A decade ago, if a desktop computer got infected with malware the chief symptom probably was an intrusive browser toolbar of some kind. Five years ago you were more likely to get whacked by a banking trojan that stole all your passwords and credit card numbers. These days if your mobile or desktop computer is infected what gets installed is likely to be “ransomware” — malicious software that locks your most prized documents, songs and pictures with strong encryption and then requires you to pay for a key to unlock the files.
Here’s some basic advice about where to go, what to do — and what not to do — when you or someone you know gets hit with ransomware.
Image: nomoreransom.org
First off — breathe deep and try not to panic. And don’t pay the ransom.
True, this may be easier said than done: In many cases the ransom note that hijacks the victim’s screen is accompanied by a digital clock ominously ticking down the minutes and seconds from 72 hours. When the timer expires, the ransom demand usually goes up or even doubles. Continue to ignore the demands and your files will be gone, kaput, nil, nyet, zilch, done forever, warns the extortion message.
See, the key objective of ransomware is a psychological one — to instill fear, uncertainty and dread in the victim — and to sow the conclusion in the victim’s mind that any solution for restoring full access to all his files involves paying up. Indeed, paying the ransom is often the easiest, fastest and most complete way of reversing a security mistake, such as failing to patch, opening a random emailed document e.g., or clicking a link that showed up unbidden in instant message. Some of the more advanced and professional ransomware operations have included helpful 24/7 web-based tech support.
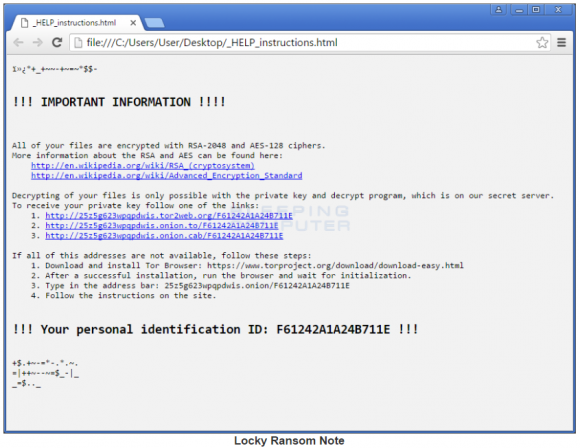
The ransom note from a recent version of the “Locky” ransomware variant. Image: Bleepingcomputer.com.
Paying up is certainly not the cheapest option. The average ransom demanded is approximately $722, according to an analysis published in September by Trend Micro. Interestingly, Trend found the majority of organizations that get infected by ransomware end up paying the ransom. They also found three-quarters of companies which had not suffered a ransomware infection reported they would not pay up when presented with a data ransom demand. Clearly, people tend to see things differently when they’re the ones in the hot seat.
And for those not yet quite confident in the ways of Bitcoin (i.e. most victims), paying up means a crash course in acquiring the virtual currency known as Bitcoin. Some ransomware attackers are friendlier than others in helping victims wade through the process of setting up an account to handle Bitcoin, getting it funded, and figuring out how to pay other people with it. Others just let you figure it all out. The entire ordeal is a trial by fire for sure, but it can also be a very expensive, humbling and aggravating experience.
In the end the extortionist may bargain with you if they’re in a good mood, or if you have a great sob story. But they still want you to know that your choice is a binary one: Pay up, or kiss your sweet files goodbye forever.
This scenario reminds me of the classic short play/silent movie about the villainous landlord and the poor young lady who can’t pay the rent. I imagine the modern version of this play might go something like…
 Villain: You MUST pay the ransom!
Villain: You MUST pay the ransom!
Victim: I CAN’T pay the ransom!
Villain: You MUST pay the ransom!
Victim: I CAN’T pay the ransom!
Hero: I’ll pay the ransom!
Victim: Oh! My hero!
Villain: Curses! Foiled again!
