The American Dental Association (ADA) says it may have inadvertently mailed malware-laced USB thumb drives to thousands of dental offices nationwide.
The problem first came to light in a post on the DSL Reports Security Forum. DSLR member “Mike” from Pittsburgh got curious about the integrity of a USB drive that the ADA mailed to members to share updated “dental procedure codes” — codes that dental offices use to track procedures for billing and insurance purposes.
“Oh wow the usually inept ADA just sent me new codes,” Mike wrote. “I bet some marketing genius had this wonderful idea instead of making it downloadable. I can’t wait to plug an unknown USB into my computer that has PHI/HIPAA on it…” [link added].
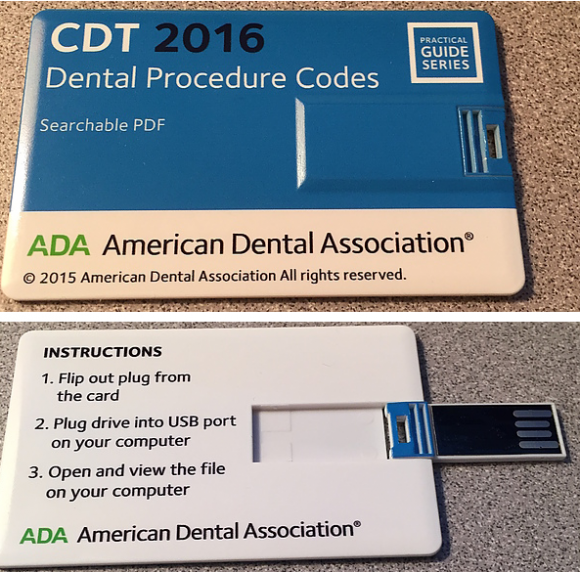
The ADA says some flash drives mailed to members contained malware. Image: Mike
Sure enough, Mike looked at the code inside one of the files on the flash drive and found it tries to open a Web page that has long been tied to malware distribution. The domain is used by crooks to infect visitors with malware that lets the attackers gain full control of the infected Windows computer.
Reached by KrebsOnSecurity, the ADA said it sent the following email to members who have shared their email address with the organization:
“We have received a handful of reports that malware has been detected on some flash drives included with the 2016 CDT manual,” the ADA said. “The ‘flash drive’ is the credit card sized USB storage device that contains an electronic copy of the CDT 2016 manual. It is located in a pocket on the inside back cover of the manual. Your anti-virus software should detect the malware if it is present. However, if you haven’t used your CDT 2016 flash drive, please throw it away.
To give you access to an electronic version of the 2016 CDT manual, we are offering you the ability to download the PDF version of the 2016 CDT manual that was included on the flash drive.
To download the PDF version of the CDT manual:
1. Click on the link »ebusiness.ada.org/login/ ··· ion.aspx
2. Log in with your ADA.org user ID and password
3. After you log in you will automatically be directed to a page showing CDT 2016 Digital Edition.
4. Click on the “Download” button to save the file to your computer for use.If you have difficulty accessing or downloading the file, please call 1.800.947.4746 and a Member Service Advisor will be happy to assist you.
Many of the flash drives do not contain the Malware. If you have already used your flash drive and it worked as expected (it displayed a menu linking to chapters of the 2016 CDT manual), you may continue using it.
We apologize if this issue has caused you any inconvenience and thank you for being a valued ADA customer.”
This incident could give new meaning to the term “root canal.” It’s not clear how the ADA could make a statement that anti-virus should detect the malware, since presently only some of the many antivirus tools out there will flag the malware link as malicious.
In response to questions from this author, the ADA said the USB media was manufactured in China by a subcontractor of an ADA vendor, and that some 37,000 of the devices have been distributed. The not-for-profit ADA is the nation’s largest dental association, with more than 159,000 members.
“Upon investigation, the ADA concluded that only a small percentage of the manufactured USB devices were infected,” the organization wrote in an emailed statement. “Of note it is speculated that one of several duplicating machines in use at the manufacturer had become infected during a production run for another customer. That infected machine infected our clean image during one of our three production runs. Our random quality assurance testing did not catch any infected devices. Since this incident, the ADA has begun to review whether to continue to use physical media to distribute products.”




