People who cheat on their partners are always open to extortion by the parties involved. But when the personal details of millions of cheaters get posted online for anyone to download — as is the case with the recent hack of infidelity hookup site AshleyMadison.com — random blackmailers are bound to pounce on the opportunity.
According to security firms and to a review of several emails shared with this author, extortionists already see easy pickings in the leaked AshleyMadison user database.
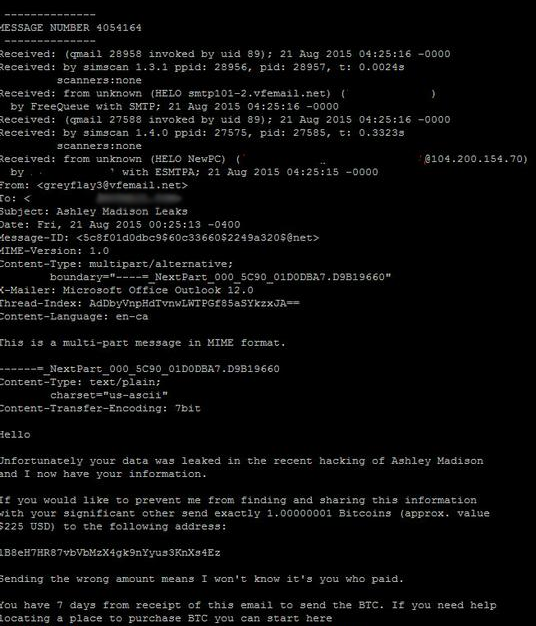
Earlier today I heard from Rick Romero, the information technology manager at VF IT Services, an email provider based in Milwaukee. Romero said he’s been building spam filters to block outgoing extortion attempts against others from rogue users of his email service. Here’s one that he blocked this morning (I added a link to the bitcoin address in the message, which shows nobody has paid into this particular wallet yet):
Hello,
Unfortunately, your data was leaked in the recent hacking of Ashley Madison and I now have your information.
If you would like to prevent me from finding and sharing this information with your significant other send exactly 1.0000001 Bitcoins (approx. value $225 USD) to the following address:
1B8eH7HR87vbVbMzX4gk9nYyus3KnXs4Ez [link added]
Sending the wrong amount means I won’t know it’s you who paid.
You have 7 days from receipt of this email to send the BTC [bitcoins]. If you need help locating a place to purchase BTC, you can start here…..
The individual who received that extortion attempt — an AshleyMadison user who agreed to speak about the attack on condition that only his first name be used — said he’s “loosely concerned” about future extortion attacks, but not especially this one in particular.
“If I put myself in [the extortionist’s] shoes, the likelihood of them disclosing stuff doesn’t increase their chance of getting money,” said Mac. “I just not going to respond.”
Mac says he’s more worried about targeted extortion attacks. A few years ago, he met a woman via AshleyMadison and connected both physically and emotionally with the woman, who is married and has children. A father of several children who’s been married for more than 10 years, Mac said his life would be “incredibly disrupted” if extortionists made good on their threats.
Mac said he used a prepaid card to pay for his subscription at AshleyMadison.com, but that the billing address for the prepaid ties back to his home address.
“So they have my home billing address and first and last name, so it would be relatively easy for them to get my home records and figure out who I am,” Mac said. “I’ll accept the consequences if this does get disclosed, but obviously I’d rather not have that happen because my wife and I are both very happy in our marriage.”
Unfortunately, the extortion attempts like the one against Mac are likely to increase in number, sophistication and targeting, says Tom Kellerman, chief cybersecurity officer at Trend Micro.
Kellerman is convinced we’ll see criminals leveraging the AshleyMadison data to conduct spear-phishing attacks aimed at delivering malicious software such as ransomware, a different type of extortion threat that locks the victim’s most treasured files with a secret encryption key unless and until the victim pays a ransom (also in Bitcoins).
