For an extra $50 a month, Paunch also rented customers “crypting” services; cryptors are designed to obfuscate malicious software so that it remains undetectable by antivirus software.
Paunch worked with several other cybercriminals to purchase new exploits and security vulnerabilities that could be rolled into Blackhole and help increase the success of the software. Paunch bought the exploits to fund a pricier ($10,000/month) and more exclusive exploit pack called “Cool Exploit Kit.”
As documented on this blog in January 2013 (see Crimeware Author Funds Exploit Buying Spree), Paunch contracted with a third-party exploit broker who announced that he had a $100,000 budget for buying new, previously undocumented “zero-day” vulnerabilities.
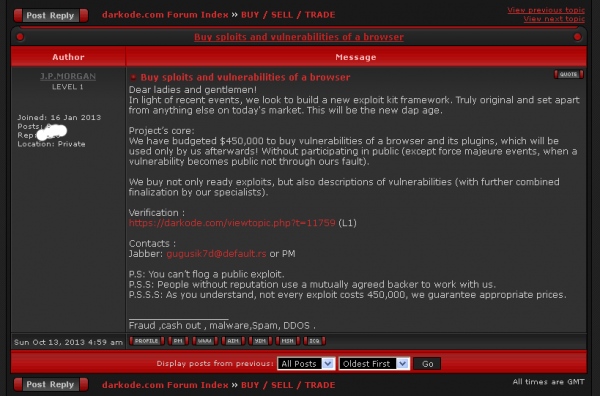
Not long after that story, the individual with whom Paunch worked to purchase those exclusive exploits — a miscreant who uses the nickname “J.P. Morgan” — posted a message to the Darkode[dot]com crime forum, stating that he was doubling his exploit-buying budget to $200,000.
In October, shortly after news of Paunch’s arrest leaked to the media, J.P. Morgan posted to Darkode again, this time more than doubling his previous budget — to $450,000.
“Dear ladies and gentlemen! In light of recent events, we look to build a new exploit kit framework. We have budgeted $450,000 to buy vulnerabilities of a browser and its plugins, which will be used only by us afterwards! ”
The MVD estimates that Paunch and his gang earned more than 70 million rubles, or roughly USD $2.3 million. But this estimate is misleading because Blackhole was used as a means to perpetrate a vast array of cybercrimes. I would argue that Blackhole was perhaps the most important driving force behind an explosion of cyber fraud over the past three years. A majority of Paunch’s customers were using the kit to grow botnets powered by Zeus and Citadel, banking Trojans that are typically used in cyberheists targeting consumers and small businesses.
In its statement, the MVD said Paunch was being prosecuted, but it did not say how he has pleaded to the charges against him, which include the creation of malware and the participation in a criminal organization to jointly commit one or more serious crimes.
Update, Dec. 9, 3:06 p.m. ET: Just published another story on Paunch that traces a trail of clues from local news reports about his arrest to a very likely real-life identity. See: Who Is Paunch?
[EPSB]
Have you seen:
Who is Paunch?…So far, few details about the 27-year-old defendant have been released, save for some pictures of a portly lad and a list of his alleged transgressions. Today’s post follows a few clues from recent media coverage that all point to one very likely identity for this young man.
[/EPSB]





Here it is:
http://www.group-ib.ru/index.php/7-novosti/1362-group-ib-pomogla-presech-deyatelnost-izvestnogo-khakera-s-psevdonimom-paunch%22
Thanks to @GroupIB
Well he wasn’t going hungry was he?!
“cryptors are designed to obfuscate malicious software so that it remains undetectable by antivirus software”
The subject of cryptors is one on which anti-virus companies need to make a decision. A cryptor is a fancy name for a stub of code which includes encrypted malware. Normally anti-virus software cannot detect the usual signature because it is encrypted. The stub is innocuous, possibly even containing nonsense code. Once inside, it unencrypts the malware and attacks.
But any encrypted code in an application should be a red flag in itself. If I were running an anti-virus vendor, I would block any application containing encrypted contents. If a user wanted to allow it, it would have to be included in the exclusions — an explicit opt-out situation.
That could go for obfuscation techniques too. Like Snort/Suricata rules can be written for obfuscated JS, at least obfuscated JS is a possibly legit attempt to protect code (another discussion entirely). But obfuscated crazy jump tables and string garbling in an executable? Seems like an obvious red flag.
