Cybercriminals have long relied on compromised Web sites to host malicious software for use in drive-by download attacks, but at least one crime gang is taking it a step further: New research shows that crooks spreading the Dyre malware for use in cyberheists are leveraging hacked wireless routers to deliver their password-stealing crimeware.
Dyre (a.k.a. “Dyreza”) is generally installed by a downloader Trojan that is flagged by most tools under the name “Upatre.” The latter is most often delivered via malicious e-mails containing a link which directs unsuspecting users to servers hosting malicious javascript or a basic redirection to a malicious payload. If the user clicks the malicious link, it may serve a bogus file — such as an invoice or bank statement — that if extracted and opened reaches out to an Upatre control server to download Dyre.
According to a recent in-depth report from Symantec, Dyre is a highly developed piece of malware, capable of hijacking all three major web browsers and intercepting internet banking sessions in order to harvest the victim’s credentials and send them to the attackers. Dyre is often used to download additional malware on to the victim’s computer, and in many cases the victim machine is added to a botnet which is then used to send out thousands of spam emails in order to spread the threat.
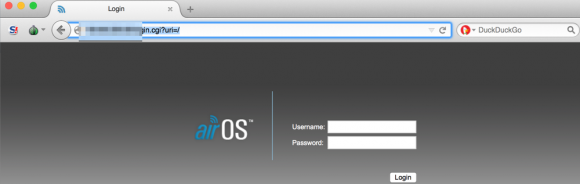
Recently, researchers at the Fujitsu Security Operations Center in Warrington, UK began tracking Upatre being served from hundreds of compromised home routers — particularly routers powered by MikroTik and Ubiquiti’s AirOS.
“We have seen literally hundreds of wireless access points, and routers connected in relation to this botnet, usually AirOS,” said Bryan Campbell, lead threat intelligence analyst at Fujitsu. “The consistency in which the botnet is communicating with compromised routers in relation to both distribution and communication leads us to believe known vulnerabilities are being exploited in the firmware which allows this to occur.”
Campbell said it’s not clear why so many routers appear to be implicated in the botnet. Perhaps the attackers are merely exploiting routers with default credentials (e.g., “ubnt” for both username and password on most Ubiquiti AirOS routers). Fujitsu also found a disturbing number of the systems in the botnet had the port for telnet connections wide open.
In January 2015, KrebsOnSecurity broke the news that the botnet used to attack and briefly knock offline Microsoft’s Xbox and Sony Playstation’s networks relied entirely on hacked routers, all of which appeared to have been compromised remotely via telnet.
Whether you use a router from Ubiquiti or any other manufacturer, if you haven’t changed the default credentials on the device, it’s time to take care of that. If you don’t know whether you’ve changed the default administrative credentials for your wired or wireless router, you probably haven’t. Pop on over to routerpasswords.com and look up the make and model of your router.
To see whether your credentials are the default, you’ll need to open up a browser and enter the numeric address of your router’s administration page. For most routers, this will be 192.168.1.1 or 192.168.0.1. This page lists the default internal address for most routers. If you have no luck there, here’s a decent tutorial that should help most users find this address. And check out my Tools for a Safer PC primer for more tips on how to beef up the security of your router and your Web browser.





There are two separate logins to consider. One is for linking over WiFi to access the internet and the other is for logging into the routers’ internal software for making settings changes. Most people seem to forget all about the second one. Changing the SSID and WiFi password is one thing but if the firmware login is left at default then it is very easy to get in from the outside. Many routers (especially those that are built into modems from the ISP) will already have secured WiFi and do not need their SSID/password changed. But, changing the firmware login is usually overlooked.
Many people know the risk of leaving the default router configuration credentials, but choose not to change it because they believe WEP/WPA(2) is enough defense (or they simply don’t care about security).
WiFi Protected setup also defeats the purpose of passwords because it relies on an 8 digit PIN, however it only authenticates with the first 4 digits. This flaw makes online and offline exploitation incredibly easy as there is almost never a password lockout.
