Organized cyber criminals stole more than $25 million from small to mid-sized businesses in brazen e-banking heists in the 3rd quarter of 2009 alone, federal regulators said last week. In contrast, traditional stick-up artists hauled less than $9.5 million out of U.S. banks over that same time period last year.
Speaking at the RSA Security Conference in San Francisco last week, David Nelson, an examination specialist with the Federal Deposit Insurance Corporation (FDIC), said online banking attacks against small businesses of the sort I have chronicled countless times over the past year netted thieves $25 million between July and September of 2009.
I wondered how that stacked up against real-life bank robbers here in the U.S., so I had a look at the FBI‘s published bank crime statistics for that same time period last year. Turns out, traditional bank robbers committed a total of 1,184 bank robberies during those three months, netting slightly more than $9.4 million (including $3,071 in travelers checks).
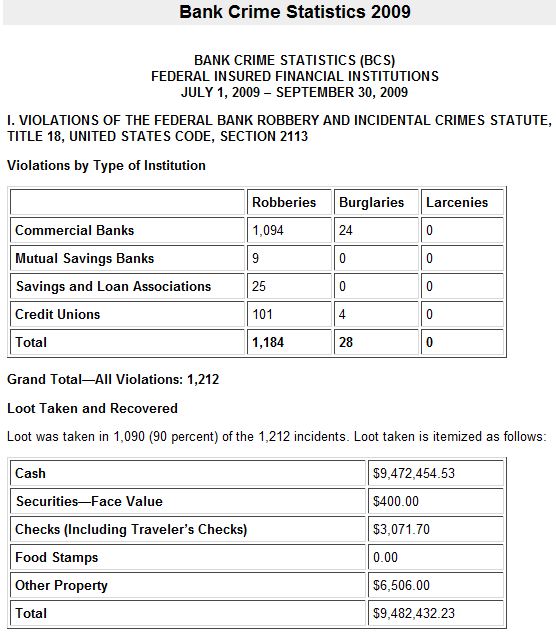 In fact, real-life bank robbers stole a total of just over $30 million in the first three quarters of 2009, just $5 million more than cyber crooks did in the third quarter of last year alone.
In fact, real-life bank robbers stole a total of just over $30 million in the first three quarters of 2009, just $5 million more than cyber crooks did in the third quarter of last year alone.
Small wonder that the haul from cyber bank robberies has overtaken that of physical heists: Cyber thieves take far fewer risks to life, liberty and limb than do real-life bank robbers. In that same three month period last year, the FBI says bank robberies at bricks-and-mortar institutions caused five deaths — all them perpetrators of the crime.
What’s more, the perpetrators of these incessant attacks against small businesses banking online for the most part reside in countries that are traditionally beyond the reach and influence of U.S. law enforcement. Sure, bank robbers occasionally kill people (more often themselves) while they’re stealing your money, instead of silently lifting it out of your bank account from afar like cyber thieves. That alone makes them a more emotional high-value target for the feds. But let’s face it: Traditional stick up artists are a lot easier to collar. For one thing, by necessity they are all here in the United States.
In addition, while traditional bank robbers are limited to the amount of money they can physically carry from the scene of the crime, cyber thieves have a seemingly limitless supply of accomplices to help them haul the loot, by hiring so-called money mules to carry the cash for them.
I can’t help but notice one other important distinction between these two types of bank crimes: The federal government sure publishes a lot more information about physical bank robberies that it makes available about online stick-ups.
Indeed, the FBI’s bank crime stats are extraordinarily detailed. For example, they can tell you that in the 3rd quarter of last year, bank robbers were more likely to hold up their local branch between the hours of 9 a.m. and 11 a.m. on a Wednesday than at any other time or day of the week; they can tell you the number of tear gas and dye packs taken with the loot, the number of security cameras activated, the number of food stamps taken, even what percentage of suspected perpetrators had illegal drug habits at the time of the robberies. About the only thing the stats don’t tell you is what brand of jeans the perpetrators were wearing and whether the getaway car had cool vanity plates.
