Europol, Microsoft Kneecap Click-Fraud Botnet
Authorities in Europe joined Microsoft Corp. this week in disrupting “ZeroAccess,” a vast botnet that has enslaved more than two million PCs with malicious software in an elaborate and lucrative scheme to defraud online advertisers.
The action comes partly from Europol’s European Cybercrime Center (EC3), as well as law enforcement cybercrime units from Germany, Latvia, Switzerland and the Netherlands, countries that hosted many of the Internet servers used to control the ZeroAccess botnet.
In tandem with the law enforcement moves in Europe, Microsoft filed a civil lawsuit to unmask eight separate cybercriminals thought to be operating the giant botnet, and to block incoming and outgoing communications between infected PCs in the United States and those 18 control servers, according to a statement released by EC3.
The malware the powers the botnet, also known as “ZAccess” and “Sirefef,” is a complex threat that has evolved significantly since its inception in 2009. It began as a malware delivery platform that was used to spread other threats, such as fake antivirus software (a.k.a. “scareware”).
In recent years, however, the miscreants behind ZeroAccess rearchitected the botnet so that infected systems were forced to perpetrate a moneymaking scheme known as “click fraud” — the practice of fraudulently generating clicks on ads without any intention of fruitfully interacting with the advertiser’s site.
It remains unclear how much this coordinated action will impact the operations of ZeroAccess over the long term. Early versions of ZeroAccess relied on a series of control servers to receive updates, but recent versions of the botnet malware were designed to make the network as a whole more resilient and resistant to targeted takedowns such as the one executed this week.
Specifically, ZeroAccess employs a peer-to-peer (P2P) architecture in which new instructions and payloads are distributed from one infected host to another. P2P-based botnets are designed to eliminate a single point of failure, so that if one node used to control the botnet is knocked offline, the remainder of the botnet can still function.
The actions this week appear to have targeted the servers that deliver a specific component of ZeroAccess that gives infected systems new instructions on how to defraud various online advertisers — including Microsoft. While this effort will not disable the ZeroAccess botnet (the infected systems will likely remain infected), it should allow Microsoft to determine which online affiliates and publishers are associated with the miscreants behind ZeroAccess, since those publishers will have stopped sending traffic directly after the takedown occurred.
For now, at least, the actual ZeroAccess P2P botnet appears to be otherwise operating normally. said Brett Stone-Gross, a security researcher with Dell SecureWorks who has studied ZeroAccess activity at length (PDF).
“The problem is that the botnet operators can still easily push a new plugin through the P2P network to restart their click fraud and search engine hijacking activities,” said Stone-Gross.
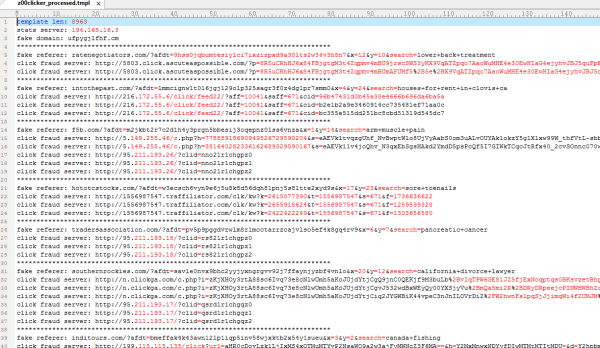
Below is a screen shot of a recent template uploaded to the machines infected with ZeroAccess; it includes information that compromised systems will need in order to carry out future click-fraud schemes.
This is the latest in a string of legal maneuvers that Microsoft attorneys have used to dismantle or disrupt botnets that target Microsoft Windows users. As with a 2011 action targeting the “Rustock” spam botnet, Microsoft in this case invoked The Lanham Act, federal statutes that prohibits trademark infringement, trademark dilution and false advertising.

An analysis of the estimated size of ZeroAccess (ZA) and other P2P botnets. Source: P2PWNED — Modeling and Evaluating the Resilience of Peer-to-Peer Botnets at IEEE Symposium on Security & Privacy, May 2013
Microsoft has posted an enormous amount of information about this botnet and its civil law enforcement strategy at this Web site. Stay tuned for further updates on this story.
Update, Dec. 6, 1:36 p.m. ET: According to Stone-Gross, the operators of ZeroAccess botnet last night pushed out a configuration file for distribution to the 2 million systems still infected with the bot malware. The new “z00clicker” template uploaded by the badguys temporarily brought the click fraud network back online, Stone-Gross said, but by this morning the servers were down again. “The ZeroAccess guys then pushed new configuration files/plugins with the message ‘WHITE FLAG’,” perhaps signalling that for now they do not plan to try to resuscitate the click fraud network.
Separately, Lance James, head of intelligence at Deloitte, confirmed that the new Z00clicker modules were uploaded shortly after Microsoft and Europol announced their action.





ZeroAccess reported to a few ‘domains’. Actually IPs as the HTTP Host header was faked.
I wrote about this when I bought two of these domains. Now I am ‘John Doe 4’
http://dnsamplificationattacks.blogspot.com/p/blog-page.html
From ZD Net article about Patch Tuesday next week. It states “There are currently two public zero-day vulnerabilities in Windows being exploited in the wild: A bug in TIFF parsing in some, generally older, versions of Windows and Office; and a local privilege escalation vulnerability in Windows XP and Server 2003. Wolfgang Kandek, CTO of Qualys, thinks it likely that the TIFF vulnerability will be patched, but not the local privilege escalation bug. The latter is probably too recent to have made it through the process, and the fact that it’s limited to XP and Server 2003 doesn’t help to raise its priority at Microsoft. Both zero-day vulnerabilities have effective workarounds described by Microsoft.”