“There is going to be a dramatic crime wave of these types of virtual shakedowns, and they’ll evolve into spear-phishing campaigns that leverage crypto malware,” Kellerman said. “The same criminals who enjoy deploying ransomware would love to use this data.”
The leaked AshleyMadison data could also be useful for extorting U.S. military personnel and potentially stealing U.S. government secrets, experts fear. Some 15,000 email addresses ending in dot-mil (the top-level domain for the U.S. military) were included in the leaked AshleyMadison database, and this has top military officials just a tad concerned.
According to The Hill, the U.S. Defense Secretary Ash Carter said in his daily briefing Thursday that the DoD is investigating the leak.
“I’m aware of it, of course it’s an issue, because conduct is very important,” Carter told reporters at the briefing, The Hill reported. The publication notes that adultery in the military is a prosecuteable offense under Article 134 of the Uniform Code of Military Justice. Maximum punishment includes dishonorable discharge, forfeiture of all pay and allowances, and confinement for one year. As such, Carter told reporters that service members found to have used adultery website Ashley Madison could face disciplinary action.
Kellerman said attacks against military personnel who used AshleyMadison may well target spouses of people whose information is included in the database — all in a bid to infect the spouse as a way to eventually steal information from the real target (the cheating military husband or wife).
“Something must already be going on for [the Secretary of Defense] to actually have a press conference on that,” Kellerman said. “We may actually see spear-phishing campaigns against spouses of individuals who are involved in this, attacks that say, ‘Hey, your wife or husband was involved in this site, do you want to see proof of that?’
And the proof, in this scenario, would be a a booby-trapped attachment that deploys spyware or malware.
Mac, who’s not a military man, says he doesn’t regret the affair he had via AshleyMadison; his only regret is not finding a way to keep his home address out of his records on the site.
“I regret using my home address and some of my personal information that AshleyMadison didn’t take as good care of as they should have,” he said. “But I really, I’m mad these hackers feel it’s so important to force the hand of people that have a different outlook on life.”
The AshleyMadison data is leaked on various sites, but the data itself is not easily searchable by folks who aren’t familiar with raw database files. However, several sites have since popped up that allow anyone to search by email address to find if that address had an account at AshleyMadison.com. True, AshleyMadison.com did not always verify email addresses, but some of these AshleyMadison search services coming online will indicate whether the associated email address also has a payment record — a marker which could be useful to extortionists.




As someone with an email on the list, (I never managed a hook-up since 95 % of the female profiles are fake) I can tell you that Gmail is successfully sending all my extortion emails to the spam folder. That will make it pretty hard for me to pay all of the thousands of blackmailers.
So the owner of the website amicaught just said he would remove my name for $1,000. These people are scumbags.
I did some quick research. He purchased the domain via GoDaddy and used Cloud Flare out of San Fran as his server. Anyone able to out who these people are?
Maybe someone should talk to the police on the subject of extortion. Anyone who tries to profit off of this deserves legal trouble.
Really? Perhaps you and other cheaters should take a good hard look in the mirror before casting such rubbish. If YOU used the site, shame on you…and I am laughing AT YOU. Foolish little lewzzzers.
I do feel bad for the folks that are wrapped up in this. Dirty business all around. Would be kind of ironic to out the “outers”. I have a buddy that works for one of those two companies. Will see what I can find out. More to come.
That’s extortion and should be reported. The IP should also be reported to Cloudfare and AM immediately
We should report to godaddy for violation of privacy policy.
Promising steps. Buddy is getting information for me.
Got him. Using such big outfits like GoDaddy and CloudFlare not very smart on his part. If the big data release happens on Wednesday as planned, I will release his information to 30 million people. I would only do this, of course, as a public service. The irony is that my name isn’t even on the list. But people deserve some level of privacy. Hopefully he sees this post before folks start showing up at his door on Wednesday!
Please! Do not wait until Wednesday! Can’t you do it now?