> If I were running an anti-virus vendor, I would block any application containing encrypted contents.
Oh the fail.
Encrypted data doesn’t look any different from data your app doesn’t understand.
How are you going to tell the difference between encrypted code and the latest Brittney Spears track (encoded using some audio codec you hadn’t heard of)?
+1.
Not to mention many of the software protection mechanisms use many of the same techniques.
Oh, the horror; the horror!
You assume that things must continue as they are today. I do not.
I could imagine an anti-virus product requiring an app to self-identify its data type(s). If the data is that of someone who cannot sing without the aid of electronic manipulation, then the anti-virus product could test the data, i.e. play it through an algorithm for validity. If the app is deceitful, i.e. the data is something other than what was advertised, the anti-virus product would prevent the app from running. This would be selectable in the options, with people like you allowing the current state of affairs to continue.
Would this prevent many current apps from running? Almost certainly. Would this be trivial? I doubt it. Is this the final answer? Probably not, but your view is not the only view.
While by no means perfect, there are already plenty of ways to get around this — for instance heuristics. What you fail to grasp I think is that most people do not and would not tolerate losing so much of their system’s resources to anything that does not include watching a BluRay in brilliant colour while having 300 tabs of IE/Firefox/etc open. There’s also the fact that encryption isn’t going anywhere but up. You’re assuming things will stay the way they are in many ways and do not even realise you’re doing so. More likely the way forward involves abandoning any MS-based (or hopefully any Google-based, but I doubt that will be any time soon either) operating system and moving everything into their own virtual sandboxes — sort of similar to what the Qubes project is doing albeit far more user-friendly.
“What you fail to grasp I think is that most people do not and would not tolerate losing so much of their system’s resources”
What part of “selectable in the options” didn’t you understand? I realize that most people use their computers solely to watch movies, steal songs, trade child porn, send inane emails, and commit online financial robberies, so they would not select the option I mentioned.
“You’re assuming things will stay the way they are in many ways”
I am doing nothing of the kind; I am simply trying to solve a problem. Some people claim that whitelisting will solve these problems, yet what happens when someone hacks your trusted source, as the U.S. government has done a few times?
“moving everything into their own virtual sandboxes”
I do find it amusing that you claim that I am “assuming things will stay the way they are in many ways,” yet you push sandboxing which has already been beaten because malcontents write their code to listen for the normal activity of an OS and play possum if none is detected, frustrating AV researchers (I cannot remember which AV vendor said that). Admittedly this is only a research issue.
I agree that sandboxing appears to be a great solution to many security problems, but pray tell, why hasn’t it become more ubiquitous in the Windows world? Adobe includes it in its Reader, but that isn’t an OS. Why didn’t Microsoft include it in Windows 8, other than the fact that Gates and Ballmer are not the gods the industry makes them out to be?
P.S. SELinux came from the NSA which you and others here rail against.
Read my other comment to this same comment… Also I’m not sure you’re understanding my suggestion of sandboxing — I’m not talking about merely what something like Acrobat does. I’m talking about something implemented at the operating system level which completely cuts every app off independently, regardless of what is built into the app.
No matter WHAT anybody tries to do on TOP of an operating system there will *always* be ways around it. Always. And it’s not profitable to fix things at the operating system level. An entire ecosystem relies on this business model, and it has since the 1980s/early 1990s.
The only way to vastly decrease this sort of thing is to drop the idea of ‘antiviruses’ altogether and build something from the ground-up which prevents such things from being possible in the first place. There will perhaps be a breakout every year or so but nothing compared to the constant onslaught that we have now, and once that is patched and the operating system itself made more hardy, then (with any luck) that entire string of possibilities gets cut off (until the next one comes along — also this sort of attack tends to require far more skill and time — more corporate or government levels — nowadays).
“I’m not sure you’re understanding my suggestion of sandboxing … I’m talking about something implemented at the operating system level which completely cuts every app off independently, regardless of what is built into the app”
Actually I did understand it. What you are talking about is a brand new OS built especially for sandboxing or maybe a new Linux version incorporating it.
