Many companies believe that if they protect their intellectual property and customers’ information, they’ve done a decent job of safeguarding their crown jewels from attackers. But in an increasingly common scheme, cybercriminals are targeting the Human Resources departments at compromised organizations and rapidly filing fraudulent federal tax returns on all employees.
Last month, KrebsOnSecurity encountered a Web-based control panel that an organized criminal gang has been using to track bogus tax returns filed on behalf of employees at hacked companies whose HR departments had been relieved of W2 forms for all employees.
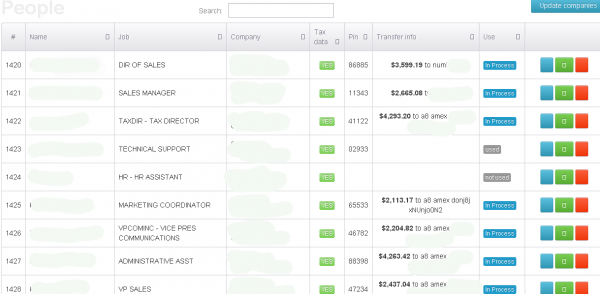
An obfuscated look at the he control panel for a tax fraud operation involving more than a half dozen victim organizations.
According to the control panel seen by this reporter, the scammers in charge of this scheme have hacked more than a half-dozen U.S. companies, filing fake tax returns on nearly every employee. At last count, this particular scam appears to stretch back to the beginning of this year’s tax filing season, and includes fraudulent returns filed on behalf of thousands of people — totaling more than $1 million in bogus returns.
The control panel includes a menu listing every employee’s W2 form, including all data needed to successfully file a return, such as the employee’s Social Security number, address, wages and employer identification number. Each fake return was apparently filed using the e-filing service provided by H&R Block, a major tax preparation and filing company. H&R Block did not return calls seeking comment for this story.
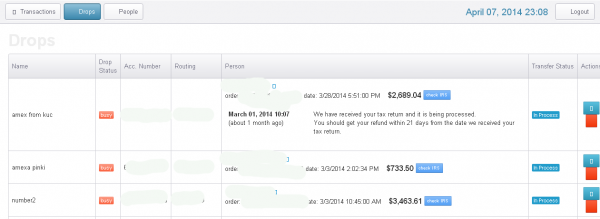
The “drops” page of this tax fraud operation lists the nicknames of the co-conspirators who agreed to “cash out” funds on the prepaid cards generated by the bogus returns — minus a small commission.
Fraudulent returns listed in the miscreants’ control panel that were successfully filed produced a specific five-digit tax filing Personal Identification Number (PIN) apparently generated by H&R Block’s online filing system. An examination of the panel suggests that successfully-filed returns are routed to prepaid American Express cards that are requested to be sent to addresses in the United States corresponding to specific “drops,” or co-conspirators in the scheme who have agreed to receive the prepaid cards and “cash out” the balance — minus their fee for processing the bogus returns.
Alex Holden, chief information security officer at Hold Security, said although tax fraud is nothing new, automating the exploitation of human resource systems for mass tax fraud is an innovation.
“The depth of this specific operation permits them to act as a malicious middle-man and tax preparation company to be an unwitting ‘underwriter’ of this crime,” Holden said. “And the victims maybe exploited not only for 2013 tax year but also down the road, and perhaps subject of higher scrutiny by IRS — not to mention potential financial losses. Companies should look at their human resource infrastructure to ensure that payroll, taxes, financial, medical, and other benefits are afforded the same level of protection as their other mission-critical assets.”
ULTIPRO USERS TARGETED
I spoke at length with Doug, a 45-year-old tax fraud victim at a company that was listed in the attacker’s control panel. Doug agreed to talk about his experience if I omitted his last name and his employer’s name from this story. Doug confirmed that the information in the attacker’s tax fraud panel was his and mostly correct, but he said he didn’t recognize the Gmail address used to fraudulently submit his taxes at H&R Block.
Doug said his employer recently sent out a company-wide email stating there had been a security breach at a cloud provider that was subcontracted to handle the company’s employee benefits and payroll systems.
