Crooks who deploy skimming devices made to steal payment card details from fuel station pumps don’t just target filling stations at random: They tend to focus on those that neglect to deploy various tools designed to minimize such scams, including security cameras, non-standard pump locks and tamper-proof security tape. But don’t take my word for it: Here’s a look at fuel station compromises in 2016 as documented by the state of Arizona, which has seen a dramatic spike in fuel skimming attacks over the past year.
KrebsOnSecurity examined nearly nine months worth of pump skimming incidents in Arizona, where officials say they’ve documented more skimming attacks in the month of August 2016 alone than in all of 2015 combined.
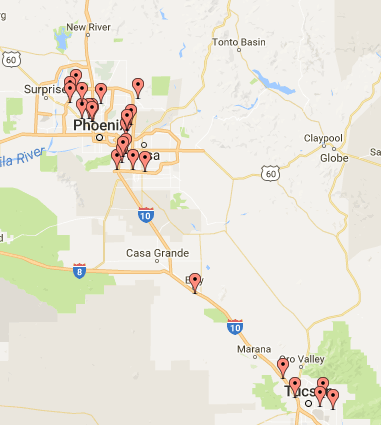
With each incident, the Arizona Department of Agriculture’s Weights and Measures Services Division files a report detailing whether victim fuel station owners had observed industry best practices leading up to the hacks. As we can see from the interactive story map KrebsOnSecurity created below, the vast majority of compromised filling stations failed to deploy security cameras, and/or tamper-evident seals on the pumps.
Fewer still had changed the factory-default locks on their pumps, meaning thieves armed with a handful of master keys were free to unlock the pumps and install skimming devices at will.
These security report cards for fuel station owners aren’t complete assessments by any means. Some contain scant details about the above-mentioned precautionary measures, while other reports painstakingly document such information — complete with multiple photos of the skimming devices. Regardless, the data available show a clear trend of fraudsters targeting owners and operators that flout basic security best practices.
Indeed, the data assembled here suggests that skimmer thieves favor off-brand filling stations and target pumps furthest from the station/closest to the street. Also, all but three of the 35 incidents included in this report targeted fuel dispensers made by one manufacturer: Gilbarco — probably because the skimmer thieves responsible were armed with a master key for Gilbarco pumps.
In only one documented skimming incident did the station owner report having used non-standard pump locks. In some cases, the same filling station was hit with separate skimming attacks just a few months apart.
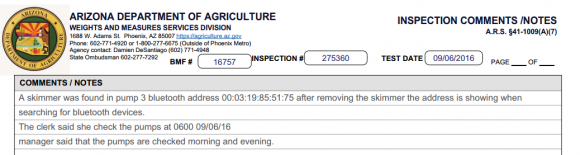
A portion of the incident report for the Bluetooth skimmers found at a gas station in Phoenix on Sept. 6, 2016
Investigators also appear to be increasingly finding pump skimmers that employ Bluetooth wireless technology. Bluetooth-based skimmers allow thieves to collect stolen card data merely by pulling up to a pump and downloading it with a Bluetooth-enabled laptop or mobile device (as opposed to taking the risk of re-opening the pumps to retrieve the siphoned card data).
A review of the locations of the skimmed stations suggests that skimmer scammers prefer poorly secured stations that are quite close to a major highway, no doubt so that they get away from the station relatively quickly after the skimmers are planted. It’s unclear whether the skimming attacks documented here are the work of one or multiple scammers or gangs, but the activity pretty clearly shows a focus on stations directly off the main arteries from Phoenix on down to Tuscon.
In some of the images in the slideshow above, it may be difficult to readily tell among the jumble of wires which bit is the skimmer. When in doubt, look for an area wrapped in black or grey colored electrical tape, which seems to be found in nearly all of these pump skimming attacks.
Arizona is almost certainly a microcosm of pump skimming activity going on nationally. Last year, KrebsOnSecurity ran an in-depth piece profiling a U.S. Secret Service task force that’s been battling a surge in pump skimming scams perpetrated by organized crime gangs in and around Los Angeles. Other stories on pump skimmers can be found in this search link.