Okay, nobody’s going to pay the ransomware demand for you (that’s only in Hollywood!). But just like the hero in the silent movie, there are quite a few people out there who are in fact working hard to help victims avoid paying the ransom (AND get their files back to boot).
Assuming you don’t have a recent backup you can restore, fear not: With at least some strains of ransomware, the good guys have already worked out a way to break or sidestep the encryption, and they’ve posted the keys needed to unlock these malware variants free of charge online.
But is the strain that hit your device one that experts already know how to crack?
WHERE TO GO?
The first place victims should look to find out is nomoreransom.org, a site backed by security firms and cybersecurity organizations in 22 countries. Since its launch on July 25, 2016, nomoreransom.org estimates that it has been able to save 6,000 victims of ransomware more than $2 million USD to date. Last week the group announced the site is now available in Dutch, French, Italian, Portuguese and Russian.

Visit the Crypto Sheriff page at nomoreransom.org, upload one of the files encrypted by the ransomware, and the site will let you know if there is a solution available to unlock all of your files for free.
Another destination that may be useful for ransomware victims is bleepingcomputer.com, which has an excellent Ransomware Help and Tech Support section that is quite useful and may save you a great deal of time and money. But please don’t just create an account here and cry for help. Your best bet is to read the “pinned” notes at the top of that section and follow the instructions carefully.
Chances are, whoever responds to your request will want you to have run a few tools to help identify which strain of ransomware hit your system before agreeing to help. So please be patient and be kind, and remember that if someone decides to help you here they are likely doing so out of their own time and energy.
HOW NOT TO BE THE NEXT RANSOMWARE VICTIM
Regularly backup your data, and make sure the backups are not connected to the computers and networks they are backing up. Most ransomware variants can encrypt files on any attached drives or network files that are also accessible to the host machine (including cloud hosting and cloud-based backups if those passwords are stored on the machine). Bleepingcomputer’s Lawrence Abrams just published this a nice primer called How to Protect and Harden a Computer Against Ransomware.
Many companies are now selling products that claim to block ransomware attacks. Those claims are beyond the scope of this article, but don’t be lulled into thinking these products will always protect you.
Even products that could somehow block all ransomware attacks can’t prevent the biggest reason that ransomware attacks succeed: They trick victims into taking an action that inadvertently undermines the security of their device — be it a smart phone, tablet or desktop computer.
This usually involves clicking a link or downloading and opening a file that arrives in an email or instant message. In either case, it is an action that opens the door to the attacker to download and install malware.
Remember my Three Rules of Online Security:

…For Online Safety.
1: If you didn’t go looking for it, don’t install it.
2: If you installed it, update it.
3: If you no longer need it (or, if it’s become too big of a security risk) get rid of it.
These rules apply no matter what device you use to get online, but I’ll add a few recommendations here that are more device-specific. For desktop users, some of the biggest risks come from insecure browser plugins, as well as malicious Microsoft Office documents and “macros” sent via email and disguised as invoices or other seemingly important, time-sensitive documents.
Microsoft has macros turned off by default in most modern Office versions because they allow attackers to take advantage of resources on the target’s computer that could result in running code on the system. So understand that responding affirmatively to an “Enable Macros?” prompt in an Office document you received externally and were not expecting is extremely risky behavior.
Enterprises can use a variety of group policy changes to harden their defenses against ransomware attacks, such as this one which blocks macros from opening and automatically running in Office programs on Windows 10. Other ransomware-specific group policy guides are here, here and here (happy to add more “here’s” here if they are worthy, let me know).
Also, get rid of or hobble notoriously insecure, oft-targeted browser plugins that require frequent security updates — like Java and Flash. If you’re not good about updating these programs frequently, you may fall victim to an exploit kit that delivers ransomware. Exploit kits are malicious programs made to be stitched into hacked or malicious Web sites. People who visit these sites or who are redirected to them and who are browsing the Web with an outdated version of Flash or Java can have malware automatically and quietly installed.
