The process of buying or selling a home can be extremely stressful and complex, but imagine the stress that would boil up if — at settlement — your money was wired to scammers in another country instead of to the settlement firm or escrow company. Here’s the story about a phishing email that cost a couple their home and left them scrambling for months to recover hundreds of thousands in cash that went missing.
It was late November 2016, and Jon and Dorothy Little were all set to close on a $200,000 home in Hendersonville, North Carolina. Just prior to the closing date on Dec. 2 their realtor sent an email to the Little’s and to the law firm handling the closing, asking the settlement firm for instructions on wiring the money to an escrow account.
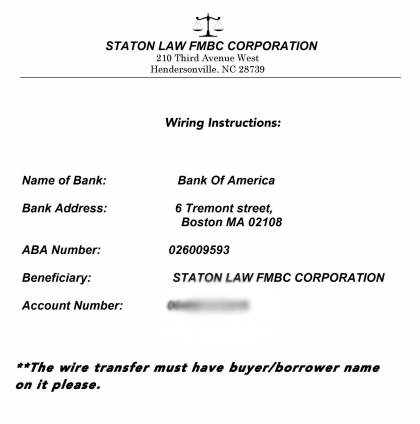
The fraudulent wire instructions apparently sent by the hackers via the settlement law firm.
An attorney with the closing firm responded with wiring instructions as requested, attaching a document that had the law firm’s logo and some bank account information that was represented as the seller’s account number. The Little’s realtor sent the wire on Thursday morning, the day before settlement.
“We went to closing at 1 p.m. on Friday, and after we signed all the papers, we asked the lawyers if we were going to get back the extra money we had sent them, because they hadn’t be able to give us an exact amount in the wiring instructions. At that point they told us they had never gotten the money.”
After some disagreement, both legitimate parties to the transaction agreed that someone’s email had been hacked by the fraudsters, and was used to divert the wired funds to an account the criminals controlled. The hackers had forged a copy of the law firm’s letterhead, and beneath it placed their own Bank of America account information (see screen shot above).
The owner of the Bank of America account appears to have been a willing or unwitting accomplice — also know as a “money mule” — recruited through work-at-home job schemes to receive and forward funds stolen from hacked business accounts. In this case, the money mule wired all but 10 percent of the money (a typical money mule commission) to an account at TD Bank.
Fortunately for the Littles, the FBI succeeded in having the resulting $180,000 wire transfer frozen once it hit the TD Bank account. However, efforts to recover the stolen funds were stymied immediately when the Littles’ credit union refused to give Bank of America a so-called “hold harmless” agreement that the bigger bank wanted as a legal guarantee before agreeing to help.
Charisse Castagnoli, an adjunct professor of law at the John Marshall Law School, said banks have a fiduciary duty to their customers to honor their requests in good faith, and as such they tend to be very nervous legally about colluding with another bank to reverse payment instructions by one of their own customers. The “hold harmless” agreement is usually sought by the bank which received a fraudulent wire transfer, Castagnoli said, and it requires the responding bank to assume any and all liability for costs that the requesting bank may later incur should the owner of account which received the fraudulent wire decide to dispute the payment reversal.
“When it comes to wire fraud cases the banks have to move very quickly because once the wires make it outside the U.S. to foreign banks, the money is usually as good as gone,” Castagnoli said. “The receiver or transferee usually insists on a hold harmless agreement because they’re moving the money on behalf of their own account holder, kind of going against their own client which is a big ‘no-no’ when you’re a fiduciary.”
But in this case, the credit union in which the Littles had invested virtually all of their money for more than 40 years decided it could not in good faith provide that hold harmless agreement, because doing so would stipulate that the credit union affirms the victim (the Littles) hadn’t willingly and knowing initiated the wire, when in fact they had.
“I talked to the wire dept multiple times,” Mr. Little said of the folks at his financial institution, Atlanta, Ga.-based Delta Community Credit Union (DCCU). “They finally put me through to the vice president of loss prevention at the credit union. I’m not sure they even believed all that was going on. They finally came back and told me they couldn’t do it. Their rules would not allow them to send a hold harmless letter because I had asked them to do something and they had done it. They had a big meeting last week with apparently the CEO of the credit union and several other people. Then they called me on Monday again and told me they would not could not do it.”
