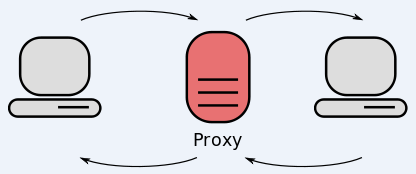
Netflix, Hulu and a host of other content streaming services block non-U.S. users from viewing their content. As a result, many people residing in or traveling outside of the United States seek to circumvent such restrictions by using services that advertise “free” and “open” Web proxies capable of routing browser traffic through U.S.-based computers and networks. Perhaps unsurprisingly, new research suggests that most of these “free” offerings are anything but, and actively seek to weaken browser security and privacy.
 The data comes from Austrian researcher and teacher Christian Haschek, who published a simple script to check 443 open Web proxies (no, that number was not accidental). His script tries to see if a given proxy allows encrypted browser traffic (https://), and whether the proxy tries to modify site content or inject any content into the user’s browser session, such as ads or malicious scripts.
The data comes from Austrian researcher and teacher Christian Haschek, who published a simple script to check 443 open Web proxies (no, that number was not accidental). His script tries to see if a given proxy allows encrypted browser traffic (https://), and whether the proxy tries to modify site content or inject any content into the user’s browser session, such as ads or malicious scripts.
Haschek found that 79 percent of the proxies he tested forced users to load pages in unencrypted (http://) mode, meaning the owners of those proxies could see all of the traffic in plain text.
“It could be because they want you to use http so they can analyze your traffic and steal your logins,” Haschek said. “If I’m a good guy setting up a server so that people can use it to be secure and anonymous, I’m going to allow people to use https. But what is my motive if I tell users http only?”
Haschek’s research also revealed that slightly more than 16 percent of the proxy servers were actively modifying static HTML pages to inject ads.
Virtual private networks (VPNs) allow users to tunnel their encrypted traffic to different countries, but increasingly online content providers are blocking popular VPN services as well. Tor offers users the ability to encrypt and tunnel traffic for free, but in my experience the service isn’t reliably fast enough to stream video.
Haschek suggests that users who wish to take advantage of open proxies pick ones that allow https traffic. He’s created and posted online a free tool that allows anyone to test whether a given proxy permits encrypted Web traffic, as well as whether the proxy truly hides the user’s real Internet address. This blog post explains more about his research methodology and script.
Users who wish to take advantage of open proxies also should consider doing so using a Live CD or virtual machine setup that makes it easy to reset the system to a clean installation after each use. I rely on the free VirtualBox platform to run multiple virtual machines, a handful of which I use to do much of my regular browsing, tweeting, emailing and other things that can lead sometimes to malicious links, scripts, etc.
I’ll most likely revisit setting up your own VirtualBox installation in a future post, but this tutorial offers a fairly easy-to-follow primer on how to run a Live CD installation of a Linux distribution of your choosing on top of VirtualBox.




good article!
I saw a great quote the other day. I would credit the originator if I recalled who it was.
“If you’re not paying for, you’re not the customer. And if you’re not the customer, you’re the merchandise.”
If you are not paying for the product, then you are the product!
I am using a secure VPN to post this, because we wouldn’t want Krebs to know my real IP address. :–)
I used to do this when traveling to Canada for business. I would get on my US-based company VPN in the hotel room. I was always assuming this was safe, but must admit that was not my top priority at the time. I seem to recall I was watching music videos, like Vimeo or the like, but it was a few years ago.
A bigger hazard to you in this case is your employer might consider it an inappropriate use of corporate resources; this could lead to many things, up to and including termination of employment. Best to check that this is OK before you do it.
It’s a spin on a classic cliche: “Look Around the Poker Table; If You Can’t See the Sucker, You’re It”
Thanks for another good tip, Brian. Always a pleasure reading your blog.
I wonder if anyone has yet done similar research with regard to “free” VPNs such as vpnbook, vpngate, and the OpenVPN servers that can be found using the Android app EasyOvpn.
Why pay for a VPN when you have a perfectly good Internet access at home? May as well build your own VPN service like this guy did using a Linux PC or even a Raspberry PI and connect to it when travelling.
https://www.sans.org/reading-room/whitepapers/networkdevs/soho-remote-access-vpn-easy-pie-raspberry-pi-34427
Great story Brian. I can pass the word to my clients, whom I always encourage to visit your site every day, already! Thanks!