Mobile users in general need to spend just a tiny fraction more time discerning the origin and reputation of the applications they wish to install, as mobile ransomware variants tend to mimic or even piggyback on popular games and applications found in app stores and other places. Don’t just download the first app that matches your search. And always download from the original source whenever possible to ensure you’re not getting a copycat, counterfeit or malicious version of the game or application that you’re seeking.
For more tips on how not to become the next ransomware victim, check out the bottom half of the FBI’s most recent advisory on the topic.




One thing that confuses me about ransomware is it seems to me to be an easy fix IF you properly back up the files on your computer. I do this weekly using an external hard drive that is never connected to my PC unless I AM backing things up.
So, and I’m guessing I will get some feedback on this… Why not just ignore the warning, accept the fact some of my new files are gone forever (some I can probably get back via the internet if it was my original source, or have to recreate), and do a simple format and reinstall my operating system? I know this would be a lot of work, but since I do have a back up routine, and i faithfully follow it, I don’t see the big deal about ransomware.
Someone please explain to me the problems with my logic. I am sure there are many you will find and any comments are appreciated.
Two cents…
1) If on Windows, create a non-administrator account and ALWAYS operate out of that. Don’t use the Windows administrator account for anything other than administration.
2) If there is a built-in delay between infection and execution then with a week delay between backups the ransom-ware infestation may also get backed up.
3) Connecting the backup drive to the computer may be a trigger… A script connecting to a non-local or intermittently connected machine (NAS) is better.
4) I would recommend that a business do daily, at minimum, incremental backups, with a weekly full backup. Keep at least a month’s worth of backups available off-line/off-site. Insure those backups are non-volatile or fail-safe write protected. An incremental backup may allow the ransom-ware to be more easily found.
Imagine you have paperwork that needs to be kept on hand for X number of years. Tax returns, for instance. If your computer goes belly up, kaput, the government won’t accept that as an answer during the audit. You are expected to maintain those records. You could print them out and stick them in a drawer, sure, but you could lose paper records to floods, fire, etc.
Another instance is if you’re using your computer as your source of income. For instance, working on video or art projects under commission. If you don’t give them the finished product at the end of the project they’re going to expect you to return all funds advanced, if not fees to cover expenses for someone else to do the work on short notice.
When you come to a full scale business, there’s far more data than can be reasonably expected to just download it off the internet someplace again. I’ve heard of police departments who were hit with ransomware who paid up because records about who was being held on what charges and similar data was kept in electronic-only form. They can’t exactly walk from cell to cell asking the people what charges they’re being held on.
What you should do is have a media rotation. Hook up a drive to your computer during the backup. Perform the backup. Disconnect the drive. Next time you run a backup hook up a different drive. Perform the backup. Disconnect the drive. And so on. After you have a month or two of backups you’re undoubtedly going to have a backup of your system from before the infection took hold.
I am With you Joe,
I totally agree with the idea of running a backup system that is designed for the possibility of a total loss scenario.
By working on the presumption that it is virtually impossible to protect anything digital that has an internet connection the user can get used to the idea of losing then restoring the original files/programs/operating system, and work accordingly.
The quoted example of $750 USD for an average ransom would be better spent only once on a quality total back up and restore system. IMO
Joe you are correct that proper backup is the simple defense against ransomeware extortion. However as developers of low cost backup software and appliances we find it difficult to convince users to make backups that are vaulted, versioned and verified. There seems to be a belief that anti-virus is essential, but backup is boring and optional. Then even when we sell our products to users, too many just don’t get around to installing and using them till we remind them. Maybe users want to add a bit of excitement into their lives and live dangerously!