Pete; thank you so much for the help you’re providing! Since the extortion has already begun by that site, is there anything you can do sooner than Wednesday morning? Thank you again!
Sue the extortionist then arrest him then sue the abby website for crap security. I love all these companies that take no responsibility when their systems get hacked. Almost always from an internal source selling information. Most hacks like this guy are not really that good, just hack his site which has already happen he just doesn’t know it yet. To the person protecting the name you are liable legally to report criminal activity it’s the law.
Pete, don’t know if you’re still monitoring this but a suspiciously similar site just popped up on the reddit board with an .xyz domain. Did a quick search and returned exact results from previous site
Release the name. Rumor has it that this guys website is tied to the suicides.
I appreciate everyone wanting to know who is the individual behind the site but I beliieve in humanity. If I released his name now I would be no better than him. I don’t want to turn a mob on anyone. He has a chance to do the right thing.
So go to the police. Seriously. If you can give them info to act on then you could be stopping more pain.
Pete- please! Can’tyou warn him that his ID is known and that if he proceeds his info will be made public? Please! There could be more suicides if he proceeds!
God help him if the rumor is true and his site was connected to those suicides. Not sure how a person could have such a blatant disregard for life.
What is supposed to happen Wednesday?
If the new data dump happens as this bottom feeders site said it would i will plaster his name and address on every blog I can find. I wish Pete would release the information now so we could go after this puke.
The email address posted on his site for the whole world is as follows:
Amicaught@gmail.com
Maybe we should all email him and tell him to check these postings so he understands?
That website is now down.
I’m not understanding why that website wasn’t shut down earlier?
What are the steps we can do to take action against sites like AIC?
Yep. The site is down. For the sake of millions hopefully for good.
Not sure why down. I did file complaint to Godaddy yesterday. Hopefully it stays down
Look at allaboutashley.cr – this is the most comprehensive site I have seen so far. It seems to be missing fields for some records, yet more complete for others. Not sure why. Seems professional…..Hope it goes down soon.
Well, they are clearly profiting from stolen data given all the advertisements. Someone needs to locate the domain provider and where the server is located in contact those companies.
http://allaboutashley.cr/ is hosted @ https://hostsailor.com/
abuse@hostsailor.com
Thanks BW
Looks like http://allaboutashley.cr moved to another hosting company after hostsailor suspended them.
They told me their URL is resolving to 46.183.221.171 now.
According to this their now being hosted by ‘Dedicated Servers’ but I can’t seem to find any page for these guys. Maybe some of the more techy guys here will have better luck
http://www.whoishostingthis.com/?q=46.183.221.171
There information can be found and should be found. These people should be outed – just like what they are doing to the people they are outing on their website. Monetizing off of the misery of others is far worse than having paid for a membership to AM. I am sure someone can find them. If so, post their contact information here….
How is this allab******.cr site still up? ANyone have look with Server provider? Anyone check with the affiliate link they are using in the ads they try and display when the check is “loading”? I see Shareasale links there – anyone communicate with Brian Littleton at Shareashare – find out who the encrypted affiliate link belongs to, they have to have some legitimate info at Shareasale to actually get paid off this.
AllAboutAshley.cr is hosted here:
https://www.dataclub.biz/en/support/contactUs
http://whois.domaintools.com/allaboutashley.cr
So why do you post the link…?
Domain name registered at dnsimple.com here in states.
dnsimple owned by Aetrion in Florida. Small firm.
Aetrion LLC
2045 Corey Road
Malabar, FL 32950
3215050025 Is phone. I’m calling.
dnsimple is based in Avignon, France and owned by Aetrion. The president is an American that went to the university of Miami, Anthony Eden. The fact that the company president is an American kids hope that he will do the right thing and take the site down.
Did you get a chance to speak with them?
Any update on this?
