Security conferences are a great place to learn about the latest hacking tricks, tools and exploits, but they also remind us of important stuff that was shown to be hackable in previous years yet never really got fixed. Perhaps the best example of this at last week’s annual DefCon security conference in Las Vegas came from hackers who built on research first released in 2010 to show just how trivial it still is to read, modify and clone most HID cards — the rectangular white plastic “smart” cards that organizations worldwide distribute to employees for security badges.
Nearly four years ago, researchers at the Chaos Communication Congress (CCC), a security conference in Berlin, released a paper (PDF) demonstrating a serious vulnerability in smart cards made by Austin, Texas-based HID Global, by far the largest manufacturer of these devices. The CCC researchers showed that the card reader device that HID sells to validate the data stored on its then-new line of iClass proximity cards includes the master encryption key needed to read data on those cards.
More importantly, the researchers proved that anyone with physical access to one of these readers could extract the encryption key and use it to read, clone, and modify data stored on any HID cards made to work with those readers.
At the time, HID responded by modifying future models of card readers so that the firmware stored inside them could not be so easily dumped or read (i.e., the company removed the external serial interface on new readers). But according to researchers, HID never changed the master encryption key for its readers, likely because doing so would require customers using the product to modify or replace all of their readers and cards — a costly proposition by any measure given HID’s huge market share.
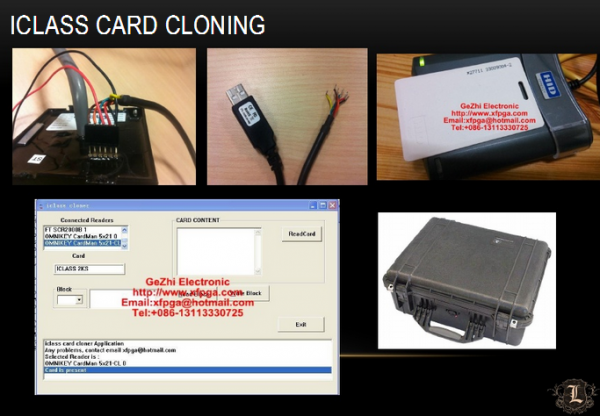
Unfortunately, this means that anyone with a modicum of hardware hacking skills, an eBay account, and a budget of less than $500 can grab a copy of the master encryption key and create a portable system for reading and cloning HID cards. At least, that was the gist of the DefCon talk given last week by the co-founders of Lares Consulting, a company that gets hired to test clients’ physical and network security.
Lares’ Joshua Perrymon and Eric Smith demonstrated how an HID parking garage reader capable of reading cards up to three feet away was purchased off of eBay and modified to fit inside of a common backpack. Wearing this backpack, an attacker looking to gain access to a building protected by HID’s iClass cards could obtain that access simply by walking up to a employee of the targeted organization and asking for directions, a light of a cigarette, or some other pretext.
Perrymon and Smith noted that, thanks to software tools available online, it’s easy to take card data gathered by the mobile reader and encode it onto a new card (also broadly available on eBay for a few pennies apiece). Worse yet, the attacker is then also able to gain access to areas of the targeted facility that are off-limits to the legitimate owner of the card that was cloned, because the ones and zeros stored on the card that specify that access level also can be modified.
Smith said he and Perrymon wanted to revive the issue at DefCon to raise awareness about a widespread vulnerability in physical security. HID did not respond to multiple requests for comment.
“Until recently, no one has really demonstrated properly what the risk is to a business here,” Smith said. “SCADA installations, hospitals, airports…a lot of them use HID cards because HID is the leader in this space, but they’re using compromised technology. Your card might not have data center or HR access but I can get into those places within your organization just by coming up to some employee standing outside the building and bumming a light off of him.”
Organizations that are vulnerable have several options. Probably the cheapest involves the use of some type of sleeve for the smart cards. The wireless communications technology that these cards use to transmit data — called radio-frequency identification or RFID – can be blocked when not in use by storing the key cards inside a special RFID-shielding sleeve or wallet. Of course, organizations can replace their readers with newer (perhaps non-HID?) technology, and/or add biometric components to card readers, but these options could get pricey in a hurry.
A copy of the slides from Perrymon and Smith’s DefCon talk is available here.





Been doing this for years. The vendors made it easy up until a few years ago when they started charging for their application developer kits instead of giving them away. However the cost is still not a barrier. In my experience, with the right gear, you can clone an unprotected Prox card from up to 5’/1.5M away.
