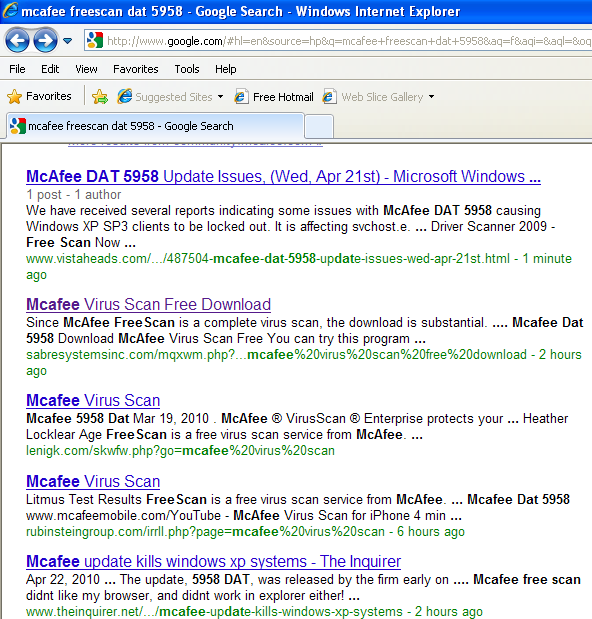
Purveyors of rogue anti-virus, a.k.a. “scareware,” often seize upon hot trending topics in their daily efforts to beef up the search engine rankings of their booby-trapped landing pages. So it’s perhaps no surprise that these scammers are capitalizing on search terms surrounding McAfee, which just yesterday shipped a faulty anti-virus update that caused serious problems for a large number of customers.
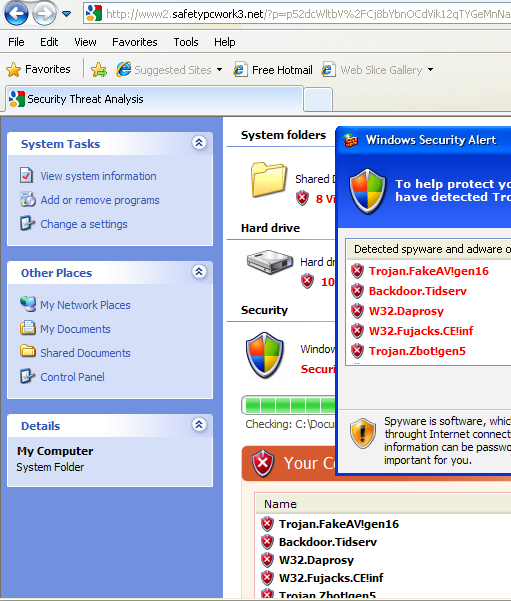
Searching for McAfee’s free scanning tool along with the name of yesterday’s bad update returns page after page of results that when visited launch the familiar come-ons that try to frighten visitors into purchasing bogus (if not also malicious) anti-virus products. I took the screen shots here with Internet Explorer 8, because as usual the booby-trapped pages simply would not load with the noscript add-on enabled in my version of Firefox.
Update 11:08 a.m. ET: Panda Security just published a similar post which lists a number of McAfee-related search terms that can lead to sites like those in the screen shots below.




The only McAfee product that I run is the SiteAdvisor, and I do like it. If they ever update that, you bet I’ll wait before implementing. Of course, I always wait a few days before downloading and installing any software updates, especially MS and Java. I allow absolutely no updates to download and install without my permission.
I hope this type of thing doesn’t — or is much less likely to — happen to Norton.
Funny, the Fake AV shows on their fake av scanner an infection of Trojan.FakeAv as the top infection…classic!
Of course, there is a basic flaw to applying my policy, above, to the downloading of virus definitions. If one turns off automatic definition updating (I run F-Secure AV and Threatfire) and waits until it is “safe” to download new definitions, how long does one wait? Meanwhile, the whole purpose of timely definition downloads is compromised. Whether auto-downloading or opt-in downloading, I suppose that what happened to McAfee subscribers can happen to subscribers to any AV service.