“Our company sent out a blanket email saying there had been a security breach that included employee names, addresses, Social Security numbers, and other information, and that they were going to pay for a free year’s worth of credit monitoring,” Doug said.
Almost a week after that notification, the company sent out a second notice stating that the breach extended to the personal information of all spouses and children of its employees.
“We were later notified that the breach was much deeper than originally suspected, which included all of our beneficiaries, their personal information, my life insurance policy, 401-K stuff, and our taxes,” Doug said. “My sister-in-law is an accountant, so I raced to her and asked her to help us file our taxes immediately. She pushed them through quickly but the IRS came back and said someone had already filed our taxes a few days before us.”
Doug has since spent many hours filling out countless forms with a variety of organizations, including the Federal Trade Commission, the FBI, the local police department, and of course the Internal Revenue Service.
Doug’s company and another victim at a separate company whose employees were all listed as recent tax fraud victims in the attacker’s online control panel both said their employers’ third-party cloud provider of payroll services was Weston, Fla.-based Ultimate Software. In each case, the attackers appear to have stolen the credentials of the victim organization’s human resources manager, credentials that were used to manage employee payroll and benefits at Ultipro, an online HR and payroll solutions provider.
Jody Kaminsky, senior vice president of marketing at Ultimate Software, said the company has no indication of a compromise of Ultimate’s security. Instead, she said Doug’s employer appears to have had its credentials stolen and abused by this fraud operation.
“Although we are aware that several customers’ employees were victims of tax fraud, we have no reason to believe this unauthorized access was the result of a compromise of our own security,” Kaminsky said. “Rather, our investigation suggests this is the result of stolen login information on the end-user level and not our application.”
Kaminsky continued:
“Unfortunately incidents of tax fraud this tax season across the U.S. are increasing and do not appear to be limited to just our customers or any one company (as I’m sure you’re well aware due to your close coverage of this issue). Over the past several weeks, we have communicated multiple times with our customers about recent threats of tax fraud and identity theft schemes.”
“We believe through schemes such as phishing or malware on end-user computers, criminals are attempting to obtain system login information and use those logins to access employee data for tax fraud purposes. We take identity theft schemes extremely seriously. As tax season progresses, we have been encouraging our customers to take steps to protect their systems such as enforcing frequent password resets and ensuring employee computers’ are up-to-date on anti-malware protection.”
PROTECT YOURSELF FROM TAX FRAUD
According to a 2013 report from the Treasury Inspector General’s office, the U.S. Internal Revenue Service (IRS) issued nearly $4 billion in bogus tax refunds in 2012. The money largely was sent to people who stole Social Security numbers and other information on U.S. citizens, and then filed fraudulent tax returns on those individuals claiming a large refund but at a different address.
It’s important to note that fraudsters engaged in this type of crime are in no way singling out H&R Block or Ultipro. Cybercrooks in charge of large collections of hacked computers can just as easily siphon usernames and passwords — as well as incomplete returns — from taxpayers who are preparing returns via other online filing services, including TurboTax and TaxSlayer.
If you become the victim of identity theft outside of the tax system or believe you may be at risk due to a lost/stolen purse or wallet, questionable credit card activity or credit report, etc., you are encouraged to contact the IRS at the Identity Protection Specialized Unit, toll-free at 1-800-908-4490 so that the IRS can take steps to further secure your account.
That process is likely to involve the use of taxpayer-specific PINs for people that have had issues with identity theft. If approved, the PIN is required on any tax return filed for that consumer before a return can be accepted. To start the process of applying for a tax return PIN from the IRS, check out the steps at this link. You will almost certainly need to file an IRS form 14039 (PDF), and provide scanned or photocopied records, such a drivers license or passport.
The most frightening aspect of this tax crimeware panel is that its designers appear to have licensed it for resale. It’s not clear how much this particular automated fraud machine costs, but sources in the financial industry tell this reporter that this same Web interface has been implicated in multiple tax return scams targeting dozens of companies in this year’s tax-filing season.




If I’ve been filing electronically with a PIN in past years, can they file at H&R Block without it?
It seems to me that the IRS could be just a little smarter than they are. If I have filed tax returns previously using a given address, and a new return comes in with a different address, either I moved or it’s a scammer filing the return. Maybe they should delay refunds for returns with different addresses, or at least send an inquiry to the original address to see if there has been a move. Certainly won’t stop all improper refunds, but a little common sense might go a long way.
