A crackdown by the Chinese government on anonymous domain name registrations has chased spammers from Chinese registrars (.cn) to those that handle the registration of Russian (.ru) Web site names, new spam figures suggest. Yet, those spammy domains may soon migrate to yet another country, as Russia is set to enforce a policy similar to China’s beginning April 1.
In mid-December 2009, the China Internet Network Information Center (CNNIC) announced that it was instituting steps to make it much harder to register a Web site anonymously in China, by barring individuals from registering domains ending in .cn. Under the new policy, those who want to register a new .cn domain name need to hand in written application forms, complete with a business license and an identity card.
Chinese authorities called the move a crackdown on phishing and pornographic Web sites, but human rights and privacy groups marked it as yet another effort by Chinese leaders to maintain tight control over their corner of the Internet. Nevertheless, the policy clearly caught the attention of the world’s most profligate spammers, who spam experts say could always count on Chinese registrars as a cheap and reliable place to buy domains for Web sites that would later be advertised in junk e-mail.
According to data obtained from two anti-spam experts, new registrations for sites advertised in spam began migrating from .cn to .ru just a few weeks after the Chinese domain policy took effect.
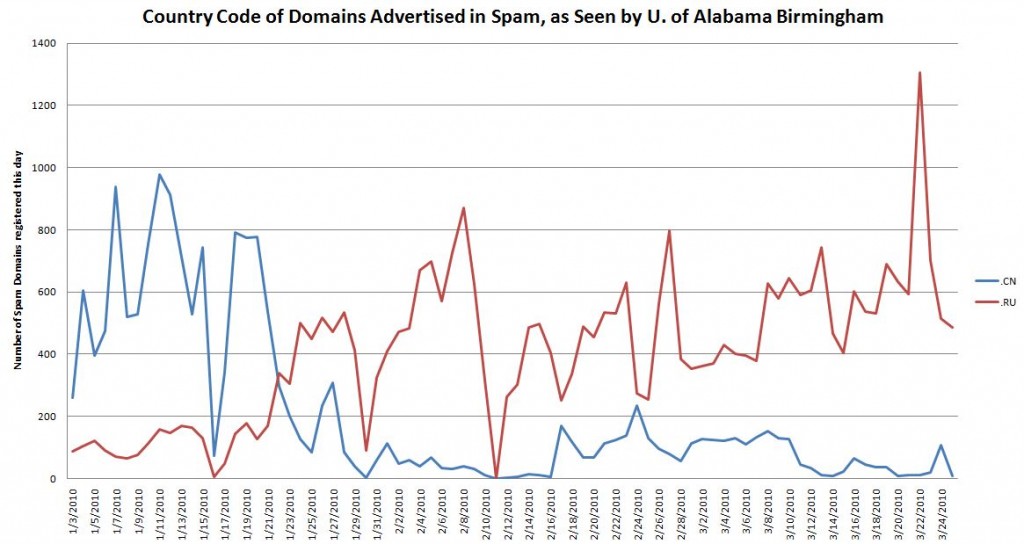
In early January 2010, and indeed in the months leading up to the new year, the percentage of domains advertised in spam registered in the .cn space dwarfed the number of .ru spam-related domains, according to figures gathered by the University of Alabama at Birmingham. But by mid-January, the number of .cn spam domains began to fall off dramatically, while the number of .ru spam domains increased markedly, UAB found (see graphic above).
Gary Warner, director of research in computer forensics at UAB Birmingham, said a sizable share of spam-related new domain registrations continue to come through the .com space — which is served by hundreds of domain name registrars. But he said the biggest bulk registrations for spam domains routinely came out of .cn, particularly those associated with rogue online pharmacies.
“The .com never had the volumes of abuse you’d see at one time in .cn, where you’d typically have one guy registering hundreds or thousands of spam domains every day,” Warner said.
There is a decent chance that the spammers will move to another country-code registrar soon. Beginning April 1, Russia’s Coordination Center for domain registration will require individuals and businesses applying for a .ru address to provide a copy of a passport or legal registration papers.
Warner said he’s looking forward to seeing a similar exodus from Russia in the weeks ahead.
“I’m excited about the prospects of seeing the [number of] .ru spam domains going down just like we saw with China,” he said.
I wanted to gut check these figures, so I asked Andy Fried, a computer forensics expert who formerly tracked spam and phishing domains at the Internal Revenue Service, and is now a researcher at the Internet Systems Consortium, a Redwood City, Calif., company whose open-source domain name system (DNS) software powers millions of Internet servers around the globe. Fried checked ISC’s spam traps a few days ago to see if they were showing the same trend.