The Littles had to cancel the contract on the house they were prepared to occupy in December. Most of their cash was tied up in this account that the banks were haggling over, and so they opted to get a heavily mortgaged small townhome instead, with the intention of paying off the mortgage when their stolen funds are returned.
“We canceled the contract on the house because the sellers really needed to sell it,” Jon Little said.
The DCCU has yet to respond to my requests for comment. But less than a day after KrebsOnSecurity reached out to the credit union for comment about the Littles’ story, the bank informed the Littles that the other bank would soon have its hold harmless letter — freeing up their $180,000 after more than four months in legal limbo.
The Littles’ story has a fairly happy ending, however most of the other few dozens stories previously featured on this blog about wayward mortgage, escrow and payroll payments wound up with the victim losing six figures at least.
One of the more recent advertisers on this blog — Ninjio — specializes in developing custom, “gamified” security awareness training videos for clients. “The Homeless Homebuyer,” one of the videos Ninjio produced for a government client seems appropriate here: It features an animated FBI agent breaking the bad news to some would-be homeowners that their money is gone and so are their dreams of a new home — all because everyone blindly trusted unsecured email for what is essentially a high-risk cash transaction.
I like the video because its message is fairly stark and real: You could get screwed if you don’t take this seriously and proceed carefully, because once the money’s gone it usually stays gone. Check it out here:
So here’s what you need to know if you or anyone you know, love or even like are about to buy or sell a home: Never wire money based on the say-so of one party to the transaction made via email. You simply don’t know if their account is hacked, so from a self-preservation standpoint it’s best to assume it is.
Agree in advance who will contact whom — preferably by phone — on settlement day to receive the wiring details, and who will manage the wiring process. Never trust bank account details and payment instructions sent via email. Always double or even triple check any instructions for wiring money at settlement. Confirm all wiring instructions in person if possible, or else over the phone.
By the way, these same precautions can help make organizations less susceptible to CEO fraud schemes, email scams in which the attacker spoofs the boss and tricks an employee at the organization into wiring funds to the fraudster.
The Federal Bureau of Investigation (FBI) has been keeping a running tally of the financial devastation visited on companies via CEO fraud scams. In June 2016, the FBI estimated that crooks had stolen nearly $3.1 billion from more than 22,000 victims of these wire fraud schemes.
Castagnoli said many credit unions and small banks don’t have the legal staff with the clearance to make calls on whether to issue a hold harmless agreement, and so they usually try to punt on that when requested. Were she in The Littles’ position, Castagnoli said she would have called the head of the credit union and demanded assistance.
“If the head of the bank wouldn’t do it, I’d call my congressperson or a state banking regulator,” she said.
If you’re selling or buying the home yourself and somehow also in charge of wiring money, consider using a Live CD approach (all of these “live” Linux distributions will just as happily run on USB-based flash drives). I have long recommend Live Linux usage as a smart option for small businesses to avoid paying dearly when a Windows banking trojan snarfs their business banking credentials.




Interesting stuff. I’ve always advocated purchasing a home with cash if you can do that, but this is a very solid argument for using the borrowing bank’s money for several months until the dust of the transaction settles, then pay off the balance. The bank will be more diligent about wiring their own money than wiring your own. Bring a cashier’s check to closing and that’s that.
I tell all my colleagues in public accounting to never EVER trust an authorization through email. And as a bank auditor, I’ve worked with banks who accepted wire authorizations via email. They’ve received very pointed comments in my reports for that practice.
The only problem with cashiers check is title companies have also experienced fraud with this mechanism and they have moved towards only accepting wire transfers as payment.
I can also confirm that Title companies will not accept Cashier’s Checks anymore. They require that you wire the money.
Well said. It’s food for thought.