Do you know how to change the router login password on a Comcast wifi modem? I spent an hour in an online chat with a Comcast support person before s/he closed the chat session without giving me the answer. S/he kept thinking I wanted to change the private wifi network name and password, even though I kept saying that I had already changed it.
Yes, but if you do, you will very likely destabilize the WiFi. Doing that is not a good idea and is not necessary anyway. That is not the item that needs to be changed.
Sometimes, doing this will have the desired effect but there is something about those modems that just creates more problems than it’s worth when not on defaults.
OK, thanks. That’s good to know.
You are not alone in having problems with Comcast. I already have two internal WiFi networks and did not want a third or a fourth public one. You can turn off the public WiFi …. theoretically. After two hours over three days nothing I was able to do turned it off. Magically on the fourth day it went off. Wonderful! Until the 30th day when the Comcast supplied router failed. (what you might call very de-stabilized)
While being on telephone hold I so enjoy being repeatedly told I can look up many answers on the web at …. umm, if I could access the web in the first place!
Got a replacement router and …. the public and private WiFi are back. GAK!
There has to be a better way.
Jonathan @nc3mobi
“Got a replacement router and …. the public and private WiFi are back. GAK!
There has to be a better way.”
There is. Buy your own modem. That gives several advantages: DOCSIS 3 support, a lower bill…and no public wifi. Win-win-win.
are the antennas external?
A 50 ohm dummy load would prevent the Wifi signal from extending more than a few inches from the router.
No one has any idea which Router Comcast chose to use?
I had similar issues with Charter, blown off by thier support team and left to my own devices, Google is Good but not always enough, sometimes the initial browser page you land on when accessing the internal settings for the router will provide most all information you would need to determine exactly what router your working with, atleast it did in my case or I was just lucky or maybe stubborn.
Default Settings are just plain Dangerous, PNP is still an issue, so I just dont expect much anymore.
Access a Comcast router
10.0.0.1
Username: admin
Password: password
Change default passwords, SSID’s, put router in bridged mode to disable public Wifi (but will need your own Wiif device if you do)
http://customer.xfinity.com/help-and-support/internet/wireless-gateway-username-and-password
Simple answer if you cannot get an answer from Comcast (or any other provider), set up a router/firewall within your network directly attached to your broadband modem in the uplink port. You can certainly secure that router and base all of your networking, internally, from there.
Other, very popular routers, are points of unauthorized entry that come pre-hacked in the box.
The SURFboard SBG 6580 made by Motorola and also sold under the “Arris” brand name has THREE CVE documented vulnerabilities allowing outside attackers to take control and cause a computer inside the protected zone to become exposed to the world.
details at
http://nc3.mobi/references/2015-summary/#20150409
Jonathan @nc3mobi
At least here in the U.S., firmware updates to Motorola’s latest cable modems are supplied via the ISP (which normally happens rarely if ever). You can’t even download a firmware update if you wanted to. Here’s the download page for this cable modem:
http://arris.force.com/consumers/ConsumerProductDetail?p=a0ha000000GNcsnAAD&c=SURFboard%20Modems%20and%20Gateways#panel4
Control over firmware upgrades should be in the buyer’s hands, not the ISP’s (which can be ordered / partnered to conform to govt demands for backdoors). A very corruptible situation for people’s front door to the internet (I don’t think DSL or Cable Modem vendors are any better).
wonder if you can use tomato or dd-wrt on routers like that.
It wasn’t too long ago that Time Warner got slapped with a law suit over modems that were so bad that they had multiple vulnerabilities, and were easily cracked from the web side of the network, no mater how they were configured. You won’t find the story very easily though, because so many people are suing them over modem scams that it is pitiful!
Which routers allow admin connection from WLAN by default?
User’s LAN must be infiltrated to be able to use default admin credentials on gateway address.
Believe it or not, most routers let you configure it wirelessly, as crazy as that is….
One of the first things I turn off with a new router…crazy that its allowed to be on by default.