Actually, no, you haven’t. As you said, you (and the rest of the world) have been cloning PROX cards, not SMART cards for years. If you don’t know the difference there is a primer on HID’s website.
Its important that these issues be discussed out in the open as we see here because companies are not going to point out their own security frailties. The problem in this instance is not that the system has flaws, but rather that it not be used to protect highly sensitive areas.
Brian, have you done a piece on NFC, specifically tap and go payment cards?
There is a lot a FUD and general BS being circulated about the technology and it would be good to have a definitive review by a credible source such as yourself.
Another vote for a credible discussion of “wave and forget” payment cards.
Dangers from:
1) being hacked / cloned
2) mistakes (such as when going through London Underground ticket gates with both a bank debit and an LU Oyster payment card in your wallet – when it is said it is a toss up which card gets charged)
My bank assures me that there are no problems and that aspects like “random requests for PIN confirmation” protect me. But when I ask if they can set the request for PIN confirmation to every 1 use, they say no can do!
Socially “wave and forget” cards encourage a spendthrift attitude – which is bad for us, but good for the card business. It also encourages an attitude of not checking our spending – and checking our spending has to be a key protecting against loss.
Stories about the problems with the London Underground Oyster card have traveled across The Pond.
Google: Hedge fund exec busted for cheating subway system
Another scam.
Google: Said Dlimi London Tube
“Detectives found the details he had stolen had been electronically transferred on to some 92 clones that were then used as far afield as Bombay.”
No.
The ‘hedge fund exec’ you mention exploited a weakness in the *implementation* of Oyster that allowed those who failed to ‘enter’ the system to pay a smallish fine on exit. This individual worked out that the fine was less than the actual fare for his commute. Naff all to do with the security of the card or its being contactless.
Even less relevant is the second case you quote: Said Dlimi was a clerk at Baker Street station who cloned customer payment cards when they were handed to him. If anything, this is a problem with the whole card system.
NFC is card to reader and wiegand is behind the reader to the controller. A number of early implementations of NFC door controller simply spit a number in the clear. Pretty much tap and go. That is not access control. Thanks for pointing to another area that needs a look see for any security value or control.
” Worse yet, the attacker is then also able to gain access to areas of the targeted facility that are off-limits to the legitimate owner of the card that was cloned, because the ones and zeros stored on the card that specify that access level also can be modified.”
Is that true ? When adding permissions to my badge (to get me into other buildings/areas), my understanding is the permissions are stored on a server, not on the card. (Because security asks for my badge serial #/ID and add permissions on a web interface there, not reprogramming the badge it self)
Access control decisions are either made by 1) the controller, which is periodically updated by the server or 2) the server directly if the card information is not currently cached on the controller. If the card identifier is copied onto another 125 kHz card, that card can be used on a reader. HID’s newer 13.56 MHz cards offer additional security, since the read range of the 13.56MHz cards is considerably shorter.
With the 125kHz cards, the reader actually starts to read the card at a distance of a couple of feet, and by the time the card is near the reader, the card information has been transmitted by the card reader to the controller. That’s why the read is relatively quick.
With the 13.56 MHz card format, ISO14443 requires that the maximum read range is around 4 inches. The card information also consists of more bits to be transmitted. As a result, the “read” time is significantly longer. The federal government’s Personal Identity Verification cards, which have been widely used since 2007, can be kept in an electromagnetically opaque sleeve which blocks the 13.56 MHz ferquency but not the 125 kHz frequency. Some PIV cards contain antennas for both frequencies to maintain compatibility with older access control systems.
It really depends on the system you deploy.
The better systems split the transaction into two parts where the card says who you are and the system tells the access point if you have access. The best system will store the access DB in the controller and the card will never have any thing on it other than the PII and biometric data needed to verify that you are who you say you are. The server will refresh the controller only when a change occurs and it runs independent of the server and can be recovered in network or power loss and remain operable even if the server is down.
The better readers are not on Ethernet but controller specific wiring using low voltage signals.
Even the really cheap HID stuff does not encode the users access levels on the card, you load them into a chip in table format at the access points.
The access points are weak in the cheaper systems and could be subverted pretty easily with 5 volts in the right place.
Too bad about the keys being in the open, lots of money will be spent to get rid of this issue.
