Crooks who make a living via identity theft schemes, dating scams and other con games often run into trouble when presented with a phone-based challenge that requires them to demonstrate mastery of a language they don’t speak fluently. Enter the criminal call center, which allows scammers to outsource those calls to multi-lingual men and women who can be hired to close the deal.
Some of these call centers are Web-based, allowing customers to upload information about their targets to a service that initiates the call to a bank, credit provider, shipping company or dating scam victim (for more on the role played by call centers in dating schemes, see last week’s story, Fraudsters Automate Russian Dating Scams). Other call centers require customers to supply information about the target and the needed service via Jabber instant message. This post focuses on Web-based call services.
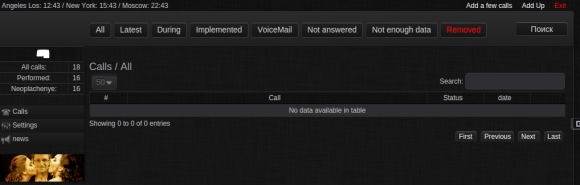
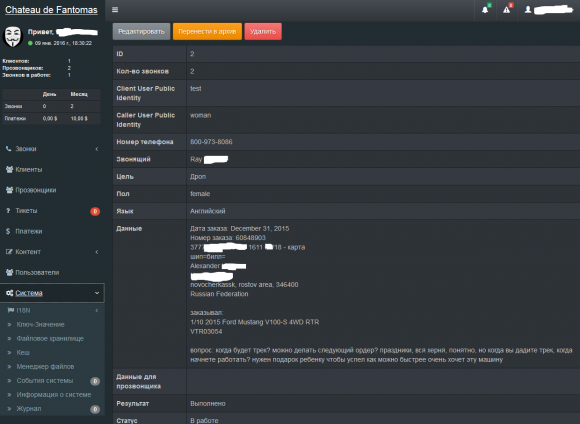
In the call service pictured below, we can see one user ordering a $250 radio-controlled toy Ford Mustang as a gift for someone’s kid for the holidays. The customer of the call service specifies the American Express card account to be used for the transaction, and requests that the order be expedited to a reshipping mule who will forward the goods to Russia. The status of the transaction indicates that this particular order was successfully placed on Jan. 7, 2016.
One of the cybercrime underground’s oldest call center services — CallMeBaby — serves a variety of swindles but specializes in helping criminals cash out dating scams. It charges $10 for each call in English, and $12 for calls in German, French, Italian, Spanish, Portuguese and Polish. Here’s an ad for the four-year-old service, which features an illustration of a blonde woman chatting with President Obama:
CallMeBaby advertises the availability of a male and female to impersonate anyone in the above-supported languages, and operates between the hours of 17:00 to 03:00 Moscow time (business hours in America).
The CallMeBaby Web-based service, pictured below, includes a “urgent” button where paying customers in a special hurry can expedite calls for an extra fee. “Sparta,” the nickname of the cybercrook who runs the service, warns customers that if the call service has to make a second call to complete the transaction because of insufficient information provided by the customer, that customer will be charged twice.
Criminal call service CallMeBaby. The guy pictured between the two girls is NSA whistleblower Edward Snowden.
“If you call the bank it can take up to 40 minutes (during rush hour, getting bank statements sometimes takes a long time),” Sparta says in an ad for his service. “But we will do everything to make your call as quick as possible.”
Crooked call services, like other dodgy online businesses, rely on catchy advertisements and graphic designs to differentiate themselves from other services and to attract new customers. The sketch below — shown from concept to completed product — was commissioned by a call center operator and intercepted after being posted to a file-sharing site online. The image depicts a female call service employee successfully tricking an American Express customer service person into approving a fraudulent transaction.

This image shows a commissioned ad for a criminal call center service, from concept to final design. Credit: Hold Security.
Criminal call centers would seem to be a terrific opportunity for voice biometrics technology, an anti-fraud solution which focuses on building unique voice fingerprints of known criminals and applying special anti-fraud screening to future calls from individuals who match those voice profiles.





Isn’t it fairly easy for LE to find out where these call centers are located? What are the steps the cybercrooks take to prevent their location from being disclosed?
Not so easy. Few call centres nowadays are in one physical location. It’s much cheaper and lower overhead to give everyone a phone and have the PBX route to whomever is free.
I wonder if vulnerable VoIP servers have a part to play in the anonymity of these call centres, ultimately these calls have to route to someone identifiable be it a landline or disposable mobile phone
I think we’ll see security researchers mail these guys at some point
No they dont have to present anything indentifiable in a lot of cases, its entirely possible on some very big names in telecoms sip trunks to present the calling number as whitespace and have the call connect correctly, with the privacy headers set. Its even worse if the call originates from one system, connects to a compromised PBX or SBC and uses that via a proxy which scrubs any of the originating information in the initial SIP invite message.