No it is just that most consumer grade software ( and most pro stuff too) is crap. It is not intuitive to use and kludgy at best. Help systems are almost non-existent and usually aren’t kept up to date with the software. Vendor support! Don’t make me laugh. People buy the dream from your sales brochure, as the product is made to sound good and easy to use, then when they find out it is not, it is too late. Develop better software, get rid of the crappy programmers working for you and hire people who think about the user first. You will then find your software being used. Unfortunately, if all the crappy programmers were forced into other jobs they were suited for like janitor work, there would be almost no one left in the industry.
First, your external hard drive can be possibly be encrypted during your weekly backup. You didn’t say how many external drives you have but you should have at least three. If you have three, and the one you just used just got encrypted, you should have the one from a week ago to use for restoring your system.
Second, before you format your drive and restore your operating system, do a backup. This way, if you find that after you’ve formatted your drive that you can’t restore from your backup, you will at least have a copy of your encrypted files that you may be able to decrypt.
Sure, these two things are overkill but I like overkill when it comes to backups and restoring.
One thing that hasn’t been mentioned in these comments is that you need to test restoring from backups periodically to ensure that the backups are working properly. If there is a problem, you don’t want to find out when you try to recover from the ransomware.
that is a huge problem at even the enterprise level… Full DR scenarios are rarely practiced and backup sets are rarely verified (the backup software itself running a verify doesn’t cut it)… full restore testing is a must.
Like most people that drive cars, they just use them. If it wasn’t for Check Engine lights, Maintenance wouldn’t get done and most cars would be junk early on.
Computers (out side of companies) rarely get real service. They get used until they stop working, then maybe they get serviced. Often they get set aside and replaced. It’s very intimidating, frustrating and embarrassing to people that are not familiar the workings of computers. So they get serviced or junked only after the worst has happened to them.
I don’t see a solution, less fully monitored and supported systems like cars are. Which is an expense most people will skip “it won’t happen to me”, “my friend can do that” , “it comes with antivirus”, “the OS does all that auto-magically”
I utilize files that important can be backed up to another HD that is outside the operating system. Operating system can reformatted and fixed if a crytpolock lock the drive.
I have heard people backing up their drive only to find their backup drive is infected as well.
I remember a time where I used to work, someone sent an email that used one letter off the domain name of the company to an employee who clicked on it and presto a crypto lock. The company utilized the backup system on a daily basis.
Talking to the IT people, I learned it took them a week to assess what happened, what file is infected and reinstalled the infected operating system bring back the lost file via backup. The system that company used for their accounting system was not affected as it is backed up at two other locations (for safekeeping if one goes down) . I was still able to work despite losing one application on my desktop.
Long story short they never paid it.
On the hand, recently the Dighton PD in MA paid the $5k ransom to unlock the crypto-lock and the town officials defended the payment. It goes to show you they did not back up anything to prevent loss of files.
http://turnto10.com/news/local/hack-of-police-computer-system-costs-department-5k
You have only one external hard drive?
Hard drives are cheap, relative to the cost of losing the data. Get several more.
Also get a program that does an image backup, and which can be booted from a CD or a USB device. This will isolate the image backup from all programs on your computer.
Second that. A USB3 hard drive case with laptop-sized (2.5inch) hard drives is big, fast, and very robust. I’ve even dropped them on a hard floor and they’ve kept working. About software, well, windows and linux are very different.
It might be worth checking SourceForge for decent software…
Joe: that was true with the earliest ransomwares. However, malware programmers aren’t, for the most part, stupid. Many/most modern ransomwares will attempt to encrypt any backup devices that they can detect as well.
Yes, external drives that get connected to the computer would be included in that list.
With ransomware, always assume that your backups are only available if the ransomware doesn’t have the capability to navigate any and all instances of mounted drives of any kind including network attached storage. If the ransomware is aware of other mounted drives, then assume your backups are gone and toast if you are unable to decrypt them. That is my two cents.
Most people (not all) just don’t care about internet security until it’s to late. People just don’t want to be educated on protecting themselves from internet threats like ransomware.