I am not convinced this concept could be applied to Windows mainly because of the legacy aspect. I’ll bet you have not worked in the software business too long so you have not experienced the joys of working with large legacy systems. I have. It is almost impossible to drastically change something as large and complex as Windows, so you would need to rewrite large parts of it. However, the cost would be prohibitive. And Microsoft would never accept it, in my opinion.
One big problem is market share. Linux has less than 2%, around half that of Vista. And why is that? Business applications. No, I am not talking about the app which tells you if you are about to sleep with a first cousin (Iceland has such an app). I’m talking about products which enable businesses to perform work, for example, Office, Quickbooks, and LexisNexis (the legal research product); Turbotax and the like would also be necessary for consumers. They would all have to be ported to your new OS. Given that these companies have not ported to Linux, they probably would not be receptive to a port to a new OS without a really good business case.
In other words, I am not arguing with the technical merits of your idea, just the business merits.
That said, I wish I knew someone like Warren Buffet to provide venture capital. Create a new Linux with sandboxing, convince the major business application companies to port to it, give it a GUI which vaguely resembles Windows 7 to attract the people (like me) who believe that Windows 8 is a disaster, add LibreOffice, and voila, an OS for the masses.
Any venture capitalists reading this, feel free to contact me.
“Linux has less than 2%, around half that of Vista.”
Oops, that is for desktops. App-based smartphones are another market entirely.
Point being… if you’re still trying to solve the problem outside of the operating system, you will always lose — every time. This sort of thing needs to be built into the operating system, not on top of it. At best you just buy yourself a tiny frame of time — and a large profit. Which is what AV vendors are really most likely to care about whether you realise it or not. Just like many health problems, curing the problem does not create a profit.
Its going to be interesting to find out which dark room secrets the combo of McAfee and Intel have been researching. I am sure there is a futuristic chip coming out that doesn’t use signatures, but some other more accurate means. In due time I am sure we will see.
Its all about ease of use and lack of security. People can boot a DVDROM each day and have a fresh load, but they don’t want the complexity or issues with that. So, crooks will win in the end, unless the weakest link becomes stronger.
AdamM- it’s called entropy.
Instead of wasting time/money prosecuting and incarcerating these low-life bottom feeders, perhaps it would be more appropriate for them to run a gauntlet consisting of all the innocent people they have bilked. Arm the folks with canes, sticks, clubs, pillow cases filled with bars of soap, etc and let them have it. A bit draconian, but probably very effective. Why should these criminal animals be treated like humans?
You are setting your sights too low. Clearly they should have never stopped burning witches at stakes or lynching negroes for having sex with the white women. Countries that slice off hands, too, for stealing a loaf of bed should obviously be commended on their fine attention to poetic justice.
Vigilante ‘justice’ is not the answer, troll or not. The situation is far more complicated and complex, and the truth is that most ‘cybercriminals’ are quite capable of ‘rehabilitation’, in large part due to the virtual nature of the crime. It’s possible that reoffense after a reasonably smallish sentence, in fact, may have one of the lowest recidivism rates in most countries, depending on the culture of the country. Most likely definitely in yours. Perhaps not so mine. But a lot of this has to do with economics, not character.
As a case in point I would mention Max Vision/Max Butler who went to prison, got out, tried hard to get work and ultimately ‘had’ to return to crime because nobody would give him a job or a chance. THIS is usually why people in your ‘first world countries’ reoffend.
Sure, you may ask, why trust these people? And the answer is because if you do not figure out a way to do so then they WILL almost certainly reoffend in some way. The problem with most justice systems is that that people do not finish ‘paying’ for a crime after they have ‘done time’. There is penalisation and demand for rehabilitation but when the rehabilitation ‘takes’ then nobody is willing to give the rehabilitated a chance. Which leads to bigger crimes because hope of anything better becomes lost.
Of course there are cases to the contrary as well, but ‘justice’ as a concept should be on a case by case basis, and this is why your post bothered me so much.
But if it is personally satisfying to torture the accused, then who am I to judge?
Their is some truth in what you write. Because of lack of computer programming jobs in many countries , many people fall back to the thing they know best and that is criminal activity. Because of a past criminal record, many companies won’t hire these types of people for fear of unknown consequences.