The issue is that carriers trust the customer to have secured the connection properly, and are stuck in the analog mindset of physical wires connecting buildings, not virtual pipes operating as a layer over public and private packet switched networks, where any weakness in the chain can and will be exploited. A huge number of trunk providers do not support TLS encrypted communications, and EVERYTHING is sent in plain text and unencrypted RTP data. VoIP networks have a security maturity HTTP did in the mid to late 90’s
So essentially they strip out the identifiers between themselves and a compromised system, as the call is established from them to the victim all the in between systems just need to know the next step, I’d guess the first step in the chain is also compromised to the extent any logging is disabled or useless
Which law enforcement, Russian? Do you really think they have any interest in shutting down a local business that’s creating jobs and doesn’t target Russians?
It’s pretty difficult. Cyber crooks don’t use usual means of communication or advertising, usually obfuscating information that would lead investigators to their websites. It’s also fairly difficult to find websites on the “deep web” if you don’t have a pre-arranged list of addresses and what they are. You can use tools like Not Evil search engine to help you find websites with key words but when you consider which region you’re in when searching for these types of organizations, especially russian websites, they’re not at the top of the list. You gotta dig deep.
Handling these kind of business requires an effective approach from effectees and govt agencies as well. I think they can handle them individually.
How much criminals making then??? Isit really worted??
Interesting article as usual, but really enjoyed the AmEx rep having an American Flag and bottle of Coke on his desk. His pet bald eagle is just out of the frame…
His flag is flying backwards (union away from pole)
https://en.wikipedia.org/wiki/United_States_Flag_Code#Displaying_the_flag_outdoors
… When the flag is displayed from a staff projecting from a window, balcony, or a building, the union [stars] should be at the peak of the staff …
Do the “Rachel from Cardholder Services” or “Anne from Account Services” scammers use these call centers, or do they have their own? How about the “Google Small Business Listing” scammers?
> The guy pictured between the two girls is NSA whistleblower Edward Snowden.
ZOMG can you post a higher-resolution copy of this image? I so want it.
It’s such a nice touch !
It’s a cruel world. The saddest part of this story, which I don’t know if anyone’s talked about it yet, is the women that are being employed by these scammers to do their “illegal” (depending on country/jurisdiction) activities.
I know that some of these women may not want to make money in this way by scamming other guys halfway across the world, but they need the cash, and number two, you never see the victim face to face, making the crime feel “less guilty”… but I wonder how some of these women actually feel about this. It would be incredible to interview one of them.
This shows how huge the “underground economy” of cybercrime is, in some countries in the world. In some European countries I’m betting that i’s not so underground. While the US is all up in arms over the new “sharing economy” there are other countries who have no ethics at all and fully embrace the new “cybercrime economy” all in the name of money.
On the other hand I feel no sympathy for the stupid chumps who would fall for such a thing…
Sympathy for the criminals, but not the victims. Got it.
Remember though, victims might have mental disabilities, or just be old
”Sympathy for the criminals, but not the victims. Got it.
Remember though, victims might have mental disabilities, or just be old”
Japan or USA, bastions of capital, and why would capital place cash in the hands of the mentally disabled or decrepit?
Oh yeah…. pooooor innocent women… They probably all have a gun pointed at their head by an angry and threatening man while on the phone pretending to be someone else.
Funny though: Every time I see a documentary or a journalist with a hidden cam, there’s always a woman in the leading pack, giving the instructions. (Whether it’s a prostitution ring, fraud or eastern europeans wives to be married.)
But hey! Gotta feed their 15 kids someway or another, right?
”It’s a cruel world. The saddest part of this story, which I don’t know if anyone’s talked about it yet, is the women that are being employed by these scammers to do their “illegal” (depending on country/jurisdiction) activities. ”
wow you’ve really fallen for that amy schumer line of dribble.
And the God said… Hades go and make them suffer until they start looking up to me again then I come and throw all the demons for ever into underworld and it will be golden age for ever but the mankind have become mature enought:) well the alll what we see round us today it’s all predicted ages ago people just don’t undestood what means God and who is God
Hard to understand it when its proponents make no sense
Blacklisting has high overhead. I prefer whitelisting. I sue this for email and financial institutions should start to capture a biometric voice print of the card holder, so that if it does not match, it does not complete.
Seems to me one easy way the credit card companies can get around this problem under most circumstances is to have a system which calls the customer back after the original call to customer service to confirm the transaction (or just have the CSR call the customer back). Unless the crook has hold of the customer’s phone then the transaction won’t get approved. You’d also want to check to make sure that the phone number on file hasn’t been changed in say the past couple of weeks (and if it has then the CSR needs to be extremely suspicious of the request).
Nice read! That’s one of the reasons why we’ve created http://www.iamreal.me
Why government is not taking action against CallMeBaby? They are helping swindlers and everyone knows it yet they are still not caught for their wrong deeds.