It would have been nice of the ADA to
1) get a sample of the malware
2) upload it to virustotal.com
3) provide the link to the VT results in the email
4) advise anyone who opened the file to
4a) confirm the date they opened it
4b) the AV they run
4c) confirm the AV would have detected the malware by the date opened OR
4d) if NOT protected – follow their incident response plan for malware. I am SURE all dental offices have this…I mean what could go wrong…and highly technical and malware removal process or willing to wipe and install new…
LOL No. The ADA is not interested in going to extra lengths to clean up the actual problem, only to do damage control from a marketing and image perspective. This is not meant to be a criticism of the ADA in particular, this is the usual reaction of any large corporation or association or group. So when you see it, know that that’s what it is. Why else would they claim “Your anti-virus software should detect the malware if it is present” implying 100% of the time when they know good and well it’s only a small percentage of such anti-virus software will catch it… such lying and bending of the truth is indicative.
I like how they tell members to just throw the flash drive away versus destroying it or the like.
My thought exactly. Stupidity, Part II.
I’ve never destroyed a flash drive before, what’s the most practical way?
Snap it in half, hit it with a hammer, give it to a goat.
Putting it in a washer and dryer may not hurt it (experience).
Personally, I would format it and use it. (formatting system has a read only drive/CD)
I eat them.
Destroying Flash drives…
Personally I’d recommend a 5lb pound sledge hammer. Or you could always Burn it (or Shred it if you have the equipment).
(But there was the one my daughter ran through the washer and drier by mistake, it was thoroughly dead too.)
Well that was a very sensible response, In reality, drilling holes through them is probably safest. flash drives can take a lot of physical damage before they stop working.
Or eat them. 🙂
They like to microwave things on the show Mr. Robot. Does that actually work?
Yes, but at the risk of damaging the microwave.
So the ADA is generating more e-waste.
Well…
A microwave is nothing more than an EM-Generator. Higher frequency than a Radio Tower, but at a lower transmission power.
As we all know “EM-Pulse BAD”, but HOW bad largely depends on the electronics and the design. With Solid State Devices, it can be quite borderline. On one hand, you lack inductors, which are the principal components that “receive” the EM energy. (Yes, the PCB can also act as an antenna, as can dozens of other components, just that inductors can cause bigger problems.)
BUT, CHEAP Solid State Devices are significantly more vulnerable to voltage spikes which can cause damage to internal components. This deals more with cheap interconnects that break due to the electro-motive force (basically, electric flow can cause the atoms in the interconnect to move). Or even simply due to shear heat (large current can melt the interconnect).
There is ONE THING to keep in mind though, even if the device, when plugged in, doesn’t work… it doesn’t mean I cannot open it up, unsolder (though, I really would use a heat gun here since it is likely ball grid array) the NAND chip and, after using a new interface, be able to read off of it.
Of course, after that, we’re talking about using an electron microscope to read the state the device is in and admitting additional losses while breaking it out of the protective casing… but yeah.
Best solution? Drill. Drill directly into the chip.
But if you AREN’T paranoid, you could simply do a low-level format and be content that the likelihood of anyone even guessing that a zero use to be a one is minuscule and would require an electron microscope just to see the effects of residual charges.
of course, if you’re still paranoid, you can format it to ones, then format to zeros, and then format to ones until the drive breaks into little tiny pieces.
The clueless leading the blind, or vice versa.
So many things wrong with this program. Why distribute physically when they can do so from a secure portal – which is plan B that they have gone to anyway? Why increase cost by distributing physically? Manufacture USB drives in China (known manufacturing malware insertion) and send to entire membership? No testing?
Clearly, the marketing dept was in charge without any risk or info sec review of process and procedure.
Will be interesting to see what the fallout will be. We will hear in a few months about dental office breaches with both PCI (credit card) and HIPAA (PII) concerns.
> Manufacture USB drives in China (known manufacturing malware insertion) and send to entire membership? No testing?
They did random sample testing, but because only some of USB drives were infected, it didn’t caught the problem.
I beg to differ and to believe they didn’t check a single one of them… Given how much of a s**t they seems to give about security…
Clearly true. They would just have outsourced quality control to their manufacturer.
Therefore their statement isn’t necessarily untrue- it’s just the same manufacturer that caused the problem in the first place…
How about not purchasing such devices from China-based vendors in the first place?
where do think all usb drives are made?
Because that would cost more.
Also not a perfect solution, because malware infects people and factories in US too.
I knew there was a reason I didn’t trust dentists.
You’re an anti-dentite!
You just need a shnickle of AV.
“thank you for being a valued ADA customer.”
I don’t know how it works; do the dental offices even have a choice?
Nope, they have to have the current CDT codes to bill. It’s a racket, like many things in the medical/dental world.
