Adobe, Microsoft and Oracle today each issued security updates to fix serious vulnerabilities in their products. Adobe released patches for AIR, Acrobat, Flash and Reader, while Microsoft pushed out fixes to shore up at least a half dozen security weaknesses in Windows and Office. Oracle released an update for Java that fixes at least three dozen security holes in the widely-used program.
 All of the vulnerabilities that Microsoft fixed this month earned “important” ratings; not quite as dire as those labeled “critical,” which involve flaws so dangerous that they can be exploited by bad guys or malware to break into systems with no user interaction. Nevertheless, flaws marked “important” can be quite dangerous, particularly when used in tandem with other attack techniques.
All of the vulnerabilities that Microsoft fixed this month earned “important” ratings; not quite as dire as those labeled “critical,” which involve flaws so dangerous that they can be exploited by bad guys or malware to break into systems with no user interaction. Nevertheless, flaws marked “important” can be quite dangerous, particularly when used in tandem with other attack techniques.
By way of illustration, this month’s MS14-002 patch addresses an important zero-day flaw that was first found to be exploited in targeted attacks late last year. In one version of this attack, documented quite nicely in this fascinating yet somewhat technical writeup from Trustwave Spiderlabs, attackers used this Windows flaw in combination with a bug in Adobe Reader. According to Trustwave, the bad guys in that attack included the Windows flaw as a means of bypassing Adobe Reader’s security sandbox, a technology designed ensure that any malicious code embedded in documents only runs under limited privileges (i.e., isn’t allowed to invoke other programs or alter core system settings).
In short, don’t put off applying this month’s patches from Microsoft. They are available via Windows Update or Automatic Update. Also, Microsoft took this opportunity to remind Windows XP users that the company will no longer be supporting Windows XP after April 2014 (guess I will have to retire the above broken Windows graphic as well). The lack of ongoing security updates for XP means it will likely become an even bigger target for attackers; if you rely on XP, please consider transitioning to a newer operating system sometime soon. Who knows, it might be a great excuse to try Linux, which tends to be very light on resources and ideal for older hardware. If you’ve been considering the switch for a while, take a few distributions for a spin using one of dozens of flavors of Linux available via Live CD.
 Speaking of Adobe Reader, the company today released updates to fix at least three vulnerabilities in the widely-used program. Users of Adobe Reader XI (11.0.05) for Windows and Mac should update to Adobe Reader XI (11.0.06). Obligatory note: There are other options.
Speaking of Adobe Reader, the company today released updates to fix at least three vulnerabilities in the widely-used program. Users of Adobe Reader XI (11.0.05) for Windows and Mac should update to Adobe Reader XI (11.0.06). Obligatory note: There are other options.
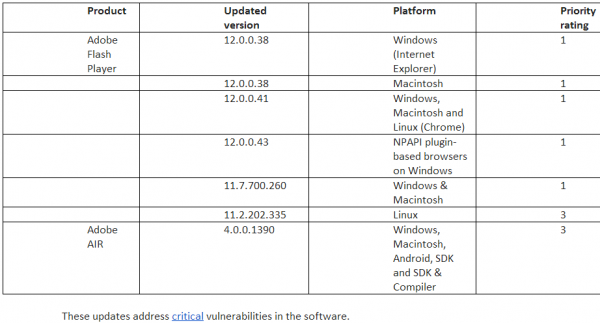
Adobe also pushed out patches for its Flash Player and AIR products. The Flash update brings the media player to version 12.0.0.38 on Windows and Mac OS X. This link will tell you which version of Flash your browser has installed. IE10 and Chrome should auto-update their versions of Flash. If your version of Chrome (on either Windows, Mac or Linux) is not yet updated to v. 12.0.0.41, you may just need to close and restart the browser.
The most recent versions of Flash are available from the Adobe download center, but beware potentially unwanted add-ons, like McAfee Security Scan). To avoid this, uncheck the pre-checked box before downloading, or grab your OS-specific Flash download from here. Windows users who browse the Web with anything other than Internet Explorer will need to apply this patch twice, once with IE and again using the alternative browser (Firefox, Opera, e.g.).
In addition, Adode AIR (required by some applications like Pandora Desktop, for example) was updated to v. 4.0.0.1390 for Windows, Mac and Android devices. Adobe AIR checks for and prompts you to install any available updates anytime you launch an application that uses AIR; in any case, the download link is here. See the chart below for the updated version numbers for your operating system.
Separately, Oracle issued its critical patch update, which includes some 36 security fixes for Java. This update brings Java to Java 7 Update 51, and is available via the built-in Java updater or from Java downloads.
