Criminals this week hijacked ChronoPay.com, the domain name for Russia’s largest online payment processor, redirecting hundreds of unsuspecting visitors to a fake ChronoPay page that stole customer financial data.
 Reached via phone in Moscow, ChronoPay chief executive Pavel Vrublevsky said the bogus payment page was up for several hours spanning December 25 and 26, during which time the attackers collected roughly 800 credit card numbers from customers visiting the site to make payments for various Russian businesses that rely on ChronoPay for processing.
Reached via phone in Moscow, ChronoPay chief executive Pavel Vrublevsky said the bogus payment page was up for several hours spanning December 25 and 26, during which time the attackers collected roughly 800 credit card numbers from customers visiting the site to make payments for various Russian businesses that rely on ChronoPay for processing.
In the attack, ChronoPay’s domain was transferred to Network Solutions, and its domain name system (DNS) servers were changed to “anotherbeast.com,” a domain registered at Network Solutions on Dec. 19, 2010.
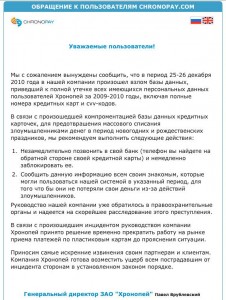
The attackers left a message on the ChronoPay home page – designed to look as if it had been posted by Vrublevsky (see image above) – stating that hackers had stolen the personal data of all ChronoPay users who had shared payment information with the company in 2009 and 2010.
Vrublevsky said the message was faked — that it was “absolutely not true” — and that the damage was limited to the 800 card numbers. He added that the company was still working with its registrar Directnic and with Network Solutions to understand how the attackers managed to hijack the domain.
The hackers also stole and posted online at least nine secret cryptographic keys ChronoPay uses to sign the secure sockets layer (SSL) certificates that encrypt customer transactions at chronopay.com. Vrublevsky said all but one of those certs were issued long ago: One of the certs was issued in September, albeit with an older key, he said.
Loyal readers of this blog may have noticed that I have spent a lot of time digging into the activities and history of ChronoPay and Vrublevsky. In my earliest report on these two, I followed a string of evidence that suggested Vrublevsky also was the founder and curator of Crutop.nu (NSFW), a Russian adult Webmaster forum that has been linked to all kinds of badness. In that report, I noted that Crutop.nu and Chronopay.com even shared the same Google Analytics code (UA-630887) on their homepages, which further suggested a fundamental connection between the two sites.
At the time, a ChronoPay spokesperson dismissed the connection, yet the code disappeared from the ChronoPay home page shortly after that story ran. But sometime recently — perhaps in the last few days — it was apparently put back. You can see it by loading the home page of each site, right-clicking on the page and selecting “view source” or “view page source,” depending on your browser. Here’s a list of the other sites that also are using this Google Analytics code.




Happy Birthday Krebs I see your at the cutting edge again.
Payment processors have to tighten up their authentication security pronto. The thesis by that smart young researcher at Cambridge Uni shows that chip and pin is vulnerable and your article highlights the flaws with existing systems designed to shore up old style authentication don’t work despite the claims of the vendors. Authentication at every level is wrong so its not surprising that attackers can gain leverage from the weakest points as it appears to be in this case.
Authentication (and authorization, equally important) are one side of the issue. I suspect at the bottom of this rabbit hole investigation it will be revealed that DNS account was compromised due to password issues: harvested by malware, stolen by social-engineering, or guessed because it’s “st@rt123” or some such.
A human being should always be shoehorned into any business process where critical assets or info are being swapped between external parties. Whether it is changes to DNS or changes to Electronic Fund Transfer approvers (a problem well illustrated on this site), a human being serves as the best sanity check there is. A phone call to a pre-verified list contacts at Chronopay would quickly have verified whether DNS should be getting transferred or not.
Instead, 800 (presumably) innocent customers are taking unexpected deposits in the tailpipe.
Redeye/Pavel please respond to the Google Analytics-code re-appearing.. you connected the dots yet again for all of us
ohoh they have now so much cc’s they can sell it…
nice to see that pavel has some “friends” I hope the data stolen can be used to prove the criminal activity chronopay was set up for…
Well what do you know a site that is mixed up in some of the badness get’s a taste of their own medicine, well I would say that’s a shame but it seems like karma to me.
When do these guys mixed in the murky waters of payments for those that can’t get them done thru legitimate sources ever fess up that they may be on the worng side of the law… usually never… and of course they always want to downplay the damage done.
What and have their fellow crooks think their hard earned money they made scamming people is in jeopardy, no, no… Can’t have that now can we.
Is ChronoPay a predator info exchange or a legit site?
Good question. Based on a review of ChronoPay’s business clients and services, they appear to be something of a Jekyl and Hyde operation.
Here are some of their legit “white” clients:
retail (holodilnik.ru, dostavka.ru, kupiVIP.ru),
online games (Electonic Arts),
dating services (Mamba, Loveplanet),
Hosting (Masterhost),
Software (Kaspersky)
Media (Kommersant, Independent Media),
Downloadable content (mp3.ru, muz.ru)
Advertising (Begun),
Charity (WWF, Greenpeace, Unicef),
ticketing (afisha, kassir.ru),
forex (forex club, alpari, finam),
lotto (gosloto, rosloto),
utilities (Mosenergosbyt),
betting company(marathonbet, vabank)
They also specialize in providing processing for “high risk” merchants, including rogue AV vendors, online pharmacies, cigarette sales, “replica” sites, as well as hardcore/bestiality/rape porn sites.
Interesting that Kaspersky wouldn’t moved from that. Would really like to see WWF and UNICEF move away also. How long has that info been exposed?
Brian, check out redeye-blog.com. It is like wikileaks for all Pavel’s activities. Includes all accounting info(including bribes), corporate emails and call recordings. All data was gathered when their servers were hacked earlier this year.
Yes, thanks, CC. I am aware of it and reading it. I already have all of that information, anyhow.
As Randy Quaid said in “Independence Day,” payback’s a bitch. Brian, this sounds like a classic “man-in-the-middle” attack with some other shenanigans thrown in. Would DNSSEC deployment have mitigated this?
About me: http://bit.ly/fQZRHb
Probably not.
Once you control DNS you get to pick/use your own signature for your domain entries.
If the registrar required you to contact them using a key (asymmetric) you deployed with DNSSEC (perhaps SIPS), then in theory it could help, but it’s unlikely anyone uses something like this.
Russ in #comment-16406 is probably right about what happened.
Yesterday (18.01) Chronopay hack again
http://redeye-blog.com/news/bugagashechki-3ij-raz-vzlomali-chronopay-tochno-kontrolnyj.html
Here’s my experience.
I tried to book an airline ticket. For payment, they directed me to Chronopay. I tried 3 credit cards, all good, and all were declined.
My bank says they received no attempted transaction.
So I contact Chronopay support. They say they don’t know why, just that the payment was “declined by our automatic system” and they don’t know why – but they want me to send scans of my credit card and driver’s license so they can “help [me] to process the payment”.
Just how this will help them intervene in an online booking process is an interesting question…