WLAN is not the wireless side; it’s the internet side of the connection. While configuration of the router from a wireless connection may offer some small risk (especially in a public or semi-public context like a coffee shop or airport), it’s not nearly the hazard as allowing the configuration to happen from outside the local network. Which is what the “WLAN” is talking about.
Peter, WLAN *is* wireless. You’re thinking of “WAN”.
I keep hoping for a central database of router vulnerabilities, and a specific list of which routers are susceptible to them. Since the router manufacturers don’t seem overly forthcoming with the information, or quick to patch vulnerabilities once a 3rd party discovers them, I doubt such a database will ever exist. Still, it would be nice to be able to go to the store and confidently buy something you know is secure.
+1
Such a database would likely be found via hacker website/darknet. Router makers have lawyers/PR firms/federal regulatory guidlines and rules. There is very little to be gained for the manufacturer to distribute this type of thing.
I would agree that the populous needs to be able to trust something. But the only router out there that can in any way be trusted is the one YOU setup by turning a computer into a server (as a router). It’s just that very few people go this way. Very few businesses go this way.
The time for that flashing 12:00 getting ignored has come and gone. People NEED to start learning how to do things on their own. The needed information will not be readily available. The user must have the motivation to do their due diligence.
It is the USER’S responsibility to secure such devices.
If they do not know how, then they shouldn’t be messing with it in the first place.
That’s why we hire people to do this type of work.
“That’s why we hire people to do this type of work.”
That only works to a certain point. Websites like this one (among many others) are proof that this philosophy cannot be applied universally. At some point, the person that bought the equipment needs to take responsibility for it. When the situation turns to the software that runs the hardware and the owner cannot be responsible….the the owner should reconsider wether or not they really need to own such hardware.
My computer is mine. It belongs to me. I own it. The moment I lose control and responsibility is when this machine will no longer exist in my home. It’s the same for my vehicle and everything else I have purchased.
How many people don’t even reconcile their checking account or their charge card statements? You want them to fiddle with them there electronic gadgets?
Until sometime in the mid-1950s it was possible to get an 8th grade education and know enough to get thru life. We can’t do that any more. We saddle people with a minimum of 12 years, more likely 16 (and usually a lot of debt) and the average person can’t keep up in technology and other fields.
As a nation we cannot afford to continue to let bad design remain the standard and make hundreds of millions of people tweak the setups to get around the flaws. Think of what could be accomplished with just one hundred million people hours! Think this isn’t a problem? How many “emergency patches” have there been from mainstream software in the first five months of this year alone? TOO MANY.
There has to be a better way.
Jonathan @nc3mobi
ps: I’ve completely lost my zymurgy skillset.
“Until sometime in the mid-1950s it was possible to get an 8th grade education and know enough to get thru life. We can’t do that any more.”
Tell that to the teachers union.
“As a nation we cannot afford to continue to let bad design remain the standard and make hundreds of millions of people tweak the setups to get around the flaws.”
How does a person even know what “bad design” is? We completely accept and are willing to pay big money for bad design. We even demand it in some cases. Then cry when bad things happen.
________________________________
I’m sorry that other people don’t know how to do things in life. We are so completely dependent on these machines. It’s too scary to live in this world and be so ignorant of how anything works. It is just beyond me how people can actually live that way. If it tells ya something though, I have just about lost the ability to write in cursive (except for my signature).
I don’t understand what happens when I encrypt my router.
My concept of encryption is that both ends of an encrypted session need to be using the same key or hand-shaking algorithm. How does this work when only I do the encrypting?
@DaveN There is the Offensive Security Exploit-db which is a db of almost all public vulnerabilities, but you can easily narrow down a search to just router vulnerabilities. https://www.exploit-db.com/
@Bart router encryption only happens between your IoT device, and the router. Your local network encryption never goes to the internet, so there is no need for an external handshake(SSL encrypts internet data). Sorry to spam the comments!
Thanks, Dylan.
So it is for wireless connections where there is a danger of local snooping, perhaps a neighbor or drive-by person hoping to capture banking info, etc.