What do we get about e-crime statistics from the federal government? One guy from the FDIC giving a speech at the RSA conference. And as we heard from the FDIC last week, the federal regulators could start collecting (and hopefully publishing) these kinds of statistics from America’s banks, but that would require an okay from the White House.
One of the first posts that I published at krebsonsecurity.com was a story about how much time and effort I put into trying to get the government to acknowledge how much cyber crooks were stealing from small to mid-sized businesses last year in these online banking attacks. Given this latest disclosure, it’s not hard to see why the banks and feds would be reluctant to part with that information.
The FBI hasn’t yet published the 4th quarter 2009 bank crime statistics, but if the $25 million cyber heist figure is representative of a quarterly trend last year — and the first three quarters of stats from last year’s FBI stats don’t deviate much in the 4th quarter — cyber crooks will have stolen well more than twice as much as traditional bank robbers last year in the United States.
I’m quite certain that if the infamous Willie Sutton had his heyday in the present culture, Sutton’s fabled answer to the question of why he robbed online banks would have been, “Because that’s where the *easy* money is.”




A theory. People are comforted by the fact that real world robbers will be pursued by authorities. Shoot-outs, whatever – people see they’re being protected. Or at least perceive it to be so.
But – and this is no secret to anyone here – there is as yet nothing to be done (save you-know-what) to stop the stream of money out of accounts through cyber heists.
In the one case the govt can say: ‘here’s what’s been happening and you know how we’ve been fighting it’. In the other case the only thing they can admit is: ‘here’s what’s been happening and up to now we’ve been powerless to prevent it’.
Which can of course lead to a hysteric string of withdrawals with everyone moving their savings to the 1st National Mattress Bank. And the fed govt can’t afford to let that happen. The banks can’t pony up if everyone wants their money back at the same time. The FDIC would have to step in and that would cost the fed govt a lot. And people would still lose as they’re only insured to a certain level – in this case not against cyber theft but against their banks running out of liquidities.
The guess is people are going to have to get a handle on and curb cyber theft first before anyone is going to formally admit just how bad it is.
Great article, Bk. Someone is going to start turning up the heat on you (if they haven’t already). Keep in there. Cheers.
A theory. People are comforted by the fact that real world bank robbers will be pursued by authorities. Shoot-outs, whatever – people see they’re being protected. Or at least perceive it to be so.
But – and this is no secret to anyone here – there is as yet nothing to be done (save you-know-what) to stop the stream of money out of accounts through cyber heists.
In the one case the govt can say: ‘here’s what’s been happening and you know how we’ve been fighting it’. In the other case the only thing they can admit is: ‘here’s what’s been happening and up to now we’ve been powerless to prevent it’.
Which can of course lead to a hysteric string of withdrawals with everyone moving their savings to the 1st National Mattress Bank. And the fed govt can’t afford to let that happen. The banks can’t pony up if everyone wants their money back at the same time. The FDIC would have to step in and that would cost the fed govt a lot. And people would still lose as they’re only insured to a certain level – in this case not against cyber theft but against their banks running out of liquidities.
The guess is people are going to have to get a handle on and curb cyber theft first before anyone is going to formally admit just how bad it is.
Great article, Bk. Someone is going to start turning up the heat on you (if they haven’t already). Keep in there. Cheers.
Bank robbery is up, it is said, because of two factors:
1) Less cash at small stores thanks to debit cards;
and
2) Bank tellers never shoot. Store clerks sometimes do.
Even at $150 million in combined physical and cyber losses per year, that works out to be what…the money banks make if each of their customers make a single out-of-network ATM withdrawal each year?
$150M is readily insurable. And yes, you can insure deposits of more then $250K — my town, for example, pays a small premium that guarantees our entire bank balance against risks such as the bank failing.
I suspect this is where most of the outrage is on small organization cyberthefts were seeing — they hit a very small number of businesses very, very hard; the industry would probably be able to handle the issue for less money and better PR simply by insuring accounts against such losses then the expense of extremely tight security like out-of-band transaction authentication.
