A highly targeted, malware-laced phishing campaign landed in the inboxes of multiple credit unions last week. The missives are raising eyebrows because they were sent only to specific anti-money laundering contacts at credit unions, and many credit union sources say they suspect the non-public data may have been somehow obtained from the National Credit Union Administration (NCUA), an independent federal agency that insures deposits at federally insured credit unions.
The USA Patriot Act, passed in the wake of the terror attacks of Sept 11, 2001, requires all financial institutions to appoint at least two Bank Secrecy Act (BSA) contacts responsible for reporting suspicious financial transactions that may be associated with money laundering. U.S. credit unions are required to register these BSA officers with the NCUA.
On the morning of Wednesday, Jan. 30, BSA officers at credit unions across the nation began receiving emails spoofed to make it look like they were sent by BSA officers at other credit unions.
The missives addressed each contact by name, claimed that a suspicious transfer from one of the recipient credit union’s customers was put on hold for suspected money laundering, and encouraged recipients to open an attached PDF to review the suspect transaction. The PDF itself comes back clean via a scan at Virustotal.com, but the body of the PDF includes a link to a malicious site.
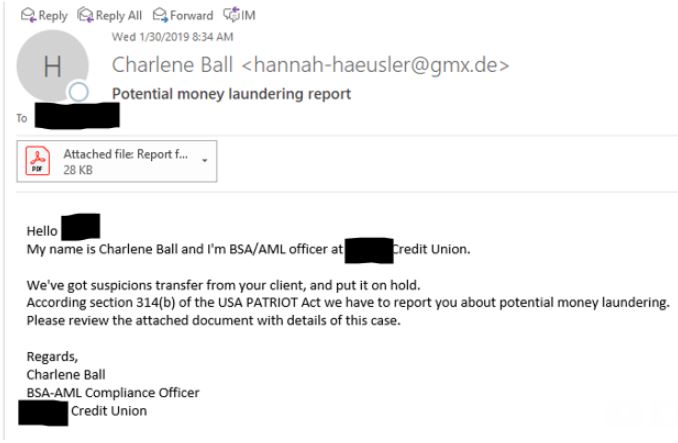
One of the many variations on the malware-laced targeted phishing email sent to dozens of credit unions across the nation last week.
The phishing emails contained grammatical errors and were sent from email addresses not tied to the purported sending credit union. It is not clear if any of the BSA officers who received the messages actually clicked on the attachment, although one credit union source reported speaking with a colleague who feared a BSA contact at their institution may have fallen for the ruse.
One source at an association that works with multiple credit unions who spoke with KrebsOnSecurity on condition of anonymity said many credit unions are having trouble imagining another source for the recipient list other than the NCUA.
“I tried to think of any public ways that the scammers might have received a list of BSA officers, but sites like LinkedIn require contact through the site itself,” the source said. “CUNA [the Credit Union National Association] has BSA certification schools, but they certify state examiners and trade association staff (like me), so non-credit union employees that utilize the school should have received these emails if the list came from them. As far as we know, only credit union BSA officers have received the emails. I haven’t seen anyone who received the email say they were not a BSA officer yet.”
“Wonder where they got the list of BSA contacts at all of our credit unions,” said another credit union source. “They sent it to our BSA officer, and [omitted] said they sent it to her BSA officers.” A BSA officer at a different credit union said their IT department had traced the source of the message they received back to Ukraine.
The NCUA has not responded to multiple requests for comment since Monday. The agency’s instructions for mandatory BSA reporting (PDF) state that the NCUA will not release BSA contact information to the public. Officials with CUNA also did not respond to requests for comment.
A notice posted by the U.S. Treasury Department’s Financial Crimes Enforcement Network (FinCEN) said the bureau was aware of the phishing campaign, and was urging financial institutions to disregard the missives.
Update, 11:13 a.m. ET: Multiple sources have now confirmed this spam campaign also was sent to BSA contacts at financial institutions other than credit unions, suggesting perhaps another, more inclusive, entity that deals with financial institutions may have leaked the BSA contact data.