Anyone have look with Server provider? Anyone check with the affiliate link they are using in the ads they try and display when the check is “loading”? I see Shareasale links there – anyone communicate with Brian Littleton at Shareashare – find out who the encrypted affiliate link belongs to, they have to have some legitimate info at Shareasale to actually get paid off this.
Nice work everybody! Help please go to pastebin and help me report abuses there to take down their lists!
Like what? I saw Mississippi and LA but they were taken down…
Those were allowed to stay up for a long time and some of them are still available. Disheartening.
Has anyone tested Allaboutashley.cr? Wondering if it’s complete or missing info?
Pastebin had 10 pages full of lists this morning of 12 different states many of them with valid information! Hourly, things get posted there and remain there for many hours. We need to remain vigilant on that site!
check out cheaterscout.com. Probably harvesting emails like trusify.
I don’t understand how Pastebin can allow it to continue to happen. Very disappointing that they allow the trafficking of stolen data. You would think the Feds would halt it. Any thoughts on why it is allowed?
Pastebin is still at it! There are lists this morning that are being posted. Please, let’s all help out and go into the posts and report the abuses to Pastebin.
I agree- we have to stay on top of this
However I am a little computer illiterate (that’s why I’m in this mess) but what is the best way to search. I generally just search pastebin trends and my state…
In Pastebin: Search “Ashley Madison” – sort by date once the 10 pages come up. You can sign up for free. Once you sign up, go to “report abuse” under each post so they can take them down. I have been doing it for every state I see posted, or for every posting with e-mails, even though I am not on any list. I just cannot believe people think this is their business…
I searched Pastebin, but found little. Typed “Ashley Madison” in the search, then sorted by data. Nothing new? Not sure where you are seeing all the posts. Note, there are old posts – but many of them have been removed. There are a few with only email addresses, which I have reported.
Other than that, I am looking high and low for AM search engines. Nothing really credible, except for one. The few that I have searched contain different information on accounts (i.e., some have address and telephone, while others have nickname, name, etc). Its not really consistent. Well, it’s only been less than a week since the data leaked, so it is only a matter of time before someone can provide a comprehensive search of all AM accounts…hoping these sites are taken down, as they violate privacy on so many levels. Sad that there are those out there who seek to monetize on the misery of others. This is a dark chapter of the Internet.
When you type in Ashley Madison into their search bar, 10 pages of posts pop up.
You can also email them directly at admin@pastebin.com
I have been reporting abuse. However, I want to know what we can do to take down some of the search engines that are popping up?
So I never accessed this website but some how my email address was on there… I also got an email from someone at ashley@ashleymadisonteam.com trying to blackmail me saying:
“Unfortunately your data was liked in the recent hacking of Ashley Madison and I now have ALL your information. I have also used your account info to find your Facebook profile, using this I now have a direct line to message all your friends and family.
If you would like to stop me from sharing this dirt with all of your known friends and family (and perhaps even your work too?) then you need to send exactly 1.05 bitcoins to the following address.
Bitcoin Address:
1HexkLpEG4qtZNqrx4cZJ67Y9mH9QmZP3K
You may be wondering why should you and what will prevent other people from doing the same, in short you know to change your privacy settings on Facebook so no one can view your friends/family list. So go ahead and update that now (I have a copy if you don’t pay) to stop any future e-mails like this.
You can buy Bitcoin’s using online exchanges easily. If the Bitcoin is not paid within 3 days of 23-August-2015 then my system will automatically message all your friends and family. The bitcoin address is unique to YOU.
Consider how expensive a divorce lawyer is. If you are no longer in a committed relationship then think about how this will affect your social standing among family and friends. What will your friends and family think about you?
Sincerely,
Guerrero”
I found this in my junk mail today… Should I be worried? I’ve never even used the site before but I don’t want to explain myself to all of my friends and family on Facebook. Has anyone else received this? And is it even possible to do this? Please let me know.
Thanks.
No – I would not be worried. Change your settings now and report this to FB. This is a fear tactic.