Whats surprising is both pale in comparison to the $1B/year in ATM skimming in the domestic U.S. reported on this site.
Even that, among all the accounts in the U.S., would represent perhaps $10 per account per year to insure any individual against loss.
The risk with all three is left un-checked that such losses would grow beyond the relatively trivial amount they currently are.
Reading between the lines, it is clear Brian that you’re intensely frustrated that your months (years?) of work in exposing these cyber-frauds conducted against small businesses is simply not being taken seriously – either by the mainstream media or by the relevant authorities. I share your frustration!
I am no conspiracy theorist…but when you see this kind of silence despite the overwhelming evidence, there is only one reasonable conclusion to draw. There must be a concerted effort going on to cover up these crimes. Why could this be?
For me, that’s an easy question As we all know, the Western financial system came to the brink of collapse a year or so ago…and many banks are not out of the woods yet. In fact, most of their losses have been swept under the carpet and are still sitting on their books.
Banks enjoy huge efficiencies (and thus profits) from moving their customers to online banking. if there was a wholesale loss of confidence and rejection of this electronic banking by customers resulting in a return to personal visits to the banks, more tellers would have to be hired and all these efficiencies (and profits) would disappear.
In addition, the real estate mess in the US continues with Alt-A residential mortgage resets due to climb this year and the commercial real-estate carnage just getting going. These losses for the banks will be in the billions. That is where their focus will be rather than on a few million being lost to small businesses due to online fraud.
Please continue to expose these frauds…but realise that you’re fighting a very powerful industry that does not want the dirty secret of the Internet to come out…and that is that the Internet is fundamentally broken when it comes to security and that no sensitive financial transactions should be carried out on the Internet using a Windows PC.
Good luck!
Rather than harp on the bank industry (which I certainly have done my fair share of in past postings), I’m willing to bet that the visibility problem is more about personal safety than it is about money.
Bank robberies are bad because they put “innocents” in harms way. The threat of death in the pursuit of a few bucks is a completely illogical act to most people since we tend to rank life a whole lot higher than wealth. So, the FBI tracks bank robberies in more detail because the perceived impact of a robbery is pretty high.
By comparison, cyber-thefts are fairly easy to ignore. They only deal with the age-old premise of forcing the movement of money from one pocket to another. Most people probably consider this to be a “victimless” crime because the probability of an “innocent” being hurt is nil. Sure, we may consider losing money from our bank account to be a huge inconvenience, but it most likely won’t directly impact our ability to live life.
To demonstrate that these types of crimes warrant an increased level of attention, we need to be able to demonstrate that they represent a significant impact. Without the threat to personal safety, the only way to do that is to encourage a perception of a strong economic consequence. Unfortunately, at $100-$150M a year (my loose estimate) in losses for all US businesses, we don’t have much of a case to make.
Ah, so if you can’t do the time, do white collar crime, right?
I don’t think that I would put it that way, but we all have to admit that these kinds of crimes are made much easier by the general inability to be held accountable for it.
I caught Steve’s response below about how the FBI shouldn’t try to fix everything and agree completely with it. What we have here is a risk management conflict. We recognize that businesses are losing money, and we agree that the economic impact is larger than the closest off-line equivalent, but what is the value of the actual risk from the US perspective? If there is no perceived risk that lives are at risk, then these attacks fully represent a class of financial risk. That risk, as demonstrated in the statistics that we’ve been collecting as a community, is negligible from a US perspective.
In an economic environment where losses are measured in hundreds of billions and a man like Bernie Madoff can milk around $20B from investors while staying under the radar for decades, we’re just not talking about a significant loss from a regulatory perspective. It would be like a police officer pulling over someone for a seat belt violation when someone is getting beaten up across the street. Where would we rather limited resources be focused?
None of us like it, and we’ve been having these revolving door discussions on what should be done, but the real question is what can we do?