One of the problem you create when using cash to buy a house is that you are required to fill out a form with the bank if you take out more than $2,500 (this was designed to avoid structuring) and the recipient will have to do the same thing on their end and that becomes a hassle. This is why it is easier to wire or electronically pay and it shows up quickly. I used POPMoney to pay my fees to the closing firm when I sold my house because I can write an email to them to let them know it is coming and it used as a trace to the payment.
Having worked with financial institutions in the past where part of my job involved sending “hold harmless” documentation where fraud was involved, I can’t understand why the CU was so difficult. If there were any difficulties, it was where the would-be recipient said there were very few funds left, making from a business standpoint sending a letter of indemnity pointless. In no instance was I ever flat told the recipient bank wouldn’t honor the LOI.
Somewhat surprised by this. I just finished buying my first home last month and when I went for signing they gave me the payment instructions then, in person. Which frankly I kind of thought was the only way you would do this.
Though I guess anything that shaves time off of closing a deal will be viewed as a good thing and just ignore the increased risk it brings to the situation.
LOL – in Boston there is actually a corner of Tremont Street and Tremont Street! I’ve been there, confused the heck out of the GPS. Maybe there’s really a bank there too.
I’ve bought several houses, for the last few years the Realtor I’ve worked with used a Loop message system that required validation every time. Email to notify we had a document to validate in that system. Email was not used to for more than coordination of inspections and things, but all verification of those inspections were in the loop system.
Email has been insecure since Day one. When Fido Net evolved/prototyped into the current email of today, it was always considered insecure.
Currently I sit stunned in meetings where people tell me MS 365 is the future and hosting all their legal and other docs in those 365 cloud servers will be just fine. I love the “MS has never done anything bad” to its customers debate. I’ll act surprised when MS invests in all types of stuff that they were never interested over the next 10 years now that they have all the details of every business in their cage. It will all be done through subsidiaries of course.
Loop message system does not solve the problem. The hacker will phish the Loop credentials from the Realtor. Then use Loop to post updated wire transfer instructions.
The problem is not insecure communication. The problem is insecure credentials.
You can also use docusign for documents and that requires you to have an account. I used that to signed document when I sold my house. The reason for that is the distance just to sign a single paper everytime something needs to be done.
I once had a arpa.net account – and email. it’s never been trusted, except by the untrustworthy.
This guy gets it.
This is a clear inside job
It seems that the risk of getting caught in such a scheme is very high since there have to be domestic accounts involved and their owners are easily identifiable. So what happened to the owners of the two accounts involved? Did they go to prison? Did they reveal who was behind the fraud?
Sometimes the owners of the bank accounts are simply unwilling pawns, recruited by “work from home, just deposit money from here to here” scams.
Give them a good plea deal in exchange for telling everything they know, and then go after the masterminds. It can’t be that hard if prosecutors are willing. If there were effective law enforcement, these schemes wouldn’t be possible. I don’t hear these kinds of stories in Europe.
I’m curious where the suspected leak in information came from?
Questions, questions… law firm, bank or salesperson via dumpster diving, hack or collusion?
All this starts when title companies use 3rd or 4th party ‘vetting’ companies. For example, Lenders are demanding compliance with Gov’t regs (CFPB, etc.) this trickles down to the title companies. Lenders & banks now demand all the title companies they provide loan funds to are ‘vetted & verified’ in some way. This opens the door to all kinds of these ‘security’ companies. The security companies may know they are a mule or may not. Many of these security companies have websites that are cloud based and require their client (title company) to upload all of their control environment documents including emails address, personal addresses, employee names, phone numbers, banking information, E&O insurance, etc. If the login and password on the security company’s website matches other logins and passwords, it’s game over. This is the root cause to how all this fraud begins.
My prospective mortgage lender seems to be aware that email is not secure. So they sent me my username and password for their secure site in two separate emails. The third email with instructions contained the following line:
“You will not be able to access this secure service using Google Chrome. The site is best viewed with Internet Explorer 7.0 – 9.0.”
WHY
It is the way their system was set up when they created the webpage. I have done some webpage design and they do have a part that you can require to use certain browser to access it and it is what they use on their computers.
I think that’s funny.