Doh ! This should have went in the article “How Many Zero-Days Hit You Today?” Sorry
The ZAccess back door which I seem to remember as Trojan.Win32.ZAccess (variant here), was one of the worst rootkits I’ve ever had to remove. Fortunately I was able to back up the files and scan them with Avast to get rid of the re-install executable. As expected the MBR was hosed trying to destroy this nasty rootkit, which even though had a Kaspersky definition, used chameleon techniques to prevent removal – I don’t remember how I forced the removal of the files, but it made the PC unbootable from the damage incurred.
This malware/virus should be considered a zero day threat, because it keeps itself updated to the newest dastardly version, and the machine may have to be taken off line for at least 24 hours before an MBR repair can be attempted using automated methods; or you can read up on the long drudgerous methods that might save you from a complete wipe and re-install.
I always first attempt rootkit removals from safe-mode using MBAR downloaded from the tools tab in MBAM. You may have to enable networking and do that in safemode as well. I usually have better luck getting the Master Boot Record and/or system files repaired using this venerable utility.
You can always go to a rescue disk in the PE environment, but I can’t guarantee the PC will be bootable, unless you are good at manually replacing corrupted MBR and system files from the Linux PE environment.
You know what works pretty good on rootkits?
Format and clean install.
For hell’s sake dude, seriously? Treat any modern infection as a disk failure and move on.
Don’t pay Russian gangs to unencrypt. Don’t try running MBAM and 15 other tools you swear will work. Don’t go tinkering with all that BS.
Ripley and SANS ISC agree: Nuke it from orbit.
If you have any kind of imaging capability, even Clonezilla, just keep an image of a last-known-good. It’s faster to re-image than tinker with all that garbage and MAYBE you “remove” it.
Sorry j;
I work for the client, not you. If they were as smart as you or I, they wouldn’t need my services. If they say that they want all efforts to recover files and machine integrity, then that is what I do – even if I tell them they can never trust the machine after that.
Agreed. In some cases a wipe/re-install is not an option.
There’s nothing special about running a bootrec /fixmbr, tdsskiller and combofix.
Just sayin’
Mechanical hard drives ALWAYS fail.
If you aren’t prepared to reimage or reinstall, then you aren’t prepared for anything at all.
True – they always learn this after the disaster, but sadly never before.
It may be that the click fraud traffic is being used directly by the botmasters, but most likely it is being sold on to other affiliates through sites such as realtrafficsource dot com, and mixed with genuine traffic from paid search etc. to disguise its origins. Pure click fraud form an affiliate in an ad network is fairly easy to detect statistically as a number of the metrics end up being outliers.
This is nothing compare to click fraud run by Google .
You have no idea how many samples of ZAccess/Sirefef I’ve been uploading and reporting this year. A few hundred wouldn’t be underestimating- they just kept pumping out new variants daily on the infection sites I know of.
Obvious: there are many that have expired or no AV solution.
Every week, I newly visit a Windows user that can’t comprehend their actions of responsibility in owning a PC. So as a good netizen, I clean what I can, and attempt to teach the party of the do’s and don’ts of the web. I can only teach/show so much.
And Brian, your website is my best tool to show these folks why they need to be diligent. Keep up the great reporting and exposures!
Obvious: AV provides a false sense of security.
While I still had my XP machine I used a BotHunter.
However, as I understand, it is not available for newer versions of Windows.
Does anyone have different information ?
Please see my previous comment as an attempt to answer your inquiry. Gearge G.; for some reason it went south in the thread.
I received an e-mail notice of a new version a couple of weeks ago but hadn’t looked at the details until now — seems that it has become wrapped into several companion (but commercial) AV rootkit software packages which will run on Win7+. Check to determine whether you’d like it further at:
http://www.bothunter.net/
Thank you Jim V – NxFilter might be another good freebee; it has excellent user reviews at CNET. I put more weight on user reviews than editorials.
Some techs like to run TDSKILLER from Kaspersky in safemode with networking, then RKill to assure any malicious processes don’t recover the malware upon scanning or reboot. then MBAM, and then some like to use Hitman Pro for a 2nd opinion. But honestly there are many ways to attack the problem – some of them safer than others – a lot of techs like Combo fix, but I don’t concider it one for newbies.
Since the anti-malware technical field changes so rapidly, it is probably better to go to CNET and read the user reviews for specialty tools like this, and see which ones are most effective from one period of time to the next. You Tube has some really good videos on the quickest easiest methods. I like watching Mat’s videos from Remove-Malware.com, because of his dry matter of fact, sense of direction.
Even if you simply re-image instead of going to all this trouble, don’t forget to scan your backup archive before recovering files backed-up incrementally from last image date.
I believe a blended defense/removal is necessary since the malware is designed to overcome many (but not all) AV/AM products on the market. Depending on a single product is pretty silly at this point, since no one product catches everything, but running multiple products tends to work around the product-specific exploits malware uses to hide itself.
What I also like to do is disconnect the boot drive and connect it up to a disparate system (Linux, OS X, etc.) for purposes of poking around the HD, looking for traces of rootkits. This can sometimes be a futile gesture, since how many default/cleverly named folders can a rootkit hide in (nearly infinite), but I’ve caught remnants left over by removal tools this way.
Is there any solid published data on either the destinations ZA contacts, or http packet data that ZA uses? I see a few ZA hits a month in AV over 5000 nodes, but ZA never actually seems to be present (false positives). I am interested in building some basic rules within our web gateway to detect / block / notify on ZA communications.