My suggestion is that we begin a grass-roots effort to improve the culture of security in the current business environment. If we really believe this to be a problem, then we should be a part of the solution. Here are some suggestions of ways we can act:
– Reach out to small business owners you know to help them understand the risks and to develop simple, low-cost ways for them to better protect themselves.
– Set up meetings with various government representatives to identify outreach opportunities and enhance existing messaging if you have the credentials to deliver.
– Host free security seminars for your local business community.
– Distribute BK’s postings over social network channels to your family, friends, and colleagues.
These are the actions that my company is doing today, but I’m sure that there’s more that we can do. I credit BK for providing the ammunition to fuel these efforts, but we need to look to ourselves, and not the government, if we want to solve the problem.
I think it’s a numbers game. Law enforcement may willingly go after the guy who stole M$5 from a bank but may not if he stole $1 each from 5 million victims unless people complain in sufficient numbers to warrant launching an investigation in the first place, and who would complain about losing $1?
Michael — The crimes I have been referring to in this post are those that I have documented ad nauseum here:
http://www.krebsonsecurity.com/category/smallbizvictims/
We’re not talking about $1 and $5 here and there from different victims. We’re talking about $100,000 and $500,000 and in some cases millions being stolen at a time from small businesses, counties, cities, school districts and governments across the country.
Brian is correct. It was clear during the June, 2003 hearings on the identity theft provisions of the Fair and Accurate Credit Transactions Act (FACTA) that the bank executives at the witness table measured the crime in “dollars”, while the elected representatives of the people at the front of the room measured them in “victims”. To quote the Vivian Ward character in the movie “Pretty Woman”, “Big Mistake. Big, HUGE Mistake!”
$25,000,000 is 250 $100,000 losses, and, as Brian has documented with the sad case of Long Island-based Little & King, a $100,000 loss is enough to *kill* a small company with a thriving business.
A small- and medium-sized enterprise
Federal regulators could start collecting (and hopefully publishing) these kinds of statistics from America’s banks, but that would require an okay from the White House.
OK. So who do we start sending our letters to, urging them to change this policy?
“that would require an okay from the White House.”
You mean like the President’s call for transparency in his inaugural address, or more like the Presidential Directive he issued that day?
Who needs the engraved invitation, and on what basis are the new regulations insufficient?
Excellent article. Excellent suggestion: who do we write to encourage more transaprency here?
A follow-on question: does anyone know why banks have to be beaten/threatened/compelled to disclose anything? Why is it that in 2010 blogs such as this one are our only source of info on what’s going on?
It’s not just bank crime. All kinds of crime on the internet are largely ignored by the FBI. This is so wrong. It’s probably because it takes a long time for the FBI to change direction. Thats how they missed 9/11.
Scammers, junk mail, DOS,viral attacks, phishing etc. All these cause so much loss but are mostly ignored as far as I can tell.
Quoting from Brian’s article might help to explain why this gets ignored by the FBI:
“In fact, real-life bank robbers stole a total of just over $30 million in the first three quarters of 2009, just $5 million more than cyber crooks did in the third quarter of last year alone.”
We don’t look at “cyber” crooks as “crooks!” We prepend with a statement like “real-life bank robbers,” when we turn around and refer to what *are* real-life bank robbers.
Steve wrote:
“> It’s probably because it takes a long time for the FBI to
> change direction. Thats how they missed 9/11.
How about something more realistic, and to the point. Sometimes, there isn’t anything that they can do.
You can’t look at every failure, no matter how big, and say ‘look, they didn’t protect us’. ”
I don’t know if the commenter Steve replied to meant the FBI should prevent this, but the investigation, follow-up and prosecution is sorely lacking. Our laws are sufficient but very few attorneys and judges understand that electronic crime isn’t all that different from real-world crime, and even fewer can make the correlation necessary to help others understand that.
A bank robber is someone who steals from banks. But the fact that it isn’t considered robbery if a robber steals from a specific account is ridiculous. That $25 million should be reported and tracked by the FBI just like the “real” robberies are.