You mentioned Max Butler, when he gets out of federal prison, what company is going to hire him with his record? If society doesn’t give people second chances then of course they will resort back to criminal activity
As strange as this may sound, I would also partially blame outsourcing and the removal of physical labour and factory jobs from first world to second and third world countries — historically a person could make a reasonable wage if they could get hired with a criminal history in, for instance, the United States, and not need to go anywhere near a cash register or forms of payment. Now it is probably difficult to even get a job in your fast food restaurants (not that a person could live on this — even noncriminals cannot with no money owed) due to access to money. And no office establishments due to proximity to technology. The computer limitations and monitoring also make it difficult if not impossible to use skills even if you could get a job with a criminal history.
Prison for hackers — and for most criminals these days — is not the time in prison, it is what happens when they are released from prison; prison becomes their lives.
I meant to add, ironically this is less true outside of North America/most English-speaking countries as well as Western Europe. The problem making money outside of those places is largely the always problem with making money — but at least then the society is more accomodating to things like poverty, there is stronger family ties, and in many places there is a bit less judgment (even the places where crime is not hailed, which for some reason people from first world countries seem to think applies to anywhere that is not both wealthy and starving their workers). I live in a place where I can get a kilogram of fruit for under a US dollar. In the US, sometimes one would be lucky to be able to buy a single apple for this. Crime may be *more* acceptable there than you may think given the option of starvation.
Paunch’s arrest is encouraging and a message to others they are not out of reach by the long arm of the law enforcement; these investigations require a lot of resources, cooperation and perseverance. Kudos to all involved!
The guy looks like he needs to lay off the McDonald’s and cheap Vodka. Maybe Krebs can take up a collection from everyone here so we all can send Paunch a couple bottles of Smirnoff Vodka while he enjoys his jail cell.
He looks like one of those real creepy kind of guys that you will find on any sex offender database.
It’s not important how this guy looks like, there are many pretty guys/girls which profit from their look. Under some conditions we all can be something opposite we are now. You can’t reject this fact. Env affects you and you affect the env.
Hope paunch will have enough time to reconsider his path.
Dear friend, I can give you a couple of hundreds dollars to buy Smirnoff Vodka. It’s not so expensive as you think. Will you be able to send it to Punch? I’m sure you’ll not because Punch is in Russian pre-trial detention center where nobody drinks vodka.
Ah Igor, at least there are still cigarettes. Hehe.
A few years at hard labor in some remote prison gulag will slim him down and remove that paunch….
It’s interesting to try to decode the relationship of Russia and its governmental organs, police and otherwise, to their malware industry.
It’s accepted wisdom that a great deal of the world’s malware is written and administered in Russia. This implies that government has at least a tolerant attitude towards the ‘industry,’ and that bribery of officials keeps the enterprise in business.
In the case of Vrublevsky et al, it’s a safe bet that their downfall was a result of high-profile feuding and misbehavior, instead of maintaining a low profile–which any intelligent criminal does. The government couldn’t afford to let them attract that kind of publicity, no matter how rich the bribes were.
“Paunch” didn’t draw unwarranted attention to himself. But he’s still in trouble. Is it a show trial? Did he offend someone? Did he try to renege on some financial arrangement? Do the authorities use malware kindpins to squeeze bribes out of them until they become too embarrassing? Do the malware kingpins accept this sort of prosecution as a cost of doing business?
The arrest of Paunch is indeed an unusual event for a number of reasons. I think we can all thank Group IB for this accomplishment, I’m sure all the investigative and tech work was done by them.
Arguably it could be because many of the people using Blackhole were targeting Russian banks. I’ve gotten the impression over the years that his employees were not cautious enough about how they were selling these packs and who they were selling them to, and I assume on his rented servers he was not blocking any IP ranges (just a guess).
Not only the hosted servers of Paunch but also some of the bulletproof servers hosting independently paid for Cool and Blackhole kits were based in CIS and targeting CIS. CIS tends to care when it affects CIS, and Russia does not like to be made a fool of.
It probably does not have much to do with drama or payments and probably does have a lot to do with pride and shame.
“Arguably it could be because many of the people using Blackhole were targeting Russian banks.”
There’s no “arguably” about it. Russia only cracks down on cyber-theft when it affects Mother Russia. That’s why Russia is the home of most cyber-crime. And China is the home of most industrial theft.