As I stated in a past article, doing regular backup’s to a encrypted hard-drive that’s not permanently connected to the computer is the way to go.
As usual an excellent helpful article that I will pass along to my clients/friends. I’ve had one that was hit twice, but thankfully had offsite backups of critical QuickBooks, document, and database files. All it took was one office employee opening an email with an attachment on Windows 7, and it propagated through the intranet, causing here thousands of dollars, but still less than the miscreants wanted…
Happy Holidays, and thanks for your efforts!
I just installed: Cybereason. https://www.cybereason.com/
I have no idea whether it works or not. I found an article singing its praises so I took a chance. What does everyone else think?
We just hope you didn’t install malware…
Another useful site that I didn’t see listed is ID ransomware, which tells you what ransomware has infected your computer.
(Some ransomwares lie about their names because they can’t get the file encryption right and therefore pretend to be some other ransomware that does work.)
I also rather like ID Ransomware. I tend to send users there when they report ransomware infections, especially if I wasn’t able to identify anything obvious in the logs. Michael Gillespie (aka. demonslay335) does a pretty good job with the site.
CyberReason is a legit program. From what I understand, it works by setting up honeypot folders using characters like $ and !, which are scanned early on by many ransomware. If it detects one of its honeypot files is encrypted, it will alert the user and pause the process.
Though this definitely works, it has two disadvantages that I can see:
1. There are ransomware infections that are now being a bit more random in what files and folders they encrypt first.
2. Files may be encrypted before a honeypot folder is touched.
I also agree about ID Ransomware. Great tool and updated daily by Michael, who is a very dedicated ransomware researcher.
Hi, I agree with Joe to prep with backups. However, I used to have too many versions of backup which made my decision to choose which backup that is reliable and good is rather a challenging task.
I always try to defense it from the source, ie its the malware that triggers the file encryption issue, thus I invested quite some money in anti-virus, anti-malware software. I always believe freeware comes with ‘hidden’ danger. 🙁
Hope the above helps, 🙂
It depends on your sophistication or intuition. The simplest way to do automated backups is having a external hard drive attached to the server. Then, have the server on one of those timers that turns the external hard drive on 30 minutes to an hour before the backup starts, and powers down about three hours later. The external hard drive uptime can be configured around the amount of time your server takes to do a bare metal backup, with all drives included. You can plan backups on whatever days you wish, and the external drive will be available during that time.
You can on occasion have a “known good” backup on another drive that can be done on a less frequent basis. For me, at the current level of need, I do a known good backup once every three months and store that one away. I do a complete full backup on three servers once a week. During the busy time of year, I may do bare metal backups twice a week. This eliminates the need for partial backups and trying to decide what is good or bad.
For me this is a simple cost effective way to ensure my stuff is backed up and at the ready should need arise.
Does anyone know if storing my data files/documents in Dropbox protects me from ransomware? Or at least protects me from losing the data. From what I have read Dropbox would have the files in backup and could recover them for me.
I have personally seen several strains of ransomware that were able to traverse up to the Dropbox files and encrypt them as well. I would not rely on Dropbox as a viable alternative to local backups taken offline or off-site afterwards.
As Troy said, “I would not rely on Dropbox as a viable alternative to local backups taken offline or off-site afterwards” (and I’d add that you shouldn’t).
That being said, I’ve helped a friend recover from a ransomware hit thanks to Dropbox. In most cases, Dropbox will in fact protect you from ransomware (at least currently).
Dropbox keeps backups of files for 30 days for all types of accounts (including free) and, up until now, I haven’t heard of ransomware that tries to interfere with dropbox backups. In fact, the only way they could try to do this would be via the “delete permanently” API, which is only available to dropbox business apps. In theory, if a ransomware stole the session token used by a dropbox business app, they could make calls to that API and permanently delete a file. I do not know whether the main Dropbox for desktop app is part of these “dropbox business” apps, which is a big unknown regarding the feasibility of ransomware that interferes with Dropbox versioning.
