Underground hacker forums are full of complaints from users angry that a developer of some popular banking Trojan or bot program has stopped supporting his product, stranding buyers with buggy botnets. Now, the proprietors of a new ZeuS Trojan variant are marketing their malware as a social network that lets customers file bug reports, suggest and vote on new features in upcoming versions, and track trouble tickets that can be worked on by the developers and fellow users alike.
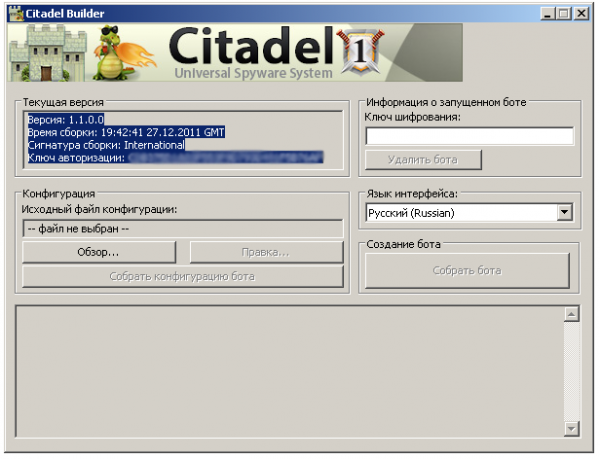
The ZeuS offshoot, dubbed Citadel and advertised on several members-only hacker forums, is another software-as-a-service malware development. Its target audience? Those frustrated with virus writers who decide that coding their next creation is more lucrative and interesting than supporting current clients.
“Its no secret that the products in our field — without support from the developers — result in a piece of junk on your hard drive. Therefore, the product should be improved according to the wishes of our customers,” Citadel’s developers claim in an online posting. “One problem is that you have probably experienced developers who ignore your instant messages, because there are many customers but there is only one developer.”
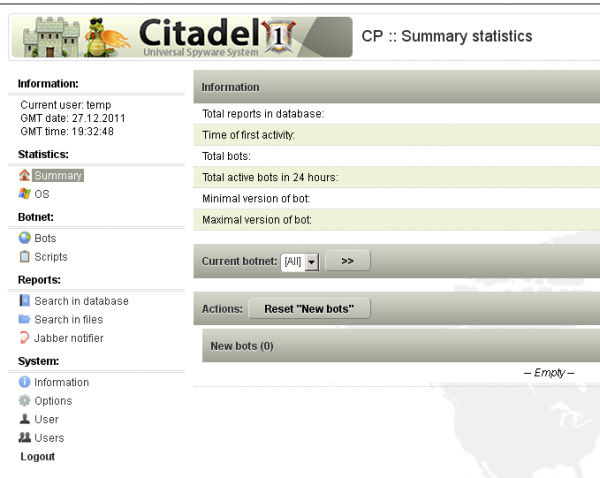
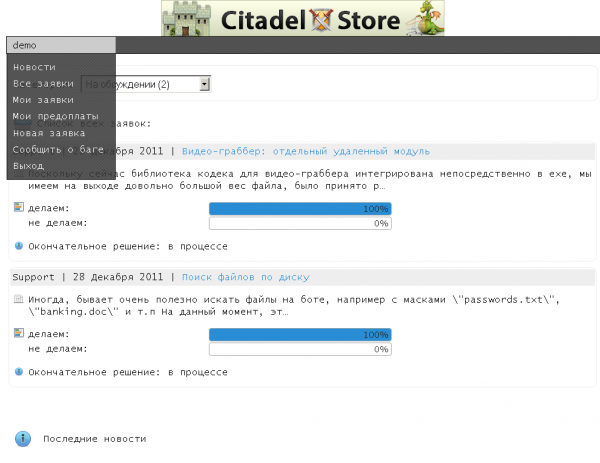
In the following excerpt, taken from a full description of Citadel’s innovations, the developers of this malware strain describe its defining feature as a social networking platform for malware users that is made available through a Web-based portal created by the malware itself.
“We have created for you a special system — call it the social network for our customers. Citadel CRM Store allows you to take part in product development in the following ways:
– Report bugs and other errors in software. All tickets are looked at by technical support you will receive a timely response to your questions. No more trying to reach the author via ICQ or Jabber.
-Each client has the right to create an unlimited number of applications within the system. Requests can contain suggestions on a new module or improvements of existing module. Such requests can be public or private.
-Each client has a right to vote on new ideas suggested by other members and offer his/her price for development of the enhancement/module. The decision is made by the developers on whether to go forward with certain enhancement or new module depending on the voting results.
-Each client has the right to comment on any application and talk to any member. Now it is going to be interesting for you to find partners and like-minded people and also to take active parts in discussions with the developers.