That’s not a bad idea, but it doesn’t necessarily scale. Works well if you are processing a few dozen or hundred returns. Not so well when you are processing hundreds of millions of returns, where tens or hundreds of thousands of people move every year, equipped with inadequate staffing and facing a hostile congress looking for any excuse to start hearings on how bureaucratic and taxpayer unfriendly you are. (50,000 people got late refunds because they IRS thought it was suspicious that they moved!)
We need to rethink the whole concept of identity in this country. Going to be difficult or impossible to do so, considering the backlash we get whenever anybody mentions the concept of a federal id card.
How well does “rethinking the whole concept of identity in this country” scale?
Challenging, to be sure. We’ve gotten pretty good at making sure everybody gets a birth certificate and social security number. Maybe they could be assigned a public/private key pair when they are 18 or 21. Many more logistics to be worked out, but something along those lines.
+1
In a perfect world the IRS would make improvements but ‘inadequate staffing’ a ‘hostile congress’ & investigations for “controversies” initiated by the party investigating them we’re lucky we get our refunds at all
We already of federal IDs it’s called a social security number. Adding another sequence of numbers to your name will not fix the identity theft problem.
Agree. Assymetric encryption should be part of this strategy.
I like the common sense idea.
Maybe the IRS just shouldn’t issue refunds until, say, April 30 and any conflicting (double/triple) returns get delayed until the issue is resolved for them. This would solve most of the problems.
Frightening prospect with all this as your/families ID is owned indefinately thereafter.
That could be a solution
The H&R Block PIN and the IRS PIN are separate things, correct?
So is IRS policy to automatically tell anyone whose SSN has already filed taxes that a return was already received and processed? That’s what happened to Doug; I hope it happens to all victims so they will at least know.
The IRS seems to be its own worst enemy in trying to prevent tax refund fraud. Use of a PIN could be a very effective counter measure, yet it appears the IRS won’t issue a PIN until after you’ve already become a victim. A taxpayer ought to be able to obtain a PIN simply by asking for one, saving both himself and the IRS a lot of problems and money.
> Use of a PIN could be a very effective counter measure
What about compromised end users who lose their PIN to the bad guys? The bad guys can just continue to file using this PIN.
The only solution may be to delay refunds for those taxpayers whose information has changed (Email, mailing address, etc).
“> >Use of a PIN could be a very effective counter measure
>
>What about compromised end users who lose their PIN to the bad guys? The bad >guys can just continue to file using this PIN.”
That’s a preferable alternative because that doesn’t scale. If you lose YOUR PIN that doesn’t affect ME, whereas if I worked at that anonymous company it would have.
Years ago, when e-filing was new, the IRS sent a postcard with a PIN that was required to complete the e-file. Now, you make up a PIN and that is considered your “signature.”
Whiskey
Tango
Foxtrot
??????????????
Go back to mailing a postcard every year, it would be a hell of a lot cheaper than the $4B they paid in fraudulent returns last year.
If the IRS hands out PINs willy-nilly, the bad guys will just ask for PINs and then use them. Getting a PIN must be onerous in some way, or else it won’t do the job it is intended to do.
If we step back a bit, maybe letting the IRS do rebates wasn’t the smartest idea. Criminals wouldn’t pursue this, if the IRS wasn’t handing out money.
Oh, but the rebates were an excellent idea – for the US government. This way they get to collect and keep all that money, interest free, and just return the excess once a year. It doesn’t come out of their pocket if the wrong person gets the rebate.
Think a little more broadly than just that they keep the money. It would have to integrate with your Personnel office, but there can be a lessened collection instead of a direct refund/rebate. The problem that this creates is that then the refunded money, which is money from, say, 2013, would be counted as income in 2014 if not accounted correctly. If accounted correctly, then it would not be considered “W-2” income (taxable) or whatever your personnel office calls it. There may be other ways of refunding through employers instead of directly to people, even as a distribution separate from paychecks at the employer level, rather than altering the next paycheck. I’m sure there are other possibilities.