The statement released by the MVD alleges that Paunch and other alleged co-conspirators did in fact target banks in Russia.
“activities of a criminal community members affected customers of Russian banks located throughout Moscow, Tyumen, Ulyanovsk, Krasnodar, Petrozavodsk and Kursk region.”
These criminals must not be good communists because Ulyanovsk is the birthplace of Lenin.
I must admit I am shocked that any Russian cyber-thief would attempt to steal from a Russian bank. There are so many banks and companies in the USA which have neglected their computer security, so why steal from a local bank? Maybe because he created the BlackHole exploit kit, he thinks he’s some kind of cyber-stud, invulnerable to everything.
Oops, I forgot to say that I realize he may not have been the one doing the actual stealing, but he had to know that some of his customers might not discriminate.
Yes you are 100 % right on this .He was arrested only and i repeat , ONLY cos he was robbing some Russian banks its a BIG No , No ( it is strictly forbidden to commit any types of e-fraud against Russian companies ) if you are Russian national or any other old USSR national ,ofcos you can try but you wont last for long .
P.s Try to hack White House from US soil and you will see how long will it take before your door will come of its hinges ( usually around 5-6 o’clock in the morning . )
Likely he will now just work for the Russian Government. They may say they will send him to jail, but it will be a very plush ‘Jail.’
Ah come on Krebs, you are above remarks such as those found in the 2nd picture caption.
Sometimes I’m reminded he spends his days on what I’m sure are some pretty juvenile criminal forums, where he can’t afford to break cover. He’s gone Brasco.
I’ve often been curious as to if this is the case or if he is deliberately just going for a shaming approach (while making himself sound more adolescent in the process). It’s also possible that it’s become a severe form of over-correction. I think this sort of behaviour is a mistake in either case, as it tends to spur the vicious circle ever further on. At least one side in ‘the fight’ should be mature, or else what is there left to respect?
Anyone with a large gut who goes by the nickname of Paunch is just asking for derision. If he wants respect he should use a nickname like mastermind or virtuoso. And Brian’s writing that he “certainly lived up to his nickname” is hardly adolescent.
Oh? I’m not sure what commenting on anybody’s looks in a negative way achieves in the midst of a story about the arrest/charging of anybody — it is an adolescent form of ad hominem that is completely off-topic and exists only to be clever. But feel free to enlighten me.
This Paunch charter sounds like a person who is very narcissistic,and lacks any type of moral value or conscience. Basically a lifetime criminal
It’s hardly ad hominem. The guy picked his own nickname; it wasn’t picked for him. I wouldn’t have even mentioned it otherwise.
Vokslana, you seem to find ad hominem attacks in any story on this blog involving accused Russian hackers.
It still looks juvenile.
I see. Well, take a look at today’s follow-up post on Paunch, and let me know if you still feel the same way.
http://krebsonsecurity.com/2013/12/who-is-paunch/
The detail is important because, as I show in this follow-up story, Paunch had a habit of picking nicknames that made fun of his own appearance. In addition to “Paunch,” he also used the nicknames “tolst” or “fatty”; “paunchik” or “doughnut”; and puzan, “potbelly.”
Your mom looks juvenile.
Hard to break character? Possibly.
Lol.
It’s weird thinking about a $450.000 budget from the user J.P.Morgan, while the Bank JPMorgan Chase was hacked in July and about 465.000 records stolen. They said no money was stolen, but still? Coincident?
I’m pretty sure it’s unrelated.
Esteemed software vendors have differing opinions of darkcode.com.
McAfee
http://www.siteadvisor.com/sites/darkode.com
darkode.com
This link might be dangerous. We tested it and found security risks. Beware.
Website Category:
Malicious Sites
Norton
https://safeweb.norton.com/report/show?url=darkode.com
Safe Web Report for:
darkode.com
Web Site Location Bosnia And Herzegovina
Summary
Norton Safe Web found no issues with this site.
Computer Threats: 0
Identity Threats: 0
Annoyance factors: 0
Total threats on this site: 0
Off Topic.
Brian:
I am using the new security tool put out by
https://calomel.org/firefox_ssl_validation.html
It reports the SSL implementation on your site as “BROKEN or UNTRUSTED.”
