Many news sites and blogs are reporting that the data stolen last month from 37 million users of AshleyMadison.com — a site that facilitates cheating and extramarital affairs — has finally been posted online for the world to see. In the past 48 hours, several huge dumps of data claiming to be the actual AshleyMadison database have turned up online. But there are precious few details in them that would allow one to verify these claims, and the company itself says it so far sees no indication that the files are legitimate.
Update, 11:52 p.m. ET: I’ve now spoken with three vouched sources who all have reported finding their information and last four digits of their credit card numbers in the leaked database. Also, it occurs to me that it’s been almost exactly 30 days since the original hack. Finally, all of the accounts created at Bugmenot.com for Ashleymadison.com prior to the original breach appear to be in the leaked data set as well. I’m sure there are millions of AshleyMadison users who wish it weren’t so, but there is every indication this dump is the real deal.
Original story:
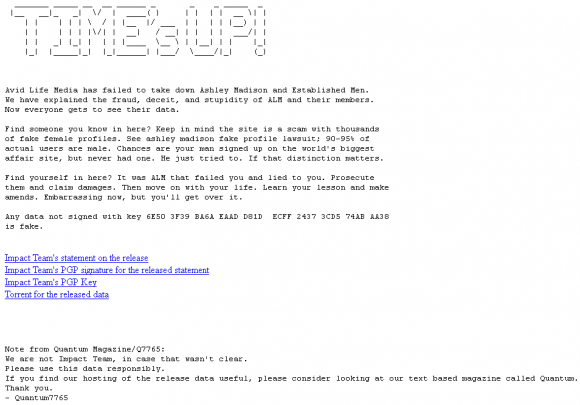
A huge trove of data nearly 10 gigabytes in size was dumped onto the Deep Web and onto various Torrent file-sharing services over the past 48 hours. According to a story at Wired.com, included in the files are names, addresses and phone numbers apparently attached to AshleyMadison member profiles, along with credit card data and transaction information. Links to the files were preceded by a text file message titled “Time’s Up” (see screenshot below).
From taking in much of the media coverage of this leak so far — for example, from the aforementioned Wired piece or from the story at security blogger Graham Cluley’s site — readers would most likely conclude that this latest collection of leaked data is legitimate. But after an interview this evening with Raja Bhatia — AshleyMadison’s original founding chief technology officer — I came away with a different perspective.
Bhatia said he is working with an international team of roughly a dozen investigators who are toiling seven days a week, 24-hours a day just to keep up with all of the fake data dumps claiming to be the stolen AshleyMadison database that was referenced by the original hackers on July 19. Bhatia said his team sees no signs that this latest dump is legitimate.
“On a daily basis, we’re seeing 30 to 80 different claimed dumps come online, and most of these dumps are entirely fake and being used by other organizations to capture the attention that’s been built up through this release,” Bhatia said. “In total we’ve looked at over 100GB of data that’s been put out there. For example, I just now got a text message from our analysis team in Israel saying that the last dump they saw was 15 gigabytes. We’re still going through that, but for the most part it looks illegitimate and many of the files aren’t even readable.”
The former AshleyMadison CTO, who’s been consulting for the company ever since news of the hack broke last month, said many of the fake data dumps the company has examined to date include some or all of the files from the original July 19 release. But the rest of the information, he said, is always a mix of data taken from other hacked sources — not AshleyMadison.com.
“The overwhelming amount of data released in the last three weeks is fake data,” he said. “But we’re taking every release seriously and looking at each piece of data and trying to analyze the source and the veracity of the data.”
Bhatia said the format of the fake leaks has been changing constantly over the last few weeks.
“Originally, it was being posted through Imgur.com and Pastebin.com, and now we’re seeing files going out over torrents, the Dark Web, and TOR-based URLs,” he said.
To help locate new troves of data claiming to be the files stolen from AshleyMadison, the company’s forensics team has been using a tool that Netflix released last year called Scumblr, which scours high-profile sites for specific terms and data.