I wonder if this might have anything to do with counterfeit devices manufactured in China. The Chinese have broken up the production of those devices but didn’t do anything to find the ones manufactured and distributed. Ubiquity gets to go to court, but this kind of problem is not something that a court can compensate for.
Just use a WIFI router password that you know for example “password123456789” and convert it to base64 encode. Then after that use the base 64 decoded numbers and letters as you new router password.
password123456789
converted
cGFzc3dvcmQxMjM0NTY3ODk=
I am shocked that Mikrotik routers seem to be among the exploited ones. First someone who goes and buy a Mikrotik is not the type of user to leave default login credentials. Second I considered Mikrotik to make the best consumer/prosumer routing devices. I fact I was wondering why a large section of OpenWRT forums are dedicated to flashing Mikrotik devices (which come with at least a Level 3 or Level4 Mikrotik license to OpenWRT. Go figure. Maybe is the layer 2 “telnet” utility provided by Mikrotik being abused for inside (from a pwned PC)
“First someone who goes and buy a Mikrotik is not the type of user to leave default login credentials. ”
Although they were aggravatingly vague in the report (which is really a disservice to those of us in the field who need to stay on top of this stuff), it’s intimated that many of the exploited devices were supporting captive portals. So we may not not talking about devices set up by enterprise engineers or computer scientists, but installations done by contractors employed by coffee shops and other storefront businesses — where the same guy who pulls the cable through the wall is also supposed to configure the firewall and secure the box. Mikrotik’s by default don’t have a password, and until recently didn’t come with any firewall rules defined. Right out of the box they are lit up like Christmas trees, running telnet, ftp, ssh and http servies just like most other systems. Remediating security risks by turning off some of those services, setting strong admin passwords (Mikrotik also lets you change the login name for its root user), and inserting a half dozen bare minimum firewall rules may not seem like a challenge for many of this column’s readers, but for small shop owners and their electrician-turned-network-installer contractors it is probably a bridge too far.
As others have noted here though, it really is high time the general public stepped up and started educating themselves. After spending a couple of decades of late nights after hours in a struggle to keep up with rapidly evolving computer technology, I don’t have a lot of sympathy for those who think all they need to do is sit back on their butt and click away with the remote until some reality show lead-in catches their eye.
This article seems to indicate that rather than just Trojans/Ransomware that some online criminals are experimenting with compromising routers from the internal LAN using default passwords and exploits.
http://malware.dontneedcoffee.com/2015/05/an-exploit-kit-dedicated-to-csrf.html
On! On ! Mr. Carter, !! Loved the discussion about router security.
Some minor points…
Email problems again. The security of the router just being investigated again. Backdoors in routers again. Chipset outsourced again. Again, again.. Seems never ending. People are looking for useful, able products to do everyday work and play. Maybe they should have two products. Setup differently.
The government and businesses want to be able to monitor you. To sell services. So they insist on backdoors. Knowing there is a back door, lets others in who may be nefarious. So why all the complaints. Knowing the vulnerabilities means you know what not to do. On that device.
Especially loved the bit about encrypting to the router, and its back to plain text afterwards…
Hi,
Great read, as always.
I wanted to point you to our post about, what appears to be, the same Ubiquiti router botnet used for DDoS attack.
https://www.incapsula.com/blog/ddos-botnet-soho-router.html
Our clients were terrorized by them for over 6 months. Prior to publishing this, we’ve reached out to Ubiquiti, sharing detailed IP information and got in touch with multiple ISPs who resell these routers. Sadly only few actively took steps to investigate and prevent further abuse.
Thanks for bringing more attention to this issue.
I consider myself to be somewhat of an advanced user and work in the field professionally.
I purchased my own cable modem for use with my provider (without any wireless anything in it), and put a DD-WRT router in front of that. I changed to a super long non-default password, and added good passwords for the SSID’s. The best part is I save on paying the cable company for their modem each month, the savings is close to a $120 a year.