Reading all this bad news makes me glad I filed the same weekend that all my forms were available, at the start of February. If my ID has been stolen already, at least I beat the crooks to the filing office!
Berend, I think you’re right. There are several ways to attack the problem, perhaps the simplest and most efficient is to make it difficult if not impossible for the thieves to get the refund money. Deposit into a bank account or a check mailed to the address on the W-2, no exceptions, and require a valid picture ID to cash the check. Not perfect, but it creates more complexity and more tracking.
Or just delay all payouts till April 30 or so and delay any “double/triple” files until their ownership issues get resolved – problem solved.
“minus their fee for processing the bogus returns” – Is this a fixed amount or a percentage?
The software requires the user to identify the prior years adjusted gross income. The other option is to request a pin, however it would seem best to stick with actual tax filing information from the prior year as I did not see anything that would have kept a bogus filer from getting a pin number just by requesting it.
“Doug said his employer recently sent out a company-wide email stating there had been a security breach at a cloud provider that was subcontracted to handle the company’s employee benefits and payroll systems.” Sounds like a vote for keeping data in house. Let the argument begin.
Another real interesting article.
I like the response “we have no reason to believe this unauthorized access was the result of a compromise of our own security,Kaminsky said. Rather, our investigation suggests this is the result of stolen login information on the end-user level and not our application.”
Once Again ,it’s always blame it on someone else instead of taking full responsibility for the security breach.
+1
C’mon now… the HR users credentials were stolen. How is that the fault of ANY online service provider? User shows up, provides login, gets in. That’s the design.
However, if you track the topic you can see plenty of businesses are trying to sue banks saying basically “the bank should not trust anyone with my username and password because it may not be me”. They almost always lose in court, unless they show the bank was informed or somehow specifically negligent.
Doug could try suing his employer for using a cloud provider for such a service that did not require two-factor authentication- on the basis that such a decision is in fact negligent (i.e. criminally stupid). It won’t work (yet) but I sympathize with that view.
It would be interesting to know if UltiPro offers any additional security. If they do, then it truly isn’t their fault because it would be up to each company to utilize it.
I always end up having to send in huge checks to the IRS because of the AMT. So yay for me, I guess.
Or not. Just because you’re not due for a refund, doesn’t mean that they can’t claim one for you. Make up some bogus tax write-offs, and they’re all set. Now you have to deal with an audit while you try to claim it wasn’t you at all.
Right, Bruce. Jim Dandy, how nice of you to donate $1 million to the Kardashian family charity.
Couldn’t you mitigate a lot of this risk by adjusting your witholding?
Perhaps you should adjust so that you underwithhold to the max allowed by the IRS.
You could adjust withholding, but the criminals could claim they now are blind and disabled, have adopted 6 children (using stolen SS #’s) and spent half their salary on dental and medical care, while giving the rest to charity.
Your comment is a reason to deliberately underwithhold. If you always have to pay then you’ll never be screwed out of your refund. It doesn’t help with all of the work you have to do to correct the mess, but at least you won’t be even more upset because you were expecting $$ and were screwed out of it. I accidentally underwithheld last year and now I think I’m going to do it this year and all subsequent years.
Interestingly Ultimate Software claims that it was not an issue on their end but with the HR of the companies doing business with them.
On one end, I’m not a fan of just passing the buck like that but on the other hand I’ve seen some of the stuff HR and Purchasing departments do where I work and I’m shocked we haven’t been breached due to end user stupidity
I think I have a symptom of this kind of scam. I got a series of messages addressed to “Blanca Ramirez” from Intuit / TurboTax – indicating…
o welcome message
o indication that the returns were electronically filed (Fed & CA)
o the California one was accepted
o the Federal one was rejected (incorrect data of birth & either incorrect $$ or PIN)
It looks to me they just pick random email addresses to spam people with. (plus TurboTax doesn’t verify email addresses – a pet peeve for me)
I reported all of this to Intuit – not sure what they will do about it. I am not even sure they acted on my request to get my email address out of their system, but I haven’t gotten any further messages about it for a couple weeks now.