You might want to look into this. It could be a bug in the FF add-on but maybe not.
https://www.ssllabs.com/ssltest/analyze.html?d=krebsonsecurity.com
Agrees that the server’s configuration isn’t ideal.
Sigh. I think I’ve explained this a number of times already. It’s because there are some images on this site that are not served via https. That is all. If you don’t like seeing that message, why not just load the non https version of this site?
As weird as it may seem after the infamy paunch has gained. He is still small fish. I am more interested in finding out who is behind J.P. Morgan. As mentioned by Brian, The budget was doubled again and more which leads me to believe Paunch was just a worker not so much a “kingpin” as it has become clear that Paunch was not funding him but he was funding Paunch. I wonder what the new pack will be and who will become the next “Paunch”. The Cycle Continues.
Certainly JPMorgan is a person of interest now. If he has a funding that is double of what Paunch was offering, then he might even become a bigger image than Paunch.
He could also be an exploit broker for any number of shady companies that sell to the military complexes of various governments — to them 750k US is a drop in a bucket. I am curious if there is any proven connection between exploits he may have bought and exploits that may show up in an exploit pack. Generally these bugs are not “0-day” but tend towards “1-day” or so — or they would become so very fast.
I have not typed this number in correctly. I meant 450K.
Brian, from your side it’s very unprofessionally to write about a man and even not to publish scan copy of his passport attested by investigators from MVD like in your article about me http://krebsonsecurity.com/2012/06/who-is-the-festi-botmaster/
You are loosing your skills, Brian.
Yes, I loose them more and more each day, Igor.
Nice to see you again. I thought perhaps since I hadn’t heard from you in a while that you had finally begun your prison sentence. But perhaps that is not the case? Have you been given time off for good behavior, or cut a deal perhaps? Or maybe an appeal has delayed things? I am quite curious.
I’m glad to read you again, dear Brian. I cannot answer your questions because it’s not public information but thanks to our old friendship you can learn the details if you write me in Skype.
Igor Im sure you can fill a lawsuit against Brian Krebs based on false accusations .The law protects those who have been wrongly accused of crimes when those accusations are untrue and have caused damage to the person’s reputation. The law allows those falsely accused of a crime to pursue a cause of action in court, generally based on defamation of character, which requires the accused to prove that a false statement was made, the statement was conveyed to a third party and that statement caused harm.
False accusation laws protect victims of libel and slander. Libel is a type of defamation that is made in writing, for example, through mediums such as newspapers or magazines. Slander is the spoken form of defamation.
If you need any help please do let me know im more then happy to help .
Thanks for your offer to help. Please find me at Facebook and add me to your contacts. But just now I’m extremely bothered of judicial proceedings in Russia which are fortunately came to an end to be engaged in such business in the USA. It’s all the same that Mr Krebs writes about me, it’s his personal fabrications, which can seriously disperse from reality. I don’t know how in the USA, but in Russia there is a law on protection of personal information, for illegal distribution of which it is supposed criminal liability. Therefore I would be quite satisfied if my dear friend Brian cleaned the screenshot of the copy of my passport from his blog.
My story about Mr. Artimovich was about evidence Russian investigators had gathered at the time. Mr. Artimovich maintains he didn’t build a botnet and use it to spam and attack others online. The Russian courts (flawed as they may be) decided otherwise.
http://www.nytimes.com/2013/09/03/business/global/online-attack-leads-to-peek-into-spam-den.html
I don’t speak about the essence. I say that to spread personal information – extremely unprofessionally. As for the Russian courts, they in any way couldn’t consider any questions of spam as the Russian Criminal Code doesn’t assume any responsibility for spam distribution.
As I know from the primary source, namely from materials of the criminal case, investigators didn’t talk about spam, about ddos, perhaps.
You give the reference to the article in The New York Times newspaper in which there are a lot of biased facts, in particular, about imprisonment. What a pity that even The New York Times writes nonsense, so do you.
Brian,
I still do not understand why you have not redacted unncessary PII from these sorts of articles (for example Igor’s passport photo). Even in the US court systems, PII must be redacted on all documents — and you are among many who shame people for posting PII themselves (like tweeting credit cards or passport photos). Are you suggesting that because somebody is allegedly (allegedly!) criminal, they should be the victims of crime and have all of their privacy violated? While I understand you wish to attempt to ‘prove’ that somebody is somebody online, Igor had a point then and he has a point now. I am not an apologist, but I do seek to point out the lack of parity, here. In many places, doing this sort of thing is, itself, illegal.