> It’s probably because it takes a long time for the FBI to
> change direction. Thats how they missed 9/11.
How about something more realistic, and to the point. Sometimes, there isn’t anything that they can do.
You can’t look at every failure, no matter how big, and say “look, they didn’t protect us”. Believe it or not, stopping crime before hand (whether its bank robbery or mass murder) is beyond their capabilities until “crystal balls” are perfected.
9/11 was no more of a failure than these online bank robberies. They are the result of people with their own agendas exploiting specific problems to achieve their goals. The FBI cannot, and SHOULD NOT TRY, to find every such problem and fix it. Its a futile effort and has to be done by the people involved.
You want to see it fixed…. make banks liable for your lack of access to your money during the period where you don’t have it. Make it more than just a matter of “well we can insure against that” and they will take measures to make sure that it doesn’t happen more.
Hi Folks,
Reading with some interest here since we’re trying to develop our focus for our December Financial Services event for InfraGard. InfraGard is a public/private initiative of the FBI http://www.infragard.net and the undersigned runs the NY InfraGard Members Office http://www.nym-infragard.us.
So, why, why..why? Well, my considered opinion and years at NYPD and now with the FBI InfraGard Program places me in a position to discuss this and perhaps to add some daylight to the why’s in law enforcement.
First, there is a difference in NYPD Vs FBI focus. Let’s face it, the NYPD has something like the 6th or 7th largest army in world. So by size the NYPD dwarfs the FBI in personnel numbers. The FBI’s largest field office is here in NYC. It is the number one largest field office in the world. Some exception with the Headquarters building. NYPD’s focus is on NYC and how outside ops can impact it so far as safety and security is concerned.
NYPD is looking at the NYS Penal Law. So examine it and see how it applies to your discussions and go from there. I’m sure that there are plenty at NYPD who with great delight would pursue addressing crime under NYS law. In NYS we call 911 for crimes in progress or visit a local detective squad if we have information on a crime. We do this quietly, politely and with a passion for crime control, safety and due care, not out of an eye for an eye.
The FBI is a totally different animal. Yes, both are law enforcement agencies…..but you need see and understand the limited bandwidth of the FBI and the 180 or so violations that they are charged with addressing nationally and how it takes them worldwide. So you have this image of a giant funnel and only so much can fit through the tiny spout at the bottom. When you begin looking at things with this set of eyes then you can begin to understand how the FBI reacts differently then a local law enforcement agency. Remember, the FBI has national jurisdiction and when they are challenged to address an issue…..they do so with efficiency, stealth and poise so that the greatest impact can be made. While it may be true and can be argued that what’s worst a thousand cuts of the knife or a broken limb? That’s not going to get you anywhere in these discussions. Its more of the dog casing it tail again and again….oh yes and again. It really doesn’t resolve things. So the single one dollar crimes are certainly something to look at, but the big fish is always going to get the attention for national resources to be dedicated.
So what can be done and what should be done? We hear much of the government should be regulating this and that and protecting all of us from the FUD……fear, uncertainty and doubt – that we hear of every day. Fraud here, Academic sites compromised for ACT or SAT scores there, another bank with customers hanging out there…..more credit exposures the list just goes on and on.
Well, first safeguard your own PI. Then work on your family and friends. Unless you have the depth of Citi Group or Morgan Stanley you can’t write these losses off. So as independent citizens we need to take personal responsibility for our own PI and use of the internet smartly. Once we have accomplished this…..a long term strategic goal….then we can talk about national ID, and many other thoughtful and suggested recommendations to tighten things up. No one is going to protect you from a poor education. So don’t get behind the wheel of an automobile unless you’ve taken drivers ed, don’t operate machinery without safety equipment on and don’t go on the internet unless you know what you’re getting into and have taken some awareness course (most free) so that you can enjoy your experience. If you pull just any life saving device off the shelf and don’t examine whether its been inspected, ready for use or is just laying there by mistake because someone put the old broken one on the wrong shelf……well…..you’ve got a problem. Invest in your internet use and technology use by understanding what you’re bringing into your home/office and then calculate the risk of putting any information out onto the web at all. In the end this is all going to fall on the shoulders of YOU, the individual. Corporations pay big bucks to shield themselves from harm. What has your family invested in to shield its members from harm? Attend an awareness course in the last ten years? Ever?? Most likely not, although some most likely got the lecture at work and slept through it. Otherwise we wouldn’t be focused on it here.