If you really need and use Java for specific Web sites or applications, take a few minutes to update this software. Updates are available from Java.com or via the Java Control Panel. Keep in mind that updating via the control panel will auto-select the installation of the Ask Toolbar, so de-select that if you don’t want the added crapware.
Otherwise, seriously consider removing Java altogether. I’ve long urged end users to junk Java unless they have a specific use for it (this advice does not scale for businesses, which often have legacy and custom applications that rely on Java). This widely installed and powerful program is riddled with security holes, and is a top target of malware writers and miscreants.
If you have an affirmative use or need for Java, unplug it from the browser unless and until you’re at a site that requires it (or at least take advantage of click-to-play). Java 7 lets users disable Java content in web browsers through the Java Control Panel. Alternatively, consider a dual-browser approach, unplugging Java from the browser you use for everyday surfing, and leaving it plugged in to a second browser that you only use for sites that require Java.
There are a couple of ways to find out if you have Java installed and what version may be running. Windows users can click Start, then Run, then type “cmd” without the quotes. At the command prompt, type “java -version” (again, no quotes). Users also can visit Java.com and click the “Do I have Java?” link on the homepage. Updates also should be available via the Java Control Panel or from Java.com.
Update, 5:33 p.m. ET: Included information about Java patches.




Google Chrome is already getting updated to: 32.0.1700.76 m
so what your trying to say is the nsa has been exploiting these holes for 8 months?
Add Java to the list… 7.51
Yeah, thanks. I had that on my list but forgot to write about it. I just updated the post to include mention of the Java fixes.
Just a technical clarification for the article (though it’s very clear in the above table) — the AX (IE) version of Flash for Windows is updated to 12.0.0.38, but the plugin version used with other browsers is 12.0.0.43. Presumably at some point, the AX version will be updated again to conform with the plugin version.
I’m kinda surprised that the manual offline Java installer files for both 32-bit and 64-bit versions are *.com, rather than *.exe filenames — haven’t seen anyone use the .com extension for a major release in a long time.
And if you want the direct link to the manual download webpage for all OS flavors, it is:
https://www.java.com/en/download/manual.jsp
“Windows users who browse the Web with anything other than Internet Explorer will need to apply this patch twice, once with IE and again using the alternative browser (Firefox, Opera, e.g.).” Adobe Flash does have an automatic update option. In Windows 7, the status of the automatic update option can be seen in the Flash Player Settings Manager which can be accessed by going to Start, Control Panel, System and Security, Flash Player (32 bit), Advanced. Adobe documents the automatic update feature here: http://forums.adobe.com/message/4723788 . The last paragraph says: “Please note that major Flash Player releases will prompt the user with an update dialog, allowing them to read the key features new to the release. The user can choose to update immediately or the automatic update will silently install the update 30 days after release. ”
More information is available here: http://www.adobe.com/devnet/flashplayer/articles/background-updater-windows.html . “When Adobe releases new versions of Flash Player through the background update channel, Adobe Flash Player Background Updater automatically updates all instances of the release version of Adobe Flash Player for web browsers on any computer on which it is installed and enabled. ”
I have never relied on the auto update option so user comments are welcomed. Please remember to mention the browser and authority level, Admin or User.
Well, I tried hard to upgrade Google Chrome to 32.0.1700.76 m, but it wouldn’t upgrade itself. I had no choice but to uninstall Chrome and then reinstall it for the upgrade to work. What a pain!
Light month on the security patches including the flash update
As always, Brian, I want to thank you for keeping all of us alert and sharing so much important information with us!
Would you or anybody else possibly know how I can find out which version of Google Chrome is installed on my computer? I find it in Internet Explorer under HELP > ABOUT INTERNET EXPLORER but can’t find that setting in Google Chrome.
Look for the three stack bars icon directly to the right of the URL bar. Click that, and select “About Google Chrome.”
Thanks for your reply, Brian! Using your instructions, I found version 32.0.1700.76m listed under “About Google Chrome” but not 12.0.0.41, as you mentioned?
That version number (32.0.1700.76m) is a Google Chrome version number. Because you are running that version (which is the latest version of Chrome), you also have the newest version of Flash installed (12.0.0.41). But don’t take my word for it: I included a link in the story that you can click to find out which version of Flash you have installed.
Here it is again:
http://www.adobe.com/software/flash/about/
For those that have old XP boxes around and wonder if they can swap the OS out: Anything that is at least a socket 370 (1999 or so mainboard socket, and this is as old as you’ll want to go and have the system fast enough to use for a modern OS) will run Vista (but not Win8) or pretty much any flavor of Linux alright enough. For Win7, Win8 you just need a CPU with an SSE 2 instruction and a decent amount of ram, video card, etc. There are also Linux distros such as DSL or Tiny Core Linux and either of those run on systems as old as early 90s. So unless you’re just keeping an XP system around for the hell of it or for the nostalgic factor (I have a Windows 98 486 myself) there are still some ways of getting more out of your older hardware.