Consumers should remember that they’re not liable for fraudulent charges on their credit or debit cards, but they still have to report the phony transactions. There is no substitute for keeping a close eye on your card statements. Also, use credit cards instead of debit cards at the pump; having your checking account emptied of cash while your bank sorts out the situation can be a huge hassle and create secondary problems (bounced checks, for instance).
I realize that the project above — made with the free StoryMap tool from Northwestern University’s Knight Lab — may be difficult to view comfortably within the confines of this blog. Here’s a direct link to the full map and timeline.




I have a feeling that the vast majority simply won’t make the October 2017 EMV deadline, at least if the gas pumps around here are any indication. How many are going to stop offering pay at the pump altogether as a result?
The gas stations around me have responded to skimming by giving a discount to people who pay in cash vs. credit. A few of them have taken the additional step of disabling the on-pump card readers and make you go inside.
OTOH both these measures could be to try and drive up sales of their overpriced store items.
That discount isn’t from skimming.
That’s done as a matter of course at the vast majority of gas stations. That’s because credit/debit cards charge a per transaction fee as well as a percentage of each transation. That’s nationwide, doesn’t just apply to gas. Like if you buy something at walmart, they card company takes a couple percent off the top.
Yup – that there is what you could call a ‘corporate tax’ since it affects not only cardholders but also those who pay in case since retailers often are raising the prices of everything for everyone regardless of payment method in order to pay that corporate tax.
While true, the handling of cash has its own overhead. Sometimes that “couple of percent” is less than the cost of counting, securing, and depositing cash.
It’s a few things. One, gas stations generally use gas as a loss-leader or break-even sale to drive people into the convenience store (and car wash, etc), where they actually make money. The average station profit margin on gas is usually only a few pennies per gallon. I’m interested to know if these stations are violating their credit card merchant agreements, which generally prohibit a merchant for offering better pricing for certain cards or cash – that being said, gas stations get a lot of special treatment from credit card companies (the Oct 2017 deadline for EMV vs. 2015 for everyone else being an obvious example).
Gas stations were able to negotiate with the credit card companies to allow them to offer a lower price for cash transactions vs credit card. This was partly because of the higher price of gas when it was up to $4+ per gallon and the decreasing margin when credit card companies were making more money per sale because they are percentage based, and gas stations were being heavily scrutinized for price gouging so they had to keep their prices low.
Cumberland farms has introduced a program where you sign up to have the sale drafted from your checking account via ACH which is much cheaper for them to do, therefore you save 10 cents per gallon all the time. This also alleviates the concerns for skimmers because I never swipe a card, I simply use an app, sign in, input my store and pump number, and I am good to go. Its a pretty good system and is a win for both the customer and the gas station.
Oh yeah! Direct ACH access to my bank account. BINGO – all money gone.
This is a part of why WalMart’s MCX effort failed.
The answer is NO !! NO direct ACH access.
I go to Cumberland Farm for gas because they are the only one capable of using NFC for gas transaction which I go in the store to initiate the transactions. So far, I never had a problem. I have been doing this for three years.
One time, I had one customer was using the app and held up the line because of data connection was taking too long and the cashier had to ask him if others can forward while he waits.
A merchant is allowed to offer different prices for cash/credit if all the products they offer discounts on are labeled with both prices.
So for gas stations, they can show the cash price and the credit price for the 3 gas brands. But for the food items inside the convenience store, no discount is offered for cash.
The reason that station owners got an extra year to become EMV compliant is that to retrofit a gas pump to support EMV can run $10,000 – $15,00 per pump compared to an inside pin pad that sell for hundred of dollars.
As someone else noted the station owner makes pennies per gallon so this is a high expense and I suspect EMV upgrades at the pump will take some time. Also once the EMV date occurs the retailer becomes liable for card fraud not the card brands so expect to see a huge impact on these retailers, many of whom are small business owners who may end up going out of business which will not be good for any of us.
The best way to protect from skimming was previously noted: pay inside and watch your credit card statements.
How do you think, Brian, are these Russian hackers Hillary “Rotten” Clinton are speaking about really exists?