Thanks for interesting angle Brian.
You are correct, access control decisions and authorization levels are handled by the door controller or the server, and not stored on the access card. What Brian is referring to (I think) is that with this attack, you can change the card number and masquerade as someone else. With cards being issued in sequential order, it’s not that hard to find another valid card number.
Correct. You need 3 pieces of info to clone or modify an iClass card. Bit length (ex- Corp 1000 35 bit), FAC (Facility code), and User ID.
Essentially, if you dont have access you modify the user ID until you get one that has access (Admin, physical security, guards).
PIN or Bio helps, but also issues with some of this being stored on the card. Not all implementations do this, but a lot do. If 2factor is used, be sure that the PIN + BIO template isn’t stored on the card.
Potentially, you could also tap the basic wiegand (green, white) wires and replay just the wiegand which could potentially bypass PIN or BIO depending on how the reader works and how those credentials are stored.
Also can’t forget to protect the badge system itself. If we can penetrate the network and control the badge server you can open individual doors, or open them all at once. Also hide logs and elevate privileges. If you get the 3 pieces of info you need, an actor could show up with premade card in hand.
Correct, but needs clarification. After reading a card one of the memory blocks can be modified with a different access card number, re-encrypted (with the compromised key) and then written to a new card. Privilege escalation made easy. And there are a number of ways to obtain an access card number that you want to change to.
Yes we know this vulnerability is there. But what can we replace our HID system to something isn’t vulnerable to this exploit. RFID protection sleeves have been proven NOT to work. And requires all of our employees to use them (impossible.)
I wish people would give me a company name or solution that I can upgrade my system to get resolve this issue.
There are these things called keys. You put them in the lock …
So maybe there are good reasons for using computerised locks in these instances I’m sure but often these days I find myself questioning why some functions are computerised like locks for example. Did we not have a very secure (provided you buy the right lock of course) solution already that could avoid this?
Heh.
Physical locks are not subject to this type of attack. I would argue that when involving a company of more than say 50 people per building it is very expensive to re-key and re-distribute the new keys.
As a result you run into the security hole of “once an employee always an employee” because the locks never seem to get rekeyed, and copying physical keys is very trivial.
Correct. We also need to know WHO is coming and going. Keys don’t do that.
And access cards also don’t tell you who is coming and going. Unless you make sure that only one person can enter at a time you only get the first person that just got off the bus to the front of your office. Also I can’t tell you how many times people forget their card and borrow someone else’s card to go pee (hint: a lot).
Only cameras will tell you WHO is coming and going and only if you don’t wear disguise.
Turnstiles…
True. We however have cameras everywhere.
What I am after is a secure RFID system (or maybe even a system that isn’t RFID but uses contact method.)
Sure using biometrics is always the good thing, but with the gazillion entry points and different doors, its not possible. We need a secure system. Who sells one?
We migrated to computerized access control systems for accountability and control. Who passed through the door and at what time? Keys don’t give you that information, and cannot become dysfunctional at 6PM so there is no after hours access for individuals who don’t need it.
Keys don’t offer the protection you think they do, and are susceptible to theft at much greater distances than RF cards. See http://vision.ucsd.edu/~blaxton/sneakey.html for details, and an example of copying a key at a distance of 195 feet using a telephoto lens.
You can move to two factor authentication. Add a PIN terminal and users will need to have something and also know something. Or add biometrics (fingerprint or palm reader) like Krebs mentioned and they’ll need to have two somethings.
You can protect your cards using proper OpSec, or by using one of the test kits I released at b-sidesLV for reading your HID reader during transmission of the Manchester data. You can also shield your reader from “leaking” data with conduit tape inside the plastic casing. Without it, we proved reads up to 10ft away during our demo. I released my schematics and the ability to purchase a kit to build on your own on kit-start dot com or just reach out to me on twitter @seanwayne.
Um, hello?
If the reader is wiegand, why bother with the encryption?
If you can sniff the data 0 & data 1 lines, you don’t even need to bother.
Just add an MIM and record and play back the card data.
Wiegand access control is all smoke and mirrors.
Most of the systems I have worked with have no contingency of tamper protection, so access to these data lines is trivial.
Agree.
Yes, basically need to upgrade a few things here, modern key, encrypted and bidirectional comms to support challenge, modern control and word lengths, etc. Can re-use wiring for encrypted 485. Fact is that 10 year life cycle and entry point for tech often means vulnerable in use.