You still should not turn off automatic updating. For the most part think big picture how many definitions and heuristics updates come out daily and this one incident (which is easily fixable) happens and you want to consider changing your habits?
I for the most part am a big proponent of stronger heuristics which AV is moving towards because signature based is really failing and am glad to see them moving in the right direction.
agreed. failures are not an option, they are a given – plan for them. its only a matter of WHEN it fails, and WHY. but not updating is INVITING the problem. i have cleaned a boatload of virii from pcs in the last few weeks – the most common ones are due to java not being updated to v20, or ie6 and 7 not being updated. im working on a dell xps laptop now, java v6, ie7, and he has lots of virii – no task manager, and all that that goes with it, except no rootkits.
after that, its user training – which is harder.
@BK & hman: Good sense re auto AV updates. One more thing re software updates that makes me hesitate: The latest MS patches and Java 19 both made my XP/SP3 system “hang” at the log-in screen during the mandatory restarts. Both times, I had to totally shut down (took forever), wait awhile, cross my fingers and reboot from total off. Took a long time, but I finally got back to my desktop this way. Everything else in my system works fine, but these two aborted restarts have made me wary about updates, at least from MS and Java.
Mark, I have encountered similar problems with the Microsoft Windows XP updates issued on Tuesday, April 13. I was finishing the process of re-installing Windows XP “from scratch” before I added those six, and I don’t know which patch or patches are the source of the unstable and irregular behavior.
Sandboxie, which I’ve been using for over a year, could not function properly because of the KB979683 security patch, and the developer rushed to issue a version that will work with that patch installed (it won’t work without that patch installed, too).
@Stardance: Thanks for your relevant note. Since my last post, I have downloaded and installed Java 20. Significant that, unlike Java 19, Java 20 did not require a restart. Thus, it gave me no problem. However, I just now noticed that installation of Java 20 undid my disabling of Java 19’s deployment toolkit in Firefox. As for “I don’t know which patch or patches are the source of the unstable and irregular behavior,” I wiped my hard drive and reinstalled OS et al. software a little over a year ago, with no problems from software updates until recently. Thus I suspect that, in your case, more recent software updates are boogering your just-wiped system.
i don’t use any antivirus. they take up space and your computer can still get hijacked. if you get viral popups, try opening the command window and cancel any processes that look rogue, like hotfix.exe. if that doesn’t work, reboot to safe mode with networking by tapping F8 upon reboot and selecting safe mode w/ networking at the advanced options screen.
go to http://www.malwarebytes.org and download the free version. MAKE SURE YOU UPDATE IT EVERY TIME BEFORE YOU RUN IT. and run a quick scan. download “hijackthis” from cnet.downnload.com (you can google search it and go from there). download and open hijackthis and select “system scan and save logfile”. copy and paste the logfile in the empty box at http://www.hijackthis.de then get rid of anything in hijackthis that has a red X next to it on the analyzer list
a good follow up is super anti-spyware. go to http://www.superantispyware.com and download the free version. once again, MAKE SURE YOU UPDATE IT EVERY TIME BEFORE YOU RUN A SCAN.
if either malwarebytes and/or superantispyware find rootkits then you will need to run a rootkit remover. now is the point where you do research on rootkit removers before it’s too late. for 32 bit operating systems, research how to run combofix. for 64 bit operating systems i recommend gmer, but do your research first.
the more you reseach now and get ready to fight off infections, the better off you will be.
but remember, you could spend a hundred bucks on norton or mcafee or even avg, and you could still get infected. do anti-virus programs really protect you from everything? the answer is no. i worked at a tech support company where people would call up with infections and their antivirus programs were usually norton or mcafee.
do your research on how to get rid of rogue anti-virus programs and i guarentee malwarebytes will be the most recommended program