I recently filled up at a Chevron station in San Francisco that had NFC wireless payment functionality. Finally, a way to remove physical cards from the gas pump fraud equation completely!
At least here in Europe NFC payment is limited to 25€ (about $28). You can’t buy a lot of gas with that amount of money.
This is not correct. Above 25 EUR (or other local value) the customer ist required to enter a PIN as CVM. The threshhold you mention is just for non-CVM contactless transactions.
http://www.nfcworld.com/2015/09/08/337579/high-value-contactless-payments-available-across-europe-in-2017/
The limit is apparently 30GBP (~35EUR) in England under certain circumstances. And slated to rise.
Whenever possible, I buy gas at Chevron and pay inside with Apple Pay. Most secure way to do it.
Keep an eye out on credit card marketing too as you will notice they are now allowing options to block and turn off your credit card. Why is this important?
In time the card companies may start shifting the risk back to the consumer with something like “you forgot to turn off your credit card while you went to bed to block fraud”..so guess what..who might get stuck..just keep your eyes open. That’s how it works with software preferences and settings sometimes:)
That is completely inc0rrect. Card Associations do not allow FIs to push the fraud loss back to the cardholder in cases of fraud. This common misconception has become the norm with media coverage. Read up on Reg E. Only under specific circumstances can a cardholder be liable for a fraud loss, such as untimely reporting of loss or theft after discovery by the consumer.
The federal law doesn’t allow them to do that.
9-27-16
Thank you very much for this article. I called the AZ. Dept. of Agriculture following a local TV news story on AZ. gas stations that had been compromised.
The AZ. Department of Agriculture decided to not release the names of the businesses nor addresses of compromised locations. I asked how consumers who shopped at the locations would know that their accounts had been compromised and then take appropriate action to protect personal financial accounts?
I was told not releasing details, was done to protect the “privacy” of the businesses.
Business 1, consumers O.
Less than one week later I found a skimmer sitting on top of a trash bin at a large national Gas Station-Convenience store chain store. I knew what is was after having reviewed your great articles. I notified the station manager who was probably just over age 21. Should have just called the police. Keep up the excellent work. Thank you !
Arizona Consumer.
My son was called soon after his card was skimmed by 5/3 Bank’s security department. The trigger was a card-present transaction at a beauty shop in a distant state. He was able to decline the charge on the spot as well as another mail order charge and have the card canceled and replaced. Is your bank doing this for you?
That’s interesting. I didn’t know these thieves are actually making a “card” with a mag strip using the stolen data. How else could it have been a card present transaction? I assumed they were always doing card not present transactions.
Michael — Check out this story, which explains in detail what is done with stolen magstripe data.
https://krebsonsecurity.com/2014/06/peek-inside-a-professional-carding-shop/
Since bluetooth is low range, the thieves must periodically come into fairly close proximity (say less than 30 meters) to download the skimmed data. Surely this opens the possibility to detect the bluetooth access electronically and nab the crooks when it happens, if Law Enforcement actually made the effort that is…
I don’t think the police care. This is a property crime, not a personal crime. My understanding is that they focus on personal crimes including crimes connected to drugs.
Most victims do not report to law enforcement unless the bank requires them to. Once their money is refunded they assume it has been handled. I investigate these types of crimes in my current investigation I have over 500 victims but only 3 made police reports.
I remember telling the ADA that the source of my cards information was probably a skimmer. She didn’t seem to understand.
The guy got 7 years for taking my card.
Was pretty simple. After calling the cc company. Called all the local vendors where the $5K was charged. Denied it was me. Given a description of the couple.
One stored called the police when coupled showed up two days later. Police called, I pressed charges.
Important point was in-person transaction and video of the actual purchases.
ne’er-do-well was out with someone else’s card. Gets to add multiple felonies to his CV.
Not possible.
There is no way to know which of the likely several vehicles within that 30m radius is the one responsible for accessing the bluetooth device and so does not provide the probable cause required for law enforcement to detain anyone and search their vehicle.
Unreasonable search and seizure and all that jazz.
There most certainly is. You can triangulate the source of the signal with 3 receivers posted around the station.