“For the most part, we can quickly verify that it’s not our data or it’s fake data, but we are taking each release seriously,” Bhatia said. “Scumbler helps accelerate the time it takes for us to detect new pieces of data that are being released. For the most part, we’re finding the majority of it is fake. There are some things that have data from the original release, but other than that, what we’re seeing is other generic files that have been introduced, fake SQL files.”
Bhatia said this most recent leak is especially amusing because it included actual credit card data, even though AshleyMadison.com has never stored credit card information.
“There’s definitely not credit card information, because we don’t store that,” Bhatia said. “We use transaction IDs, just like every other PCI compliant merchant processor. If there is full credit card data in a dump, it’s not from us, because we don’t even have that. When someone completes a payment, what happens is from our payment processor, we get a transaction ID back. That’s the only piece of information linking to a customer or consumer of ours. If someone is releasing credit card data, that’s not from us. We don’t have that in our databases or our own systems.”
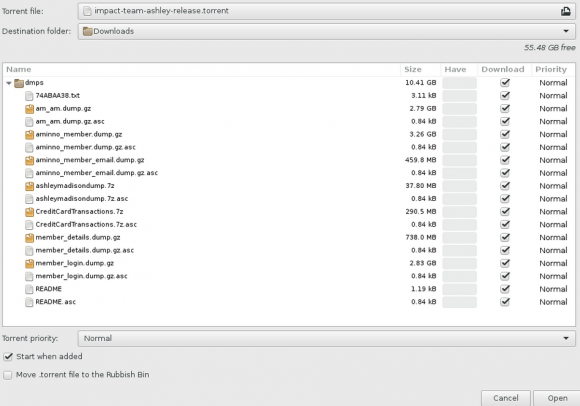
A screen shot of the archive released recently that many believe is the leaked AshleyMadison database.
I should be clear that I have no idea whether this dump is in fact real; I’m only reporting what I have been able to observe so far. I have certainly seen many people I know on Twitter saying they’ve downloaded the files and found data from friends who’d acknowledged being members of the site.
Nearly every day since I first reported the exclusive story of the Ashley Madison hack on July 19, I’ve received desperate and sad emails from readers who were or are AshleyMadison users and who wanted to know if the data would ever be leaked, or if I could somehow locate their information in any documents leaked so far. Unfortunately, aside from what I’ve reported here and in my original story last month, I don’t have any special knowledge or insight into this attack.
My first report on this breach quoted AshleyMadison CEO Noel Biderman saying the company suspected the culprit was likely someone who at one time had legitimate access to the company’s internal networks. I’d already come to the same conclusion by that time, and I still believe that’s the case. So I asked Bhatia if the company and/or law enforcement in Canada or the United States had apprehended anyone in relation to this hack.
Bhatia declined to answer, instead referring me to the written statement posted on its site today, which noted that investigation is still ongoing and that the company is simultaneously cooperating fully with law enforcement investigations, including by the Royal Canadian Mounted Police, the Ontario Provincial Police, the Toronto Police Services and the U.S. Federal Bureau of Investigation.
“This event is not an act of hacktivism, it is an act of criminality. It is an illegal action against the individual members of AshleyMadison.com, as well as any freethinking people who choose to engage in fully lawful online activities,” the statement reads. “We know that there are people out there who know one or more of these individuals, and we invite them to come forward. While we are confident that the authorities will identify and prosecute each of them to the fullest extent of the law, we also know there are individuals out there who can help to make this happen faster.”
Readers should understand that if this dump does turn out to be legit, that just finding someone’s name, email address and other data in the archives doesn’t mean that person was a real user. As the above-mentioned Graham Cluley points out, AshleyMadison never bothered to verify the email addresses given to it by its users.
“So, I could have created an account at Ashley Madison with the address of barack.obama@whitehouse.gov, but it wouldn’t have meant that Obama was a user of the site,” Cluley wrote. “Journalists and commentators would be wise to remember that the credentials stored by Ashley Madison must be considered suspect because of their shonky practices, even before you start considering whether any leaked databases are falsified or not.”