Fried found that over a 24-hour period, ISC’s spam traps had identified more than 10,000 unique domain names being advertised in spam. More than 1,870 of those domains were tied to recently registered rogue pharmacies, and of those, 491 were registered in the .com space, while 18 were from .cn and 1,366 were at .ru Web sites.
“Originally, the vast majority of the pharmacy spam site registrations were coming out of China, and now they’re almost all coming out of Russia,” Fried said. “It’s a good bet they’re going to be moving from Russia to some other top-level domain soon.”




SSpeaking of Spam… Looks perfectly legitimate to me!
Something doesn’t seem to add up with the below para. Shouldn’t they add to 1170?
More than 1,170 of those domains were tied to recently registered rogue pharmacies, and of those, 491 were registered in the .com space, while 18 were from .cn and 1,366 were at .ru Web sites.
Hey John. Thanks for pointing that out. My typo. Should be “more than 1,870”. I’ve fixed it in the copy above.
Thanks for the spam followup. If spam domains move from China and Russia to a location that will not crack down on unsolicited email, will ICANN get involved? What will be the recourse then?
Unless I’m mistaken, ICANN has no jurisdiction over country-code top level domains. They can exert influence over .com, .net. biz., and other generic top level domains, but they can’t do much but ask on the country-code stuff.
The sponsorship varies from country to country, but there is a central registrar – ICANN operates IANA.
http://www.iana.org/domains/root/db/
I saw a “policies and procedures” link near the top.
And finally got to this
http://www.iana.org/abuse/faq.html
There are some very helpful hints on using whois (worldwide)
Gary Warner is a great asset for the InfoSec community. He introduced me to the practice of phrying phish several years ago. Thanks, Gary! .. and Brian too.
They will use stolen credit information to buy domain space in the free world, where it is still unregulated. It has already happened to me.
The cockroaches will skitter to the next country that does not have a bright light shining on them, like Korea or Romania. No doubt some registrar will gladly accept the buckets of money thrown at them by the RBN (Russian Business Network) for bulk registrations of spammed domains…at least until they are shooed to the next country.
From your posts, understand that you had mentioned the RBN.
From the Book Title: Fatal System Error, understand that James McQuaid actually blocks out RBN through a list of RBN IPs. Googled and located the list here :
http://doc.emergingthreats.net/bin/view/Main/RussianBusinessNetwork -> http://doc.emergingthreats.net/bin/viewfile/Main/RussianBusinessNetwork?rev=174;filename=RussianBusinessNetworkIPs.txt
In your expert opinion, is such list workable?
If yes, why isn’t such list made commonly to the wider public?
There are lots of lists of bad IP ranges that people do use for blocking, but it’s not that easy. There are malware infected computers all over the world that can be used as open proxies for criminal activity. Those computers are often owned by people in your own community and are often dynamic IP addresses (the computers are assigned new IP addresses every time they log in). If the RBN is working through your neighbor’s home computer, you can’t block them without blocking everyone in your area using your ISP. And if your neighbor were competent enough to block the RBN’s own IP range so they can’t access his computer, he probably wouldn’t have gotten his computer infected with a trojan in the first place.
krebsonsecurity.com у Вас хороший блог контекст правда нужно почаще обновлять васже читают.С праздничком
Я ни понимает. Я пишу в английском.
If anyone is interested, the address for reporting hotmail addresses used for spam and abuse is report_spam@hotmail.com
Thanks AlphaCentauri! I was beginning to think the “mark as phishing email” was not enough. I got to admit, the junk mail is pretty slim on hotmail. But I’m finally noticing a very few phishing emails for the first time in more than three years!
That’s the report for reporting hotmail email accounts being used in violation of their terms of service, not for spam sent to hotmail addresses.
It’s for spam actually sent from a hotmail address, or spam with email contact information that uses hotmail (e.g., a Nigerian spam that asks you to send your personal information to a hotmail address).
If you want to do more than just click a button to report spam arriving in your hotmail email inbox, there is a forum at http://ksforum.inboxrevenge.com that will orient you to spam reporting. You will learn about the various illegal activities that support or are supported by spamming, and how to get criminal websites shut down fast enough to impact their profitability.
The forum spam that was posted here has been removed, so the hotmail reporting address is not pertinent now.