– You can see all stages of module development, if it is approved other members. We update the status and time to completion.
– You may pay a deposit, if module is approved (50%). After the deposit is paid by the members, the project starts moving forward, so that the money is paid directly to coders and there will be no laziness or inaction. Everything is clear: every stage of development is thoroughly shown.
-Easy jabber [instant message] notification of new member or developer comments, or the availability of new custom applications.
Citadel may be the first notable progeny of ZeuS since the ZeuS source code was leaked online last year. The authors claim that it includes a number of bug fixes for the most recent ZeuS version, including full support for grabbing credentials from victims using Google Chrome. Also bundled with this update is a component that can record and transmit videos of the victim’s screen activity.
The basic Citadel package — a bot builder and botnet administration panel — retails for $2,399 + a $125 monthly “rent,” but some of its most innovative features are sold as a la carte add-ons. Among those is a $395 software module that allows botmasters to sign up for a service which automatically updates the bot malware to evade the last antivirus signatures. The updates are deployed via a separate Jabber instant message bot, and each update costs an extra $15.
Citadel also boasts a feature that hints at its creator’s location(s). According to the authors, if the malware detects that the victim’s machine is using a Russian or Ukrainian keyboard, it will shut itself down. This feature is almost certainly a hedge to keep the developers out of trouble: Authorities in those regions are far less likely to pursue the Trojan’s creators if there are no local victims.
It will be interesting to see if these malware developers hold true to their word. The growth of a more real-time, user-driven and crowdsourced malicious software market would be a truly disturbing innovation. For now, the miscreants behind Citadel appear upbeat about their chances of ushering in such a reality.
“It’s very interesting for us to work with our clients,” they wrote in an online forum posting. “A lot of authors write in forums that they ‘support the product,’ but at the end the updates only come out once every three months or the author disappears forever. Problem is in author’s motivation. You support us, we support you. It is easy.”




It seems to me that the best way to combat this is for software writers (i.e. Adobe Reader/Flash/Shockwave/AIR and Oracle Java) need to make their updates more automatic with less user interaction (ala Google Chrome) They also need to up their time for the default check for updates – once a day at least instead of once per week or month.
On kind of a sidways note – has any one seen a recentl explination why the 64-bit version of Java for windows does not have an auto updater yet? I am seeing this installed more and more by OEMs and with no auto-updater since its release in late 2008 no auto-updater means that ther are alot of unsafe machines out there.
My problem with approach is that it makes the already ignorant user (which is most users) even more dependent on the major software vendors. I’m reminded of the old saying that the only thing it takes for evil to flourish is for good people to run to those in authority. In some ways I fear the omnipotent reach Google/Java more than I do these guys.
There has to be a better solution than an ever escalating arms race between various groups of brainiacs. At a certain point all the members of the intellectual oligarchy look alike.
Unfortunately most end users don’t know what to do when the update boxes for Flash/Java etc pop up so they tend to ignore them. The end result – horribly out of date software with easily exploitable vulnerabilities. The only other solution I see in the end is to start requiring a licence to use a computer (kind of like a driver’s licence) – like that’s going to happen any time soon.
CP means child porn
Someone break this down for me, please. We have developers that actively tout their latest and greatest malware versions, offer support, and charge one time and/or maintenance fees for the software and/or support.
It looks like this would require registering domains and setting up payment systems, which, with some effort, could be tied to a real, living and breathing human being with a birth certificate and a government-issued ID of some sort…not just a witty handle on a forum somewhere.
With the amount of Customer Identification Program (CIP) required by US banks (and I am assuming similar laws in foreign countries), the banks WILL have identifying information on these individuals, even if they are IDing them only as a signitory or beneficial owner on an account that’s receiving payments for the malware.
Or maybe I am ignorant and overly optimistic…?
Sadly it generally doesn’t work out that these guys can be easily caught by the methods you mention. They tend not to funnel their money directly through US banks for one thing. There are also cash services like Liberty Reserve or Web Money that make these type of transactions even more difficult to trace.
In addition there are also escrow services out there that these guys can use to ensure their transactions are safe.
And finally even if you do track one of these guys down, getting local law enforcement to prosecute can be extremely challenging. These guys tend not to operate in countries where law enforcement is on the ball with this stuff.
There is a whole slew of other challenges I’m glossing over, but hopefully that provides you a bit more insight into how these guys do that stuff.
I wonder what CIS means when they say :
“Our software does not work on Russian-language systems. If a Russian or Ukrainian layout is detected, the bot terminates.
This is done to prevent installs on CIS systems. You may disagree, but that’s taboo for us.”
??????