Another charity store chain has been hacked: America’s Thrift Stores, an organization that operates donations-based thrift stores throughout the southeast United States, said this week that it recently learned it was the victim of a malware-driven security breach that targeted software used by a third-party service provider.
 “This breach allowed criminals from Eastern Europe unauthorized access to some payment card numbers,” the company’s CEO said in a statement. “This virus/malware, is one of several infecting retailers across North America.”
“This breach allowed criminals from Eastern Europe unauthorized access to some payment card numbers,” the company’s CEO said in a statement. “This virus/malware, is one of several infecting retailers across North America.”
The statement continues:
“The U.S. Secret Service tells us that only card numbers and expiration dates were stolen. They do not believe any customer names, phone numbers, addresses or email addresses were compromised. This breach may have affected sales transactions between September 1, 2015 and September 27, 2015. If you used your credit or debit card during this time to purchase an item at any America’s Thrift Store location, the payment card number information on your card may have been compromised.”
Nevertheless, several banking sources say they have seen a pattern of fraud on cards all used at America’s Thrift Stores locations indicating that thieves have been able to use the data stolen from the compromised point-of-sale devices to counterfeit new cards.
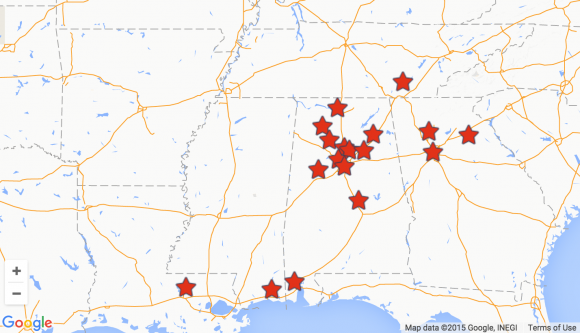
Founded in 1984, America’s Thrift Stores is a for-profit thrift store and operates in the southeastern United States. The company is headquartered in Birmingham, Alabama and operates stores in Alabama, Georgia, Tennessee, Mississippi and Louisiana. According to the company’s site, the organization employs over 1,000 employees and pays over $4 million to its non- profit partners annually, as it turns donated items into revenue for their missions.
The breach involving America’s Thrift Stores comes on the heels of a similar incident at Goodwill last year. That incident was tied back to security weaknesses at third-party payment vendor C&K Systems, although there is no indication yet which third-party service provider may be at fault in the America’s Thrift Stores breach.




This breach angers me more than any of the ones that actually effected me. When I lived in Mobile my trailer burned down and Americas Thrift and St Vincent helped me get back on my feet, Supplying me with the necessities. I know the criminal element has no shame guilt or remorse, but they should. I hope the people responsible understand it is real people that will be hurt by this. some day they will get caught, go to jail and when they get out organizations like this will have to step up and help them. They may not even realize how messed up that is.
They changed the statement link: http://www.americasthrift.com/news-articles/a-statement-from-our-ceo/
Fixed the link. Thanks.
It should be noted that (according to the article so far) this problem has NOTHING to do with any particular OS on any particular machine. There is NO indication at all that any form of update even exists that would have prevented this. What ACTUALLY IS indicated here is that the biggest problems have to do with various levels of access being given to 3rd party (partner/contractor/vendor) businesses. This is also what happened with Target along with so many other retailers.
It’s not just the level of access that they have, but it’s how they don’t protect that level of access, that makes these breaches possible and so damaging.
I guarantee you that the same stuff that happened in the Target breach is present here. Credentials written on Post-It notes out in the open, spreadsheets and Notepad files full of plain text username and passwords, using the same easy passwords across a gamut of operation-critical systems, etc. That Target breach is, and should have been, a huge wake-up call for businesses everywhere to adapt and evolve their IT security practices…
And where can more be found about the particular malware product implicated in this breach? Granted, this could affect further investigation; however, one cannot be protected if one does not know what one is protecting against. “…know your enemy…” –Sun Tzu
Hey Krebs, what’s up with this?
Looks suspicious, especially the lack of a domain name, and your site only started doing this today. Is this an intended change or have you been hacked?
Site is silently eating comments without posting them, even with a note of “awaiting moderation”.
Not sure what you mean. Both of your comments are here on display.
I got a similar error late last night/early am. Firefox blocked a script from running, but when I reconnected using Chrome, I got the page that I expected. I think that there’s a bug in Firefox that’s being exploited by an ex-furry rodent’s ad networks, which is odd because I never allow scripts on those types of sites.
Brian, if you need my IP to investigate, its the same one I’m connected from now.
I’m inclined to say this a false or malicious positive. There is zero third party content on my site, aside from a Google Analytics urchin.
@testing. I am using U-Matrix instead of NoScript. U-Matrix has finer grained control and I am not seeing the IP address you are seeing. However, I was curious. When I looked up that IP address I got :
—————-
NetRange: 64.230.192.0 – 64.230.255.255
CIDR: 64.230.192.0/18
NetName: BEL100704-CA
NetHandle: NET-64-230-192-0-1
Parent: BELLCANADA-5 (NET-64-228-0-0-1)
NetType: Reassigned
OriginAS:
Customer: Bell Advanced Communications Inc. (C00925492)
RegDate: 2004-10-07
Updated: 2004-10-07
Comment: For abuse cases please use
Ref: http://whois.arin.net/rest/net/NET-64-230-192-0-1
CustName: Bell Advanced Communications Inc.
Address: #350-181 Bay Street
City: Toronto
StateProv: ON
PostalCode: M5J-2T3
Country: CA
RegDate: 2004-10-07
Updated: 2011-03-19
———————–
That isn’t the complete record but the rest of it was mostly a repeat of the above record. Not sure what you were seeing. Like you, I find the IP address a bit sketchy.
