In October 2010, I discovered that the authors of the SpyEye and ZeuS banking Trojans — once competitors in the market for botnet creation and management kits — were planning to kill further development of ZeuS and fuse the two malware families into one supertrojan. Initially, I heard some skepticism from folks in the security community about this. But three months later, security experts are starting to catch glimpses of this new hybrid Trojan in the wild, with the author(s) shipping a series of beta releases that include updated features on a nearly-daily basis.
It probably didn’t help that the first report of a blended version of SpyEye/ZeuS (referred to as SpyZeuS for the remainder of this post) — detailed in a McAfee blog post — turned out to be a scam. But a little more a week ago, Trend Micro spotted snapshots and details of SpyZeuS components, noting that the author appears to have received help from other criminals in polishing this latest release; in particular, an add-on that grabs credit card numbers from hacked PCs, and a plugin designed to attack the anti-Trojan tool Rapport from Trusteer. (Trusteer’s Amit Klein addresses this component in a blog post here).
Seculert, a new threat alert service started by former RSA fraud expert Aviv Raff, includes some screen shots of the administrative panel of SpyZeuS that show the author trying to appeal to users of both Trojans, by allowing customers to control and update their botnets using either the traditional ZeuS or SpyEye Web interface.
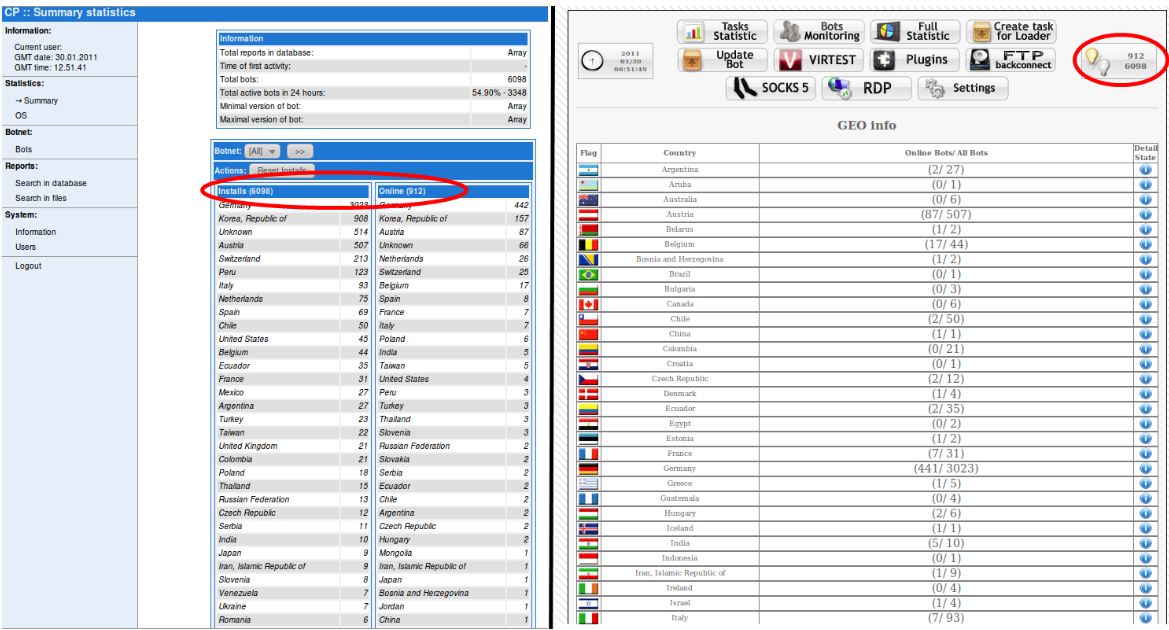
The hybrid SpyZeuS Trojan lets users interact with bots via the ZeuS control panel (left) or the SpyEye interface.
Raff said the author(s) has been adding new features to both the bot and the control panels nearly every day.
“This is under heavy development at the moment,” Raff said. “That’s why the version we wrote about was called 1.3.05 Beta, because it’s still not the [general availability] version. The author is still trying things out.”
The same day Raff’s post went up, a source forwarded me a link to a video posted to a popular hacker forum by a SpyZeuS customer who was using an even newer version, v. 1.3.09 Beta. The video (which the poster starts with a typo confusing ZeuS and SpyEye) shows how this user managed to hack the protection scheme built into SpyEye that is supposed to prevent buyers from making unauthorized copies of the crimeware package. Very shortly after posting that video, the user who recorded it had his forum account compromised and his personal and financial details posted online.
Update, 10:26 a.m.: Added response from Trusteer. Also, a previous version of this post incorrectly attributed a McAfee blog post to Trend Micro. The above text has been corrected.




The first report that ended up being a scam was on the McAfee blog, not Trend Micro.
Doh! That’s what I get for blogging so late in the evening/morning. Thanks. I’ve corrected the post, with an update noting the correction.
Also just added a link to a blog post from Trusteer that addresses the anti-Rapport element.