Wiegand is old tech that has never evolved.
Wiegand: 1 way, everyone has different color scheme for up to a dozen different wires, no challenges, used on majority of electronic access control systems, vulnerable, hacked, needs to change.
Take a look at SIA Online Supervised Device Protocol (OSDP), held interop earlier in year, common bi-directional serial comms from reader to controllers, encrypted option, working on IP, other physical security devices also among next steps. #siaosdp
Spot On!
Modern companies are inherently cheap — unless an illegal intruder kills the CEO, nobody cares…
This is one of the most interesting posts for a little while! Thanks to Brian and all who are commenting here – it is good to revisit and catch up to the subject.
They have metal wallets for these things that are supposedly guaranteed to block RFID surveillance, but I had my doubts about the technology itself for some time. This is the first time I’ve read why my fears were founded, in detail.
HID has PIV enabled readers. You authenticate with your PIN and then verify by cert. If the PACS is modified to use this method even the best of hackers can’t take advantage of the RFID weakness.
Not really PIV enabled readers alone as others have pointed out, the readers don’t do the challenge and response in PIV with PIVclass or RPx40 or so. And that functionality exists in a limited number of PACS controllers with secure comms to a reader.
They do have the PIV readers, but haven’t seen any used in a commercial environment. Not an easy switch from an existing iclass implementation. And you can’t use Wiegand with that setup either.
However, the badge system itself is still vulnerable to attacking electronically and we are back to popping all the doors. So I wouldnt say that PIV/PAM implementation is 100% secure either.
I would say the industry needs to get away from HID’s closed source approach and look at more open standards like PLAID and OPACITY.
To make the move from iclass to PIV/PAM/SAM is a substantial investment. And at this point, no-one has really looked at the new SEOS/SIO technology to determine potential issues and attack vectors. I can assure its not “hacker proof”.
Looks like we have another company to add to the growing list of victims of identity theft.
SuperValu Food Stores
http://www.darkreading.com/supervalu-food-stores-reports-network-intrusion/d/d-id/1298068?
Card credentials or any other credentials typically store a facility code and a card number. This is the only thing being passed to the reader to gain access through a portal which is processed by the controller. This is by no means specific to HID card stock. Yes it is a volunerability that exist with single form authentication. As stated earlier card and pin is more secure as well as other multi mode authentication methods which typically include. What you have, what you know and what you are (biometrics). So yes you can get your hands on a HID K 100 OR K1000 card encoder and go at it. How about mag stripe? Yes old technology but still used quite alot and is extremely susceptible to cloning.
I wonder if this can be done with security cards used in hotels or company entrance points?
Yea.by adding it to the loyalty card they should use that card through the whole process.
so yes if they are using prox but usually not the case, a lot of magnetic stripe (really) and 1`st generation 13.56 MHz contactless that has also been broken (same stuff used in a lot of transit). Also seeing some upgrade here but the same is true that likely a majority of the legacy card readers are vulnerable. Battery operated is typically worse since design look to save. Same true here of some battery operated locks that use legit crypto and know how to protect and manage keys but vastly underrepresented in the installed base.
I remember the H4rdw4re guys were supposed to release ProxPick, a hardware kit that allowed you to clone the cards, but it never went anywhere.
check out Proxmark3
it’s open source.
you can buy one on ebay for about $300US
Some months back, I bought a couple of cheap USB RFID readers from eBay to try and learn something about the technology. I only made half-harted attempts, and I didn’t have much luck though – the access cards that I have didn’t register. I couldn’t even detect the chip that is implanted in the cat.
The tricky bits is that there are several wireless technologies out there with different frequency bands and all that, and if you don’t have the right type of reader you get nothing.
This does get me thinking however – I feel motivated to try harder..
Mr. Krebs,
Your web site is invaluable, but could you make it accessible via https? (Perhaps you have already explained the reason?)
Thanks (for all your work and risk).
pH
This also affects Enhanced Drivers Licenses. Allegedly, the EDLs don’t contain personally-identifiable information, but I would think its only a matter of time before someone figures out a nefarious way to use what they can read off of it.
There are several ways to attack iClass systems; a few seconds with a proxmark and a legitimate iClass elite reader and the custom master keys can be obtained.
I wrote a more thorough write-up here: http://martin.swende.se/blog/Elite-Hacking.html