Drone, my car offers bluetooth connectivity to its radio. My phone sometimes connects to it so that I can play music through the car’s speakers.
Setting up a computer that searches for active bluetooth connections would be relatively simple, but would give a heck of a lot of false positives for all the BT waves on the air.
That same computer cannot ask the BT connection “are you naughty or nice?” so there’s not any way this would be feasible. I imagine that when the scammer needs gas, he pulls to the pump on the other side of the island, gets gas, and while filling up, (s)he loads their phone with the card data. The person could be calculating their MPG, sending a text, looking up naughty pictures … so phone use shouldn’t be considered suspicious either.
And as the Phisher King said, there are certain laws that police are required to obey to protect us.
Plus I’m not so sure you can’t set your blue-tooth to ignore incoming requests entirely, so they’d be invisible until they pinged the device.
I’m pretty sure you could have a device which listens for a broadcast (or even some odd sequence of broadcasts — a “knock-knock protocol”) before it starts transmitting. It wouldn’t have to be standard Bluetooth protocol, but getting the stack to support it would probably be pretty doable.
Unfair to say law enforcement isn’t working the issue. Like everywhere, its a matter of manpower. Second, the crooks are capable of extending the range of their devices to several hundreds of feet placing themselves in positions not obvious to law enforcement… especially in high population areas.
isn’t there some kind of liability shift to the seller when EMV is not employed, when the card supported it? i thought this is already in effect in the US (it has been in the rest of the world for some time now)
btw the US and a few third world countries are the last ones using magstripes, and are the last resort for criminals wanting to use skimmed cards. if you would stop it, then all of our cards would be safer, not just for people in the US
US petrol stations have until October 2017 for their AFDs to fall under the chip liability shift.
How would the gas station with the skimmer be held liable? The card info is skimmed from the gas station and the purchases are then done somewhere else. The merchant accepting the fake card will be left holding the bag.
Quack, that assumption is ridiculous. In the US, limits on credit card fraud to consumers is a government regulation. The card companies won’t be able to shift the liability to consumers whenever they want regardless of the technology.
Doesn’t the US have chip+pin, or is it actually the chips on the cards being skimmed here?
Sorry, I’m in the UK.
We have chip, but the vast majority of fuel pumps still use mag stripe. And anecdotally, probably half of stores I shop at still use mag stripe.
@Inaya Interesting, in the UK it’s basically impossible to use the mag stripe, everybodys card has a chip.
@Brent Yeah the chip doesn’t protect you online, but it makes it difficult to actually use a chip enabled card in store
Walking into a store and trying to use a card without a chip would probably raise red flags straight away
John, from what I’ve seen even European cards can be compromised. My vendor noticed several European cards being used on my website and they were all fraud. Luckily nothing was processed or shipped out.
Brent – many European cards still have the mag stripe in case they’re used in the U.S. That’s a no-never-mind in Europe of course but if the data is on the stripe then it can be cloned and used in the U.S.
This problem only goes away when the U.S. eliminates swipe transactions – a few years away yet.
Brian, I recall you posted an series about skimmers in Mexico last year back. In that article you mentioned the Bluetooth name which you were seeing was the default Free2Move, which was the default name for a beacon by a company with the same name. Did any of the reports happen to mention the name(s) of the Bluetooth beacons in use in these cases? If so, were they the same device?
Surely this is the work of the Russians, yes Brian? Or will you be blaming the Colombians this time?
Brian,
Do truck stops or diesel pumps get more or less attention from the skimmer fraudsters? Do fleet fuel credit cards present better opportunity to blend into large number of charges or do non-fuel charges against these cards standout, making them less attractive target for these fraudsters?
Gas pump skimmers found in Salem, NH
http://www.wmur.com/news/skimming-devices-found-at-salem-gas-stations/41834694
Even the station employees are often clueless. I found a station like this in CT.
https://pbs.twimg.com/media/CjP2w_LUkAA89az.jpg:large
Got a tweet back from the company and I gave them the location, I was nearby this past week and they STILL haven’t put stickers on properly.