“Fool me once, shame on — shame on you. Fool me — you can’t get fooled again…”
It has been suggested that cashier’s checks are not safe. I suppose checks can be forged. But the forgery is certain to be detected within at most a day, and the risk of immediate detection and arrest at time of closing is considerable. Even if the clsoing agent is duped, you need to sell the property to a legitimate buyer for real money immediately. How do you pull that off? You can’t bring it to a pawn shop. And most important, how do you avoid arrest once the fraud is detected? They have copies of your papers. Ok your papers are forged, but even so, they have pictures, they can describe you. The risk is so high and the chance of succeeding so low, what rational criminal would try something like that?
Unless there is no effective justice system in place?
So, at what point did the fraudulent account number come to be on the attachment? The law firm has some splainin’ to do.
It would be unlikely for the mail to be altered in transit, unless it went though some hacked private server. More likely a compromised host at the law firm?
My comments from the peanut gallery relate to several posts:
1. “This is a clear inside job.”
If they were inside jobs, the losses would be larger.
2. “It seems that the risk of getting caught in such a scheme is very high since there have to be domestic accounts involved and their owners are easily identifiable.”
Brian’s article outlined that the initial $200K transfer was to a money mule who took a 10% cut. That person may have a domestic account. The next wire or two will usually be to a non U.S. bank. My understanding is that when the money goes to China or Russia, it is not coming back.
3. “It has been suggested that cashier’s checks are not safe. I suppose checks can be forged. But the forgery is certain to be detected within at most a day, and the risk of immediate detection and arrest at time of closing is considerable.”
Our bank once took a week to tell us that they put a hold on a million dollar bank check. It wasn’t a bad or counterfeit check. They just randomly decided that week that a hold was in style.
Your risk of detection may be moderate. The likelihood of getting the police to come and arrest you is negligible. We lost a customer once because we refused to accept a $400K bank check from a buyer who was not coming to closing. Their accountant advised them not to wire money. Tough! A $400K bounced check would ruin my day. And the seller might be unhappy also.
4. “Even if the closing agent is duped, you need to sell the property to a legitimate buyer for real money immediately. How do you pull that off? You can’t bring it to a pawn shop. And most important, how do you avoid arrest once the fraud is detected? They have copies of your papers. Ok your papers are forged, but even so, they have pictures, they can describe you. The risk is so high and the chance of succeeding so low, what rational criminal would try something like that?”
A. Maybe you want to live in a house you can’t afford until they can get you out.
B. Maybe you are a squatter and you know it is going to take 6-9 months to get you out of the house.
C. I don’t care why you do it. I want to protect the sellers and other folks who have money in the account.
D. You set up a deal with a hard money lender to loan you 50% of the value of the home at 15% because you have a medical bill you have to pay immediately. You need a quick close.
E. The FBI has pictures of their top ten most wanted. Many driver license pictures are so bad you don’t even have to bother to fake them.
Ad 2: Brian’s article specifies at least two domestic accounts that were involved, which is why in the end the money could be retrieved. If the money mule had wired the money abroad, you are right, the money would likely have been gone. But the mule would still be on the hook and there would likely be evidence pointing to the masterminds. I’m convinced that if law enforcement moved forcefully in these cases, fraudsters would know better than to try such transparent schemes. There is hardly a shortage of law enforcement energy in the US – still the highest imprisonment rate in the world, and most of the convicts have done lesser crimes than that – it just seems that white collar crimes are not the priority of prosecutors. Again, why?
Further: US banks don’t wire large amounts of money so easily, even domestically. I have always found it extrenely cumbersome to do a money transfer. There are also money laundering laws that require the banks to report suspicious transfers. I don’t know in detail but it seems that such a case should be suspicious enough.
Ad 3. “Your risk of detection may be moderate.” No, it is 100%. The forged check *will* be detected very soon. How could it not be?
“The likelihood of getting the police to come and arrest you is negligible.” If you are caught shoplifting two dollars worth, the police will come and arrest you. If you present a forged $200,000 check – which can usually be verified with a phone call -, why wouldn’t the police come and arrest you? I’m really curious what your explanation is. Are you saying law enforcement doesn’t care about forgery as much as they care about shoplifting? If that is so, why isn’t this perceived as a monstrous scandal? What I find fascinating is that all the American commenters seem to simply accept that theirs is a broken system, as if nothing could be done about it.