But the biggest worry to me are all the work places that still have XP systems, and said same places usually don’t even keep up with the Windows Updates anyway, so… As long as it turns on and it does want they want it to is about all some places care about.
I thought I knew every possible variation of command prompts ever invented. You just taught me one more, the java -update one.
It even works on OSX/bash. Who knew?
:-$> man java
Whoa!
Thanks for an excellent post, Brian. Right after the holidays, my pc caught a bug, despite my up to date internet security program and firewall. Suddenly I was plagued by constant unwanted audio audio playing in the background on my pc. My computer was literally turned into a radio, music, ads, and newscasts all day long. Worse, it was tripping the Windows DCOM application server process and shutting my entire computer down. Windows would allow changes to the process. I tried reloading the audio drivers. I tried 5-6 different, well-respected malware checking programs, including the Microsoft Security Malware Safety Scanner. The full MS scan took almost 3 hours, but nothing helped. Everyone said I was “clean,” but the music, ads, etc played on. I hired a “tech buddy” from my IS software provider, and he was totally unsuccessful in removing the problem. Searching posts found lots of people who had suffered this problem, and while people had lots of ideas, none that I tried moved this bugger an inch.
I was just about to give up when a couple of your posts gave me another clue about what might be wrong. In fact, the problem was the Adobe Flash Player vers. 11, later verified on other posts once I knew what to look for. The only place that was totally silent was the Adobe site. I dumped the flash player and it has been quiet ever since. In fact, it has been so peaceful this past week that I am hesitant to reload any Adobe Flash Players, but I work in an internet-based business and I may have to. Maybe I just got a dirty file download, but some posts think that it is an Adobe Flash vers 11 a program bug. Hopefully they have de-bugged and a clean download will work. I’ll be sure to use only your links here.
Thanks, Brian, as always for the really helpful update info and the link to http://www.livecdlist.com/
The Windows XP issue is beginning to feel like Y2K all over again…
The same crap, from the same crap companies.
I don’t use IE for any browsing. Do I even need Flash installed on it?
Doug – you don’t have to have Flash installed, but many websites do rely on it for viewing portions of their content, so depending on the sites you want to view, you may find it a necessary evil to have. You can always uninstall it and see how things look. If you find you need it, simply visit the Adobe.com website, click on their Downloads link, and then re-install it.
Thanks Brian really helpful article..
http://www.javatrainingchennai.co.in/
The list is quite long at the Live cd list; be careful of what you download from there, some programs may no longer be supported or updated. As for Linux, I didn’t check those links, I find those programs at another location.
I feel a trend about Java – To me its buggy, and there are alternatives to using it. Sencha for example can be used across many platforms, and as far as I know, it uses html5.
For the XP users, Windows 7 is probably as close as your going to get for an upgrade. I did move up to windows 8, and that was an awful experience. Win7 was an easy upgrade and though there may be some navigation differences, it isn’t earth shattering.
Could you help me further? I only use Java for playing a couple of word games on Yahoo. Since these recent patches, I am not able to get back into the games. I have tried everything I know to figure out what I need to do. When things are going well, Java only is activated while I play these games.
I get “Application Blocked by Security Settings’ but am unable to figure out what settings are blocking this. Any ideas? I would so appreciate it.
Thanks for your help and information about this matter.
I found this in Yahoo and it worked to enable Yahoo games. It is a copy and paste. Hope this is helpful for others.
Players have reported that the latest version of Java: Jave 7 (Update 51) is causing them to encounter an error that states the application has been blocked by security settings. These steps should correct the issue for most players:
For Windows: Go to Start and click on Settings, then Control Panel Locate Java and launch it, go to the Security tab and change the vertical slider to Medium. This should fix the issue for most browsers.
Some players (likely those using Firefox) may need to take one more action for games to begin working for them again. From the Firefox browser click Tools, then Options. Select Security then click the top Exceptions button. For the address of the website type *.yahoo.com and click Allow.
IMPORTANT NOTE:This Known Issue post is for Yahoo! staff to communicate current known issues to benefit Yahoo! customers. We do not gain extra Answers points for questions added to this “Known Issues” category.
Additional Details
For Mac: Click on System Preferences. In the Other section, click on Java. Click the Security tab and and change the vertical slider to Medium. This should fix the issue for most browsers.
3 mins ago
Thanks for the Mac fix… that worked! My MIL will be very happy she can play bridge again!
That is NOT the safest way to deal with it. You basically just circumvented (globally) the security settings. A better approach is (not the best either) to add the affected site to the exclusion list and leave the security @ high…
Java is only dangerous when You enable it in a web browser, there is no need to uninstall it completely.