Unless someone has more information, I’m inclined to believe Kaminsky at Ultimate Software. They do business with hundreds of companies, and we have only found evidence of breaches at two definite, up to 6 possible (since this article doesn’t identify where the other companies on the list do their payroll).
Maybe I’m not reading the info correctly, but my understanding is that there are at least 6 affected companies, it’s been verified that 2 of them use UltiPro, and we know nothing yet about the others. They might be using UltiPro too. Kaminsky said that UltiPro’s security wasn’t compromised, and that seems to be correct. The thefts appear to have been done with valid user IDs and passwords. Is there any way that UltiPro can determine whether or not any of the other companies who use them were affected? Mass downloads of W-2 data all within a day or two? All going to IP addresses different than the ones typically used for logging in? If I were Kaminsky I wouldn’t just wipe my hands clean, I’d try to help.
Whether the breach was at Ultimate or not it would behoove them to take a second look at their security protocols. Better to respond to a wake up call than the aftermath of a security breach that could have been prevented
I went to the IRS site. Unfortunately, you can’t simply request a PIN for filing your taxes. You must have already been the victim of identity theft or have had some incident which increases your risk of being the victim. So the only way I get this extra layer of protection is to for to already be too late to stop the theft.
Seriously? Great going, IRS. Glad to see that my tax dollars are at work, not to protect me, but to lessen your workload. They need to remove that limitation, and think about the people they “serve” rather than just themselves.
“is to for” -> “is for it”
Who in their right mind would send a rebate card to any name or address other than the one on the return?
Is it H&R Block or the IRS or both? As far as I know, the IRS does not offer rebates in this manner, so apparently this is HRB’s doing.
If so, HRB cares only about making money, rather than the security of their customers. If I’ve put this together correctly and this really is how the scam works, HRB deserves to be sued out of existence.
I advise against anyone jumping to conclusions if they don’t know how IRS refund process works. The IRS transmits/deposits the returns electronically to an account or sends a paper check directly from the Treasury Dept. to the address on the current (bogus) return. There are no “rebate cards” sent to an address.
The reference above is that the accounts used to receive electronic refunds are in fact portable/pre-paid Amex cards (i.e. not easily traced) and not physical bank locations. Anything with a Bank Routing deposit number is accepted, which is arguably a flaw in IRS procedure.
HRB only transmits the return info, they have no fiduciary responsibility to validate the person using the computer is who they say they are. Nobody in that business requires such measures. Do you recommend ID checks in person?, etc. Note the description in the article of the burden of proving your identity to the IRS to get an person PIN. HRB should do that for every person every year?
It’s a flaw in the whole tax process design. According to the HRB Tax program, unless you have an IRS PIN, the IRS accepts your return if you provide last year’s AGI value. This is sort of a short validation. That should require looking at last years 1040 form or importing the data from last years data file. Your employer doesn’t know it. What I don’t see is reference to why this isn’t working- but again this seems to be a problem for the IRS.
So saying HRB has acted criminally and deserves to be sued out of business is simplistic and borderline defamatory. No, I don’t work there or know anyone who does. I just have to advise against jumping to wrong conclusions.
Great post.
Good post! If the return is mailed in, no validation is required. If they are filing online, perhaps they they are using the salary information as the AGI value to validate the return. For any taxpayer who only has one source of income and has not had a raise, their salary would be the same as their previous year’s AGI.
“What I don’t see is reference to why this isn’t working- but again this seems to be a problem for the IRS.”
This!
So does this mean the IRS is not validating this? Or doe sit simply means, this fraud only work for people who are simple 1040 + standard deduction filers?
If so, the breach could simply mean they also have access to the W2 from the previous year. If a person has no other income (or did not report for whatever reason) or deductions it is pretty simple to derive last years AGI from last years W2.
Actually I found the answer.
1) You can call the IRS to get your last years AGI. You just need your address, birthday and SSN. The thief already has those.
2) If you don’t have those, you can also request an e-file from the IRS website. This can be used instead of using the last years AGI.
This does make it more complicated. There are always honest users who forgot their AGI and lost their paperwork. Also people do move. How to handle that and stay safe is a classical conflicting priorities issue.
I asked some co-workers from Europe how this is done in European counties where they have mandatory PIN/TIN codes, and there they send either the PIN to the last known address, which handles almost all honest cases. A thief would be able to request a PIN, but it would be send to the actual person and not the thief.