Ad 4. Really, you think there are people who would try buying a house with a forged check and then live in that house hoping that the victims of the fraud will just leave them alone? I really have no idea what universe you live in.
I found your site on https://secure360.org (5 information security blogs page). I always find something new to read related computer security.
I am glad to find your site.
Did my comment get submitted?
It seems that there is moderation, even though I have posted before without a problem. Please kindly free my comment out of moderation and discard the “test” messages, thanks!
Excuse my but is it possible to publish my original response to Spike and delete the tests instead of the other way round? Thanks.
The Whatsapp outage was likely caused by an ongoing DDOS attack. Mr Krebs, can you confirm who was behind this and why?
Brian – you have a typo in paragraph 2.
“.. their realtor sent an email to the Little’s …”
Littles, not Little’s.
I’ve learned 99% of my computer security skills from your site and grc.com, really appreciate the effort you put in.
I do my banking on a Mint linux live CD boot from a VirtualBox VM, is that as secure as booting directly on a PC?
Thank you So Much for this informative Post!
I just wonder why there is not a process in place to check.
If somebody sends me to request to send money, I would double check with them ( give them a phone call or ask them in person, and do not use the phone number in the email).
This would be a very simple solution.
This doesn’t directly address the Littles’ scenario, but I put together a few mini-seminars on Internet safety that might be useful. Take a look here:
http://dgregscott.com/resources/
– Greg Scott
Random thoughts on the above:
1. Cashier’s checks. These are practically worthless in real world transactions. In one instance a client was paid with a legitimate cashier’s check and when presented for payment the institution refused payment. In another instance I took the legitimate cashier’s check to the bank days before closing so my bank could confirm the authenticity of the check before the time came to make disbursements. My bank told me “ok, you can disburse, we have confirmed the check is good.” So, I recorded the deed and went to wire the purchase money to the seller and then my bank told me they would require a two week hold on the cashier’s check before they would allow the wire to take place.
2. Do not understand the issue on interbank indemnification. Since this was a US transaction, the bank that wanted indemnification could have just interpleaded the money into court, made all potential claimants to the money parties and then the court could have decided who was the proper owner of the fund. When the case is over the court would pay the money to the “winner”and risk of paying the wrong person would be $0.00. Meanwhile the likelihood criminals would go to court to assert their claim is likely to be 0.0%.
3. FBI: do not count on them. They will will not pursue interstate wire and similar fraud cases unless the money involved is “enough ,” or involves governmental corruption. Yes, $200k was enough the last I checked, but since my case involved interstate wire of funds for bribery purposes of someone who was not a governmental employee and the amount was less than $100,000, that was all she wrote.
I wonder if PGP signatures on all e-mail messages related to a transaction would help. Especially e-mail messages with bank wiring information. Though if a title company’s e-mail servers are compromised the crooks could sign fraudulent e-mail messages and still get the money sent to bank accounts they control.
On second thought, the measures suggested by other commenters (phone verification of wiring instructions) are better than PGP signatures.
My law office does not send out going wire transfers. Instead, we issue paper checks from the trust account and send them via FedEx or UPS to the intended recipient. We will not automatically honor any instructions from anyone to change the address of the recipient. For incoming wire transfers, we do not send out our trust account wiring instructions via email – only via a confirmed land line fax number, with subsequent phone call confirmation at the number of the sender we are initially given by the sender. Further, we employ a bank security protocol called “payee positive pay” by which we notify our bank at the end of each day what items we have issued, with full identification. The bank is duty bound to honor only those items and none other.
This is an insecure email issue? It seems more that there were folks lurking on one-party’s servers to obtain knowledge of the transaction. It’s not phishing. It’s intervening in a known transaction, the information the bad guys have having been obtained through some other data breach. Otherwise, how could the tricksters have known to send such an email? The story is mis-presenting the risk and likely the liability.