Regarding recovering your files: what happens is that, when a file is deleted, Dropbox actually creates a new “deleted” version of that file, so you can work with the API to restore the previous, non-deleted version. So when a file is encrypted then deleted on your desktop, in Dropbox the old file is changed to it’s new deleted version and a new file is uploaded. To get back to the previous state, you’d have to write your own tool (or use & modify one that I shared on Github a while ago https://github.com/l01cd3v/CryptowallDropboxRecovery) and wait until your thousands of API calls are made.
I’m waiting for malware that performs delete-account against things like Dropbox and Carbonite…
In short, no current technology will perfectly defend against future threats.
Basically the feature you want in a backup system is something that is “append-only”, that doesn’t allow the (corruptible) data source to issue deletes/rewrites to the backup system. That’s what made WORM (write once, read many) style CD-R/DVD-R (not CDRW/DVD-RW) based backups valuable. Worst case, something corrupts a recent session of a multisession disk, you just need software to let you access a previous session.
If you have a trusted Unix system which can receive backups and persist them using snapshots (ZFS), that’s probably the best.
It should also be noted that a few of the ransomware versions claim to have 3DES or AES encrypted all your files, replacing them with .crypted extensions, and demanding payment via Bitcoin. In fact, they have just XOR’d the first 1024 bytes of the file with a string from the ransomware package itself. The same ransomware package contains flag which reverses the encryption when you have “paid”.
These typically come in as Javascript/WScript email attachments claiming to be “Invoice_xxx” or “Delivery_Confirmation_xxx”. I have deobfuscated and extracted the encryption key from a number of these.
Some of the file names I have witnessed are pretty common;
par_cert_(7 random numbers).zip
user(7 random numbers).zip
Mpay(7 random numbers).zip
scan(7 random numbers).zip
doc_(7 random numbers).zip
inv(7 random numbers).zip
payment(7 random numbers).zip
softlic(7 random numbers).zip
f_license_(7 random numbers).zip
invoice-(7 random numbers).zip
order-(7 random numbers).zip
tax_pdf_(7 random numbers).zip
invoices(7 random numbers).zip
receipt(7 random numbers).zip
bill(7 random numbers).zip
SCAN_jout1999.zip
details_jout1999.zip
unpaid_jout1999.zip
payment-jout1999.zip
ATM_jout1999.zip
order_jout1999.zip
The jout1999 file naming convention was coming from supposedly many different countries.
I looked up the majority of these via sha256 and they are related to cryptoware or a javascript type payload that will call home for other malicious files.
Be safe out there.
I read somewhere that there is a UK based website that helps individuals and may have decryption keys for a limited amount of cryptoware strains. Is it the place mentioned in this article? I don’t remember. =)
For the small business user or home office, nothing beats a portable external hard drive that’s plugged in for a short period of time to back up the machine. Buy one for each important workstation and server owned. It’s a small price to pay to back up data and unplug the device when the backup is finished
Brian introduces this right at the start of the article – nomoreransom.org
For a few small crumbs of comfort, here’s an article which shows that a lot of ransomware products are inherently flawed and this may help researchers to get the keys necessary for decryption. Briefly, ransomware developers don’t bother to understand encryption, and make a lot of mistakes as a result.
http://www.infoworld.com/article/3130672/encryption/stupid-encryption-mistakes-criminals-make.html
Ad blocker for your web browser and don’t click on files and links in emails from an unknown source. Know how to use the task management tools in your OS to kill your web browser if some nasty advertising hijacks your browsing with infinite dialog boxes.
If you run across a website that won’t let you see it unless you disable your ad block, don’t do it. Think twice and then open a different browser without ad block just to view that site.
I’m so old, and have been online so long, I can remember when it was a joke to newbies on usenet that you could catch a virus by reading an email.
Then Microsoft made it possible.
Who needs macros in a word processing document?