Billing codes are like short hand for efficient communication. Like telling other musicians what key/mode you’re playing in so you don’t have to talk for 10 min with the band to play along.
And these are the guys and gals who access my teeth regularly? Yikes!
Yikes is right! I think the fillings my Dentist recently put is are now transmitting skimmed data. Lucy Ricardo was right all along!
OMG! now they know what I eat.
So what if they plug in the USB and AV doesn’t detect malware but the USB is infected?
Or you plug in the USB and later and AV detects malware?
What if in 6 months, people in offices across the country run into identify theft issues or experience spear phishing attempts?
Sheesh!
Usually, this goes like this:
1- Statement out with: “We take security seriously…”
2- “Free identity theft services for 1 year! yeah!”
3- They wash their hands
Rinse and repeat the above…
I have a VISA card that gets shut off almost every time I leave town. I have to call them to get it re-activated. They keep telling me how concerned they are about security.
Last time was in Vegas. I purchased the airline tickets with the card and they thought it was unusual activity when I used it during the trip a month later? It’s starting to pi$$ me off.
Received a new replacement last month as the old one had expired. The new card is a swipe card – no chip. Hey VISA! Could you tell me again how concerned you are about security?
Just to be fair. Whether you get a swipe only or a chip and swipe card is up to the bank issuing the card, not Visa / Mastercard. Who is the issuing bank?
That said, its crazy all cards in the U.S. (especially newly issued ones) aren’t Chip at this point (not that it would have helped at Target cause it wouldn’t have). Have a relative who still has a Visa that is still swipe only…seems crazy at this point let alone a newly issued credit card.
Course her credit card processing at the terminal is much faster than mine with the Chip.
Actually, I would contend that swipe is the superior technology any day of the week.
See, Chip and PIN has a major fault that no one is willing to admit.
There is NOTHING stopping the machine from requesting a second “transaction” number.
Take a moment to understand this, Chip and PIN claims that by having unique transaction numbers, someone cannot skim your magnetic strip and keep doing charges. This sounds all dandy, but all it really does is change the attack vector while giving a sense of false security to the public.
This isn’t to say that the idea is bad, just that people ignore a few truths:
1) Open Source Software makes it extremely easy for people without any formal education to do criminal actions.
There is a large portion of the open-source community that clearly believe that “someone is going to do this, so might as well be me so I can get internet fame points!” and use that as an excuse for lowering the bar for criminal enterprise to use their tools in the wrong way.
2) The Open HARDWARE movement (especially the MAKE movement) makes it insanely easy to get something working quickly.
An RFID skimmer? Sounds hard right? Except the arduino can be used to make it, and they even have a cheap reader that anyone can afford!
Now, reading the chip? it honestly isn’t going to be terribly difficult, can probably use the arduino but may need a multiplexer there… but again, I’d bet someone has done it and put online how to make it; possibly are even selling kits!
3) It isn’t the 1920’s anymore!
I am TIRED of the “bad guys are stupid” trope. It has never been true. You can defeat ADT with a $20 frequency jammer because they moved from a wired network to a wireless network. You can defeat most door / window sensors with a simple neodynium magnet… and NOW we’re saying “Look how secure we are, you’re letting ADT 24/7 access to all your locks, cameras, lights….
I mean, if you used “NSA” instead of “ADT” perhaps you idiots would recognize just how IDIOTIC this future you’ve created is. (And all it takes is one inside person; or just the know-how to capture network data for a couple of weeks and then decrypt the security codes (even rolling pseudorandom codes can be decrypted with enough capture and knowledge of the system.)
What I am really getting at here is that Chip and PIN doesn’t offer any additional security while giving the ILLUSION of additional security; and that causes a failure in the human systems regard which gets people to let their guard down.
Just FYI. For kicks, I took a earbud, wrapped it up in electric tape, and taped it to one of those RFID soda machines. (Right under the RFID reader). I left the wire, which I ran to the backside of the machine and had an old tape recorder plugged in… TECHNICALLY, it is possible to pick up radio frequency communications this way; but I was just trying to make it look like the device was tampered with.
It stayed there for 3 days… I don’t know who took it, but the supposed “security” of RFID being “short range” should really have clued people into a device taped right under the RFID reader.
*Just a small note on the technicalities here.
While an earbud is not the best tool here; if you have an antenna that peaks at the proper frequencies, you could actually use a tape recorder to capture the transmission data. Using a digital recorder can cause problems if you don’t have the option to record in WAV (or other true lossless formats); and this isn’t to say that the fidelity of the tape / tape recorder doesn’t come into play here either.