This article reminds me of irritating practices like AT&Ts excuse for leaving port 443 wide open, just because some folks can’t use their Kindles to get on the web with out blasting a hole in the hardware firewall. NOT GOOD!
The other fun thing these “free” options are doing now as well, is sucking up your bandwidth to use for other services etc. So although youre only browsing some plain websites, someone else is using your bandwidth for other things.
Agree that virtualbox creates a safe environment, providing the internet connection isn’t bridged into the home network. Sandboxie, combined with good antivirus technology is very good for daily browsing safety. I use it religiously and put the sandbox in a ram disk, which is erased whenever I log off the browser or turn off the pc.
Also have a paid for vpn for public wifi browsing – got it on sale cheap. Also use OpenVPN for safe public wifi browsing where I need to log in using my home IP address while on public wifi.
Good security takes an effort to deal with. Plus there’s the devil you don’t know who will come out later. Plus it’s a hobby.
Nothing is ever free, just fork out the few dollars for a proper service, it’s not that expensive. I went with NordVpn who are quite cheap. http://reviewmyvpn.com/nordvpn-review/
As the article points out…
“Virtual private networks (VPNs) allow users to tunnel their encrypted traffic to different countries, but increasingly online content providers are blocking popular VPN services as well.”
Wait til you get to the ‘free’ VPNs that will do ‘computer calculations’ using your resources in order to ‘support’ them, and of course, charity! 😉
https://i.cubeupload.com/wQqWHW.jpg
I saw a great quote the other day
For years Ankit Fadia has been advising users about free Russian proxies to evade schools, and businesses firewall settings and to protect your anonymity, and like the clueless ethical hacker that he is, didn’t consider or care that he was making you more insecure. Sorry to be the bearer of bad news, but I told you so.
http://attrition.org/errata/charlatan/ankit_fadia/
What Linux version do you typically use for your VM, Brian?
Thanks for the article!
It may be obvious to most but….
Just be aware – don’t try this at work, unless it is approved. Some Information Assurance and CND people consider proxy use as circumventing security, and they knee-jerk into action without questioning.
For home use, I am sure its open season, do as you wish.
Good information, as always. Maybe you could, on a quiet day, revisit the topic of setting up a multi boot system. And telling the less savey how and where to create a virtual disk, and what programs that are safe and how to utilize them. An explanation, there are newbies and grandmas who travel outside of business, some may read your article, and not know of these products and how to use them safely, and what what not to put out there.
One option for a (more) secure VirtualBox Linux environment specifically created for safe browsing is Browser in the Box from Sirrix http://www.sirrix.com/content/pages/BitBox_en.htm.
It is easy to install, doesn’t require much setup, and can even be made the default browser for a Windows environment.
It was initially developed for the German Federal Office for Information Security.
I have been using it for several years and find it rather usable.
Hehe!
I checked out those free vpn services and the https is one of the first things i checked.
So to review-
You would like me to give you(insert unknown vpn here) my cc info So i can watch netflix America for free?
Go away nubs , and find some other sucker.
My personal VPN loads Netflix movies just fine and it is not a niche service so there must be a different story to this.
The story’s about proxies, not VPNs.
If you are stupid enough to route all your traffic through a proxy you know nothing about, don’t be surprised that it’s being sniffed or modified. You’re making them the man in the middle.
Hi all,
Disconnect is a proxy/vpn that also filters ads and malware,plus other bad black listed urls. They recently filed suit against Google in the EU for them having discriminated against their Android app that got booted from playstore. There is a subsciption,but reasonable. The founder used to work at Google, but is a privacy advocate,so he left because he did not like what they were doing. I believe him and his work to be above suspicion. Check it out at “disconnect.com”
It may burst some people’s bubble, but have a read;
Top VPNs Leak Sensitive User Information – Report
http://www.eecs.qmul.ac.uk/~hamed/papers/PETS2015VPN.pdf
A justification for forcing HTTP only is that it helps caching. It’s effectively impossible to cache HTTPS content as it’s encrypted (with a different key for each session).
If I were providing a free proxy to anyone on the web, I’d want to use as much caching as possible to avoid using more bandwidth (and having to pay for that extra bandwidth).
As long as this is communicated up front, I don’t really see anything wrong with it; just don’t use that proxy for anything sensitive (which probably includes Netflix, since it has your billing info).
Cheap can be expensive