Trust Microsoft to think it was a good idea. (And now they disable them by default.)
Simple fixes: I will say with 100% confidence that the drug/bangbuddy/oral jelly/etc,/etc/etc are 100% fraudulent. Delete, do *not* open, and CERTAINLY DO NOT open the attached document.
Brian: here’s a bug that I need to file against Firefox: the last few weeks (note that I’m on CentOS 6), even if you have chosen, under View on the menu to display the email as plain text, it *ignores* that if, (assuming what I saw was true), the message has a header of display inline.
Sorry, my mistake – it’s Thunderbird, not firefox.
Anyone considering backing up to the cloud, consider SpiderOak One. Encrypted and zero-knowledge, only you control the keys.
SpiderOak one provides full file versioning: if the randsomware jumped to the cloud, you would have up-to-date versions.
Cloud-based backup can be a good PART of a total backup solution.
Ooooh, I love little advertisements like this!
A more shameless exhibitionist than Barnum and Bailey.
You never who put what up, however as a longtime user of SpiderOak – but since the guy didn’t put a link there I doubt it was advertisement. SpiderOak is a good DropBox like replacement if you want some additional privacy (they don’t get your encryption keys / password unlike DropBox which is waiting for the government’s request for your files).
It also keeps copies of each version of a file as changes are uploaded (that will eat into your space over time but you can delete them as needed) – this gives you some protection from loosing your files if ransomed versions get uploaded. Just my $0.02.
Easy and most painless way is just pay the money!
Even its just 200$ you can still pay
Your photos files and everuthing is more
Valueble then this money uou pay.
Money come money go…
People think too much about money!
Sometimes you win sonetomes u loose.
I will pay ransom.
Would you not pay ransom if your
Toughter is kidnapped? Offcourse you pay.
Nothing is free so what we can do nothing..to do
@marco, For honorable persons, there is more to life than money. If you pay ransom, you not only lose your self-respect (which is priceless), you encourage criminals to harm others.
You also show that you’re a soft touch and they won’t hesitate to have their ‘friends’ encrypt your stuff again, if you fail to harden / backup.
So..90-s was racketeering. We dont admit
But every business owner payed.
Now couse of new hi-tech new things
But things remain same.
Im very sure in future will be life
Ransom…in order to live you pay.
I guess criminals will take control
Over our small micro-chip under skin
And if we dont do as they say i guess
They swich your chip off.
But who we blame?…tgats what we ask for.
Simple!
To avoid paying ransom (worked for me) is just write to the support in russian and say that russians don’t touch russians and they’ll give you the code for free. Funny or not but it really works and the only reason That I came up with is that you usually don’t touch people from your country to avoid being prosecuted.
Yes,criminal respecting other criminal.
If you steal from criminal… you might die.
What is the status of linux in this regard. I believe I read that using only a VM, and never using dom0 to access offsite, and simply backing up the VM periodically, is safe, although malware is getting smarter concerning VMs.
There is a program called “Sandboxie” that has been around for 12 years. Running your browser with this should quarantine any ransom related malware that could infect your computer.
https://www.sandboxie.com/
Cal,
Sandboxing is mostly great. Many malware applications are coded to detect and close when running inside a sandbox or VM, and the end user will end up running the malware outside of the quarantine anyway. And these are users smart enough to even be using these tactics in the first place. Not to mention some malware examples have been found in the wild which exploit such tactics and are able to “escape the sandbox” at the application layer.
The only realistic or practical way to safeguard against ransomeware data loss caused by end users is a data backup routine using non-network shared methods.
I love Sandboxie and have been running the full version for at least five years. Sorry to hear that some malware can jump out but SBIE is still great to have.
I also just installed RansomFree, a freeware honeypot program that seems pretty well developed. Sure it can be “worked-around” but, like Sandboxie, seems hugely better than nothing.
@watching,
It is hugely better than nothing, but it relies on end user training and awareness. Which is unfortunately worthless.