Not sure how credible the data collection methodology is, but it made for interesting reading.
http://gizmodo.com/almost-none-of-the-women-in-the-ashley-madison-database-1725558944
I have been sweating for a week now and probably have an ulcer by now. I can’t help but wonder if we are all doomed eventually…
Will there be an easy search engine that can look at names by city? That is probably the way that I will be caught. So far I haven’t found a search engine that does that. All the search engines use email addresses which I luckily used a burner one… I did notice a website that requires a $5 purchase for some software (but I don’t many people will use it for fear of a virus). Obviously we should be listing websites so we can bring them down too
I agree that we should be searching pastebin but I have noticed that the number of views per posting is decreasing as the gen pop’s interest wanes. So that’s a good thing…
Thoughts?
Db – hang in there! That link requires a purchase or a survey to be completed, so it is probably spam. Why require a person to take a survey in order to download a file? It seems extremely suspect to me. Hope you are doing better today. Fight the good fight!
Thanks for the encouragement…I’ll try to calm down. i hate all this worry about something that was so stupid. I know my wife would believe me but it’s hard to defend yourself in the court of public opinion. And I don’t want to hurt/embarrass her for no reason
I think trying to squash these sites is sort of pointless. Are you going to spend the rest of your life trying to run them down? The data is “in the wild.” Someone could sit on it for five years, then just dump it online in a database out of the blue, and you might miss it before your SO finds out.
The key is to find out what, exactly, they have for you. In my case, allaboutashley.cr has revealed that they have my burner email and all my account data. Luckily, it’s all false. The only problem is that it says “possible credit card transactions.” I DID pay for 3 months nearly a decade ago (I have no idea of the actual dates, but I THINK it was pre-2007). It never went anywhere, other than making me feel guilty for considering an affair. But that’s not the point.
If that credit card data isn’t in the dump, then I’m in the clear. But if it’s there, I’m assuming it’ll be in the open eventually. Why would AM hang onto it for so long? I closed the account before “full delete” was even an option (I think). Long enough ago that I’d forgotten all the details of the account, and struggled to remember the burner email address. I only used THAT for a few months during that same period.
Like everyone else here, I’m prepared to deal with the consequences of discussing this with my SO if I have to. What I’m not sure how to deal with is the very public embarrassment that my wife and kids may have to face because of a mistake I CONSIDERED making a long time ago. I don’t feel sorry for me. I do feel sorry for them. They did nothing wrong, but are potentially going to be hurt.
If anyone finds a safe, reliable way to find out that information that doesn’t cost an arm and a leg, please let the rest of us know. I don’t have the credit card information anymore, so I need a zip code search or an email search that returns EVERYTHING associated with the email.
Here’s the full rundown for anyone needing the original sources with instructions for use, plus some pretty lulzy stuff on the AM CEO:
http://am.peen.es/
The reason you might want to go this route is that some of the ‘database search sites’ which have been set up are actually another front for the scammers, who will take the email address you enter in their search box and use it to spam/extort you or someone you [don’t] love.
https://www.reddit.com/r/ashleymadisonhack/comments/3hrcux/well_that_didnt_take_long_trustify_attempting_to/
I just read this on pastebin. It said that it was informing SO’s. I’m not sure how they would do that…
Anyway here is the site: http://bit.ly/1JkOzHl
It requires a file download. Has anyone done this?
See my response to your previous post…
Easiest way to stop worrying is to come clean with your SO. It may be an uncomfortable situation but is weeks of fear and loathing better? I was in your boat came clean last weekend and now all is well and actually better. Good luck and hang in there
Fred,
I think your comments are well taken. I was on interestingly enough almost a decade ago in a previous marriage. I actually told my current wife but I still feel quite ashamed (as I should be). Like most,nothing every came of it (a method of escape). I actually had charges against my account later(I had to cancel my credit card because of charges from AM and other illicit sites hitting my card years later) and paid for the hard delete but as they say, you can’t out run your past. I’d be interested in how you found peace.