Is there a site where I can search for criteria other than just email address ? Name, address, etc ?
I downloaded yesterday -2- different sets of data. Both had the same file naming and the file sizes were comparable.
While one of the data sets was full of fake data the other one was the real data.
1) I verified by using my own account and my own confirmation mails including my login, my email and my internal user number (that would show on payment receipts). All of this data was not used at any other site. NB: I posted from the mail you will find in the real data set only.
So yes, there is a data set out with -real- profiles.
Only the payment data looked strange, I could not find my transactions and some data would not add up. So yes, the credit card payment log might be false or incomplete.
2) Now to the fake data set: The files looked like the real data files but would include random names and emails. You could tell that easily since it data included:
a) A lot of firstname@yahoo.com, firstname@gmail.com, firstmail@hotmail.com mails. The percentage of people with a “firstname only” free mail was extremely high and mostly common names. Statistically impossible.
b) IP-Numbers were randomly chosen and geolocation of these IP numbers would not match to the profile data. Well, it even included a lot of local range IP numbers (e.g. 192.168.x.x).
c) Payment data included only 3 different email domains for all transactions.
—
For me the reason is clear:
Someone (and in my view Mr. Batia is a very likely candiate) is desperately trying to tell the world the data spreading is “fake” or at least “mixed” and “inaccurate”.
I guess they want to add some confusion so that mainstream media does not now what to write. And it might help some poor guys being caught with their credentials on the real files.
What were the 3 domains? I imagine 2 of them are the .gov and .mil ones?
Where do you go to find the leaked database??? I’ve searched everywhere (so it seems) and all I find are articles about the hack/release overall with no real information
thepiratebay.se
look up “ashley madison”
bhati is a corrupt indian .in usa looking for how to make money,
foo people ..This satan worshipper is very desperate..
But the list will be exposed..
It is a very good deed done by impact team best of luck
Cnet is reporting that Ashley has now confirmed the data dumps valid. Waiting for Brians update which is more reliable.
ole
Took me about 10 minutes using Google cache: “working with an international team of roughly a dozen investigators who are toiling seven days a week, 24-hours a day just to keep up with all of the fake data dumps claiming to be the stolen AshleyMadison database”.
I would be interested in the website as well.
Ha. Love it. Cheaters don’t like it! LOL
Here you can check if an email is in the database
https://ashley.cynic.al/
Can confirm. That email lookup is legit.
Yes. This site does have access to accurate email addresses used by AM customers.
Where can you download
I don’t what to say! I mean, do people really use a commercial internet company to find someone to have an affair with? Now, that’s silly! How about using the real world?
Seriously… where have you been for the last 20 or so years?
Yet another site you can use to test if email is listed in the leaked database:
https://sintonen.fi/ashley-madison/
Notably this tester never posts the given email address as-is, but rather only partial MD5-hash of the email address (calculated locally via JavaScript), thus granting some extra privacy.
Can you search for names anywhere?
How do you read the very large .dump files? I can’t figure out how to analyze those files..
I would like to know how to read the .dump files as well. Anyone?
They are MySQL dumps. You need to setup MySQL, create a database, then restore the tables that are dumped into the files. After that, you can query that database to your heart’s content.
Wow they’re security must have been totally lax to be able to dump the tables, or even access them directly, and export them somewhere.
Thanks for being a trusted source for these stories.
Hey Brian, What can we do as citizens to help stop all these hacks? It seems everything is too anonymous out there on the web. I was thinking of calling my Congressman and asking that VPNs and TOR be made illegal. I like Russia’s idea of having an internet passport. At least the NSA keeps my sex life private.
what a troll.
So based on the update and what’s in the ‘real’ leak, it looks like Bhatia was just lying out his ass? Or does he just not know what they actually store? Or was the hack so deep the hackers had access to the credit card records at the processor sites using AM’s credentials?
Omg Tom Brady is a cheater .
Who knew!
How does one read a .dump file?
If you do not have technical background it will be hard for you to look at the data.