Update, 5:26 p.m. ET: The NCUA responded and released the following statement:
Upon learning of the recent spear phishing campaign targeting Bank Secrecy Act officers at credit unions, the NCUA conducted a comprehensive review of its security logs and alerts. This review is completed, and it did not find any indication that information was compromised.
The most recent information available indicates the campaign extends beyond credit unions to other parts of the financial sector.
The NCUA encourages all credit union staff to be wary of suspicious emails, and credit unions may report suspicious activity to the agency. Additional information about phishing and other information security concerns is available on the agency’s Cybersecurity Resources webpage.
Also, the Treasury Department responded to requests for information about this event, stating:
FinCEN is aware of the phishing attempts and we’re examining the circumstances. There is no indication that any FinCEN systems were compromised.
Here is some information on 314(b) from our website
Note that the 314(b) system is designed so that individual compliance officers (registered with FinCEN) can find and directly contact each other. It provides no access to any type of broad financial database.
Original story: The latest scam comes amid a significant rise in successful phishing attacks, according to a non-public alert sent in late January by the U.S. Secret Service to financial institutions nationwide. “The Secret Service is observing a noticeable increase in successful large-scale phishing attacks targeting unsuspecting victims across industry,” the alert warns.
The Secret Service alert reminds readers that we in the United States are entering tax season, which typically brings a large spike in scams designed to siphon personal and financial data. It also includes some helpful reminders, including:
-Never click on links embedded in emails or open any attachments from unknown or suspect fraudulent email accounts.
-Always independently verify any requested information originates from a legitimate source.
-Visit Web sites by entering the domain name yourself (for sensitive sites, preferably by using a bookmark you created previously).
-If you are contacted via phone, hang up, look up the number for the institution at that institution’s Web site, and call back. Do not give out information in an unsolicited phone call.


Meanwhile our President is fighting the last war trying to build a concrete wall in the middle of the river dividing the US and Mexico when he should be building a cyber defense of our financial and communications networks our communications and power grids and our voting infrastructure. Why are the Republicans enabling this stupidity?
Because without the wall and / or significant border security measures, the rest of the issues will not matter.
Why can’t Dems see the need for border security? BTW why can’t we accomplish all of the necessary protection initiatives?
Because like everything the republicans champion, the facts show their stance is completely absurd and a waste of money that could go to other places. $50-500 billion for a total wild goose-chase that won’t affect anything. They will happily clap and stand by when he assigns the highest security roles in the country to someone with zero experience however and forces clearance to his daughter and her husband.
You mean like china?
The president is quite capable of doing both, provided that he receives the go-ahead for funding them both.
Why do you consider both items on an either/or basis, or were just being another unthinking Trump-basher?
Donald Trump regularly incites political violence and is a serial liar, rampant xenophobe, racist, and misogynist. The sooner that dirtbag is run out of office — the better.
President Cheeto isnt capable of anything but self promotion and exploitation, why oh why would you ever think he was capable of both creating a wall and cybersecurity at the same time? The guy cant even barely read, let alone make sound national security decisions.
“cant even barely read” – the irony burns.
You just haaaaad to bring politics in this didn’t you… ?
Jeez! The jerks are turning Krebs into a hate site.
Trump derangement at it’s finest. Never miss an opportunity to bash the President and ignore the members of your own party that all talked up border security until they didn’t.
Some of us have attention spans longer than a goldfish.
PS: How is the government going to fix an issue like this? Unless you are advocating for a complete government takeover of the Internet and national communications, it’s not going to happen. But you probably like that idea, don’t you?
Trump Derangement Syndrome is believing that the “truth is not the truth”. Trump Derangement Syndrome is believing that “what you’re seeing and hearing is not what’s happening”. Trump Derangement Syndrome is believing that our president is strong as he kneels and licks the boots of Putin, MBS, and any other actual dictator.
That’s right… he likes Putin sooooo much that he pulled out of the INF and is working with the EU to tighten sanctions on Russia after the Ukrainian sailors were picked up.
What was that you were saying about believing what you are seeing and hearing is not happening? You should probably go back to saving the polar bears from your parent’s basement.