I don’t like the cable companies concept of selling you service and then trying to control your Wi-Fi or even turn your router /modem into a public hot-spot.
The claims in this article are not correct. MikroTik routers by default have firewall on the public interface, and nobody can connect to the management interface except the owner.
While I’m apt to say you may not be right (Brian usually does decent research for his posts), I am wondering about this. (That said you are absolutely correct – the only outside ports open on the two I’m experimenting with are SSH and the software management port, both protected by a non-default password.)
I just recently came across the MikroTik routers and was extremely impressed by just how much functionality you get out of them for the low price. So if they ARE vulnerable to something…well, I’d rather like to know exactly how and what it is.
Just throwing this out there, since I certainly don’t have all the answers to what’s going on here…but seems to me it’s also possible that the underlying systems served by these routers are being hacked, and that the routers are being (ab)used after the fact.
http://wiki.mikrotik.com/wiki/Securing_New_RouterOs_Router
Talks about RouterOs on MikroTik, a quick read seems to indicate that it’s fairly easy for a user to install it without a firewall and with a default password and with telnet available from the WAN. (And yes, the page is full of typos, it’s a Wiki, you can fix it, I’m not interested in touching it.)
I could be wrong. I don’t have the hardware and I’m not particularly interested in becoming a Router expert. (I have loaded DD-WRT on one router recently, but that doesn’t make me an expert, and I suspect I picked the wrong category, perhaps I wanted Tomato…)
re: firewall – >>nobody can connect to the management interface except the owner
But there was an exploit using Java/Flash o-days to access routers as the owner from the inside, if passwords were still at default.
Read this: http://www.tomshardware.com/news/f-secure-router-checker-dns-hackers,28835.html
If your comfortable, scan your router with F-Secure’s tool:
http://www.tomshardware.com/news/f-secure-router-checker-dns-hackers,28835.html
Sorry the link to F-Secure’s tool is here: https://campaigns.f-secure.com/router-checker/
A quick way to identify router and LAN vulnerabilities is to search your IP at Shodan’s site, http://www.shodanhq.com/exploits
Consider adding Infosec Institute to your list of organizations that provide cybersecurity certifications. They offer a vast variety of certifications including Certified Penetration Tester and Computer Forensics. Both of which were developed by InfoSec Institute and I think are very much applicable to the cyber security field.
If you are an employer who is interested in any of the courses they provide I would recommend reaching out to Carolina Velazquez at (608) 286-2110 or by email at carolina.velazquez@infosecinstitute.com.
I’m lost on this (old man) but what about Smart TV’s that have WiFi cause I just bot a Samsung Smart TV and I have internet access via my TV. I hav Symantec/Norton on my puter but havnt installed anything like that on my TV! Should I via the browser on the TV?
Security researchers have found that some of the router manufacturers themselves have horribly incompetent programmers. One example is a fancy-looking D-Link that, due to a programming mistake, is incredibly easy to break into no matter what the user does.
An article about it was on Hackaday:
http://hackaday.com/2015/04/14/d-link-fails-at-strings/
With the technical details here:
http://www.devttys0.com/2015/04/hacking-the-d-link-dir-890l/
(The very next post after that, on D-Link’s attempt to fix it, is priceless.)
Many professionals, when they buy a router, completely wipe the manufacturer’s firmware and replace it with well-tested secure firmware like OpenWRT.
Must have been those Mexican hackers!
Is there any reason not to demand that the provider configure the modem/router as a bridge that you hook up to your own router? This removes administrative control of the router from your provider while leaving them with control of the modem.
I work for an ISP and we’ve had a round of tp-link routers set with a DNS redirection to porn sites. Happens when remote management is enabled and the router login is left at the default. It seems to be similar to the hack of the linksys routers last year, but it just changes the default DNS to 107.181.175.107. If you lock down the router by changing the login and the DNS entry, it seems to fix most of them.
If you think people should start learning how to do more of their networking, you haven’t done tech support. People don’t even want to write down their wifi password.