The dump files are MySQL dump files. If you now how to set up and operate a database you can just import the files by executing the file. It will create tables and import the data sets.
If you are on a Mac you can still search within the (text) dump files within the “Terminal” App, e.g.
cat filename.dump | grep -i ‘my@email.com’
Hi. Can you link credit card details to profiles?
Yes, you can link credit card transactions to profiles via the User ID and the email as well.
BTW the credit card data is REAL. Although I could not find one confirmed transaction I now found 5 others. So it might be incomplete – but real!
I’ve also found a transaction that corresponds to me from when I used the site many years ago. I’d like to know why they kept 6-year-old transactions still on their servers.
I found my email address on there but none of the transactions show in the CC files for any dates a transaction was made. Which led me to think the CC data was fake or from another source, however if you have found transactions that suggests it’s real but pretty sure it’s incomplete.
Is there address and full name info with CC imfo
There is if the transaction shows up, name, city/state, country and complete address in a lot of cases. Also shows date, amount paid etc.
Hi Applestar, you seem to be the most knowledgeable person on this thread regarding the data dump, and therefore I was hoping you could easily answer a question for me, since I’m not technically proficient enough to analyze the data myself. Does the transaction files include personally identifiable information regarding people who paid with Paypal?
Thx for your time and consideration!
I’m not technically proficient enough to analyze the data dump myself so I was hoping you could answer a question for me. In the transaction files, is there any personally identifiable information associated with Paypal transactions? Thx!
Need to talk to other people that have been part of this data breach. Email me tutorhelp07 (@at@) gmail(.dot.)com
I wouldn’t dare to commit my details to the care of Ashley Madison. The very thought of my wife’s sisters finding out is too terrifying to contemplate. There, I’m three shades paler already and that’s after only thinking about it.
i downloaded the file 9gb then download zipfile now stuck with dump file so much time vested i deleted everthing who cares to much hasle
It is all real and out there they have everything the credit card info is incomplete (in that it only shows the last few digits) so you are lucky that any criminals cant use it to commit fraud.
If you dont believe me check the arstechnica article.
Funny how the representative is trying to do as if nothing has happend yet.
EVERYTHING IS OUTTHERE!
http://arstechnica.com/security/2015/08/ashley-madison-hack-is-not-only-real-its-worse-than-we-thought/
See for yourself
I downloaded the whole thing; however, 7-Zip File Manager only extracts the .dump files. Not sure how to open them. Is this file the same as a MS kernel dump?
Brian
Any knowledge if pictures and conversations were hacked as well as anyone who used iTunes to pay? PayPal,as well?
That is still unknown.
Pictures are not part of the dumps. The dumps are all mysql database dumps, meaning it’s collections of plain text.
However, given that source code has been released, I wouldn’t be surprised if they have additional zip files of user uploads. This kind of stuff comes in threes and we’re only on round 2…
Wouldn’t it be illegal to download / possess the Ashley Madison data? Even for “research” purposes or to confirm if it was “legitimate”…it’s still a violation of the law to possess it I would wager.
the concept of “Possession of Stolen Property” comes to mind.
18 U.S. Code § 2315 – Sale or receipt of stolen goods, securities, moneys, or fraudulent State tax stamps
more at https://www.law.cornell.edu/uscode/text/18/2315
Which raises a question: how do many people receive the same single piece of property?
The charge might also be
8 U.S. Code § 1028 – Fraud and related activity in connection with identification documents, authentication features, and information
more at https://www.law.cornell.edu/uscode/text/18/1028
Consider too all the sites that allow lookups against the data. Are they criminal?
The defense might be pro bono publico, that it was for the public good to receive that which was stolen for the purpose of analysis and information dissemination for protection of the public. Interesting to note that there appears to be no crime for possessing the fake information.
Consider Daniel Ellsberg and the Pentagon Papers. (yes, I am an eld person, a card-carrying member of the AARP). He stole the papers, but they were later published as a book. Did anyone who purchased the book commit a crime? Don’t think so.