Yes, absolutely.
If Java for stand-alone programs has a bug, it simply makes the stand-alone programs as hazardous as programs developed in most other languages/frameworks. Either you trust the provider of the stand-alone application, or don’t install and run his programs on your computer. The fact that they are written in Java should have no effect on your decision here.
If Java *running in the browser* has a bug, it has the potential to make the *browser itself* hazardous – which has happened repeatedly. A browser plus a Java applet plus a bug means that the provider of your browser is no longer just Microsoft or Mozilla or Apple or Google – it’s them plus whoever wrote the applet.
In the past, browsers and Java itself were often set up “connected” by default. So simply having Java on your system meant you were allowing applets to run unless you took steps to block them. In the face of repeated bugs, the default has now generally been reversed: Even if you install Java, your browser won’t accept applets unless you tell it to. And, in general – you should not do so.
— Jerry
Why is it that Oracle now requires a users to login to view Java security patches? I went ahead and created an account and now it is asking for a “Support Identifier”. It seems irresponsible for Oracle to require a contract for you to even view what vulnerabilities are in their software. Does anyone know another method for accessing this data?
Ignore me. I have now noticed if you scroll down far enough there is a list of all the CVE identifiers.
My pc updated at 3 am cst turned it on this morning and it was like my pc was restored to factory condition. I can find my files but my desktop is empty except for recycle bin, and internet explorer has deleted all my favorites..
Have you checked whether any of the older (pre-3am) restore points are still available, and initiated a restore action from one prior to when that automatic update occurred? If there are no older restore points available or there is one but it doesn’t bring back your desktop and other customized functions, then you may be able to find some more information and/or advice to debug the issue(s) through the MS TechNet support webpages:
http://technet.microsoft.com/ms772425
Good luck!
Well since Windows XP lacks the improved security of Vista/Win7/Win 8 there is going to be an increased use of EMET after the end of support:
http://technet.microsoft.com/en-us/security/jj653751
Microsoft doing some backsliding. Security Essentials, Forefront to be updated on XP until 2015-07-14. Could understand doing so for Forefront on Custom Support site but consumer MSE should be clearly (in a way that is inconvenient to ignore) marked for the user as out of service.
Per “Microsoft antimalware support for Windows XP” on Microsoft’s Malware Protection Center blog.
a technology designed *to* ensure that
Your latest post on Target, http://krebsonsecurity.com/2014/01/a-first-look-at-the-target-intrusion-malware/, 404’s.
my games supported by java dont load, it says something to do with toplists, who can help? appreciated
Hi,
I use fulfilled by Amazon and in order to print bar codes Amazon uses a Java applet.
Since upgrading to 7 update 51, every time I try to print a barcode I get redirected to the Oracle site or receive a message: unable to upload java printer applet please ensure that you have a printer installed or version 1.6 or above.
I have contacted Amazon for the last few days and they say since 14 Jan 2014 this has become a Global problem. Their tech guys after 4 days came up with: Try the security slider at high and see if this cures the problem. As this is the default setting it was of course useless information.
Please has anybody got know how to fix the problem. I have not been able to work for 4 days now and with very little coming from Amazon I am getting very worried about my future finances.
Thanks
Take a look at the following FAQ posted on the Java support website to see if it will prove helpful in resolving your problem.
https://www.java.com/en/download/help/java_blocked.xml
I wood like to upgrade my flash player
What’s preventing you from doing so?
The new version of Java has blocked me from playing yahoo games. I have tried everything they told me to do in order to play again, i.e. move security to medium and list the http address in java to allow access but I still cannot get in. Very frustrating.
I downloaded the update windows x 86 jdk-7u51-windows-i586.exe. This is 32 bit as I have found out that Firefox and Chrome work on 32 bit.
Although Windows 7 is 64 bit, you have to download this version.
On the Java Control Panel (on the start menu in Windows 7)
On the security tab
security to high
Tick the box Enable Java content in browser
Add the Yahoo address to the exception list. It may be /games or something I don’t know. This is a fix I used to print Amazon labels where I put https://sellercentral.amazon.co.uk in the exception list.
On the advanced tab
Uncheck the box “Enable the next generation Java plug-in (requires browser restart)”
Hope this works for you. it took me 4 days to find this work around.
JRE 7u51 refuses to run older self-signed apps, may of which are critical such as KVMoIP remote management for servers. Oracle provided no simple way to override this behavior, though it appears that if one is willing to spend a few days crafting a special permissions JRE it can be accomplished.
I for one have put back 7u45 (one has to erase every trace of Java including user-local files or the behavior sticks) and have no plans to update. Bad move by Oracle.