It’s a mistake to think law enforcement will cure the ills of society, internet related or not. They barely touch the surface of crime as it is and then only based upon citizen reports and chance observation. Those of you ready to stand up and say I’ve been not so smart and lost X number of dollars with online betting, gambling, girly web sites or some other not too smart things please do let us all know. Right now very few admit to poor use of the internet and remain quiet victims within the environment of there homes.
With that said, many technology companies could do more to pour security into the early stages of development with Software and Hardware. But this will not in the end overcome the careless, abusive and sometimes completely irresponsible drive by internet users.
Anti-virus vendors will have to change there approach as signature based AV is a thing of the past since virus writing is now considered an “occupation” for some world-wide.
Facebook is enjoying the enlighten masses digging up contacts from yester year and plowing though the memories of a distant past. One in fourteen are on Facebook world-wide and guess what so are organized crime and the purveyors of all sorts of fraud. So what’s so new here….not much.
Lastly before I go too off focus….law enforcement will do what they can with the information that they have. If you think they are ineffective….try working with them and understand prosecutions, rules of evidence and the criminal procedure law. You voted and wrote it, so you should be aware of it. If you don’t like what you and your elected officials wrote….well, that’s another discussion for another day.
All the best,
Joseph Concannon
NY InfraGard Inc.
My bank called me last year and said it spotted some suspicious activity on my card. At the time of the call, the bank had already issued a new card and it was already on the way. They knew which retailer I shopped at, and that the activity happened about five minutes after I used my card. However, when I asked which retailer they identified, they refused to pass the information onto me. I only bought one thing that week, so I knew which retailer it was.
So, the bank industry “sees” the suspicious activity, but they don’t give any details because they want to keep the rosy picture in the forefront. And since cyber crime is becoming such a huge thorn in the banking industry, it will eventually affect us all. That the FBI doesn’t do anything about it really doesn’t shock me. I called an online retailer yesterday and I was ready to order. He read my New York address back to me, but I have never lived in New York. End of call! With identify theft the FBI has dropped the ball, so cyber criminals see the Internet as an easy, lucrative, and low risk way to get rich.
>It’s probably because it takes a long time for the FBI
>to change direction.
No, they turn on a dime.
Just have a TV news crew show up. Moths to a flame.
If there isn’t going to a perp walk that generates publicity, at best the case will be handed back to local and state police.
Been that way since J. Edgar Hoover.
But this does bring up a good point of both defense in depth and federalism.
Consumers and banks both have responsibilities here.
Insurance systems also have a role.
Its often less expensive to insure for a loss then to prevent it. You just need the right balance of actuarial science and political acumen to know what losses money can simply make good, and when there is a loss of trust that impacts the long term business.
Government, at all levels, have a role in ensuring commerce can be carried out in a reasonably safe and stable manner.
Stability is probably the more important part — we tolerate auto accidents because they happen frequently and on a small scale; airplane accidents cross a political threshold where people don’t tolerate them since they are unusual and big. Safety can follow stability, as we see with the continuous, incremental improvements in highway safety.
Knowing law enforcement, at least today, is very difficult we come down to it being more important that the Federal Government put diplomatic pressure on foreign states to end these cross-border crimes then it is to commit FBI resources on the remote hope of winning a conviction.
I agree that more transparency is needed, and note the interesting call for ideas about cybersecurity education posted by Homeland Security: http://www.dhs.gov/files/cyber-awareness-campaign.shtm
But remember, asking law enforcement to stop a crime before it happens invites a big brother, totalitarian state.