Thanks for that Trusteer link Brian; I’m very appreciative of that and all of your work!
Where is the trusteer blog post?
It’s linked in the last sentence of the second paragraph.
If you still can’t find it, here it is again: http://www.trusteer.com/blog/alleged-newmerged-spyeye-and-rapport
you got the video from osc ? <.<
Great write up and Zeus/Spyeye combo is definitely the killer threat! There are FBI and NACHA guidelines to help protect users from fraud. These guidelines recommend that a dedicated, single-purpose computing environment be used only for online banking. This may be something that your readers might be interested in pursuing to protect themselves now and in the future.
Брайан, не был бы ты так любезен снабжать свои тезисы ссылками на описываемые ресурсы?
Translation: Brian, will you not be so kind as to provide your points with links to the resources you describe?
(I hope no one clicks on Dislike just because the post isn’t in English, as I’ve seen in the past; perhaps the author just doesn’t write English well, although he obviously understands it)
В моём предложении первое слово – Брайан. Сие означает, обращение к конкретному человеку, которого не затрудняет общение на двух языках.
Тем более, предлагать столь несуразный перевод ещё большая бестактность, чем первая.
Alex, I’d rather not link to it in this blog, for several reasons. But you can find it by searching for the nickname used by the guy in the video, and also the forum opensc.
Брайан, найду я в любом случае, речь об удобстве. Линки в твоём блоге не индексируются, тем более. Хозяин барин, конечно, но было бы удобней отслеживать с линками.
То не славно, Алекс. Перевод плох, но он просто пробовал помочь.
Да понятно, что помочь. Но помогают когда знают, а тут не пойми что, а сбоку бантик.
He’s just saving us all the trouble of pasting it into Google Translate (which makes it sound even more clumsy). Other than seeing that it starts with “Брайан,” we don’t know whether it’s meant for everyone to read or not until we get it translated.
Although personally, I enjoy trying to figure out your posts for myself 😉
Он не сохранил, а потратил общее время на:
– неверный перевод
– чтение неверного перевода
– всё равно нужно идти на гугл и переводить
Yo , brain just wanted to tell you that your topic about the guy who hacked me was incorrect he did not hacked me , he just have bunch of emails that i used to register domains with it and he hack into one of them which the password was quite easy “123456” whe he access there he saw neteller account and wmz which i created newly ,
and he start posting that on forum by accesing to my account which password on forum was also “123456” ,
do you call this hack , and you talking about personal information , do i look for you like a 12 year old kid ?
he posted a blog of 12 year old kid do you think that was me ?
i guess you don’t even understand how he search .
my name is daniel wont make me “Danielbx1” or “Hamzabx1” am “bx1” only no addeding anything , and why he get angry because he asked me to the builder including the patch , which i refused , that’s he being kid thats why he is 10 year old kid
Hi Danny. Thanks for visiting. How come you didn’t reply to either my email or ICQ invite? I wanted to chat with you about this but only had the back-and-forth on the forums to go from.
Glad to hear you don’t think it’s serious. One question I’d have is, why would you use such lame passwords to begin with? Why not just pick one that isn’t so easy to guess? You also appear to have been using the same password on multiple forums, which is another security oops that gets a lot of people in trouble.
it wasnt a lame password , it was just the password that is easy for me to remember being on hacking or malware forum wont make any reason to have strong or weak password , well 12345 is my prefered numbers as i used to play poker , anyway i did not get any of ur email and ICQ invite , if u want to chat with me my just email me ur ICQ then i’ll add u , i guess u can see my email on your board
Bx1, you are such a liar. Of course I would not expect much else from a criminal like you. Your passwords are not 123456 like you claim and I have a lot more information on you than just what I posted on opensc.
http://www.sendspace.com/file/5y4d3r
What I can say is that if inkubus would have just given me what I wanted then none of this would have happened.
Yes Cybercriminal and i’m prov of what i’m , i can do what u cannot do , and i’m preparing something worse that Zeus and SpyEye , do what ever u like , because u don’t have any confirmed information about me 🙂
123456 IS a lame password, and being on a hacking forum is all the more reason to use a strong password.
Danny is right, the maker of SpyEye and now the coder of ZeusEye (SpyZeus) [These are not real names] behaves much like a kid. He is not the god coder many of those in the underground make him to be, in fact he is merely slightly above average in my opinion. We must look at people like the ZeusEye coder as criminal thugs, no longer the geniuses dwelling in their basements.
There’s no such thing like ZeusEye…omg…
Misinformation – a tactic employed by the military as well. Sow seeds of confusion in the camp of the enemy!
I wonder if Sun Tzu ever included that in his “Art of War”?
Nor is there a “SpyZeus”. I just use these terms interchangeably to refer to the combined version of zeus and spyeye. the name is just spyeye.
I like the way you put down the image of the criminals in that post. No matter who you are. or what terms you use, I will always give a big thumbs up to the criticism of web-crooks.
They, indeed, are not “gods” by any stretch of the imagination; although they may think it of themselves.