The point is that the antenna can be tiny, and earbud size really isn’t stretching it. Yeah, you probably want to amplify the signal before pushing it down the transmission line, due to how small it is, but that really doesn’t make it too much bigger.
And the “capture device” doesn’t have to look complicated either. Just remember that simple simply works.
(Hmm, thinking about this… it might be possible to make something about the size of a pen… which we can then put into a pen!)
You know the chips aren’t RFID, right? They are NOT contactless – that’s why the new cards have the contact pad on them above the first 4 digits.
You can check this for yourself with any android phone with NFC capability and some free software.
“root canal”
oral pathology
microabrasion
treatment preauthorization
panoramic radiograph
permanent dentition
reimplantation
osteotomy
viral culture
https://www.youtube.com/watch?v=Jz_MdtaJtns
Like I always say, the worst day infecting the thumb drive manufacturer is better than the best day phishing. Or something like that.
” Since this incident, the ADA has begun to review whether to continue to use physical media to distribute products.”
The correct review conclusion would consist of one, single word: “No”.
That would have be the proper conclusion many years ago, it is a common complaint about CDT codes. Before this they were sent on CD – consider how many dental offices are now full of computers that lack CD drives because that is where the market has landed.
If as per Brian’s article, the usbs were infected from another customer’s run, I am guessing some folks might be interested in who they were, and who the subcontractor was, etc. As it seems a bit wider than the ADA.
You got that right. How about it Brian, more info on the infection vector & other info please.
That info can be found just by following some of the links in the article.
As a dental IT tech, I can assure you that the majority if not ALL practice management software is manufacturer updated with CDT codes yearly at a minimum as long as the practice keeps their PM software service agreement. Any practice that still has to use the manual to look up codes is really an office I don’t want to be a patient at.
And a dentist using infected code lists is one I wouldn’t want to frequent, either…
I called my dentist to tell him about this and krebsonsecurity.com. He said his practice software automatically updates the list of codes, but he usually buys the list from the ADA every couple of years so that he can access it quicker.
Man, this makes me feel so much better about MY organization (which I thought was pretty dumb)….
Don’t the dentists need to load the dental procedure codes into the dental practice software they are using ? They do that with a pdf ?
I am just wondering how often it is actually used.
The entire thing sound completely ridiculous to me.
I can already see the setup for next year’s Dental Codes distribution. The Email: “For your safety, we have attached the 2017 Dental Procedure Codes as a PDF file”.
Of course, that email will be from the bad guys…
Or…
“Please click the link below to download the 2017 Dental Procedure Codes.”
Totally teed up for next years update for e-mail phishing. Heck with this, its teed up for e-mail phishing right now.
While online access is very good for something like this….
We still need a safe standard for a “physical” file distribution method as USB was created way back (Win 95 days?) before security was much of a concern and is fundamentally broken by design.
CD’s / DVD’s with autoplay off seems the only safe alternative at this point for physical distribution…regardless of laptop makers phasing the drives out ASAP.
You are a bit behind the times. Autorun automatic running has been disabled for a while (since like vista). And that wasn’t the issue here. The issue is that if they try to use the launcher, it will send them to a malware site.
Autorun is not necessary anymore with BadUSB firmware hacks easily available.
Gotta love the advice “worried about hackers? Just download this PDF!” Facepalm…
Thank you, notified my dentist.
Let’s see, hire a sketchy Chinese firm to mass produce cheap USB drives that I intend to distribute to thousands of organizations, each of which would be considered a target-rich environment when it comes to identity theft…
What – could – possibly – go – wrong…
This type of breach is why I refuse to disclose my social security number to medical and dental practices.
As a general note, by using ‘random’ sampling for known non-normal distributions (i.e. their small number of series) strikes me that they are confessing they do not understand their process as their process is anything but normal bell curve data. (One might do random sampling of each production line/run for example, yet it sounds like that is not the case, and at this point it is such a mess i doubt it matters anymore). I am sure the statisticians can elaborate on this better than i can.
Or more humorously, if it was not so sad, ‘random quality assurance testing’ is an oxymoron more precisely stated as ‘blind flailing in the hope we stumble on the right answer’.
SMH
OK why doesn’t my question about why do they have a login for this info seem to post???
Anyone know what malware domain it attempts to reach? I want to be sure it is in the blocklist for my clients.
Can we find out from the ADA which vendor they used to make these? We get offers almost daily, from multiple companies, about “the benefits of USB marketing.”