Oh, and you now what, this is exactly the schema that the IRS already has in place for their payments PIN. It seems they do send you a PIN to the old address when you request that without option for a thief to send to a new/false one. So I’m flabbergasted why we don’t do this in general.
So only in case you have moved and lost the PIN in the same year, you’d run into issues. Then you’d have to manually request a new one with sending in extra identifications like passport. Not fool proof, as those can be faked, but a heavy burden compared to the easy ploys today.
I’m starting to believe we are hopelessly outdated in America when it comes to this simple protection.
Jack, why do you think the thieves used HRB exclusively? Is it possible that there is something exceptionally insecure about HRB’s e-filing that makes them more attractive to fraudulent filers? Are they the only prepare that offers refunds on debit cards? Are they the quickest to issue refunds? I wouldn’t accuse them of acting criminally, but I think some of their practices make it easy for fraud to occur.
Brian – thanks for this story. It’s fantastic.
My question (for anyone who can answer) is thus:
Since we can expect to see increasing amounts of this form of tax fraud going forward, does it make sense to adjust the W4’s so that no tax money is held out during the year, then set it aside in a personal account with the purpose of making the tax payment at time of filing?
If the tax return shows that the payor owes money then are the thieves more likely to move on to the next record in order to get the return, or is it moot either way?
thanks
A) not making regular tax payments during the year means you’ll be hit with IRS penalties
B) It doesn’t matter. The crooks are filling out fake returns and are hoping the IRS accepts the return. At worst for them, it gets just gets rejected. For you though, expect audits and lost time fixing the issue, even if they didn’t get your money.
Mary, you need to withhold to the minimum set by the IRS. Here’s some info from their web site: “Generally, most taxpayers will avoid this penalty if they owe less than $1,000 in tax after subtracting their withholdings and credits, or if they paid at least 90% of the tax for the current year, or 100% of the tax shown on the return for the prior year, whichever is smaller.”
In my opinion it does make sense withhold so that you are guaranteed no refund. This way if you are a victim of a fraudulent return, at least you won’t be screwed out of the refund you were expecting. I underwithheld accidentally last year and will do so deliberately from now on. I’ll aim for the middle of the IRS’s safe range.
What a treasure trove of “public info” I found here just waiting to be exploited: http://www.softwareadvice.com/hr/ultipro-profile/#reviews
79 reviews of Ultipro made by the HR person(s) who uses it, followed by the name of the company they work for, and how many employees that company has. Of course these reviewers are given the oh-so convenient option to sign in using their “trusty” old Twitter, Linkedin, Google+, or Facebook profiles–which we all know very likely uses the exact same username:password combo used to access Ultipro…
For example, we can learn that one “Luis Johannes” from “Laureate Education” gives it 5/5 stars on all 4 parameters:
“Laureate, our worldwide network of higher education institutions, uses UltiPro as our main HR Global System. We are using UltiPro in order to process US and International division payrolls, and to consolidate employee information for each school in Laureate.
Laureate includes more than 72 institutions of higher education in 30 countries, and we use the Payroll, Time and Attendance modules, and more. UltiPro has been user-friendly and ready to use on any new acquisition in Laureate. It also helps to deliver and connect with other internal systems in each institution.
Now our HR workforce can go online anywhere (SaaS) and see employee information, using Cognos solutions. Today, we are also implementing HR Dashboard, which has been a major success in terms of consolidation and effort. The benefits of UltiPro’s enhanced reporting are excellent.”
The rest of the sales pitch should go something like this:
“Laureate’s HR workforce can go online anywhere and see employee information…AND so can you…all you need to do is obtain their LinkedIn user:pswd (insert hyperlink to Paste Bin here)!
BC, what a find! I’m sure the thieves would love to know what other companies they might be able to steal data from. This is scary.
I see that Ultimate itself offers up lots of customer info through their “Connections Conference 2014” itinerary which has a column showing “Guest Presenter(s)” with complete first and last names and companies where the people work. I hope they all have strong passwords.
Wow nice catch BC, it’s a wonder that more innocent victims aren’t losing money. You can always count on marketing to make life easier for people who misuse information.
