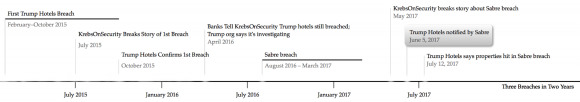
Maybe some of you missed this amid all the breach news recently (I know I did), but Trump International Hotels Management LLC last week announced its third credit-card data breach in the past two years. I thought it might be useful to see these events plotted on a timeline, because it suggests that virtually anyone who used a credit card at a Trump property in the past two years likely has had their card data stolen and put on sale in the cybercrime underground as a result.
On May 2, 2017, KrebsOnSecurity broke the story that travel industry giant Sabre Corp. experienced a significant breach of its payment and customer data tied to bookings processed through a reservations system that serves more than 32,000 hotels and other lodging establishments. Last week, Trump International Hotels disclosed the SABRE breach impacted at least 13 Trump Hotel properties between August 2016 and March 2017. Trump Hotels said it was first notified of the breach on June 5.
According to Verizon‘s latest annual Data Breach Investigations Report (DBIR), malware attacks on point-of-sale systems used at front desk and hotel restaurant systems “are absolutely rampant” in the hospitality sector. Accommodation was the top industry for point-of-sale intrusions in this year’s data, with 87% of breaches within that pattern.
Other hotel chains that disclosed this past week getting hit in the Sabre breach include 11 Hard Rock properties (another chain hit by multiple card breach incidents); Four Seasons Hotels and Resorts; and at least two dozen Loews Hotels in the United States and Canada.
ANALYSIS/RANT
Given its abysmal record of failing to protect customer card data, you might think the hospitality industry would be anxious to assuage guests who may already be concerned that handing over their card at the hotel check-in desk also means consigning that card to cybercrooks (e.g. at underground carding shops like Trumps Dumps).
However, so far this year I’ve been hard-pressed to find any of the major hotel chains that accept more secure chip-based cards, which are designed to make card data stolen by point-of-sale malware and skimmers much more difficult to turn into counterfeit cards. I travel quite a bit — at least twice a month — and I have yet to experience a single U.S.-based hotel in the past year asking me to dip my chip-based card as opposed to swiping it.

A carding shop that sells stolen credit cards and invokes 45’s likeness and name. No word yet on whether this cybercriminal store actually sold any cards stolen from Trump Hotel properties.
True, chip cards alone aren’t going to solve the whole problem. Hotels and other merchants that implement the ability to process chip cards still need to ensure the data is encrypted at every step of the transaction (known as “point-to-point” or “end-to-end” encryption). Investing in technology like tokenization — which allows merchants to store a code that represents the customer’s card data instead of the card data itself — also can help companies become less of a target.
Maybe it wouldn’t be so irksome if those of us concerned about security or annoyed enough at getting our cards replaced three or four times a year due to fraud could stay at a major hotel chain in the United States and simply pay with cash. But alas, we’re talking about an industry that essentially requires customers to pay by credit card.
Well, at least I’ll continue to accrue reward points on my credit card that I can use toward future rounds of Russian roulette with the hotel’s credit card systems.
It’s bad enough that cities and states routinely levy huge taxes on lodging establishments (the idea being the tax is disproportionately paid by people who don’t vote or live in the area); now we have the industry-wide “carder tax” conveniently added to every stay.
What’s the carder tax you ask? It’s the sense of dread and the incredulous “really?” that wells up when one watches his chip card being swiped yet again at the check-out counter.
It’s the time wasted on the phone with your bank trying to sort out whether you really made all those fraudulent purchases, and then having to enter your new card number at all those sites and services where the old one was stored. It’s that awkward moment when the waiter says in front of your date or guests that your card has been declined.
If you’re brave enough to pay for everything with a debit card (bad idea), it may be the time you spend without access to cash while your bank sorts things out. It may be the aggravation of dealing with bounced checks as a result of the fraud.
I can recall a recent stay wherein right next to the credit card machine at the hotel’s front desk was a stack of various daily newspapers, one of which had a very visible headline warning of an ongoing credit card breach at the same hotel that was getting ready to swipe my card yet again (by the way, I’m still kicking myself for not snapping a selfie right then).
After I checked out of that particular hotel, I descended to the parking garage to retrieve a rental car. The garage displayed large signs everywhere warning customers that the property was not responsible for any damage or thefts that may be inflicted on vehicles parked there. I recall thinking at the time that this same hotel probably should have been required to display a similar sign over their credit card machines (actually, they all should).
“The privacy and protection of our guests’ information is a matter we take very seriously.” This is from boilerplate text found in both the Trump Hotels and Loews Hotel statements. It sounds nice. Too bad it’s all hogwash. Once again, the timeline above speaks far more about the hospitality industry’s attitudes on credit card security than any platitudes offered in these all-too-common breach notifications.
Further reading:
Banks: Card Breach at Trump Hotel Properties
Trump Hotel Collection Confirms Card Breach
Sources: Trump Hotels Breached Again
Trump Hotels Settles Over Data Breach: To Pay $50,000 for 70,000 Stolen Cards
Breach at Sabre Corp.’s Hospitality Unit




While there are many breach happened, Capri by Fraser (Singapore) request their guess to provide all card information, including a scanned of both card sides. They must be very confident or risk free in term of protecting their customer.