Programming today is a race between software engineers striving to build bigger and better idiot-proof programs, and the Universe trying to produce bigger and better idiots. So far, the Universe is winning
Remember this? It’s still true. If you allow a way for them to fsk up, they will.
@ransomfrèe, it’s Wndows based. Call me skeptical.
Check out HoneyDrive, and moreso Autopsy.
Meanwhile…in russia…
Dimitry testing his Amg g wagen mercedes.
Or maybe porche cayenne…or bmw m5.
No question that alot expensive cars in russia.
Money from the west.
And the west is sinking in more dept.
backups backups backups….my Windows command script to backup to a USB stick or SD card which I do not leave mounted all the time so it does not become a target of ransomeware.
– first, install rsync
– use this script (edit the particulars to suit your environment), save it as a .cmd file
——————– start backup script ——————–
@echo off
REM 1. Mount your USB stick or SD card (get volume UID from ‘mountvol’ command)::
mountvol F: \\?\Volume{1d8b5a6d-cba2-11e6-829a-40167e82541c}\
REM 2. rsync command to sync d:\mydox directory to USB stick F:\bkup directory:
“C:\cygwin64\bin\rsync.exe” -czav /cygdrive/d/mydox/ /cygdrive/f/bkup/
REM (optional) Create a shadow copy of D:
wmic shadowcopy call create Volume=’D:\’
REM (Optional) delete the oldest shadow copy of D:
REM vssadmin Delete Shadows /For=D: /Oldest
REM 3. Unmount the USB stick F: drive as we don’t want it mounted all the time
mountvol F: /p
——————– end backup script ——————–
Enjoy! 😉
Brian’s article as always is insightful. DirkYottabyte, thanks for the code. It was interesting to discover (and potentially understand) what it means and how it works. Not knowing a stitch about computer language, I am amazed by it – and enjoyed discovering what each line did.
1 Milliom Dollar Ransomware Guarantee. I agree. Do not pay the ransom.
Of course people will pay for ransomware. People have far too many things to do then to clean up after lousy designs, and worse development.
Your example of the woman who cannot pay for her rent is spot on, given the number of homeless families. Last time I checked, the average age of a homeless person was nine. Most people on the Internet are similarly unable to locate the resources to protect themselves. And we have heroes (in that case, called foster parents) but not nearly enough to go around.
It is further applicable, given that when large numbers of homeless women became visible they were the subject of humor. Instead of “homeless people” women who are homeless are “bag ladies”. Some of the comments seem to fall into this victim-blaming pattern.
People who are victims of ransomeware are similarly victims of large-scale market forces they cannot control. They should not be subject to blame nor derision for trying to manage their on-line lives with inadequate resources. A solution based on the rare hero compensating for systematic global failures doesn’t scale.
There are many people overseas, and in America that just don’t care. I found a network of fake staffing companies being run off of DreamHost (based in Bria California), last year. The scammer bought 20+ domains. He would target specific job seekers sending them emails from these bought domains with matching web sites. The goal was to walk the victim through fake phone interviews and then request SSN and DOB to submit the victim to a ‘client corporation.’
I warned the DreamHost abuse staff several times showing them the threads of the scam, the posting by various victims and the DreamHost staff responded with a fu&# off. They added that they would only respond to law enforcement orders. The domains continued to exist until they expired.
As long as the employees of the hosting companies get their paychecks, they don’t care. As long as the hosting companies executives continue to see money from the scammer/client they don’t care.
I created a blogger site to document all that I found about this scammer at.
https://fakestaffing.blogspot.com
The scammer is still running with a new batch of domains hosted on American services. They are DreamHost, 1and1.com, and blue host.com.
There is one hosting company that I warned that did shut down three domains.
Free protection is available for MAC (RansomWhere?):
https://objective-see.com/products/ransomwhere.html
And for Windows (RansomFree):
https://ransomfree.cybereason.com/