Gas station employees and managers are not hired for their tech-savvy, and in most cases outside of New Jersey are to be manning a terminal inside the building most of the time. Requiring them to monitor for this is a losing proposition. A better answer is to have the card scanning take place inside where the equipment can be controlled, monitored, and examined better.
It is very alarming how this Skimmer thieves carry out their evil acts. The best practice to mitigate against this kind of attacks is routine checks of the pump machine. As a matter of facts, this will give the pump operators meaningful visibility across their premise. Security in itself requires real time event monitoring. In addition, a strong compliance policy should be enforced for pumps station operators to comply with.
This is why I always use a credit card at the pump and not a debit card. If I can’t use my credit card, I go inside and use my debit card. Much easier to contest fraud charges on a credit card as opposed to debit card. Just a phone call and they’re wiped away. I’ve also started using a bluetooth signal analyzer on my phone before I stick my card in the pump and always check the seal. If there’s no seal on the pump, I go down the road and use another station that practices security on their pumps. Can’t wait until gas stations move to EMV readers. Then again, when gas pumps move to EMV readers, there’s still magstripe data on the EMV card that can still be skimmed unless the EMV reader does something to mitigate magstripe skimming too.
Typically when you dip an EMV card, the magstripe is not read, so you’re fine.
I think Brian has pointed out and it’s so true, there will be an INCREASE in magstripe copying at gas-stations and whatnot as EMV closes off the bad-guy opportunities in regular retail. When EMV is finally everywhere, we’ll all be a lot better off.
The *pump* or terminal aren’t reading the stripe, but that doesn’t mean that the skimmer sitting inside the card slot can’t read it. The hardware is still all there, ready to be used, just the terminal isn’t utilizing it if it detects the chip.
That’s how even the chip cards can be (and are) skimmed – the strip contains all the data needed. The fraudulent transactions are then done somewhere in Mexico or Asia where chip & pin cards aren’t available yet.
So unless the banks actually *stop* issuing cards with the magnetic strip (and don’t “helpfully” encode all the information on the NFC chip – some banks are actually *that* retarded!), this will continue, regardless of whether or not the merchants upgrade their systems and switch to the chip use exclusively.
E.g. here in France it is next to impossible to use the strip – and cards still get commonly skimmed and people defrauded because all cards are still issued with the strips.
You may wipe off the fraud if you use a credit card, but the bank will have to pay for it anyway, and you will pay indirectly. There are new rules in Europe limiting the fee on Card transactions. This makes the card schemes much more sensitive to fraud losses. The use of EMV cards and PIN moves the fraud towards card not present (internet) transactions.
An EMV contact reader will normally contain a magstripe reader as well but the the reader should be built in such a way that it is very difficult to insert a skimmer into it. Data shall not leave the reader unless it is strongly encrypted.
We are now seeing the first fuel dispensers with EMV contactless readers. They are easy to eavesdrop but you cannot re-use the information for another transaction as the data contains new random elements every time.
They may be choosing stations close to the highway because the victims would be more likely to be from a different area and would not complain locally.
Since the merchant’s liability shift started in October 2015, scammers have switched to fuel pump due to the changeover in 2017 (they have been given the extension). This is something I expected along the line when the liability shift was enforced.
I myself go in the store to use my NFC phone on POS to pay for gas due to this problem.
For the case of NFC, it only has a range of 2 inches or less for a few seconds for anyone to eavesdrop from afar.
I think I’ll be doing a bit of Bluetooth scanning at the stations I frequent. Is there any reason to see bt devices in an empty gas station?
Costco has an attendant on hand to keep an eye on things. I asked him about skimmers, and he said they check the pumps regularly. Also probably helps that you have to use a membership card and a credit card (unless you’re using the Costco Visa).
Nice to see that you’re back, Brian.
Could y9u de-magnetise the stripe, just some low force magnet, without damaging the chip? If so, there will come a time when this might be a good action to take (maybe not yet).
It is actually quite difficult to alter data on a mag stripe without a card programmer.
So these devices are inside the equipment, correct? How is the consumer supposed to identify this?
Perhaps there could be a laminated picture of the pump telling the consumer what “good” looks like and if it doesn’t look like that, then not to use it??