Mr. krebs your Articcles getting less and less interesting.
so boring I was Trying to read this one Here but nothing really I Can’t even undestood where is the crime is Here??
and how do the criminals make profit??
it use to be More interesting to read about
I hereby release you to go find more interesting articles somewhere else. Bye now.
LMAO!
You are probably a fraudsters on here trying to collect information
A wall won’t stop phishing mails. And we don’t even know which side of the border they originate from.
I have other question, Mr. krebs where Will You live IF You not live in USA?
what Will you do if USA Will be falling into communism?
this capitalism regime Will not last long Trump Will devalue USA dollar… like soviet union.
Well, if I was an American citizen (which thankfully I am not), I’d be thinking seriously of moving to a civilised country such as Canada or New Zealand. Australia (where I live) isn’t all that bad either, but we too have had an idiotic government for years.
If these phishers ever hire someone proficient in the English language, we’re all doomed.
You mean you don’t address high banking functionaries you’ve never personally met as “dear”?
This comment section was a lot more useful before everyone started filling it with their political opinions.
You are liberal russian bot!
typical end-user “I got an email with an attachment and a link from someone who’s _______ so I opened it!” fill in the blank with any handy name (known to me, a stranger, a celebrity, whatever, the name hardly matters. Sad commentary on our education system and parenting today that we’re raising and teaching stupidity.
Back on topic: Coincidentally on Sunday 2/10 there was an apparent ATM skimming operation at my Credit Union in East TN with maximum per-day W/D’s of $800 that appear to be ATM W/Ds. Seems odd there are numerous and multiple skimmers at dozens of ATMs all at the same time. I alone have three friends who were hit all at different ATMs. Perhaps this is part of the phishing campaign and a backdoor network hack made to look like skimmers and masquerading as ATM W/Ds?
As silly as the scam seems, there are some that would fall for it. I like getting these and I will share them with my staff. I’d much rather share something that appears to be obvious than not share it and have someone fall for it just so I could say – yes, I saw it but didn’t think anyone would fall for it. Thanks KoS!
I love this thread
Witch hunt!
People love my wall. It’s gonna be a beautiful wall.
Witch hunt!
People love my wall and they love me. It’s going to be a beautiful wall.
Wow… amazing how politics pops up on this article.
Some how people wonder why the security field is suffering for talent and trend setters. This is why, we have individuals such as yourselves giving a horrible name to the profession with your stupid and blind rage. You are exactly what is wrong with society today.
Hopefully, Krebs can rid this site of these toxic people so we can get back to the content of what truly matters on this site.
It suffers for many reasons, including all the jobs only existing in high cost urban areas, restrictive dress codes, extremely high requirement for continued education, and at least around here fairly low pay. In my experience few companies actually value their IT security staff and few make any real efforts or budget towards it until after an event, and even then it is barely more than the minimal amount for a couple years then back to complacency. This attitude pervades every industry and government branch and goes all the way to the top.
I am sure they could used linkedin as well to find the BSA Officers then guess the email address.
The pdf attachment has only this in it:
“…The PDF file could not be opened. Please download the content of this document from the source: hxxps://interrafcu.com/336432-41835315_transfer”
Presumably the numbers and URL vary by credit union.
Interra is a real credit union, but not a Federal Credit Union. Only a knucklehead would open that pdf and then click on that link. YAMMV.
The PDF that I got (thanks Mila!) was for the Credit Union called Interra. It was sent to OCWEN which is a mortgage originator. My guess is that the criminals created custom domains and PDFs for each campaign.
$5,000,000,000 for a wall that can be easily defeated with a ladder or a shovel…
Do you honestly not see that this is just another attempt by Cheetos Jesus to line his pockets with more of the taxpayer’s money?
Ever hear of Halliburton?
Another facet of DNSpionage maybe? BTW, if it’s not related to ITSEC, please click off page to a set of sites called Facebook & Twitter. All those non-ITSEC related matters are better addressed there, IMHO…
Very interesting article, Mr. Krebs. I forwarded the link of your article to my daughter, who is lead of the KYC team (Know your Customer- AML related) at a major international bank.
I do wish all comments would be professional and on subject.