Small wonder that the haul from cyber bank robberies has overtaken that of physical heists: Cyber thieves take far fewer risks to life, liberty and limb than do real-life bank robbers.
Good point, but add this – the *banks* take far fewer risks as well. When their customers money is stolen online they get to push risk onto the consumer with claims about “identity theft” and so on, but if the actual physical dollars are stolen in a bank robbery those dollars are gone.
$25 million is a fraction of the bonus pool at Goldman Sachs, or AIG.
I like the way you’re conceptualizing this problem, Michael. So let me ask
you this question: Should it make it any more or less relevant as an issue
the federal government should care about if one could show that some of the
money being stolen from businesses is going to fund terror groups? I’m not
suggesting I can prove or show that, I’m just curious about the answer.
Knowing what I know about how the FBI at least is structured right now, it
seems like that is about the only thing that would allow agents there to
spend more time on this type of crime…aside from maybe showing that it was
benefiting child pornographers as well.
You raise an interesting point. In my experience working with the government, I would say that the link is too far removed to do much good as a justification. Folks tried to make that linkage to build greater support in fighting drugs, but I think that those efforts have largely failed. Also, the money that we’re talking about is probably still insignificant in relation to the funding that terrorists need.
Unfortunately, I think that the perception of these attacks is that they more represent mob or gang activities than terrorist activities. As such, they fall into a much more fictional reality for most people in the US. We’ve come to accept that those organizations exist, but they are perceived to go after closer associates rather than choose random targets.
Until folks understand that we are dealing with a new paradigm in criminal activity that has little connection to historical schemes, they’re perception won’t change without being victims themselves.
@wiredog
Your comment might be considered rude in some circles, but I have no problem with it at all. In fact, I think it cuts right to the heart of the matter …
When it became possible to transfer value by wire, the concept of “Other People’s Money” reared it’s ugly head. This happened long before we had desktop PC’s, The theory goes that “currency” is like any other fungible commodity in inexaustable supply, it has no Intellectual Property Value – it’s all “Other People’s Money”. Well, not quite, “Other People’s Money” is like other people’s air.
Except of course when somebody takes “Your Money”. You call that robbery. It’s fairly insane to entrust your money to people who see no difference in the act of storage and the act of going to the Casino, but at very least you can be a little skeptical when they say “Sorry, but somebody broke into the vault while I was at the Casino, but for a small fee I’ll take (our) money to the Casino next time”.
Different numbers?
Interestingly, Computerworld uses a $120M, “…rose to over $120 million in the third quarter of 2009, according to estimates presented Friday…” http://www.computerworld.com/s/article/9167598/FDIC_Hackers_took_more_than_120M_in_three_months?source=rss_news
and SANS NewsBites email says $120 Million, and $40 million each month, even though they link to you, Brian.
Care to comment on the discrepancies?
@Lynda – I don’t know where SANS got its numbers from. But I believe $120M figure you’re seeing floating around is supposed to represent a cumulative number — not just one three-month period’s worth).
I think the $120 million figure includes losses (such as those from ATM card skimming) that are covered by Regulation E and therefore the banks have to eat. The $25 million figure is FDIC’s Dave Nelson’s number for the losses to *commercial* customers that the banks did not reimburse because the government does not (currently) compel them to do so.
Brian is correct. It was clear during the June, 2003 hearings on the identity theft provisions of the Fair and Accurate Credit Transactions Act (FACTA) that the bank executives at the witness table measured the crime in “dollars”, while the elected representatives of the people at the front of the room measured them in “victims”. To quote the Vivian Ward character in the movie “Pretty Woman”, “Big Mistake. Big, HUGE Mistake!”
$25,000,000 is 250 $100,000 losses, and, as Brian has documented with the sad case of Long Island-based Little & King, a $100,000 loss is enough to *kill* a small company with a thriving business.
A small- and medium-sized enterprise being murdered in over half the congressional districts in America every quarter will draw a political response. That response will come much quicker if, for some reason, this cause attracts a “lobbyist” willing to work “pro-bono”…
I totally agree they should release the stats.