This message is for Pete, hopefully your still here. It seems our friend from the “Wednesday” site has relaunched under a .xyz domain. Still same crap incomplete info but he should be “quietly” reached out to if you can. The kid needs some guidance.
DD,
I will not pull up the sites and don’t want the names of the sites posted. So I need you to do a quick WhoIs search to identify the domain and server providers. Share with all and the campaign can begin. And perhaps someone can identify the owner.
Pete, right now it looks like the site is down so maybe he got the message. If it goes back up again he’s easy to track…used a very traceable phone # to register domain. That if nothing else proves he’s a probable amateur way beyond his depths hopefully he quits his bs this time. If anything changes will let y’all know & thanks for the response
Great. Thanks for the update DD. Actually hosting a site is far more transparent than just leaking data. More accountability thankfully. We will need to remain vigilant and do whack-a-mole. It is like having the nuclear option. These individuals MAY expose millions but in the process they DEFINITELY expose themselves.
Pete. So his site was back up yesterday with some very complete detailed data data in a searchable database. It looks like he was pulled by his server company but his site says he’ll be back with an off-shore registration. Anyway based on how the site first looked when it popped up it’s pretty evident its the same idiot who was responsible for the “wednesday” site. If you have his info still it would be helpful if you or someone reached out to him to hopefully knock some sense into him. This guy is swimming in some pretty deep water and I think he’s not aware of some of the dangers out there. Lets see if he reappears before he’s fully outed but it wouldn’t hurt to be proactive with tis flea. Thanks
I’m in the same boat as many of you. I was in a lonely time in my life and made the wrong choice to join the site. I can’t even say AM it makes me ill. I never had an affair and thought I unjoined. Now I’m on the list. I used a Yahoo.com email that has been closed for years so I don’t know how I will see the blackmail spam. When I tried the email, it bounced and gave me an error message. I’m sure they can easily cross reference some how. I’m so upset about this I prepped by starting counseling and am thinking of coming clean. My SO and I have had an amazing relationship and she should not have to go though any of this because of my poor bad judgment. Just when you put a horrible mistake behind you your life falls apart. All law enforcement on online sources say don’t respond to these damn blackmailers. Is that what everyone suggests?
Is it a reasonable assumption to assime that of the 30 million men that are a part of this hack that many of them are quite proficient in technology. And that a group of these people could be actively working to stop and bring down the search sites. I would think that this would be a pretty easy task for talented people. Does anyone believe that this is happening?
There is probably some truth to what you are stating. However, just because there is a search site out there does not mean that it is credible or reputable. In fact, most of these are probably run by sleazeballs and the credibility of their data should be questioned. Just because they claim their site can do certain things, doesn’t mean it’s reputable. It’s best to stay off of them, who knows what data they are collecting when you go on to their site.
To further my point. I went on three of these different so called search engines. I typed in the same email address in all three sites. One of the sites that the email was not on the AM list. However, one of the other ones said it was. I recorded that information and in keeping a file of it just to show anyone and everyone how unreliable and sleazy it is. You should do the same.
The “no more” site (don’t want to provide link) is up again with a ton of information. Just posting in case someone knows how to have it takendown or contact host company.
Pete, this site is the “Wednesday” site under a different name. Same Bitcoin donations button, lol and feel of data, and up till today identical incomplete results etc. If you still have his info please feel free to share
I’ve seen this one for a few days, didn’t know it was down at any point. It’s been on the same hosting provider since I first came across it 8/27. Let me know if I can do anything.
The “nomore” site – you can report to:
xyz_abuse@gen.xyz
To report abuse of a .xyz domain, please contact the .xyz Abuse Contact, Grant Carpenter, at xyz_abuse@gen.xyz or 2121 E. Tropicana Ave, Suite 2, Las Vegas, NV 89119