Relax fellas, after all they got a FREE YEAR of credit monitoring.
With all the fraud, and breaches, and security lapses in this day and age – is there ANYONE who doesn’t have ongoing credit monitoring, paid for by a myriad of companies who’ve lost their data?
I would not blame the IRS. They are short staffed by budget cuts, resources have been withheld by congress to upgrade security. If you want the blame anyone just look at all the companies that don’t pay taxes and hide their money overseas. What about the rich that only pay 15% while I pay 30%. Before anyone runs to the defense of the rich, don’t because this is math and not politics. I say if you want your freedoms in the US pony up and pay your fair share, if not get out and move to Yemen, Russia, Syria, China. I am sure these places have freedoms and fun resort towns.
Wishful thinking but I think we’re already past the point of no return… The empire is crumbling, our roads are turning to gravel and our critical engines of innovation and growth long since starved of fuel. Big money has already fled the country and built mansions on the other continents and could care less about the place that let it all happen and those still trying to find their way.
Here’s hoping this won’t devolve into a political discussion.
Another thought…
Time to bring back fat clients for software. No more allowing access to important systems via a browser.
Buh-Bye cloud. Time to write it off as an interesting, but failed experiment.
Haha… sure, and bring back the horse and buggy to resolve DUI deaths on the roadways.
Cloud, browsers, and automated online transactional systems are all here to stay. Cloud is really just the old time-sharing approach, meaning you rent time and storage on other peoples systems. It’s cheaper, which to those short-sighted MBAs means *everything* and consumer views on security will inevitably get the short end of the stick. Also inevitably, consumers go cheap. That is only rarely the horse to bet against.
One example: Look at mag-stripe credit cards lasting 20-30 years past their proper lifespan. Only now do we see a little movement there, and mag-stripe will still be around in 20 years. Unfortunately.
I think the horse and buggy analogy is more appropriate for mailing paper tax returns.
Non-browser-based clients are Hummers. Big and clunky and wasteful and expensive, but generally safe for the driver.
The IRS should only send refunds to a pre-authorized bank account in the taxpayers name and not take changes without substantial proof that its the real taxpayer. If the account is setup ahead of time in their system it doesn’t have to be disclosed on any tax forms or online. A fraudster would have to first somehow change the bank account and then process a tax return a two step process. For the real taxpayer the added security would be minimal.
I agree that sounds good. I have a stable bank account for many years, and I assume you do to. I also assume you have not divorced recently. Or moved very far. Or changed banks.
However, as a significant portion of the population DOES NOT have that stability so it would present other problems. There are lots of people who struggle just to have access to a regular bank. Of course we could write them off… I’m just saying we should be mindful of all the assumptions when we design a solution like that. For goodness sake we can’t even agree that a photo ID is required to vote. 😉
They can still issue checks but force the check cashing places to verify name and address with a photo ID. I realize the IDs can be faked but it’s just another step the thieves would have to go through. Right now it’s waaaay too easy for them.
Having spent over a year helping a relative recover from one of these false filings, I have great sympathy for these new victims knowing the ordeal they are facing. Based on my conversation with the IRS about why anyone can file a change of address and request a refund without any sort of proof of identity, I don’t expect this problem to be solved very soon unless members of congress become victims and see first hand how the current procedures are heavily stacked in favor of the criminals.
It is a big surprise that Kerbs is not blaming Russia and Kremlin on U.S. companies filing fake tax returns…
Sensitive, are we?
If the IRS were a publicly-traded company, the entire management structure would have been wiped out and replaced because of the losses. $4 billion in one year??? Congress and the IRS have failed us by allowing bogus returns to be submitted and payments sent anywhere but to the address or bank account of the filer. The designers of the e-filing system should have been concerned about this problem from the moment they started mapping out the system. I’m reminded of the heath care web site.
BK, I wish you’d remind people not to let this conversation turn into a political tussle.
Heron, my comment was not political and I resent that you have flagged it as political! I’m complaining about the people who develop government systems, not the parties who request them.
Yes, Serena, I agree. The line is very thinly drawn between politics and technology, when the subject is fraudulent tax rebate claims.