FWIW, I accessed my site using Firefox and did not get any such alert. Is it perhaps a plugin for FF that is generating this alert?
The only thing I see in your noscript tags is http://s.krebsonsecurity.com/piwik.php?idsite=1 but it maps to a different ip.
So maybe the third party tracking site you use had some sort of redirect temporarily, that noscript saw.
Nathanael A.
I think I know what it is, after retrieving source code of the script it’s injecting and reading that: a well-intentioned, but cack-handedly executed, attempt by the Bell Canada ISP to be helpful by adding a usage meter widget and rollover countdown onto all web pages for a user who is getting close to their data cap.
*Obviously* such a thing should be provided as an optional browser toolbar that can be installed, or not, at the user’s discretion, rather than by violating the “ISPs should just be a dumb pipe” rule. Altering traffic in transit is a big technical no-no and RFC violation for a reason. For starters it fucks up anything that isn’t actually HTTP, but is transferred over port 80. I bet I couldn’t use reader80.eternal-september.org for NNTP until tomorrow for instance.
And of course it’s defeated by SSL/TLS. I’m not seeing it at any HTTPS site, and in a not-necessarily-hypothetical all-TLS world of the near future they’d have to go the optional-toolbar route anyway.
There’s also a moral dimension. As we’ve just seen, it makes other peoples’ web sites look hacked, even when they aren’t, especially when it fails to either work as intended *or* be invisible. (Using a nameless machine instead of something like “usagereport.bell.ca” doesn’t exactly help matters here, and all to save what? Zero bucks, to add one more subdomain to an *existing* TLD you own?)
And of course one person’s helpful usage monitor could be another’s extremely annoying nagging wagging finger. The option to enable/disable such a thing should rest with the user, preferably at a finer granularity even than install/uninstall toolbar (options setting in toolbar? Which can be added as a visible toggle switch to browser button bar perhaps, or removed from it?)
I sincerely hope your not suggesting another toolbar???
I never saw this error so I was a little confused at first. But I have seen where it is a residential account after doing a little googling. I never considered band width caps….interesting. This could either be a someone that wishes to be a big-dog or someone getting careless. I think I never saw any issues because I already have these things filtered out. It sounds to me like the Hosts file works better than Noscript. Ironically, this thread deals with problems from 3rd party issues.
Look for more in the coming weeks. This 3rd party had other customers that were affected as well, though they haven’t gone public yet.
Oh? Is a bank considered a ‘3rd party’?
Banks had nothing to do with this.
A bank wasn’t the 3rd party in this case.
I really hate to say this…. but these breeches are becoming so common that they hardly seem news worthy any more. I imagine that the public figures every time they use their plastic, it is going to be involved in some type of breech. As long as it is not costing big business any staggering sum to correct, it will continue this way into the foreseeable future.
This company is not a charity. They are a for profit.
I concur.
ATS rides the edge of morality in a niche exploit. They need to give just enough to not be accused of being a complete fraud, while raking in huge profit from cheap labor (exploiting the ‘it’s a charity emotional arbitrage), and enjoying low input costs in donated goods.
Nobel prize winning economist Shiller discusses the theme in ‘phishing for phools’ (which appears to be a lousy book but important nonetheless, much like taleb’s black swan).
It is of note that the selective statistics of number of employees and nominal amount ‘donated’ appears designed to deceive. First it plays on emotional heartstrings …holding up the employees as some sort of shield of ‘goodness’ (think of the employment we created!). Second, it obscures that it takes the ‘donation’ number as an income tax deduction. This means they have incentive to donate an unsold desk, marking it’s value at retail, despite it’s actual cost of zero. I suspect given it’s for profit that this has happened. Of course actual cash needs to donated too, and that optimizes taxes and obfuscates the situation further. Third, a napkin calculation of 1000 employees @$12k-15k/yr) makes the donation amount less than 25%of the labor costs, which as noted above are already reduced by exploiting the ‘it’s a charity’ emotion. Given that the items are donated, there is likely a good profit margin in this ‘business’.
Another overlooked aspect is that these sorts of ‘businesses’ compete against the ones that buy or make their goods, and they contribute to the downward spiral of wages. The reduction in taxes puts a larger strain on public finances, welfare, ss etc. And in that regard makes other safetynets weaker. However on the positive side, folks can do what Warren Buffet’s son has called ‘conscience laundering’, namely they can donate some goods, or volunteer to work at these types of places and say ‘i have done my part’. And the folks that received the goods as donations are happy too…though they received something that someone donated, with over 75% friction loss along the way.
To those that think the above a bit wacky, i suggest a review of professor Shiller’s book cited above. In short, folks tend to think of equilibrium supply/demand on price. However, non monetary attributes can be exploited and converted to monetary exploit. In this regard, it’s not all that different than hackers, which makes distinguishing the bad guys from the good guys extremely difficult.
The salvation army is a charity, ATS is not. Though the story is about the hacking, the description produces a distorted view of these types of for profit ‘charities’. i think it was a mistake to cast ATS as a charity as it causes a distraction.
Anyway, that’s my two cents (donated for the public good, at par value of $4 million).
Brian Krebs, Please fix your article. This organization is NOT a charity.
Since no one else has said it yet. Great Response!
I neglected to credit George Akerlof, also a Nobel prize winning economist and husband of Janet Yellen (fed reserve chairwoman) as the co author of the book cited above.
Salient Info:
America’s Thrift Stores: “… malware entered our network through the software of one of our service provider’s systems. This virus/malware, is one of several infecting retailers across North America. …”
ATS did NOT identify the name of the service provider or the malware/virus variant.
Hummm I wonder if it had any relationship with the Salvation Army hack about 6 or so months ago.