In my opinion (because I don’t play a lawyer on television, even on basic cable) possession is an issue, but the larger issue is what you do with it. Research and journalism have generally been provided a bit of slack, but downloading it to blackmail the people in it is, in and of itself, another crime.
I wouldn’t worry. If you’re a crook, you have a lot of company.
Jonathan @nc3mobi
IANAL, but I can’t think what law would be violated. There are laws against having classified data, but this isn’t (even if some jackasses used their real dot-mil addresses). There are laws against breaking into a system, but that’s no longer necessary.
For all the AM clients freaking out here are a few words to consider and tech experts feel free to comment. It seems to me unless your famous, in some way a celeb or going through a divorce your more than likely “fly under” the radar on this. This is a MASSIVE dump and by my own experiences very hard to access unless you possess more than the average amount of tech aptitude. While this info is going to pop-up in an indexed form from time to time on websites it seems Avid to be doing an excellent job with the ‘take down notices” so it will probably remain in the ‘dark web”. You’re one in 32MM people affected so unless someone is really looking for you, you’re probably in the clear unless you run for political office or something then this will definitely pop-up.
I used a burner but made a single CC transaction. Bummer. What’s the easiest way for me to see if my card details were leaked? I’m no techie either. I’m not interested in anyone’s else’s business. Context is everything. But this is my data and I have a right to know. Now my right to privacy may have gone.
I did exactly the same, checked all the CC files in the dump that were for the dates that I made transactions (and also the day after in case of lag) and none of them contained any of my information. That’s 6 transactions total with no record in any of the leaked CC files.
The only way for you to know for sure is to download the dump and search the CC files for your name or last 4 digits of your card number.
A nasty thought – how easy would it be to create a bogus AM search site for looking up emails, then capture the email address and blackmail the people using it?
Childs’ play for sure.
I never used Ashley Madison, but I just checked my email. (I got a negative response.) If somebody tried to blackmail me, I’d tell my wife what happened, then ignore the blackmailers.
I also checked the email addresses of some acquaintances. I hope they don’t get blackmailed.
@TJ
Nothing has happened, so dont worry no hack has taken place and if they had we would downplay it like in the article it isnt as if we would have an obligation to inform you at all. Right? We only wanted your money and we dindt care to hash or realy secure any sensitive info.
/sarcasme
But you should check out the ars article linked above. It will give you a more complete insight in what really is out there.
LOL. I’ve read the article and its concerning me. My hope is that my one cc transaction is missing. That’s the only valid link to me. I was not stupid enough to use a work email. Although I obviously wasn’t as clever as I should have been.
Ashley Madison Leak Tester has been updated. Now it is possible to check if specific credit card is present in the leaked transaction history.
https://sintonen.fi/ashley-madison/
NOTE: You must type the name as it is present on the card for the check to work.
As usual no card holder name or last 4 digits are being sent to the server, but rather partial MD5 hash is calculated locally instead. The one-way hash is then used to perform the lookup server-side.
@yet another….
How do I know that is genuine? Could be harvesting info. This is a minefield.
@TJ
1) I wrote the web page.
2) Anyone with the technical know-how can view the web page source code and confirm that it does not send the information as-is, but rather the one-way hashed version. This can also be confirmed with any “man-in-the-middle” proxy, such as Burp Suite Professional or for example Fiddler.
I tried it several times. With my burner email only. It just says server not responding.
@Duckface
The site has some issues with at least Safari. If you’re using Safari try the site with for example Chrome or Firefox.
I will try to identify and fix the problem with Safari as soon as possible.
Does this work? Claims to be a name search. http://naughty.invent-stuff.com/
This site looks better to me, as it allows you to search off-line:
http://www.AshleyMadisonUncovered.com/
Seriously !! Install software and pay $5 . Machine will be compromised in a second…
http://Naughty.invent-stuff.com is free. Works to a point and isn’t trying to scam you
http://naughty.invent-stuff.com/index.php?
This link seems only to pull Canadian addresses. I ran a search under “Smith” and I would guess 95% of the names had Canadian addresses. Is anybody else noticing that?