If the IRS wasn’t collecting excess taxes in advance and rebating the excess once a year, this entire problem would never have occurred, and would instantly cease if that practice were reformed.
I agree with people who’ve suggested that personal solutions are to either file early (like in January), or submit the forms to have the IRS withhold only the bare minimum, so there’s no refund due.
Not having a refund due will not protect you from someone changing your mailing address with the IRS, then filing a return, indicating you deceased, and using bogus numbers to try and collect a refund. It can take over a year dealing with the IRS to get them to remove the deceased designation from your account. I know from hard experience.
Submitting as early as possible is your best protection if you can’t get a PIN.
good point, Mr/Ms Maersek, and one I completely overlooked.
Isn’t it odd how we filter our thoughts to assume that what we normally do is what anyone else would do? Or even be able to do?
I think a goodly share of wickedness makes hay with all the other possibilities.
I was thinking of how easy it would be for some to see what you wrote through a political prism, Serena. A warning shot, so to speak.
(Mea culpa for jumping the gun. Unreformed former mod on a different site.)
Thank you. I’m not affiliated with any party and can find fault with them all. I’m just profoundly disappointed by all of the waste of taxpayer money. We work hard for our paychecks and it seems so many in local, state, and federal governments steal or throw most of it away. The IRS handed out $4 billion in fraudulent refunds last year? I wonder if they were able to get any of it back. It’s apparently not a high priority to them to make sure their systems are secure because they have an endless pool of taxpayer $$ to pull from.
You’re welcome, Serena. I’m not happy with the way things are, either.
You’re complaining about 4 billion when there is probably 800 billion they didn’t even collect due to the tax reductions of the last 30 years?
And the solution is *so* simple: make it mandatory for *everybody* to file with let’s say a 12 digit TIN.
As described in previous discussions, from a security point of view there is nothing wrong with using a SSN for identification. The problem it is used also for authentication. That is the same as being able to log into an email account using only your email-address and no password.
And there are many western countries – e.g. in Europe – who are doing this already for 10+ years. So it is not as if it is complicated techwise, grandma wont understand, etc.
And when it comes to payment the IRS already does it! They already even have a system in place like this!
It is just a lack of interest and responsibility on the IRS side to not extend this to filing.
Jody Kaminsky/Ultimate Software should look into stronger authentication controls. If they’re using single factor auth (username/password), this is not sufficient to protect the data.
The concept of Transaction Intent Verification would come in handy here – being able to communicate with the users information about the authentication attempt securely to their mobile device, and allowing the user to confirm the transaction out of band:
https://www.duosecurity.com
https://blog.twitter.com/2013/improvements-to-login-verification-photos-and-more
Companies like H&R Block should do a better job of Identity Proofing the user before allowing them to file taxes with the stolen identities. Further, if they see this sort of activity done in mass from the same device/IP address, they should be able to flag these suspicious accounts and their associated efiled returns.
If thieves broke in because the HR payroll administrators had ridiculously simple passwords, I wonder if an employee could sue the administrator or sue the employer for not taking proper care to safeguard personal information. A year of credit monitoring is no compensation for the amount of work a person would need to do to fix the problem. And I wonder if H&R Block could also be sued for not exercising care. If I were a victim, I’d be contacting an attorney right now.
http://www.irs.gov/uac/FAQ%27s-for-Preparing-and-e-Filing-Your-Own-Tax-Return
It appears that the IRS is more than willing to help an identity thief file your return for you. Just call their toll free number and they will give you prior year AGI and/or PIN to the bad guy. This is straight from their website:
How can I get my prior year information if I do not have it?
You may call the IRS toll free number at 1-800-829-1040. If you can provide certain information to the Customer Service Representative (such as your name, SSN, and current address), you may receive the prior year original AGI amount or prior year PIN over the phone or you may request a free transcript. Allow 7 to 10 days to receive the transcript. Be sure to ask for the original AGI.
What????? I wonder how little info you can provide. Play stupid, it seems like you get away with more that way. “I don’t have my social security card with me, it’s at my mother’s house”. See if you can get the PIN or AGI with just a name and address. I would try it right now, but being Apr 15 their phone lines are probably jammed.