The reason I went to the trouble of reading this article, was to learn how paunch (‘if that -is- his real name’) was tracked. But nothing. A waste of time.
And yes, an ad hominum was disappointing. I’m not fat either, but it’s beneath you.
I’m sorry you didn’t get the whole story you were seeking, Bill. Maybe my next story on this guy will have what you’re after. I doubt you will find it anywhere else.
Don’t mind Bill, your work is much appreciated.
An ironic remark about his nickname, big deal… Nothing compared to sadists, like JimV and Zelco Munye, big supporters of the barbaric Russian penal system. Zelco goes even further, why not rally a lynch mob? Why not treat criminals like animals, especially when they look like child molesters?
Civilization perhaps…
‘Paunch’ is clearly both the miscreant in this case and a Russian national doing his business from within that political sphere which is mostly directed toward people and places outside said sphere — rather than reward his bad behavior by being brought inside the system to ply his trade on behalf of a still-corrupt government, I merely point out the traditional or legacy punishment for criminals and those who fall out of political favor might not be so inappropriate, despite its rather inhumane character.
All please welcome our new-hire, Paunch. Of course we’ll have to extradite him first to the US to “face charges” but after a bit of pressure on Congress we’ll have him hacking for “the good guys” and spying on y’all in no time.
LOL. Maybe, you never know.
It’s all been interesting reading so far – I’m just a research surfer on Mac –
Which happened quite suddenly one day using PC 7-8 years ago.
All I was trying to do is have a worth while chat session with my Son on a Nato base in Germany.
Every 9 seconds – Norton would kill the chat – then deal with their BS – then get back to chat. About 15 minutes of that – the PC ended life a bit abruptly.
In an hour – A new Mac Laptop was online in early 05.
So far so good actually – that laptop still works – but he’s tired – like me.
My main bitch was email with at Yahoo 10 -15 years ago – I wrote them a lot.
With all the Nigerian BS that sucked in many.
1. Why the hell can’t servers be the stop gap for all Viruses / Bots / Trojans – etc – before sending it off to 50m computers.
We shouldn’t be dealing with it – or fixing it.
So what if the data comes in a tad slower scrubbing it.
The only logical way to kill a disease – Right at the source – or at least a damaging kick to the groin. At 60 – angry is default mode on stupid s*it.
Walter the Angry Walmart Greeter – You know damn well he’d have his say.
Hope the talent in this group has a cure in the end – or the future.
As someone mentioned earlier on cell phones –
Droid – and others – I don’t trust it as far as slinging Cool Hwhip.
Seeing what apps have in the background that people agree to –
allowing it to scan all data & images at will – are people really that stupid?
Thanks for the rant off..
While this is an example of the advancement in cyber technology used in cyber attacks on economic markets it is only one part of future cybersecurity intrusions and attacks. There is a greater risk that effects the national security of the United States. That threat is the potential compromise of our national infrastructure of the power grid.
Cyber security test beds are being developed in utilities to determine the threat in real time system operations to ascertain threats to the power grid and their effects.
I have worked for 20 years in engineering power systems and I have authored an article in the September 2013 edition Transmission and Distribution World on cyber security of the power grid title “At the Cyber Crossroads”. In addition I presented and published an IEEE paper titled “Real Time Evaluation and Operation of the Smart Grid Using Game Theory” which describes using Game Theory principles such as decision trees, the Prisoners Dilemma and Ant Colony Optimization to reduce uncertainty in the power grid and improve reliability. I have also authored a paper to NIST on “Situational Awareness in Power Systems”.
Cyber Security and the Smart Grid are a focus and passion I have in my research for solutions to strengthen our nations power grid.
This example and others that have occurred throughout the IT world, economy and national infrastructure are only previews of the future. Cyber technology is evolving at a rate similar to that as defined by Moore’s Law and the industry must make a greater effort to stay ahead of potential cyber attackers by constantly striving to be at the cutting edge of technology and strategy to protect our nations infrastructure. We must remember we cannot operate 21st century technology with a 20th century mentality.